Several media outlets are reporting that authorities in the United Kingdom early this morning arrested an 18-year-old in connection with the denial-of-service attacks on Sony Playstation and Microsoft Xbox systems over Christmas. The arrest is one of several tied to a joint U.K. and U.S. law enforcement investigation into a group calling itself the “Lizard Squad,” and comes as the group’s attack-for-hire online service was completely compromised and leaked to investigators.
A BBC story does not name the individual, saying only that the youth was arrested at an address in Southport, near Liverpool, and that he was accused of unauthorized access to computer material and knowingly providing false information to law enforcement agencies in the United States. The notice about the arrest on the Web site of the Southeast Regional Organized Crime Unit states that this individual has been actively involved in several “swatting” incidents — phoning in fake hostage situations or bomb threats to prompt a police raid at a targeted address.
U.K. police declined to publicly name the individual arrested. But according to the Daily Mail, the youth is one Jordan Lee-Bevan. Known online variously as “Jordie,” “EvilJordie” and “GDKJordie,” the young man frequently adopts the persona of an African American gang member from Chicago, as evidenced in this (extremely explicit) interview he and other Lizard Squad members gave late last year. Jordie’s Twitter account also speaks volumes, although it hasn’t been saying much for the past 13 hours.
Update: Added link to Daily Mail story identifying Jordie as Lee-Bevan.
Original post:
An individual using variations on the “Jordie” nickname was named in this FBI criminal complaint (PDF) from Sept. 2014 as one of three from the U.K. suspected in a string of swatting attacks and bomb threats to schools and universities across the United States in the past year. According to that affidavit, Jordie was a member of a group of males aged 16-18 who called themselves the “ISISGang.”
In one of their most appalling stunts from September 2014, Jordie and his ISIS pals allegedly phoned in a threat to Sandy Hook Elementary — the site of the 2012 school massacre in Newtown, Ct. in which 20 kids and 6 adults were gunned down. According to investigators, the group told the school they were coming to the building with an assault rifle to “kill all your asses.”
In an unrelated development, not long after this publication broke the news that the Lizard Squad’s attack infrastructure is built on a network of thousands of hacked home Internet routers, someone hacked LizardStresser[dot]su, the Web site the group uses to coordinate attacks and sell subscriptions to its attacks-for-hire service. As I noted in a previous story, the attacks on Microsoft and Sony were merely meant to be commercials for this very “stresser” (a.k.a. “booter”) service, which allows paying customers to knock any Web site or individual offline for a small fee.
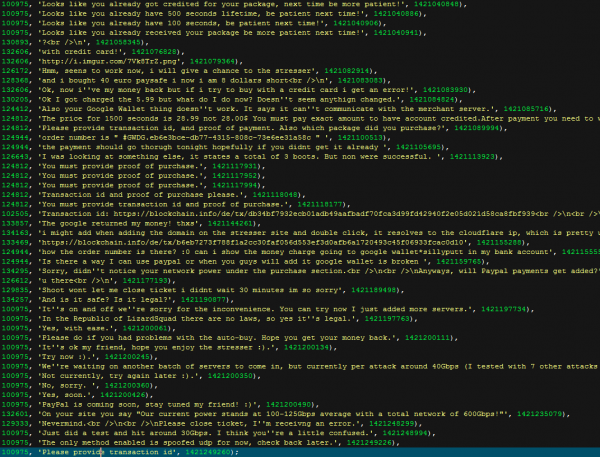
A copy of the LizardStresser customer database obtained by KrebsOnSecurity shows that it attracted more than 14,241 registered users, but only a few hundred appear to have funded accounts at the service. Interestingly, all registered usernames and passwords were stored in plain text. Also, the database indicates that customers of the service deposited more than USD $11,000 worth of bitcoins to pay for attacks on thousands of Internet addresses and Web sites (including this one).
Two other Lizard Squad members also have been rounded up by police since the initial Christmas Day attacks. In late December, U.K. police arrested 22-year-old Vincent “Vinnie” Omari, in connection with the investigation. Additionally, authorities in Finland questioned a 17-year-old named Julius “Ryan/Zeekill” Kivimäki, after he and Omari gave an interview to Sky News about the attacks. Sources say Kivimäki has been arrested and jailed several times in Finland on charges related to credit card theft, although he is currently not in custody.
Sources say the 18-year-old arrested this morning operates only on the fringes of the group responsible for the Christmas day attacks, and that the core members of the Lizard Squad remain at large.
Nevertheless, individuals involved in swatting need to face serious consequences for these potentially deadly stunts. Swatting attacks are not only extremely dangerous, they divert emergency responders away from actual emergencies, and cost taxpayers on average approximately $10,000 (according to the FBI).
In most states, the punishment for calling in a fake hostage situation or bomb threat is a fine and misdemeanor akin to filing a false police report. Having been the victim of a swatting attack myself, allow me to suggest an alternative approach: Treat all of those charged with the crime as an adult, and make the charge attempted murder.




Shows that these script kiddies are truly talentless.
I wouldn’t call them script kiddies. They put together a nice size botnet. That’s not a trivial thing to do at those levels.
Er no. But it’s not much more than trivial.
Pretty sure they used publicly available tools/source code to build their “botnet”, which makes them scriptkiddies.
I don’t know what sources they used but it reminds me of this project from 2012:
http://internetcensus2012.github.io/InternetCensus2012/paper.html
‘Mapping’ the internet using routers with default passwords
I wouldn’t call them a talentless . They are only 18 years old and yet they managed to knockout PSN and Xbox networks for two days .Not many people managed to do that .And yet they did it with little or no money .Bravo too thaad
And yet i would call (overpaid ) people in Sony and MS talentless they could not protect its networks from two 18 year old script kiddies , again it shows luck of basic security mechanisms on Sony and MS part. GUILTY ,GUILTY ,GUILTY .
What an ignorant comment. Spoken like someone who knows next to nothing about security or denial-of-service attacks.
This has nothing to do with sophistication. The sad truth is that there are millions of systems out there that are very easy to use in these attacks. The steps needed to execute massive DDoS attacks using just a few hundred systems at your disposal are all online, and not terribly difficult to execute.
Also, don’t forget, they chose to hit these gaming networks on the very day that they gained tens of millions of new customers, arguably their busiest day of the year. My guess is that these companies were more than prepared to handle tens of millions of new customers, but not tens of millions of bots.
I am by far no expert, but I also find it odd that people would consider deluging a system with requests some great feat. Really, you don’t have to know a thing about water flow or pressure, but any idiot can open a valve and flood a basement.
Though there are people who keep stating that a DDoS can be prevented, so far every thing that I have seen when researching is that there are methods that can make it more difficult, but none have said they can prevent it. It’s like you said, the systems can typically handle legitimate traffic. It’s the 10’s of millions of illegitimate requests on top of the legitimate traffic that brings them down.
Ultimately, I don’t think there will ever be a way to stop DDoS attacks since the key is that it is an onslaught of traffice created by an attack. They can take precautions to minimize the effect of the attack, but ultimately one would have to be able to prevent an attack. I liken it to retractable steel posts that prevent a car from being driven into a secure area. You can try and stop the vehicle from reaching it’s target, but the attack still occurs. Throw illegitimate traffic at the retractable posts, the posts pop up and the illegitimate vehicle gets stopped, but so does every legitimate vehicle behind waiting to get in. The very mechanism that identifies legitimate traffic is doing the same thing in a server, at a much larger scale with a massive amount of access points and a even a greater amount of traffic, legitimate and illegitimate.
Busted!
attempted murder and terrorist stalking.
By posting the information about the hacked home routers, this site put people onto the trail of the C&C network run by these miscreants. BK – you can take part of the credit on this one. Lets hope they find the rest of these kids and put a dent in the ”DDoS for hire’ market.
I thought we were to believe North Korea was behind the attack….oh wait, that was the OTHER Sony hack, right?
That one that happened the week before Christmas, right?
And this one happened on Christmas…
…oh, for the good ole days when there was only one major hack to consider…
About time!
So has this info been forwarded to the victims of the “lizard stresser?” Just think that would be a good idea so that the owners of these sites can proceed with legal action.
Brian, great reporting I love that you include actual screen shots with the facts!!!
Typical start-up company. Fancy advertising and crappy customer service.
You said on your twitter, that the database was “leaked”, where is it “leaked” at?
Were I a miscreant, I would be tempted to hire their service for a DDOS attack on LizardStresser[dot]su.
But that would be wrong :-). Putting them in jail is much better.
Awesome! Catch all the other lil’ lizards and we will be doing good! Thanks for the story Brian!
“Interestingly, all registered usernames and passwords were stored in plain text.”
Weren’t these bozos trying to pass themselves off to the media as “security analysts” or somesuch? Hah!
“security anal lists”
Brian,
Lizard Squad has claimed to have been involved with not only the DDoS attacks against Sony, but also the major breach against Sony (which the FBI blames on North Korea.)
Ars-Technica, at least, gives this claim some credence. Do you find this credible? If so, would this indicate that the group contains at least one competent member, and not just script-kiddies?
The group contains one faux-competent member, Ryan/Zeekill. Basically, this guy somehow befriends more intelligent hackers and hacking groups and then uses knowledge gained from them to sound cool.
Not a real threat.
are you going to post the download link to the database starfall? :^)
Putting one’s self at risk of becoming Bubba’s new girlfriend for a lousy $11k seems a bit braindead to me.
I enjoy Brian’s articles; he often ends with a strong and clear statement to put things in perspective. This one makes me think of people who similarly waste or divert resources (if they even realize what they’re doing) with attention-seeking or forcing responses on themselves, with the additional potential for tragedy both to the authorities who must respond, and in not being able to heal through repayment. I hope these kids learn, repay, and refocus.
Learn? Hahaha.. some of these losers (Jord, Ryan/Zeekill) have been active in the script-kiddie scene for 3+ years. They will NEVER learn and they will especially never repay, unless you mean “take more of your money and time” when you say repay.
They need to be locked up, plain and simple.
I believe this unlucky kid has been the victim of a failed dox… UK law enforcement have already confirmed he has no affiliation with Lizard Squad.
Hey BK, I haven’t posted since the initial attacks, but you’ll remember me from my long winded comments and explanations. I was posting at Tim, but I noticed that there is another Tim running around, so I’ll go with Tim C now lol! Anyway, I seem to recall my first comment stating that the biggest vulnerability with DDoS attacks the over abundance of upstream bandwidth provided to unwitting victims (like my 70 year old mother). My point was soundly refuted by a bunch of individuals claiming that these attacks do not originate from home users but from business networks. I’m smiling now. :))
“…allow me to suggest an alternative approach: Treat all of those charged with the crime as an adult, and make the charge attempted murder.”
Given the well-documented and literally murderous consequences of many misdirected SWAT raids, I second, third and fourth your motion. I would also so charge the gung-ho SWAT commanders who fall for the swatters’ nefarious “leads.”
SWAT is a pretty bad thing, but being aware of it and making your police dept. aware of it really makes it much less lethal. I entirely agree with the attempted murder charge for SWATing, but if we aren’t aware of how to defend ourselves, we just end up wasting time on frivolous suits and having things seized from us without reason. Then the objective turns from safety to revenge, and nothing turns out as planned.
Really, before we start charging the people doing this, we need to have a concerted effort to make police and potential victims aware of it.
Yes. Social Psychologists call it Herd Mentality – and it can run rampant even among the most highly educated. We need to struggle to be reasonable here, folks. Think about the results that a threat yields. Then think about the results a kid with a gun yields (and not just what they showed you on the evening news – think about the real results).
They’re not even *approximately* the same.
Sounds like this kid might deserve exoneration on your blog a bit higher up than the update paragraph. The update makes him out to be a victim, not a villain.
I am laughning while reading the criminal complant.
What a bunch of idots
I am laughning while reading the criminal complant.
What a bunch of idots
Laughning idots?
Now I am confused about the 6:19 update, because I am not certain which is the most recent, and not certain whether the right individual has been arrested because the update is light on details. What is the latest, and have they indeed apprehended the “correct” person?
Also, I would not characterize these people using dismissives or terms that lead one to discount the seriousness of their criminal activity or the harm they do, for that is likely to permit more. These are not juvenile activities, as many might agree were they to be on the receiving end.
The Omari guy was outed in the Derp crap last year, why was he not taken then. His details were in pastebin and twitter last year included he exact address
Uh… No, Krebs.
Just because it’s happened to you this time doesn’t make it a more serious crime. It’s more serious than filing a false report, but it’s not attempted murder and there’s no valid reason to charge minors as adults. It should be given its own criminal definition and appropriate legal ranges.
Casualties happen during SWAT intervention. During a SWATting, the police doesn’t know that it is a fake call, they will act as it is real and they will use real guns (and force).
That’s why “attempted murder” is a possible way to see it.
Imho
@Pal – don’t forget that not everyone will sit idly by while someone kicks in their door. Some of these swat teams will do just that: come in through the front and back door, toss flashbangs, and generally make you feel like your home is being invaded (which, of course, it is). But someone who gets woken up in the middle of the night in the dark may not be thinking clearly and may very well treat anyone bursting into his home as an intruder, and shoot first and ask questions later. A situation like that is very real and could end up getting multiple people killed, including the person being swatted.
I propose that the intent of the police arriving to a scene is not to attempt murder (the intent to kill is not made prior to arriving); yet, the intent of the person initiating the call is unknown with various possible outcomes.
“Attempted” is what seems too strong of a word; murder is a possible outcome. Yet, his “involve[ment] in several swatting incidents” may very well increase a penalty.
Yet, after serveral similar incidents he hasn’t stopped.
Here’s the catch. Hacked home routers. And everyone has one. So the bad guys set someone up as the patsy. He was probably caught unaware. Just like the swat raids. But what was his connection?
The corralary also applies. He could be the puppy with the big eyes that everyone forgives, when he pees on the floor. They need some better results or information released to show probable cause for the raid, or egg everywhere.
I stopped using the router function of my v*ris*n FIOS box when I found they had backdoored my WPA2 password onto their online web database. But the box has to stay attached to get FIOS. How to disable the router part? What critical router functions can I shut down to stop it from being “usefully” hacked?
Right now, I have a subLAN behind the FIOS box with a tomato router/WPA2. Should be unhackable.
So… have the DDoS attacks gotten heavier or lighter?
Great job Brian, I’ve truly enjoyed these blog posts on Lizard Squad. You deserve cred for this one.
Attempted Murder? What are you implying about the good men and women on SWAT Teams?