When Karim Rattani isn’t manning the till at the local Subway franchise in his adopted hometown of Cartersville, Ga., he’s usually tinkering with code. The 21-year-old Pakistani native is the lead programmer for two very different yet complementary online services: One lets people launch powerful attacks that can knock Web sites, businesses and other targets offline for hours at a time; the other is a Web hosting service designed to help companies weather such assaults.
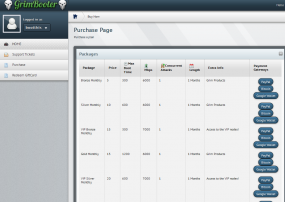
Rattani helps run two different “booter” or “stresser” services – grimbooter[dot]com, and restricted-stresser[dot]info. He also works on TheHosted[dot]me, a Web hosting firm marketed to Web sites looking for protection from the very attacks he helps to launch.
As part of an ongoing series on booter services, I reached out to Rattani via his Facebook account (which was replete with images linking to fake Youtube sites that foist malicious software disguised as Adobe’s Flash Player plugin). It turns out, the same Google Wallet is used to accept payment for all three services, and that wallet traced back to Rattani.
In a Facebook chat, Rattani claimed he doesn’t run the companies, but merely accepts Google Wallet payments for them and then wires the money (minus his cut) to a young man named Danial Rajput — his business partner back in Karachi. Rajput declined to be interviewed for this story.
The work that Rattani does for these booter services brings in roughly $2,500 a month — far more than he could ever hope to make in a month slinging sandwiches. Asked whether he sees a conflict of interest in his work, Rattani was ambivalent.
“It is kind of [a conflict], but if my friend won’t sell [the service], someone else will,” he said.
Rattani and his partner are among an increasing number of young men who sell legally murky DDoS-for-hire services. The proprietors of these services market them as purely for Web site administrators to “stress test” their sites to ensure they can handle high volumes of visitors.
But that argument is about as convincing as a prostitute trying to pass herself off as an escort. The owner of the attack services (the aforementioned Mr. Rajput) advertises them at hackforums[dot]net, an English language forum where tons of low-skilled hackers hang out and rent such attack services to prove their “skills” and toughness to others. Indeed, in his own first post on Hackforums in 2012, Rajput states that “my aim is to provide the best quality vps [virtual private server] for ddosing :P”.
Damon McCoy, an assistant professor of computer science at George Mason University, said the number of these DDoS-for-hire services has skyrocketed over the past two years. Nearly all of these services allow customers to pay for attacks using PayPal or Google Wallet, even though doing so violates the terms of service spelled out by those payment networks.
“The main reason they are becoming an increasing problem is that they are profitable,” McCoy said. “They are also easy to setup using leaked code for other booters, increasing demand from gamers and other customers, decreasing cost of attack infrastructure that can be amplified using common DDoS attacks. Also, it is relatively low-risk to operate a booter service when using rented attack servers instead of botnets.”
The booter services are proliferating thanks mainly to free services offered by CloudFlare, a content distribution network that offers gratis DDoS protection for virtually all of the booter services currently online. That includes the Lizardstresser, the attack service launched by the same Lizard Squad (a.k.a. Loser Squad) criminals whose assaults knocked the Microsoft Xbox and Sony Playstation networks offline on Christmas Day 2014.
The sad truth is that most booter services probably would not be able to remain in business without CloudFlare’s free service. That’s because outside of CloudFlare, real DDoS protection services are expensive, and just about the only thing booter service customers enjoy attacking more than Minecraft and online gaming sites are, well, other booter services.
For example, looking at the (now leaked) back-end database for the LizardStresser, we can see that TheHosted and its various properties were targeted for attacks repeatedly by one of the Loser Squad’s more prominent members.
The Web site crimeflare.com, which tracks abusive sites that hide behind CloudFlare, has cataloged more than 200 DDoS-for-hire sites using CloudFlare. For its part, CloudFlare’s owners have rather vehemently resisted the notion of blocking booter services from using the company’s services, saying that doing so would lead CloudFlare down a “slippery slope of censorship.”
As I observed in a previous story about booters, CloudFlare CEO Matthew Prince has noted that while Cloudflare will respond to legal process and subpoenas from law enforcement to take sites offline, “sometimes we have court orders that order us to not take sites down.” Indeed, one such example was CarderProfit, a Cloudflare-protected carding forum that turned out to be an elaborate sting operation set up by the FBI.
I suppose it’s encouraging that prior to CloudFlare, Prince was co-creator of Project Honey Pot, which bills itself as the largest open-source community dedicated to tracking online fraud and abuse. In hacking and computer terminology, a honeypot is a trap set to detect, deflect or otherwise counteract attempts at unauthorized use or abuse of information systems.
It may well turn out to be the case that federal investigators are allowing these myriad booter services to remain in operation so that they can gather copious evidence for future criminal prosecutions against their owners and users. In the meantime, however, it will continue to be possible to purchase powerful DDoS attacks with little more than a credit card or prepaid debit card.




This guy is involved in aiding and abetting. A FELONY! There is NO honor among liars ,thieves and murderers. You don’t talk to them nicely, you take them down and let the attorney work thru it. They are put on lists . if found again doing the samr thing . min. 30 years! Cay you say bye-bye…
depends on what you mean by “this guy.” The Pakistani script kiddy, yes, is a criminal. However, if you mean cloudflare, it’s not a viable accusation. Just because it CAN be used for criminal activity doesn’t mean it’s intended to. So as long as they respond to feds’ subpoenas, it’s a double-edged sword, but truth is, many legit sites would suffer too, if he were put behind bars. Besides, while booters are legally murky, hosting a ddos protection service is NOT; cloudflare is legal.
Kyle, nobody said CloudFlare was illegal. You seem to think that pointing out a major conflict of interest for such a big company paints every one of their customers with the same brush. I’m glad you get a benefit from them.
How many ways can describe such an appalling lack of ethical behavior? Here are a few to start with:
1. double-dealing
2. front and back office robbery
3. racketeering
4. getting taken coming-and-going
There are likely a host of others, but hopefully the FBI will be knocking on this guy’s door real soon with a RICO warrant, and give him a long look inside the US prison system if he hasn’t already grabbed the first flight out of Atlanta back to Pakistan.
The thing with CloudFlare is that it is not only booters/stressors and the odd carding forum that hide in the open there – spam, scams, phishing, knock-offs etc all can found there in great number.
Citing censorship is an easy cop-out at best and a shut-down at worst.
I use cloudflare for legal purposes because I simply cannot afford ddos protection from a more “elaborate” provider. Why should my site suffer from some erroneous federal initiative? If we prosecute people for the simple act of protecting a site which is what their service is for, we start to also prosecute whitehats and most of the people who are especially vehemently anti-fraud.
I use cloudflare and I am not involved in fraud or stress testing. Why should my site suffer because of some kid in Pakistan? When we start to draw the line into gray area, we make it okay to prosecute even whitehats, the same ones who advocate better safety and help catch these cybercrooks…
err woops that went through twice, sorry about that.
And, hosting stolen credit card data, as Brian has written about.
I believe Cloudflare will block websites if they’re actively hosting malware or phishing pages, even without a law enforcement request.
For anything advertising services, though, they simply let the legal system take its course, or wait for the hosting provider to take action on their own.
Maybe Cloudflare’s policies have changed but when I notified them about a bank phishing site in 2013 but they continued to pass traffic through to it.
Real interesting article , but adding to this story is that a lot of foreign spammer’s and phishing website also use Cloudfare which makes them very difficult to shut down.
“When Karim Rattani isn’t manning the till at the local Subway franchise in his adopted hometown of Cartersville, Ga., ” Cartersville, Georgia is north west of Atlanta , just west of I-75, the interstate that goes to Chattanooga. So here is a chance for all of the Krebs Heads in the area to meet a real live booter.
FBI my A$$
Oh fellow ar15.com members, may I ask a small favor? It seems a gentlemen in Georgia seems to have lost his way. I do believe he needs an introduction into a working value system. I’m not sure if I’m 30.8% convinced but I’m 22.3% convinced that reaching out to him from afar him will solve the problem.
Of course perhaps a more personal method, perhaps small group hands on session, might also be informative as to the American way.
I’ll return the favor when needed.
Live by the sword, die by the sword.
When you take the law into your own hands, you encourage others to do so as well.
Eventually someone will feel that something you’ve done is an affront worthy of a death sentence, at which point you’ll die by the very sword you advocate using.
Advocating the death penalty for computer crime offenses is insane.
Malsubjects run on greed and pride, ethics is not one of their best qualities!
Deceptively great article. Starts with an amateur nobody utilizing a strategy of extortion… then takes the logical steps to remind us of the big kid on the block who many would consider the ‘legitimate’ service that makes the serious money by basically doing the exact same thing but at a much larger scale and with a layer of abstraction.
And really, when it comes down to it… both seem to think “I just handle the money” is a good enough defense.
Keep up the good work.
I’m sure his friend back home sends Rattani 1099s so he can file quarterly income taxes on his online income…
Income tax evasion was enough to fell Capone, why can’t it be used to fell other miscreants?
Oh, that’s right, the House keeps cutting the IRS budget…
Love the “prostitute-escort” analogy. So apt. Good article, Brian!
Eh, maybe I’m just being too PC, but that analogy seemed a little outdated to me. Regardless, great work as usual!
This guy belongs in cuffs or a Blacksite.
I bet he makes a really crappy sandwich.
These guys remind me why water boarding needs to be kept safe and legal. It’s time to start using real punishments to deter these scumbags from their stoogery..
While we’re at it, let’s get out the thumb screws, the rack and any number of torture devices, because that attitude totally makes sense in 2015.
Why is this Pakistani still in this country? He should be deported on the next plane headed east. Unfortunately, that probably wouldn’t put him out of action….
New tagline for Subway: “Boot Fresh”
Full disclosure, I’ve been an HF member since 2008. I have also been reading your news site for 3 years now.
Now that that is out of the way, Brian, I feel the need to point out that while yes, HF does indeed have a large number of skids that really have no idea what they are doing, or has people there that feel as if they are blackhat just through visiting the site, there are people there that just want to help the userbase.
Of course I am one of these people. From what I have seen and heard through both the posts you make here as well as your talk at Black Hat, you talk quite a bit about HF and while I would say that you are correct about most of it, you are also incorrect about a small amount of it. There are quite a number of people there that go there specifically to help the users when their lack of knowledge comes to bite them in the ass, whether they get infected or end up completely making a mess of their Operating System, or simply asking for hardware advice, there are some knowledgeable people there. I myself have never purchased a single product from HF, nor do I ever plan to. Both of my upgrades have been purchased for me through other users (without my knowledge truth be told. I still don’t know who).
I feel the need to also say that the forum is vastly made up of the mid-teenage demographic and while most of them are indeed there to be a “hacker”, there are also a few that go there to learn. One could also make the argument that it is a pretty poor place to learn and while yeah, they could go elsewhere, at least they are trying to learn.
I am not really trying to say that there are a large number of users, let’s face it, there aren’t, however there are a few and those few help keep down the damage that the uninformed cause to themselves or others as much as possible :). I personally have done nothing but help users on that forum through helping secure their computers after an attack or even before an attack happens.
Just had to say something as I’ve seen you say it at least 10 times now how everyone on HF tries to act tough through purchasing booters or things like that. It’s just not true.
-Wafflemonger
P.S. I use the term attack lightly as “technically” someone trying to infect the with a RAT is an attack haha :P.
So CloudFlare is claiming that preventing “booter services” outbound content would a censorship ploy?
Why don’t they just prevent spoofed packets from leaving their network instead? That’s certainly not censorship – it’s just making sure their network doesn’t inject traffic trying to appear as being from someone elses’ network!
I may be sounding simplistic here, but if cloud providers did this one little change on their networks – and it’s not a hard change – just an ACL on their routers – it seems to me this would take the teeth out of NTP amplification being used by these “businessmen.” Wouldn’t it?
Generally speaking, the spoofed packets — if indeed the booter services are doing that at all — aren’t coming from CloudFlare. So there are two components to most booter services: The front end web site that customers use to purchase boot time and to order attacks, which is behind Cloudflare; and the back-end servers doing the attacking, which are sourced elsewhere and are not behind Cloudflare.
So why are you mad specifically at CloudFlare. Most, if not all, of these organizations have a Facebook page, Tumblr account, a Twitter account, and other web services. Just like those services follow a takedown process, so does CloudFlare.
If you are asking for more control on web content, make that argument, and make a clear case for how to do it effectively without hindering legitimate businesses. Otherwise, you’ll be writing the same blog post about thousands of web companies who interact with content.
Perhaps this cartoon image will give folks some idea of what’s happening:
http://www.crimeflare.com/gifs/kiddie.gif
By the way, the booter-stresser list at crimeflare.com linked in the above article is 18 months old. We don’t even try to keep that page up to date. The domain lists on another page (hundreds of thousands of domains at crimeflare.com/cfs.html) are kept current, but that’s also incomplete. It’s necessarily only a best-effort collection of domains that use CloudFlare, because CloudFlare doesn’t make this information available.
It’s none of our business, in CloudFlare’s opinion.
Any idea of a class-action lawsuit in the works for Cloudflare Inc being added to a Target Corporation / Home Depot / Sally Beauty/ P.F. Chang’s / Harbor Freight case?
I wonder how long long this guy will be working his other jobs now that he’s been outed. Brian why didn’t you out his other employer? Bad press for them. Subway may even be less than impressed with this guy’s potential – although that may be a harder termination to justify.
(BTW, I tried submitting this before and was informed I was trying to post comments too quickly.)
Ahh! The Wild West of the Web! Don’t you just love it? Seems ironic that they think DDOS attacks somehow represent “free speech”. I’d certainly think it was the exact opposite; but maybe I’m not reading into this correctly. :p
I kind of feel the same way about Pen Test training. I always thought that some of the people sitting in there with me may have actually been criminals in training.
Mr. Krebs, by adding the word Losersquad when you mention Lizardsquad, I wonder if you’re making a mistake.
A middle school principal wouldn’t give nicknames to a bunch of knuckle-headed seventh graders who conspired to vandalize the girls’ locker room. These guys are no different, except for their targets.
With respect, I don’t think they deserve the mindshare from you that giving them a nickname shows.
Wondered about that to, put it down to a case of poking the nest to see what comes out.
There is a lot of focus on cloudflare in the comments, however paypal and google wallets are equally disgraceful in their behaviour. There was a time when these payment accounts would get closed after being connected with such scammy actions. They do have good identity verification services and if all the scammers are blocked from mainstream payment, it would make buying such services harder.
Looks like the loser squad may have been up to something this week;
http://www.csoonline.com/article/2875080/cyber-attacks-espionage/malaysia-airlines-attacked-big-data-dump-threatened.html#tk.rss_news
Take the validity of the claim with a grain of salt. =\
Brian,
Normally you have a solid outlook but I don’t think you understand how this all works. CloudFlare is a reverse proxy that sits in front of websites, not in front of botnets, open resolvers, nth servers, or the other myriad of computers used to launch attacks. In no way does CloudFlare help these comanpies launch DDoS attacks. CloudFlare does help their websites become more easily accessible by having a global network, DFoS protection against the sites, etc. However, the same could be said about these sites appearing at a web host with a CDN, as. Facebook page, or on Tumblr. Those other services host plenty of similar content and also follow a takedown process as CloudFlare does.
If you want the attacks to stop, focus on the owners of computers, switches, routers, and other devices that launch the attacks. If you are worried about what content can live on the net, you should lobby Congress, or an international body like ICANN for stricter rules on takedowns, approvals, or whatever method you believe is best to screen out content on the web.
Focusing on one player instead of the problem does nothing more than point fingers. Please provide a solution rather than just a pointed compliant against on of the thousands of services that interacts with web content.
Also, please provide a secure way to make comments on your site. Why isn’t this form sent via https?
Dave,
I never said CF was helping launch these attacks. I understand perfectly well how their system works.
The point is that if CloudFlare did not offer the front end of these booter services (the web site) protection, most would go away because they would not be able to afford real ddos protection services, and because these booter services all attack one another all the time, so most of them would in essence ddos each other out of business.
Also, much like the kids named in the story, CloudFlare does sell ddos protection services, and it is a safe harbor for most of the ddos-for-hire services on the planet today. CF could easily acknowledge that this is an inherent conflict, and change its terms and say we won’t allow ddos-for-hire services, and then start taking them down one by one.
But the company’s CEO has said he is philosophically opposed to the idea. Its CEO has even taken to bashing me personally and very publicly over my stance on this on more than one occasion, saying I’m not a real journalist and things like that. I’m a huge believer in free speech, but ddos-for-hire services are all about stifling or silencing speech.
I think that distinction is lost in the article but that’s probably on purpose if they have been unkind to you.
While it’s true that these sites are on CloudFlare, they have a presence on other platforms that are just as hard to attack like Facebook, Twitter, and Tumblr. As the web matures, market forces dictate that a lot of these types of services will be rolled up into a few that will likely offer similar protection to CloudFlare and the above.
Isn’t DDoS for hire illegal? Perhaps it makes sense to get an agency like ICANN or Congress to form a type of complaint to ease takedowns, like DMCA for stolen content?
@Dave. Facebook, Twitter, Tumblr, et cetra (social networks) are not in the connection to hosted websites. Cloudflare is running nameservers for hosted websites, social networks don’t run nameservers for other maliciously hosted websites.
Having a social network presence doesn’t provide a Web platform for your “product”. If you want to provide a Web interface for your “customers” where they can browse your product, pick targets to attack and for how long, etc, then you need a front-end. That’s what Cloudlfare is protecting, which crosses the line from saying stupid stuff on the Internet to aiding and abetting criminal activity. You can say the same thing for PayPal and Google Wallet too.
Couldn’t they just list the 3 products they offer on their Facebook page with a link to their Bitcoin wallet? Why do you need a marketing site, and shopping cart software to make a simple transaction?
@Fireball & Dave. That’s not to say that merchant account systems (Paypal, Google Wallet, etc) aren’t a backend path of communications to the front-end of the malicious website (for payment processing).
Another way of saying this is: Social media (Twitter, etc) and merchant systems aren’t connected in the path to be able to change any configuration to instantaneously drop a malicious website off the internet, Cloudflare could shutoff that hosted path instantaneously (even if temporarily).
All the more reason to petition for an official ruling on takedowns for booters like the DMCA did for copyrighted materials. How many requests for removal of copyrighted material were acted on before the DMCA was enacted? If you want change, go for something lasting, not just after one company. you could just as easily make complaints to any other DNS provider. Stop the DNS and you’ll stop most traffic to the site.
@Dave Cloudflare is the only U.S. DNS service I’ve seen protecting carders and booters. That leaves no other U.S. DNS service companies of perhaps hundreds of thousands that are not protecting carders and booters.
There’s been testimony in U.S. House as recently as two days ago about non-carder, non-booter, malicious DNS service by Cloudflare.
I still stand by my comments suggesting that you get some legal action taken similar to DMCA for this type of content. Without a clear, legal definition of what’s malicious content, your argument is now that you disagree with CloudFlare’s terms of service. If you think that hosting any sort of web service for people who make claims to provide attacks for hire should be illegal, petition congress and make it happen. That will champion your cause with all present and future companies.
Rattani should know while living in the U.S. he can be arrested and charged whenever the authorities get around to him as a conspirator or co-conspirator as part of criminal conspiracy.
So what does this mean for someone who goes to that Subway and pays with credit or debit? I find it hard to believe that a person skilled as this one apparently is would not tinker with the POS terminal and perhaps pass his findings to others.
Proof of an exploit? I’ll leave that to others to decide. But most if not all Subways seem to use the same POS so this is basically putting their entire system at question. What access did he have? How can Subway be sure nothing happened? Do they even CARE? Most Subway franchises seem to operate willy nilly with no obvious input from Corp, and that’s assuming Corp would even take this sort of this seriously. We know many companies stick to that “we sell hammers” mantra and pretend nobody will bother them.
Speculation, of course. But I doubt I can stomach paying with plastic in any Subway again given the access this person surely has had. No way.
This won’t stop as long as companies like Ecatel (Netherlands, owned by Belorussian) and ColoCrossing (US) ‘semi officially’ (for CC; Ecatel even efficially) allow customers to send out NxGbit spoofed traffic to use open DNS/NTP/other UDP server as reflection method – No serious ISP would allow spoofed traffic to be sent out by his network. Well known for both of them, yet nobody seems able to stop them.
Do not understand how advocating the death penalty for computer crime offenses is insane.
Regardless of what one thinks of Cloudflare’s terms of service, it’s stupid to depend on a US-based company to protect your criminal enterprise. The feds probably spend so much time analyzing Cloudflare’s data that they’ve got their own assigned parking spaces out front. Letting criminals continue to operate for years while they build a case is no fun for the rest of us, but the fact is that that’s how federal investigations work. They let the criminals have enough rope to hang themselves with careless mistakes, knowing crimes continue to be committed against innocent people during that period.
Funny that the blame falls on a guy named “danial” (ahem… denial anyone)?