Two different readers have written in this past week to complain about having their Starwood Preferred Guest loyalty accounts hijacked by scammers. The spike in fraud appears to be tied to a combination of password re-use and the release of a tool that automates the checking of account credentials at the Web site for the popular travel rewards program.
 The mass compromise of Starwood accounts began in earnest less than a week ago. That roughly coincides with a Starwoods-specific account-checking tool that was released for free on Leakforums[dot]org, an English-language forum dedicated to helping (mostly low-skilled) misfits monetize compromised credentials from various online services, particularly e-retailers, cloud-based services and points or rewards accounts.
The mass compromise of Starwood accounts began in earnest less than a week ago. That roughly coincides with a Starwoods-specific account-checking tool that was released for free on Leakforums[dot]org, an English-language forum dedicated to helping (mostly low-skilled) misfits monetize compromised credentials from various online services, particularly e-retailers, cloud-based services and points or rewards accounts.
The tool is little more than a bit of code that automates the checking of account credentials stolen from other data breaches, to see if the stolen credentials also work at Starwoods.com. These types of account checking tools work because — despite constant advice to the contrary — a fair number of Internet users will rely on the same email address (username) and password pair for accounts at multiple sites.
The release of the account checking tool caused numerous Leakforums denizens to run the tool against various username and password lists stolen in previous data breaches. In less than 24 hours after its release, there were more than a half dozen Leakforums members selling compromised accounts. One seller advertised a Starwood account with 70,000 points for sale at just $3, while accounts with about 40,000 points sold for $1.50.
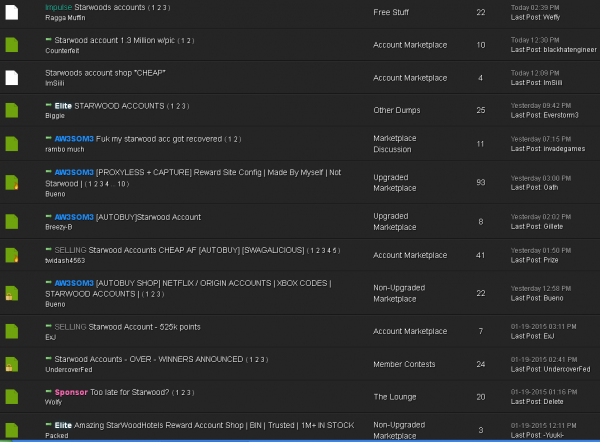
The release of an account checking tool for Starwood credentials has prompted dozens of miscreants to sell and cash out hijacked Starwood reward points.
According to a tutorial posted on the forum, hijacked account buyers “cash out” their purchases by creating new Starwood accounts and then forcing the hijacked account to transfer its account balance to the new account. The reward points are then exchanged for gift cards that can be used as cash.
Starwood does offer customers the option to receive email or text message alerts when account changes are made. But the tutorial on Leakforums encourages buyers to change the email address, password and other contact information on the victim’s account, effectively locking out the legitimate user.
Chris Holdren, senior vice president of global and digital at Starwood Preferred Guest, said the attacks of the past week track closely to the fraud patterns that have hit other loyalty programs in recent months, including Hilton Honors.
“They appear to be using credentials from elsewhere and seeing how many of those match up to Starwood accounts to see how many hits they can get,” Holdren said.
Holdren added that Starwood users who have had their accounts hijacked will not lose points due to fraud, a claim that was backed up by at least one of the two readers who initially contacted KrebsOnSecurity about being victimized by fraudsters.
“Not one guest is going to lose even a single Starwood point through this activity,” Holdren said. “We have a very large team globally mobilized to combat it.”
Could companies like Starwood be doing a lot more to facilitate safer login procedures, such as 2-step authentication? Absolutely. Even so, far too many people re-use the same passwords at multiple sites that hold either their credit card information or points that can easily be redeemed for cash.




Interesting article , a good soluton to this problem is to use invidual emal role accounts for each online ste. That role email role account is only used for that online site and no other one.
A better solution to this problem is to use an individual passphrase for each online site. That unique passphrase is only used for that online site and no other.
Or you can just change your password to base 64 encode and then use that which works real good for banking sites. Forget your long complex password, then just put the one you know in base 64 encode and their you go
+1 for that.
You could also use hash algorithms (example sha256, sha1, md5) as your password.
Of course, most people don’t know how to do that (or use password managers), so that’s why these problems happen.
Can you guys explain how to do either of these things for us normal people?
I use last pass and make passwords as long and with as many characters as a site allow me. I even try to copy and paste into programs. But I think my main problem is that I don’t change my passwords often enough. Especially the master, and there is just too many to remember on like what, I imagine some people have 100 diff passwords haha. I know I have at least a few dozen.
And just that having to have a master password is really the problem. I mean I guess the most safe guy is a guy who can remember a 100 character password by heart and change it every couple months haha.
I think lastpass just needs to automatically change passwords after a certain time period and prompt for master pw change. i couldn’t find that option in there?
Brian,
Do you have any idea how much the adaptation of two-step authentication might cost a small, medium, or large sized company?
Also, are there any studies that compare the success of different types of two-step authentication showing different rates of success? For example, physical security key vs. text message to a cell phone.
This is the kind of thing I would think might be better to have as a requirement in new legislation, versus sharing data and giving more money to law enforcement.
The expense of 2-factor authentication is trivial. It’s literally a penny or two per text message sent for authentication purposes.
Ok, so a possible solution would be to require it for all e-commerce sites. But then you have people that don’t know how to do that, so large retailers would have a huge advantage (over ma and pa internet).
The government could create a site that offers two-step authentication for every website in the world, but then you’d have anti-privacy people screaming about what they were doing with that information. (besides helping out ma and pa internet) Meaning we’d have to offer alternatives to the government service (much like we had to do with healthcare).
I guess my conclusion is that we are our own worst enemies. It seems like there’s an easy solution to this – require two step authentication. But then we complicate it with stupid politics and unrealistic expectations.
But texts aren’t a great form of 2FA. SMS is not especially secure. It’s better than nothing, but is it the single solution that should be mandated by legislation?
We’re talking about a hotel loyalty program – not a bank account. Who would EVER use MFA when buying groceries!? We’re being unrealistic. Need simpler, practical solutions.
But how much does it cost to implement 2FA?
We implemented 2fa for our VPN using Yubikeys. Cost us a few hours of labor and about $20US per user.
The cost of not having 2fa far outweighs the cost of adding it.
That cost is for the site. What about some users? I for one, don’t text. Don’t have it even enabled on my phone. It costs $0.15 when I did (and paid for lots spam) or somewhere around $20 a month for unlimited (IIRC). Considering I would not use it except for 2FA, that’s pricey by my standards. Yes, I do have a google voice account that can receive SMS, but that’s not really 2FA IMHO.
So why not just use Google Auth or Authy, almost everyone has a smart phone now a days, + it will stop people from jacking your Verizon, AT&T and forwarding Texts/etc, so they can get the code. Internet Hacks = solved.
I think one issue is two-factor for general consumer use is a relatively new thing, and it’s done in different ways by different vendors.
Standardizing on some best practices, or even better a sans.org standard or study would be interesting. Eventually we may need three factors; password, dongle and biometric. These days if someone wants to get you badly enough they probably can. For super-sensitive data keeping it off computers altogether may start becoming more common.
Eventually companies may try to lock-down their external networks as much as they do internally.
> Do you have any idea how much the adaptation of two-step authentication might cost a small, medium, or large sized company
Why yes — adding a supplemental choice for authentication via OAuth, and so adding OTP devices as well as a password credential (by using PayPal’s SecureID tokens) takes at most an afternoon
Perceived high price cannot ‘cut it’ as an excuse here, particularly relative to the higher cost of lost reputation and cleanup after a compromise
Call it bureaucracy, or whatever you want, but I don’t think most businesses do anything in an afternoon. I don’t doubt you can bang out a simple MFA implementation in dev in a few hours. But it is a long road to prod in most organizations. Furthermore, most orgs aren’t going to be interested in simple MFA. They are going to be worried about how it impacts customers. A risk-based solution that attempts to balance user experience and security takes more time to implement. However, if security is your only concern, there is always http://dilbert.com/strip/2007-11-16
The whole problem stems from the simplistic idea that authentication to access the website is equivalent to authorization for a monetary transaction.
If separate passwords or 2FA were used between these two very different trust levels, life on the Internet would be less prone to this nonsense. It really is the app designers and oauth api designers (or architects) failure to understand that difference by equating one front door access authentication to grant all permissions and authorize all activities.
We don’t need less passwords, we need more of them, for different activities. Essentially, a password is an access control point, and pretty much every website gives the customer/user only one ‘master key’ for everything in their account.
That’s what needs to change – the idea that authenticating to access the website is the same and equal to authorization to perform administrative or financial transactions on the account. That’s not the user’s fault for not wanting to remember separate unique hard to guess (and remember) passwords. That’s the website or apps failure to understand security.
“We don’t need less passwords, we need more of them” vs “That’s not the user’s fault for not wanting to remember separate unique hard to guess (and remember) passwords”
Yes, all other things being equal more (good) passwords would increase security. But all other things aren’t equal. Most users don’t want to bother.
I’m an SPG member. I stay at SPG hotels once or twice a year and have a trivial number of points. I just want to make a reservation. If you require me to enter multiple passwords just to make my hotel reservation, I’ll just re-use my throwaway password both times. If you force me to come up with new passwords, or use 2FA, I’ll probably get annoyed/go to a different hotel. *That’s* the cost they want to avoid.
Requiring multiple passwords will just lead to users using less secure passwords, or just adding something like a 1, 2, or 3 to the end of their password.
Great concept, not quite fit for end users though IMHO
As easy as it is to blame the vendors and developers for this sort of problem, at the end of the day, the biggest problem is the end-users. We struggle to get them to implement good security, because in every case — right up until the moment they are dealing with identity theft — 95% of end-users will rank convenience over security. Every. Single. Time.
Case in point: If the users in question were using a different password on each site, they would not have been affected by this particular incident. That solution costs $0.00 dollars, and with the relative ubiquity of password managers in browsers, would not rank too low on the convenience scale either, yet these users haven’t done it.
2FA, while easy enough to implement, is not the real issue. It is end-user priorities, and most businesses will not go out of the way to ignore those priorities unless they can make money doing so.
-ASB: http://XeeMe.com/AndrewBaker
Besides the password re-use issue, many travel web sites also have terrible security policies. For example, on united.com and various other airline sites you can log in using a 4-digit PIN (!), even if you have a real password on file. Besides giving access to loyalty points/miles, these sites may also expose sensitive data such as addresses and passport numbers (required for online check-in) …
I was shocked the other day when my wife and I went to Home Depot and wanted to link our purchase to her Home Depot Pro loyalty account.
“Just enter your social security number into the pinpad and it will match this sale to your account” said the nice lady at the register.
My SSN? Really? You’re retaining customer SSNs, after that whole hackathon that happened last year?
Instead of matching on my *&^%$#@! phone number, Home Depot is matching on my ENTIRE SSN?!?!?
We’re terminating participation in the Home Depot Pro. I was floored…
Add me to the list of victims. They stold 76k points this week. I was notified that my email address on the SPG account changed which prompted me to call them. They restored my points, but I’m worried about what else might be compromised.
What I have found is many of the account takeovers are occurring as a result of malware on the account holders machines that harvest their saved and stored passwords. I come across these massive lists of accounts collected by the miscreants, and there are tons of loyalty program credentials in these lists.
Alternatively, a miscreant can do similar damage with just a webmail password. Gmail search is highly efficient and bad guys can quickly spot your loyalty programs, accounts numbers, and reset passwords if necessary.
I also find it somewhat unfortunate that the media is quick to blame the loyalty programs as being “compromised” when that is clearly not always the case.
It should be noted that it is a good time for program operators to invest in user behavioral analysis tools. If companies are going to keep eating the bill for users who fail to protect their accounts then they will need advanced tools to detect and prevent fraudulent behavior. At the cost of false-positives and likely heavy $$$ for these advanced tools. (which will trickle back to the consumer)
Starwood is doing totally the wrong thing. “Not one guest is going to lose even a single Starwood point through this activity” means that not one ‘guest’ will learn how important it is not to re-use passwords.
The user has a little bit of inconvenience, but loses absolutely nothing of value. The company gets bad publicity AND is paying for the theft. And of course the thieves are laughing all the way to the bank.
At some point, one of these companies will have to take a stand and say “If you used a weak password, or used the same password on multiple sites, we refuse to pay for your mistakes”. That company will get a little bit of bad publicity until the next hack, when the next company says the same thing. Pretty soon, consumers would learn about online security. Or be broke.
You may be “correct” in some theoretical sense about what is the “right” thing to do from the standpoint of internet security as a whole. I don’t know how on earth you could claim that your proposal is right FOR STARWOOD. Pretty sure they are more interested in staying in business and prospering (which includes good customer relations more than almost anything else, particularly for their business model) than they are in making customers wrong for not being totally security conscious.
Well said, MW
I would add to what you’ve said by pointing out that they can take this opportunity to increase security awareness for their customers WITHOUT losing any of the benefits of good customer service.
Punishing customers — even those who are doing something dumb or undesirable — is not an effective way to stay in business, and will do very little to change customer behavior anyway.
-ASB: http://XeeMe.com/AndrewBaker
This is probably going to be disagreeable to some commenters but I would never use 2FA on a site like this.
There comes a point where convenience trumps security and there is just no way I am going to use 2FA on most things because of this.
I use it for banking and my primary webmail account, that’s it.
Users who want to defend against the mass probing of hacked credentials (which I think is a constant threat) cannot reuse passwords, of course. But even a simplistic approach of generating a unique password from common root that is appended with a site specific code (eg the first three characters of the domain as in “passwordSPG”) is sufficient to stop this purely automated attack. It may not be that good, but if a user won’t use a password tool to generate and track unique per site passwords it is better than nothing. Odds are nobody is going to reverse engineer a password algorithm if the testing fails…
great work Detective Krebs
Sure hope Steve Gibson gets SQRL out soon!
That would definitely help lol. Having dozens of different accounts and passwords that are logged and stored all over the place is definitely not good.
But its still just a “master password”, and no different then any other, but its all thats needed for every login. I for one hate having to manage dozens of different accounts, even with a password manager and having to remember to change them. That is the main difference imo.
But its still just as vulnerable to be stolen, but only when YOU get hacked, not the companies website, not some 3rd party passwd manager, not some server. And they will still have to bruteforce some very hard encryption that any Joe Schmoe will be able to use and that makes everyone safe.
I’d like to see more widespread use of Facebook and Google logins across commercial websites. The typical web user has accounts on many dozens of sites – managing that many passwords is impractical. Facebook and Google do much better jobs of managing credentials than most other companies, and theyare convenient too.