Over the weekend I received a nice holiday letter from lawyers representing Sony Pictures Entertainment, demanding that I cease publishing detailed stories about the company’s recent hacking and delete any company data collected in the process of reporting on the breach. While I have not been the most prolific writer about this incident to date, rest assured such threats will not deter this reporter from covering important news and facts related to the breach.
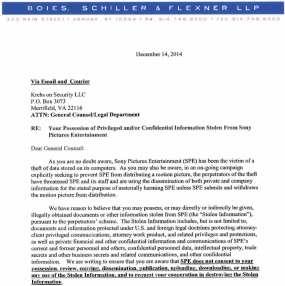
“SPE does not consent to your possession, review, copying, dissemination, publication, uploading, downloading, or making any use of the Stolen information, and to request your cooperation in destroying the Stolen Information,” wrote SPE’s lawyers, who hail from the law firm of Boies, Schiller & Flexner.
This letter reminds me of one that I received several years back from the lawyers of Igor Gusev, one of the main characters in my book, Spam Nation. Mr. Gusev’s attorneys insisted that I was publishing stolen information — pictures of him, financial records from his spam empire “SpamIt” — and that I remove all offending items and publish an apology. My lawyer in that instance called Gusev’s threat a “blivit,” a term coined by the late, great author Kurt Vonnegut, who defined it as “two pounds of shit in a one-pound bag.”
For a more nuanced and scholarly look at whether reporters and bloggers who write about Sony’s hacking should be concerned after receiving this letter, I turn to an analysis by UCLA law professor Eugene Volokh, who posits that Sony “probably” does not have a legal leg to stand on here in demanding that reporters refrain from writing about the extent of SPE’s hacking in great detail. But Volokh includes some useful caveats to this conclusion (and exceptions to those exceptions), notably:
“Some particular publications of specific information in the Sony material might lead to a successful lawsuit,” Volokh writes. “First, disclosure of facts about particular people that are seen as highly private (e.g., medical or sexual information) and not newsworthy might be actionable under the ‘disclosure of private facts’ tort.”
Volokh observes that if a publication were to publish huge troves of data stolen from Sony, doing so might be seen as copyright infringement. “The bottom line is that publication of short quotes, or disclosure of the facts from e-mails without the use of the precise phrasing from the e-mail, would likely not be infringement — it would either be fair use or the lawful use of facts rather than of creative expression,” he writes.
Volokh concludes that Sony is unlikely to prevail — “either by eventually winning in court, or by scaring off prospective publishers — especially against the well-counseled, relatively deep-pocketed, and insured media organizations that it’s threatening,” he writes. “Maybe the law ought to be otherwise (or maybe not). But in any event this is my sense of the precedents as they actually are.”
This is actually the second time this month I’ve received threatening missives from entities representing Sony Pictures. On Dec. 5, I got an email from a company called Entura, which requested that I remove a link from my story that the firm said “allowed for the transmission and/or downloading of the Stolen Files.” That link was in fact not even a Sony document; it was a derivative work — a lengthy text file listing the directory tree of all the files stolen and leaked (at the time) from SPE. Needless to say, I did not remove that link or file.
Here is the full letter from SPE’s lawyers (PDF).




Aside from the right to publish, is there an ethical obligation among publications to not publish Sony details not in the public interest?
Public interest != Sony’s interest
I agree with the positioning of the “ethical line” as referenced in the article – if this leak were reported on to the extent that it was publishing personal information to the detriment of individuals and with no journalistic value, that would be dubious. But what Sony is demanding is well beyond that and should be treated with the same contempt with which it was sent.
That said, I am not the journalist on the receiving end of the legal threat, so I’m really in not position to comment. Kudos to Krebs for standing firm though.
I don’t know why Brian does what he does, but I am glad he does it! Merry Christmas Brian! May the coming year be fruitful and blessed. Reading your book page 80 “41,000 active Interned pharmacies, … only 200 are approved and legit”
your friend – Michael
Just to add a counterbalancing opinion:
http://deadline.com/2014/12/aaron-sorkin-sony-hacking-yellow-journalism-op-ed-1201325117/
I’m not sure how I feel about this one yet. Is it really that everything points to the North Koreans?
I have my own doubts – it smells more like an inside job to me, as the amount of stuff that they got suggests that they had some ideas where they ought to be looking. In addition to everything else, I would make sure to look at former IT people who might have gotten laid off and who would have the intimate knowledge of how things are laid out and who might have even added a secret backdoor disguised as malware.
And while the North Koreans might be quite annoyed with Sony over that film that is coming out, that angle to the story might just be a smokescreen – if I were in the business of distributing malware I would make sure that I added some red herrings to try and sidetrack the investigation.
I suppose we might get a more official report in the future, but I am guessing Sony will want to keep that quiet as well.
I totally agree with you.
According to GRC.com Sony’s own servers are or were providing the seeds for the torrents of their own data.
https://www.grc.com/sn/sn-485.txt
Sony better hope to God there is not a encrypted payload in “Fury” or another unreleased movie that is in distribution to our local theaters.
Can you imagine 30 minutes into the movie and the screen goes black? Or is Sony smart enough to have the masters stored on hard drives locked in a vault that are not networked?
This is good food for thought. Thank you for the link.
I certainly agree with Sorkin’s view that media reports that focus on the juicy gossip are done for money. His line, “No one’s private life can totally withstand public scrutiny.” is mostly accurate.
That said, I would classify Krebs’ work as being informative and not an attempt to engage the reader at a level of gossip.
Thanks, Mike. Yeah, it’s a big part of the reason why I’ve only written one story about the Sony breach details. Lots of opportunities to feast on the stolen data, but I generally reserve that appetite for cybercrooks 🙂
Whoever did the hack has a prankster sense of humor. Definitely not the North Koreans.
I agree with that.
probably the same gamers that are always hacking them.
Theres nothing sony could do to stop something like this. And unfortunately these kids are hacking everyone. I feel like i’m a reality tv show sometimes.
I’m sure sony is the reason alot of torrent sites just went down, like the piratebay that was just raided and probably gone for good.
Some responses to the Sorkin editorial are found in this BBC article: http://www.bbc.com/news/blogs-echochambers-30488236
You were nice enough not to tell the Sony lawyers to eat blevit. I think they should for letting Sony allow these breaches.
Wondering if this might influence Sony going forward with the film adaptation of Spam Nation. More because the subject is now a sore spot for them rather than your not agreeing to abide by their letter. If it goes into turnaround, you know where to find me.
“…this reporter…” — Krebs
Why do you use third person? It makes you sound like a 50’s gossip columnist.
Maybe he’s a frequent TVTroper and referring-to-self-in-third-person just stuck.
Leave him alone. That is proper English usage for separating his reporting from his opinion.
Though I respect his opinion, I’m only interested in his reporting.
If Brian received formal university training, and the instructors didn’t teach the “New Journalism” style – i.e. the more personable Wolfe/Capote/Truman/S. Thompson narrative style starting in the 60’s and 70’s – then he would’ve been exposed to referring to himself in the 3rd person, if not outright taught to do so. Or maybe he got it from his stint at the Washington Post. He can clarify for us.
I, too, was exposed to that in the few journalism courses I had back in the late 80s/early 90s (never actually practiced it professionally, but I did get academic exposure to it). It’s not necessarily an affectation to refer to yourself in the 3rd person; it could be the result of schooling or professional exposure.
I’m sorry if you think it sounds pretentious or like an affectation, but it’s fairly common journalistic style for reporters to refer to themselves in the third person. e.g., see:
http://en.wikipedia.org/wiki/News_style
“While straight news stories always stay in third person point of view, it’s not uncommon for a feature article to slip into first person. The journalist will often detail his or her interactions with interview subjects, making the piece more personal.”
It comes from a standard long held in journalism schools (not that I went to J-school, mind you, but working 14 years at WaPo rubs off on you) that reporters don’t use first person, and they keep themselves out of the story. It’s also another way of avoiding the repetitive use of “I” and “me” in stories.
> It’s also another way of avoiding the repetitive use of “I” and “me” in stories.
That argument doesn’t make sense at all; if you use “this reporter” instead of “I” and “me”, that would be even MORE repetitive and distracting. The real key is minimizing references to oneself in the article.
(That said, I have no problem with the 3rd person reporting style. I’m just pointing out that if frequently using “I” and “me” would be repetitive, then so would frequently using “this reporter”.)
Hey – here’s an idea Sony: you don’t want your your crap spread all over the Internet, pay for a corporate security team, and teach your employees not to be dumbasses and fall for phishing emails. Until then, STFU.
I think SONY *had* to send the letter as evidence that they are trying to contain the spread of the leaked information.This could be part of a defense when they are sued by their employees and others.
^ what stephen said. Imagine you’re an employee of Sony.
Yup. Its actually a pretty polite letter considering the circumstances and I take it as just covering bases/asses.
Hey Sony, is this true?
Absolute Sownage
A concise history of recent Sony hacks
http://attrition.org/security/rant/sony_aka_sownage.html
Sony’s been struggling for a long time & this is just the icing on the cake.
If you can’t function as a productive entity, start trying to blame & control any criticism to divert the lack of good management.
Just the same old blame game to avoid responsiblity.
Good luck, Sony! You used to be a great company with great products, & here’s wishing you can regain your past splendour.
But not this way.
Reporting on the developments…fair game. Republishing the stolen files…Big no-no. However, Sony has demonstrated just how naive are our IT organizations; how disconnected the business is from IT (generally assuming that IT has got it covered); and how poorly we protect our networks, systems, and data.
Brian- Keep up the good work. Hang in there.
(As perhaps said by/about Mark Twain) – “Never pick a fight with people who buy ink by the barrel.”
I have seen that quotation attributed to Lyndon Johnson. Regardless, it’s a great one!
Although, when I worked IT for a small city newspaper, they had ink delivered by tanker truck.
Brian – you were the victim of a form letter from a source that could (or would) only identify you as a member of the Fifth Estate without any qualification. Reporting the theft, the how, the what, the who, the when, and maybe the why is journalism and protected by the First Amendment. There is a reason it is the first.
Too many “journalists” would write “Here is what was stolen, watch the movie!” Sony has an obligation to mitigate damages. Digital copies of protected information are still protected property of the lawful owner. Think of “possession of stolen property” as a crime.
There may be a question about that tree and file names as a “derivative work”. The United States Copyright Act (17USC§101) says “A “derivative work” is a work based upon one or more preexisting works, such as a translation, musical arrangement, dramatization, fictionalization, motion picture version, sound recording, art reproduction, abridgment, condensation, or any other form in which a work may be recast, transformed, or adapted. A work consisting of editorial revisions, annotations, elaborations, or other modifications which, as a whole, represent an original work of authorship, is a “derivative work”. (thanks to http://en.wikipedia.org/wiki/Derivative_work and send them $3)
A list or a representation of an existing tree-structured directory had nothing added to the work. No translation, condensation, editorial revisions, annotations, etc. Basically a reiterated list lacks “modifications” and is a representation of the original work (all or in part) as a whole. As such, it may not be a derivative work. The easy way around this is to generalize the content such as “HR Files including benefits, 401k files, 5500 filings, ACS, Q&A, recruiting, and retirees.” That condenses (one of the operations making for a derivative work) the first 2,000+ lines of 38,746 lines including 4,864 directories, and 33,880 files.
We’d be spared from wondering … what is Jocelyn’s Project?
Jonathan @nc3mobi
YMMV. I am not a lawyer. I don’t play one on TV. I’m just an IP holder who has been down this road (copyright infringement) before.
Brian’s use of the phrase “this reporter” is completely accurate, and the way a person uses written English depends entirely on what decade they attended college. I was taught that the story I was writing didn’t belong to me, unless it was a fictional or biographical first-person narrative.
Upstanding work, Krebs. Thanks.
Got your book – “highly recommended!”, as Jerry Pournelle used to say.
Regarding the lawyer letter: “Plus ça change, plus c’est la même chose.”
Stay strong.
BTW, did Sony ever apologize / compensate the world for the rootkit BS they perpetrated on their music CDs? Ref: http://en.wikipedia.org/wiki/Sony_BMG_copy_protection_rootkit_scandal
They’re corporate bullies, plain and simple. Godspeed, Mr. Krebs!
The letter sounds like a standard legal ploy of asking for everything regardless of what is legally required. Its more about intimidation than any legal issue. Some reasonable restraint as your UCLA adviser made is a good balance between the competing interests.
90% of recipients of such a letter would probably soil their drawers. The US legal system today is such a mess of BS that just the mere threat probably gets a lot of people to do what they want, and if they pressed it another 90% of victims wouldn’t’ be able to afford to defend themselves.
The movie about you was thru Sony pictures wasn’t it? Any leaked emails about it or about diva security reporters wanting only red M&Ms or Lagunitas in his trailer?
Sony here is some sage free advice: instead of trying to close the barn door once it has been flung open and all the animals scattered to the wind – secure the barn door to begin with.
I think I found where the stolen data is being stored.
https://www.youtube.com/watch?v=vJd-lG8D8yY
Brian, I subscribe to your website because of your style and tone of words. You report the facts and facts are what I’m looking for. It is a plus for your character that you will not give in to Sony and what I consider to be their scare tactics. Keep on keeping on and don’t change anything.
Anybody want in on a pool to guess how long it will take for http://www.bsfllp.com to get DDoS’d off the ‘net, for the partners and their families to get doxed or ???
When you think lawyering up can help contain something like this, you’re too old to be in charge. The feds couldn’t stop the Snowden leaks and doing something like this not only won’t help Sony but probably will hurt them even more. All they’re doing is drawing a Target on their backs.
Quinn, well said. My home used to be full of Sony products but no more. Very sad.
YOU HAVE A RIGHT TO KEEP THINGS PRIVATE & CONFIDENTIAL
…but…
If you don’t protect that information and it becomes public then you have failed and no amount of trying will ever put the genie back in the bottle! SONY got hacked, the hackers committed a crime but not anyone else once it was released.
I FEEL FOR SONY, im sure they will try to do better next time.
People never seem to understand certain things about the way the internet works. Email is NOT private and there is nothing about the cloud that is either. Sure, you can attach a password to things but if that does anything at all; it’s an “on the surface” measure that will only go so-far. It’s no different with the so-called privacy/security settings of certain social-networking websites.
Too many people and too many companies have a rather naive view of the web. Hackers have always been a big part of it. Without them, none of this tech would even exist. I cannot condone state-sponsored espionage/hacking/online warfare but when you are running a global company, you cannot be so careless/flippant with how you do things. Especially when your a company that steps on so many peoples’ toes for so many years (ISP’s are on this map too).
If we can not share anything, so just close the whole internet. 😛
Sony has stuffed up YET AGAIN, and they think that censorship is now their friend? Presumably this is the same company that said it would not bow to North Korean pressure about some movie, and is now trying the same kind of pressure on journalists who care to point out how poor Sony’s security is?
Surely Sony should try to stop this data at the source; its own servers! They are where the leaked data is coming from.
Of course, I have not knowingly bought anything from Sony since the company shipped a CD containing a rootkit. That pretty much confirmed the company’s attitude towards its own consumers, and it hasn’t improved since then.
Keep it up, Brian! This is the worst “closing the barn doors after the horses escape” I’ve ever seen. Do they think any reputable media will honor this request. I hope eveyone takes your position on this.
Its a weird boundary, all this stolen data.
From Wikileaks to the Snowden files, from Sony to “the fappening”.
I think reporting on what was taken and how it was taken is perfectly legit. (like Brian does)
On a personal level, you wonder, should I look?
I guess that’s where personal moral boundaries come out.
But when someone sends a letter telling you “can’t” do something, the rebel in you wants to look even more.
Judging from various news stories, the Sony data leak included some personal and sensitive gossip-worthy information about well-known people who sometimes work with Sony. I bet this threatening letter is Sony’s attempt to mollify them.
Can you imagine the publicity if Sony actually haled Mr. Krebs, or some television news company, into court?
Mr. Krebs’s attorney: Whose responsibility was it to secure your network?
Sony exec: ummm.
Mr. Krebs’s attorney: Did anybody in your organization use their computer to play a Sony / BMG CD product in the period from 2005-2007?
Sony exec: Yes, obviously.
Mr. Krebs’s attorney: Can you prove that you have expunged from your network all copies of the well-know rootkit your company distributed on its CD product in that era?
Sony exec: Ummm.
While it is all very amusing to poke fun (rightly so) at Sony, I can’t see many people here being quite so happy if it were their personal emails being splashed all over the news media outlets.
Sony should absolutely have their feet held to the fire over their poor security, but news media outlets publishing personal emails that were never intended for public viewing just seems wrong. It’s the kind of trashy and lazy journalism that seems to have become normalized in this country now. What possible benefit accrues by the public airing of this stolen, private information?
Be careful in your response, as the next victim could well be you.
“What possible benefit accrues by the public airing of this stolen, private information?”
Well, one could hope against all hope, because it’s happend hundreds of times, but maybe, just MAYBE, c-level knuckle draggers will finally take IT Security seriously and do what is right for once and protect the data you’re whining about.