Not long ago, I was working on a speech and found myself trying to come up with a phrase that encapsulates the difference between organizations that really make cybersecurity a part of their culture and those that merely pay it lip service and do the bare minimum (think ‘15 pieces of flair‘). When the phrase “security maturity” came to mind, I thought for sure I’d conceived of an original idea and catchy phrase.
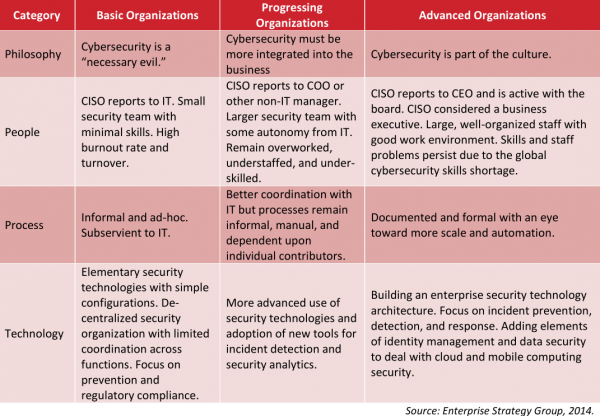
It turns out this is already a thing. And a really notable thing at that. The graphic below, produced last year by the Enterprise Strategy Group, does a nice job of explaining why some companies just don’t get it when it comes to taking effective measures to manage cyber risks and threats.
Very often, experience is the best teacher here: Data breaches have a funny way of forcing organizations — kicking and screaming — from one vertical column to another in the Security Maturity matrix. Much depends on whether the security professionals in the breached organization have a plan (ideally, in advance of the breach) and the clout for capitalizing on the brief post-breach executive attention on security to ask for changes and resources that can assist the organization in learning from its mistakes and growing.
But the Security Maturity matrix doesn’t just show how things are broken: It also provides a basic roadmap for organizations that wish to change that culture. Perhaps unsurprisingly, entities that are able to manage that transition typically have a leadership that is invested in and interested in making security a core priority. The real trick is engineering ways to influence the leadership, with or without the fleeting momentum offered by a breach.
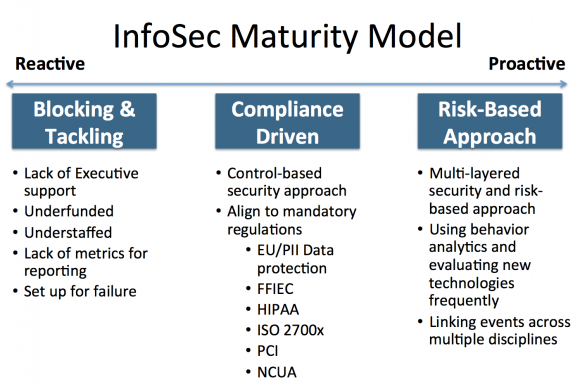
At last week’s RSA Security Conference in San Francisco, I had a chance to meet up with Demetrios “Laz” Lazarikos, the former chief information security officer at Sears. Now founder of the security consultancy blue-lava.net, Laz spends a great deal of time trying to impress upon his clients the need to take the security maturity model seriously. Here’s his sliding scale, which measures maturity in terms of preparedness and expectations.
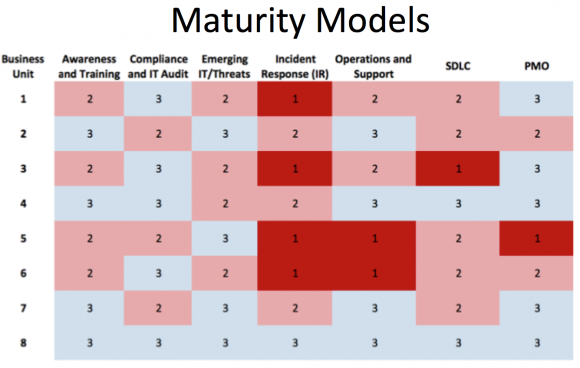
I like Laz’s models because they’re customized to every organization, breaking down each business unit into its own security maturity score. The abbreviations in the graphic below — SDLC and PMO — stand for “security development life cycle” and “project management office,” respectively. Dark red boxes (marked with a “1”) indicate areas where the organization’s business unit needs the most work.
Laz’s security maturity hierarchy includes five levels:
- Level 1 – Information Security processes are unorganized, and may be unstructured. Success is likely to depend on individual efforts and is not considered to be repeatable or scalable. This is because processes would not be sufficiently defined and documented to allow them to be replicated.
- Level 2 – Information Security efforts are at a repeatable level where basic project management techniques are established and successes can be repeated. This is due to processes being established, defined, and documented.
- Level 3 – Information Security efforts have greater attention to documentation, standardization, and maintenance support.
- Level 4 – At this level, an organization monitors and controls its own Information Security processes through data collection and analysis.
- Level 5 – This is an optimizing level where Information Security processes are constantly being improved through monitoring feedback from existing processes and introducing new processes to better serve the organization’s particular needs.
Where does your organization fit in these models? Are they a useful way for getting a handle on security and increasing maturity within your organization? Has your employer recently moved from one security maturity level to another? If so, tell us what you think prompted that shift? Sound off on these or any other thoughts on this subject in the comments below, please.




For CISA or CISM people, we highly reference the COBIT maturity levels.
For laughs though, we sometimes refer to this article in Wikipedia:
http://en.wikipedia.org/wiki/Capability_Immaturity_Model
This is great! Thanks for the link!
How about the Cyber Resilience Review (CRR) as a measure/assessment of an organization’s security program maturity?
This maturity model is like a shortened and sweetened version of the maturity analysis from ISACA’s RISK-IT -framework. The model would require more concrete steps for companies to understand the elements of the “advanced organization”. That is a topic for another article though.
I wrote my InfoSec MSc thesis on IA Maturity Modelling about 5 years ago. The models based on controls aligned with ISo27001 usually work best. The ones with 5 levels (6 if you include ‘no knowledge and doing nothing’) are the most effective. It all stems back to the quality work by Deming and the application of it to software development by Watts Humphry in the 80s . There are various models available from Gartner, ISF, ISACA and the UK government produced the Information Assurance Maturity Model which is publicly available. They all say much the same thing and each has good and bad points.
Good point. 5 level models seem to be a de facto standard and everything else is mostly suitable for coffetable conversation (or results in complicated mapping structures). Let’s not reinvent the wheel.
Great article. I’ve always been a fan of maturity models for security as they begin to offer a path, albeit a subjective one, to metrics and measurement. Please note the DOE, in consultation with industry SMEs, published and maintains 3 different versions of its Cybersecurity Capabilities Maturity Model (C2M2). Two are sector specific: for electricity and oil and gas, and the third is sector neutral. Word from utilities who’ve subjected themselves to this process has been very positive.
Link here: http://energy.gov/oe/services/cybersecurity/cybersecurity-capability-maturity-model-c2m2-program
One of the biggest issues I have seen in security, is the failure to simplify what is trying to be accomplished, by an organization. Generally people fail prey to overdramatized reporting on mainstream media, sales pitches to solutions that have no relevance to their organization etc.. While I agree 100% that a security maturity exercise is vital and governing framework as well, organizations need to understand what is most important to them and start with that. If you live in the path of a dangerous hurricane and you have minimal time to prepare you are going to do your best to take care of everything you can, however there are somethings that might take priority over others. The same should be for cyber security, laser focus on the most critical components of your organization is required.
For a regular business, like a store or a bank, this kind of thing is fine. For a software company, you need something different.
For the back office, sales automation, etc a software company is the same as any other company. When it comes to writing new software, you need to give a sandbox to developers to innovate without having security be a roadblock.
I’m not saying that production code should not have security baked in. Of course it should. Anything remotely considered for production must have the security implications thought through.
Take care not to over-complicate this: the “kicking and screaming” is the essence of the issue: It’s a sea-change in our manner of thinking: rather than simply consider “how can I make this work” I must consider “How will I keep this secure while I’m making it work?”
Secure Computing in a Compromised Environment
One might well look back and review the article published here on “SuperGet” — a “DarkNet” service specializing in providing personal identification data to anyone who want s to pay. such data includes everything commonly used to verify identification: name, date of birth, address, social security number, mother’s maiden name …
for securing business in this environment then and identification that can be verified in public control of which can be retained privately is required. Public Key Encryption provides this where no for of symmetric identification will work.
contrary to much published in “the media” — public key encryption is not difficult to use. the best current example people can work with is likely the ENIGMAIL plug-in for Thunderbird.
this “packages” the PGP or GnuPG software into a user-friendly dialog — no more difficult than much of what we do every day on Excel — and certainly easier than drawing charts 🙂
“Secure Computing in a Compromised Environment”
This is key. How can someone actually justify using Chrome or google docs when working with what is supposed to be ‘private’ and ‘confidential’ data when the world knows (or atleast should know) that google will be given access to this information over the web? But people ‘trust’ google. Google can do no wrong!
We all know (or atleast should know) that Flash and Java (among certain other things) have been compromised and yet companies insist on continuing to use these things internally and externally without a care in the world.
One of the best ways to NOT have a ton of customer information stolen from your servers is to NOT collect this kind of data in the first place. Certain things are important but there is no logical reason why every store out there needs my name and phone number.
I question the wisdom in the idea that restaurants need to have microphone/webcam Ipad type devices at each table when we all know (or atleast should know) how easy it is to intercept communications over WiFi (not counting the things these devices are designed to do in the first place.
If people actually cared that much about security, alot of things would be very different. Security is not going to be had via Microsoft/Apple updates.
While absolutely nothing can be absolutely secured, there needs to be a heightened sense of responsibility put to all things I.T. (unilaterally).
Quoting mike~acker.
“for securing business in this environment then and identification that can be verified in public control of which can be retained privately is required. Public Key Encryption provides this where no for of symmetric identification will work.”
The well-known cryptographer Peter Gutmann has been following public key cryptography (PKI aka X.509) as it is used in SSL/TLS VPNs. According to him, it is currently a huge mess. Many of the CA companies that issue PKI certificates do not vet the users properly, some of the CAs may be operating either maliciously or fraudulently. Google is storing hashes of its own PKI certificates to gmail, etc., in its Chrome browser to ensure that destination certificates received during SSL setup handshakes for its services are not substituted by a man-in-the-middle attack, which lots of countries do these days to their own citizens. Right now the whole global infrastructure for PKI/X.509 is essentially in shambles, thus making your assertion false.
Security CMM’s are very useful and have been used since about 2004 by most progressive organizations. While the models shown serve well to indicate to an org where their current CCM is, they do little to help the org understand where they should be. Some may say “just go for the top CMM level,” but that level is generally not affordable. This where Risk Analysis comes in. Your appetite for risk will point you to the level of maturity that is right for you. If you are fine with lots of risk, then a lower CMM might suffice and it would certainly be less expensive. If however, you determine that your appetite for risk is low and you take no action to address accordingly, then you are most certainly negligent and culpable for any resulting losses. Much more could be said on this topic (and I’m sure it will).
This approach basically describes feel-good security and does not offer any measure of performance. There must be quantitative evaluation. Cost is the only realistic metric, and whether money is being wasted. The costs of security can be measured and so can the likely costs of future breaches. From there, simple analytics can optimize security cost vs. vulnerability — which incidentally, turns out to be the optimum long-term profit for the organization. The focus, therefore, should be on good security as a profit center and not on compliance or feeling good. The standards do not measure performance, only compliance, nor do they necessarily validate sufficient security to avoid allegations of negligence when trouble comes. There must be quantitative validation of good and current security, which is neither difficult nor expensive and can serve to circumvent major future costs of time, money and reputation.
@ Brian, thanks for post – great to see you and congratulations on your continued success!
@Miles
Great feedback – I’ve used this model for technology companies (hardware and software). Let me know if you want to walk through or if you need additional information.
@Frank
Totally agree. This InfoSec model was the foundation for my work with risk-analysis and quantifying losses in dollars. It has been used for coaching InfoSec practitioners how to align with Business leaders’ terminology and language. ISACA recently sponsored a webinar about this topic – everything you’re mentioning starts on slide 40 if you want to review, would appreciate your insight and feedback. The link can be found here: http://goo.gl/CScHrR
This phenomenon is not just related to security. It permeates everything done by businesses–both large and small. I originally come from the accounting side, and when I was involved with it, the accounting function was ignored as much as it could be–just like security is. Most of the time, it seems to take an emergency to make the decision makers in the business aware of the importance of a function. You can see this on a national level as well. I think it is related to economics–there just isn’t enough money/budget to address everything 100%. I assume it will always be like that, but we could do a better job with our resources–depending upon the current “emergency”.
Regards,
Regards,
Don’t know if this is relly your thing Brian, but security at Educational k-12 ‘companies’ is a problem. Due to salary constraints (we’re in silicon valley), we rarely get the “A” level security employee or the latest and greatest software and policies. For example, we now have a systems manager/martinet who spends his time reading teacher streams and blocking websites and features we use, while my actual spam mail received has skyrocketed (and email servers have unrecoverable crashes.)
Maybe grist for a future study?
The question the CIO (or other C-suite leaders) pose is “Show me the state of our information security program and where we have to improve”. Given that meetings with the C-suite and BoD are typically limited and a lot of information has to be conveyed in a short amount of time, in 2009 we created a “Dashboard” concept through the design of a simple Visio drawing based on assessment of maturity leveraging COBIT, ISO27001, NIST and the CMMI. This methodology has been since practiced and enhanced over the last six years and now automated through a SaaS offering due to growing demands of enterprises clients.
There are critical actions CISO’s and other business leaders require to properly understand and manage an information security or privacy program. Our software automation was designed to accomplish these goals within a single platform leveraging technology and industry experience. The process is simplified to four key steps in the workflow.
1. Assess
2. Measure
3. Analyze
4. Improve
We have automated this methodology to help companies communicate and manage the maturity of their information security or privacy programs by department, group, business unit or subsidiary. Includes six pre-built reports with leadership in mind. Included in these reports is estimated one-time resource effort, estimated ongoing resource effort by month and estimated capital costs for improvements. Radar charts and a Dashboard (heat-map) resonates with the C-suite so they have a clear understanding of the investment required to enhance the information security program process areas and ensure people and capital is invested in areas to make the greatest impact.
The models in the article are “basic” and miss on specifics as commented by Miles Archer, Tim Ferrell, and Frank Platt. The charts don’t give any detail on how to fix the categories of problems, they note problem categories. I see this over and over, where the everchanging networked-security keeps being rehashed from networked security philosophies, never getting close to controlling the determined adversaries.
Were Target, Home Depot, Premera Blue Cross, et al (that were breached) at the “Advanced”/”Proactive” level prior to the breach, and after the breach (one day later) all the sudden at a less than advanced/proactive level, by the same model, rhetorical? A off-the-model, breach/not-breached category, outside-the-network adversary can change the level of an internal model instantaneously.
I would like to add two more models that have helped me at a State/Local government level:
The Community Cyber Security Maturity Model (CCSMM)http://cias.utsa.edu/the-ccsmm.html
&
The Cyber Security Assessment for Everyone (CySAFE)
http://www.michigan.gov/documents/cybersecurity/cysafe_flyer_SOM3_468548_7.pdf
The CCSMM is fairly academic, but does come with federal funding for deliverable courses to teach it.
The CySAFE is quick and easy (45 minutes to an hour), is based on time to implement control, cost to implement, and risk to business. Prioritizes results and is very useful.
Thanks for the article and comments, I’ve enjoyed them
Hey Brian, thanks for this blog post. I’ve long been a fan of the Carnegie Mellon Maturity Model, starting with my years at EDS, where we used it extensively to understand our capability, maturity and ability to deliver. I also used this approach when I was the CISO of Providence Health & Services. It was one that my board and senior leaders could really wrap their heads around. Gartner has a pretty good Security Maturity Model also, but you have to pay to get your hands on it.
When I moved to Core Security, I realized that there was no really coherent approach to vulnerability management other than scan+patch plus PCI as a framework. This clearly was not working just based on the number of breaches that involve systems with vulnerabilities known to exist and be exploitable. Working with some of the other smart folks at Core Security, I built a structure maturity model for Threat & Vulnerability Management that I believe will allow any organization to significantly reduce the risk of breach.
As noted by some other folks, a model without actionable details is very basic. Many of these models are just that, a description of each level and have no detail behind it on how to advance your organization, or why you should do so. So, I’m including links for a graphic of the model and also for folks to get my full white paper if they are interested in learning more, including specific actions to take to improve vulnerability management:
http://securitycigarsfud.com/2014/08/26/maturity-model-matures/maturitymodel/
http://www.coresecurity.com/white-papers/threat-and-vulnerability-management-maturity-model
“…there was no really coherent approach to vulnerability management other than scan+patch plus PCI as a framework. This clearly was not working just based on the number of breaches that involve systems with vulnerabilities known to exist and be exploitable.”
This is a big reason why it’s so important to have an in-house IT dept. and not have it outsourced (cloud or the Philippines or India or whatever). I’m sure you’ve heard something like this before though. That approach doesn’t work as you’ve stated. Neither does the installation of software on every computer in the building for someone to monitor what everyone is doing. It’s a very poor way to stop employees from going to certain websites. This could be done at the router level (proxy server). The problem with so many in-house IT departments are that they are not handled very well with inappropriate expectations while having too many of the wrong type of people within the ranks (yes-men kiss-ups, I wont work for less than $75 an hour, or just_update_your_system types). This usually starts with upper management.
Interesting. I delivered a talk on this very subject in early 2008 at Infosec World. I based my model on Carnegie-Mellon’s CMM, and used 4 levels. Simplified, they were:
Level 1: No real “program” to speak of, ad-hoc and purely tactical.
Level 2: Basic program in place, still primarily reactive in nature with little planning.
Level 3: Solid program with some strategic planning, good support from senior management. But gaps still exist.
Level 4: Highly optimized with feedback loops. Risk management is how business is done. Security is an enabler for the business and viewed as a key partner.
My key point was that immature organizations trying to tackle the more complex issues with large tool implementations, e.g. SIEM, were quite likely to fail because they just weren’t ready yet.
Disappointed to see the Enterprise Strategy Group outline maturity on who the CISO reports to.
I just posted an article which talks about the role of the CISO and how who they report to is about effectiveness and corporate culture and not about reporting to the CIO or CEO.
Read more here:
https://www.jayschulman.com/7-types-of-ciso/
Fascinating read with the linked article “JPMorgan Algorithm Knows You’re a Rogue Employee Before You Do – Bloomberg”
The one thing I can think is it will be a world run by machines as elders watching over people telling us “We know you better than you know you”. All to tell us with undeniable proof all those things that we already know but refuse to believe.
Looks like an application of the 30+ yr old CMMI Software Capability model. That’s a good thing and setting a goal of being level 3.5 is probably what most organizations should target.
Higher risk orgs should target 4+ and military and financial orgs NEED to be level 5.
The guys of The Open Group (known from TOGAF) came up with O-ISM3, Information Security Management Maturity Model.
More info: http://www.ism3.com/
It is compatible with many standards, and optimizes standards like the ISO27k.
At my first contract, I was lucky to work with an organization that had the full maturity model. I like the charts, they look like the real world to me. Some of the comments and links, show the real dregs of security as well; which is also unfortunately true!
Funny none of the sacred texts mention auditing from an independent third party, looking at all your dirty secrets on an annual schedule usually prompts management to take action and try and remain ahead of the problems.
ISO is nice and so is PCI but until you bring in a third party with NO agenda you will never really understand where you need to improve yourself.
There are plenty of companies that don’t make much of an effort. Can you name any that are at the top of their game?
Lockheed-Martin
There are companies doing good security. Not as many as we might hope, but there are. The hard part is to tell the ones doing good security from the ones who just haven’t been breached yet. Looking in from the outside makes that very difficult.
Generally speaking, the ones that haven’t been breached (yet):
http://datalossdb.org database of breaches
To everyone quoting your favorite maturity model: you are doing it wrong.
Infosec has had a relevance problem since forever, which is why nothing gets done. You can philosophize about risk management, threats, and maturity all day long and if it isn’t meaningful to the people who you are serving, it is without any merit and will provoke zero actions.
Use those soceng skills and figure out what is meaningful to the people you are trying to motivate to be successful. You’re the court mage. Figure out what kind of swords the king likes and make your liege a magical one of whatever is relevant. You don’t have to teach them magic, that’s why they pay you.
Being able to effectively implement /any/ maturity model controls is going good work if it is relevant and does something worthwhile. Most programs stall out because they come up with a huge prescriptive list of trash that no one likes, sec efforts are dismissed as more from Dr No, and it is ignored in favor of things people do understand; deals, code releases, and money.
Be relevant or perish.
>>it is ignored in favor of things people do understand; deals, code releases, and money.<<
On the whole, Ian, you make some exceedingly good points. It doesn't matter how noble ones goal is, if one does not get the ear of the people who need to facilitate that goal.
Yet, there is an aspect of Information Security that is quite ignored in the grand quest to make things relevant to the stakeholders. And that is this: If they only pay lip service to security, then they will jeopardize the things they allegedly understand — like revenue.
The onus is on the leaders of businesses to understand the risks to those businesses, just as much as it is incumbent upon the security practitioners to know how to communicate well with business leaders.
At the end of the day, cigarettes and greasy foods still kill, and that message is still true regardless of how poorly any single practitioner is in his or her delivery. It's not a secret any longer.
You can't blame your doctor for not pointing out that poor diet and a lack of exercise creates undue risk, and you can't blame your security practitioner because he didn't present a better ROSI for a necessary item of protection vs your expected revenue windfall from the delivery of your super widget.
We *may* see more businesses take security seriously if more businesses utterly go out of business for not doing so. With the prevalence of security incidents today, every org will get a chance to prove this theory soon enough.
Plenty of food for thought! +1 Ian & Andrew.
Getting back to Brian’s article, I like Laz’s approach of breaking down the assessment by business unit. IMHO, this could be a practical way of sharing with the C-level that Security is, indeed, everyone’s responsibility, and that it’s a business enabler. Likewise, BU-Heads reviewing that tactical report may become more proactive, and collaborative… Among others, companies serious with following an Enterprise Security Architecture would certainly rely on that type of report for their risk-based investment strategies as long as CISOs can tie the current/desired maturity level(s) to losses in $, reputation, etc.
@Laz, does your Model provide detailed attributes against which an assessment can be performed?
There seems to be two things missing from this discussion:
1. Risk analysis – what are the threats? their likelihood? the possible costs?
2. Design & Code quality. Are functions well defined & complete? Does Code implement them without bugs or logical holes?
As well as Security procedures, there needs to be Security-from-what plans and security needs to be baked into code, not added on.