mSpy, the makers of a dubious software-as-a-service product that claims to help more than two million people spy on the mobile devices of their kids and partners, appears to have been massively hacked. Last week, a huge trove of data apparently stolen from the company’s servers was posted on the Deep Web, exposing countless emails, text messages, payment and location data on an undetermined number of mSpy “users.”
mSpy has not responded to multiple requests for comment left for the company over the past five days. KrebsOnSecurity learned of the apparent breach from an anonymous source who shared a link to a Web page that is only reachable via Tor, a technology that helps users hide their true Internet address and allows users to host Web sites that are extremely difficult to get taken down.
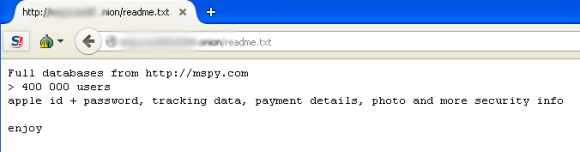
The Tor-based site hosts several hundred gigabytes worth of data taken from mobile devices running mSpy’s products, including some four million events logged by the software. The message left by the unknown hackers who’ve claimed responsibility for this intrusion suggests that the data dump includes information on more than 400,000 users, including Apple IDs and passwords, tracking data, and payment details on some 145,000 successful transactions.
The exact number of mSpy users compromised could not be confirmed, but one thing is clear: There is a crazy amount of personal and sensitive data in this cache, including photos, calendar data, corporate email threads, and very private conversations. Also included in the data dump are thousands of support request emails from people around the world who paid between $8.33 to as much as $799 for a variety of subscriptions to mSpy’s surveillance software.
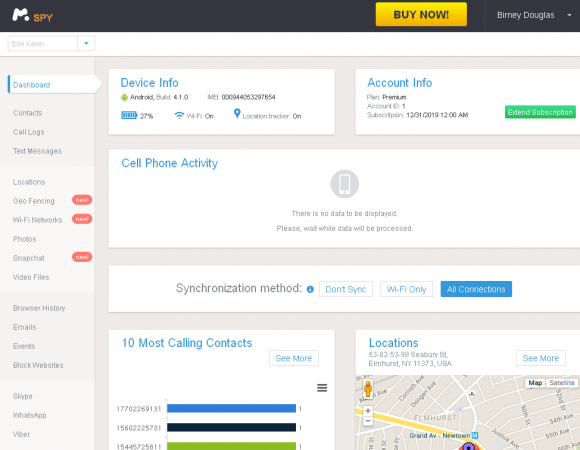
mSspy users can track the exact location of Android and iPhone users, snoop on apps like Snapchat and Skype, and keep a record of every word the user types.
It’s unclear exactly where mSpy is based; the company’s Web site suggests it has offices in the United States, Germany and the United Kingdom, although the firm does not appear to list an official physical address. However, according to historic Web site registration records, the company is tied to a now-defunct firm called MTechnology LTD out of the United Kingdom.
Documents obtained from Companies House, an official register of corporations in the U.K., indicate that the two founding members of the company are self-described programmers Aleksey Fedorchuk and Pavel Daletski. Those records (PDF) indicate that Daletski is a British citizen, and that Mr. Fedorchuk is from Russia. Neither of the men could be reached for comment.
Court documents (PDF) obtained from the U.S. District Court in Jacksonville, Fla. regarding a trademark dispute involving mSpy and Daletski state that mSpy has a U.S.-based address of 800 West El Camino Real, in Mountain View, Calif. Those same court documents indicate that Daletski is a director at a firm based in the Seychelles called Bitex Group LTD. Interestingly, that lawsuit was brought by Retina-X Studios, an mSpy competitor based in Jacksonville, Fla. that makes a product called MobileSpy.
U.S. regulators and law enforcers have taken a dim view of companies that offer mobile spyware services like mSpy. In September 2014, U.S. authorities arrested a 31-year-old Hammad Akbar, the CEO of a Lahore-based company that makes a spyware app called StealthGenie. The FBI noted that while the company advertised StealthGenie’s use for “monitoring employees and loved ones such as children,” the primary target audience was people who thought their partners were cheating. Akbar was charged with selling and advertising wiretapping equipment.
“Advertising and selling spyware technology is a criminal offense, and such conduct will be aggressively pursued by this office and our law enforcement partners,” U.S. Attorney Dana Boente said in a press release tied to Akbar’s indictment.
Akbar pleaded guilty to the charges in November 2014, and according to the Justice Department he is “the first-ever person to admit criminal activity in advertising and selling spyware that invades an unwitting victim’s confidential communications.”
Unlike Akbar’s StealthGenie and some other mobile spyware products, mSpy advertises that its product works even on non-jailbroken iPhones, giving users the ability to log the device holder’s contacts, call logs, text messages, browser history, events and notes.
“If you have opted to purchase mSpy Without Jailbreak, and you have the mobile user’s iCloud credentials, you will not need physical access to the device,” the company’s FAQ states. “However, there may be some instances where physical access may be necessary. If you purchase mSpy for a jailbroken iOS phone or tablet, you will need 5-15 minutes of physical access to the device for successful installation.”
A public relations pitch from mSpy to KrebsOnSecurity in March 2015 stated that approximately 40 percent of the company’s users are parents interested in keeping tabs on their kids. Assuming that is a true statement, it’s ironic that so many parents have now unwittingly exposed their kids to predators, bullies and other ne’er-do-wells thanks to this breach.




So sales of loperamide will be high amongst any celebs and the rich & powerful when the light dawns, wonder who will be on the list.
Such software shouldn’t exist in the first place.
The iptables firewall can track and log every connection made to or from any *nix computer on which it is installed. Should that software not exist?
Your argumentation is completely stupid and retarded. Nothing else.
LOL………1’s and 0’s
Perhaps netstat should not exist either? Perhaps this is why the command prompt is looked at as old and useless?
….as I witness a regression in the general understanding across the great unwashed masses as to the power of computers.
Twenty or so years ago, people who didn’t understand much about computers used to largely stay away from computers.
wow.. you really know your stuff guy!
Since English is not my native language, I couldn’t have stated this so eloquently… So thank you for your comment, this could be used in tig cases.
How can it be dubious when it’s available on CNET’s Download.com and gets a 4-star Editor’s Rating? 😉
http://download.cnet.com/mSpy/3000-2162_4-75765470.html
Thank you gor starting my day with a chuckle.
download.com is run by hackers now, most of the software is repacked. Reviews for the last year slam it, and I have see it first hand – cleaning up after people.
We can all thank CBS for that! :\
Never heard of this software before today. Went to their website for a quick look and a IM window opened. Here’s a very brief chat I had with one of their online people, I cut & pasted in it’s entirety:
Dustin Mill: Thank you for your interest in our products & services!
Me: heard you got hacked
Dustin Mill: Hello. Please, provide me with more details? Where did you find this information?
Me: http://krebsonsecurity.com/2015/05/mobile-spy-software-maker-mspy-hacked-customer-data-leaked/
Dustin Mill: Thank you! We do not have any requests or information about it. I we will double check it with our developers and manager. Thank you for this information!
They told me the same thing, the same person, terrible
Olga Bright: The information that you’ve seen is just black marketing. You can check our Privacy policy: mspy.com/privacy-policy.html
lmao
Good read , keep them coming
Some deep thinking needed here.
If it’s legal for the government should it be legal for citizens?
Do we hear about the government spying that is hacked?
I personally think this sort of thing shouldn’t happen. Grubby little people pawing over sexted messages is not appealing. If it’s not captured it can’t be stolen / FOI’ed etc.
Another lamentable example of weakness at the merchant. I’m glad they were not more successful.
> If it’s not captured it can’t be stolen
What Merchant’s don’t have, Crooks can’t steal
Sounds very familiar. Look at the header of
http://www.NC3.mobi
the better way
Which has nothing to do with data coming from cell phones, as people KNOW the information is being stored “in the cloud” and they WANT to be able to access it themselves “after the fact”
It’s also legal for governments to detain people under suspicion of a crime, and if found guilty, execute or detain them for life.
Are you arguing anyone should be able to do that, because the government can?
@Chris – “Are you arguing anyone should be able to do that, because the government can?”
With a little thought you will see that though illegal, it isn’t unconstitutional for a private citizen to make “spyware that invades an unwitting victim’s confidential communications.” However, there are those who would maintain that when the government does it, they are violating the First Amendment. Unfortunately the 1984 mentality of our law enforcement agencies, as they are euphemistically called, allows them to spy on us.
People get detained every day by, e.g. private security or store managers, for shoplifting. You definitely can make the case that summary executions happen often in the US and quite often that execution was proper. I certainly know via military law enforcement experience what those circumstances are and would support mandatory training for everyone (not just gun owners).
‘Mobile Spy Software Hacked’ Can you say #Irony?
What do you think about FlexiSPY? More secure?
I think OwnSpy is far better and easier to use…
Interesting, I searched the software (Ownspy) that you suggested and found no references to it from reputable sources. Flexispy has a lot of articles talking about it, so I was wondering about Brian’s opinion.
Not sure if you’re seriously asking this question. All those “articles” you see are plants by people looking to generate affiliate revenues from sales of FlexiSpy. I’ve studied nearly a dozen of these apps and they’re all basically the same – you’re sending whatever data you’re gleaning from the person you’re spying on to some overseas server controlled by a company who has little interest or concern that your data is kept secure. If your goal is to spy on someone, they work quite well. If you actually care about the person you’re spying on (e.g., your kids), then you should use a legitimate parental control and monitoring app from a well-known, reputable company.
This is why I like OwnSpy, they encrypt most of the data so if this happen the personal info won’t be disclosed.
How do you know that OwnSpy encrypt their information? No website mentions this.
I used to be a customer and they mentioned it on previous versions of their page: http://blog.en.ownspy.com/post/36754254626/app-recording
I guess it is fake.. or one more marketing trick!
this is not fake
localhost # du -ha
4.0K ./mailer/system.indexes.bson.bz2
4.0K ./mailer/log.metadata.json.bz2
24K ./mailer/log.bson.bz2
36K ./mailer
4.0K ./readme.txt
4.0K ./storage/system.indexes.bson.bz2
324M ./storage/log.bson.bz2
324M ./storage
1.2G ./monline_main/api_request.bson.bz2
1.2G ./monline_main
221M ./monline_log/log.bson.bz2
221M ./monline_log
4.0K ./keep2/system.indexes.bson.bz2
4.0K ./keep2/log.metadata.json.bz2
95M ./keep2/log.bson.bz2
95M ./keep2
4.0K ./pay/system.indexes.bson.bz2
4.0K ./pay/log.metadata.json.bz2
68M ./pay/log.bson.bz2
68M ./pay
4.0K ./keep/collection.bson.bz2
4.0K ./keep/system.indexes.bson.bz2
14G ./keep/log.bson.bz2
14G ./keep
147M ./mcloud/log.bson.bz2
147M ./mcloud
4.0K ./monline_mobile_log/system.indexes.bson.bz2
3.6G ./monline_mobile_log/log.bson.bz2
3.6G ./monline_mobile_log
66M ./pipe_queue/pipe_track.bson.bz2
66M ./pipe_queue
20G .
uncompressed size of all bases more than 1TB
Wow, you got the full stash? Share the link please.
Do you have the .onion address? I would like to check it!
Well, I can see that the files are there, however without the possibility of download the data there is no way to confirm those files are actually mSpy data… I guess we will need to wait a bit longer..
Maybe you should post a partial list of mails or something like that.
I won’t be allowing anyone to post the onion link here on this blog. I don’t think it’s right to spread this far and wide, and while I can’t stop people from doing that elsewhere, I can here.
Thank you for taking reasonable and responsible actions to protect victims.
You’re no fun Brian :,(
Brian, that was the right call to make.
Brian, I have to say I really admire your combination of technical expertise, brutal honesty, and good ethics. This blog is the go-to resource for keeping a pulse on the online ne’er-do-wells.
agree
Wish he would be as brutally honest about nsa surveillance practices and abuses, I guess that’s a no-go area for Brian. However, the rest I do appreciate.
Righteous call Brian (in the best sense). Aiding and abetting the violation by either mSpy or the “hackers” isn’t proper.
And the “testimonials” on their website look so authentic. Who’d have thought.
They look like every other testimonial I have seen for other products and services, and none of those were written by testy people.
Regarding the documents from Companies House, you should be aware that you can register a Limited in the UK by proxy and that there’s no verification whatsoever of the directors’ names. There are websites that offer such registration services for about $20. Most of these fake Limiteds have that address in St John Street. My guess is that the names Aleksey Fedorchuk and Pavel Daletski were simply made up.
No information on how they got hacked yet?
Just a note here on the public relations pitch mentioned in the article. Did it get simply pasted in as a news article for the CBS Philadelphia station?
http://philadelphia.cbslocal.com/2014/09/10/parents-can-monitor-childrens-online-activity-with-mspy/
I’d love to hear how close this news story is to the press release.
Mspy must be closed by FBI urgent. I still dont understand why the domain is still active
Me: then please tell me how your system is safe from such an attack scenario. id be happy to learn!
Betty Holmes: Our officials confirm it is false, and the technicians said it is not possible to hack the database of ours
Me: i guess we’ll all have to follow how it develops. this may not be the best time to decide on your product for us.
Betty Holmes: I am sorry for that frustration about it
The information in that article is not confirmed
Me: we’ll see how your officials will satisfy our need for information about the issue.
a simple “no” wont be enough for any user aware of what such a product needs to fulfill
Betty Holmes: hopefully there will be an official release posted for the cistomers not to worry
customers*
Me: thank you for the conversation!
Yes, I’m sure it’s just black marketing, just like mSpy’s customer support people say. Keep saying you had no breach, mSpy. Nothing to see here, move along. Whatever you do, don’t look at this sales thread for source code stolen from a mobile spy company that was put up for sale yesterday on the deep web
http://krebsonsecurity.com/wp-content/uploads/2015/05/RealDealSpySource.png
” … technicians said it is not possible to hack the database of ours …”
Somewhere out there, a hacker is hollering “challenge accepted!!”
I notice that the US Attorney said, “Advertising and selling spyware technology is a criminal offense,” not using spy ware. Wouldn’t want the US government to have to prosecute the NSA, now would we
Tor…you should have your noscript enabled, FYI.
Too funny, the lawsuit in Florida is claiming confusion on the name, and the headline for the blog is “Mobile Spy” software maker Mspy.
I guess they had a case.
Very true. Plus, unlike mSPY, the Mobile Spy product is not spyware since it shows an icon and has notifications which can’t be turned off. But the title of the post probably confuses people to think mSPY is related to Mobile Spy which isn’t true.
According to Forbes, mSpy’s founder is Andrei Shimanovich (and links to his LinkedIn profile) and its all about protecting the children (and dodging liability):
“It is the same question with the gun producer,” says Shimanovich, a Belarus native who recently moved to New York. “If you go out and buy a gun and go shoot someone, no one will go after the gun producer. People who shoot someone will be responsible for this. Same thing for mSpy. We just provide the services which can solve certain tasks regarding parents and teenagers.”
http://www.forbes.com/sites/adamtanner/2014/03/12/starting-today-jealous-lovers-can-buy-nsa-like-monitoring-powers/
Legitimate parental supervision software doesn’t need to hide its presence from the user, so it seems fairly clear that that isn’t the intended purpose of this particular product. As you say this is nothing more than a transparent (and likely unsuccessful, if ever tested) attempt to dodge liability.
Legitimate gun manufacturers/distributors aren’t legally responsible for misuse of their weapons – but if they started selling weapons specifically designed for criminal use, it would probably be a different matter. 🙂
His analogy is way wrong.
People use his software to upload and store data from their cell phones, and provide the data back to them after logging into their account. That data was somehow exfiltrated from his business servers. The storage and access to that data is under the control of his business. He is 100% responsible.
Gun and ammunition manufacturers have no direct influence over the weapons they make once the guns or bullets have left their factory. Their only influence is to persuade people to behave themselves, and to buy more guns and bullets. No gun or bullet notifies the manufacturers of who is using the gun, where the gun is located, and how many times the gun is fired, if the gun has misfired, where the gun has been aimed when fired, and whose bullets are being loaded into the gun.
internet security needs to be everysingle companys number 1 issue. these hacks are only going to become more common because of how crime has been keeping up with tech.
We have noticed same issue on couple of websites
We have stuff like that
According to Forbes, mSpy’s founder is Andrei Shimanovich (and links to his LinkedIn profile) and its all about protecting the children (and dodging liability):
“It is the same question with the gun producer,” says Shimanovich, a Belarus native who recently moved to New York. “If you go out and buy a gun and go shoot someone, no one will go after the gun producer. People who shoot someone will be responsible for this. Same thing for mSpy. We just provide the services which can solve certain tasks regarding parents and teenagers.”
Same mission about teens monitoring TheOneSpy.com gives you same feature with reliable and reasonable security and tracking apps.
I won’t repeat features and other stuff of all monitoring apps like flexispy, mobile-spy. These are also fine.
Can enyone share link to this DB?
tor or mega link?
thanks
>Those records (PDF) indicate that Daletski is a British citizen, and that Mr. Fedorchuk is from Russia.
The PDF has Fedorchuk’s nationality as ‘UK’.
There were many incorporation and directors documents which I did not publish that had conflicting information on his nationality.
Understood, thanks.
Not really good information to hear.. I thought it was a reliable app. Can you recommend any?
I used mSpy cause it was number first on the review-website of the monitoring apps. Now, I do not really know what app to choose.
I also just visited mspy.com and this chat window came up. They deny there is a leak, well, further questioning, they deny there is a leak of encrypted data…
Live Chat
Donna Haynes: Thank you for your interest in our products & services!
Me: I just wondered abou the security.
Donna Haynes: what would you like to know?
Me: Is it true that you got hacked?
How do you make sure that no private data is exposed?
Donna Haynes: Dear Customer, we kindly inform that this is not an official information and we are not aware of it’s source. It seems to be black marketing.
Can you please provide us with the source you’ve learned about it from?
Me: Its on ibtimes.co.uk – and you don’t know about it?
http://www.ibtimes.co.uk/mspy-hack-fears-400000-customers-smartphone-spy-tools-hit-claims-respected-journalist-1501454
Also I find it hard to believe that krebsonsecurity takes part in black marketing.
so anyway, how do you make sure that private infomration stays private? After all, I want to supervise my kids and not give some creeps a way to get their info
Donna Haynes: by security encryption, we know that there were articles, but no data has been leacked
Me: Just to make sure, the 400GB leak does not exist?
Donna Haynes: I am only a sales rep and have no information regarding this
Me: So you do not know whether data has been leaked?
Donna Haynes: our officials told us that no encrypted data has been leaked, this is the only information I am aware of
Me: So you do not deny that non encrypted data has been leaked
So far…
First of all, who takes the word of a customer support rep as gospel for the company? From her responses, it sounds like she doesn’t know anything more than a broad denial by whoever is in charge. “No encrypted data has been leaked.” What a relief. Only metric truckloads of *unencrypted* data has been leaked.
Huge volumes of tech support requests just like that one have been leaked from mSpy. They should read their own logs. E.g.
“actionREDACTED@hotmail.com”, “comment” : “hi i just tried to renew a subscripton referance # 35528859 and opened a whole new account somehow?could you please apply the new funds to the old account thanks steve”, “locale” : “en-GB” }, “locale” : “en”, “attachments” : [] }, “result” : { “status” : true } }
{ “_id” : ObjectId( “54cfaaf62d3cd682268b45fb” ), “_app” : “mailer/api”, “_type” : “api”, “_ok” : true, “_time” : NumberLong(294), “_start” : Date( 1422895861575 ), “_ip” : “104.193.175.75”, “_hostname” : “prod-mobi2-initial1.host.int”, “_txn” : “send”, “request” : { “template” : “mspycom_feedback”, “name” : “support@mspy.com”, “address” : “support@mspy.com”, “fields” : { “name” : “Kyla READACTED “, “email” : “brookeREADACTED@yahoo.com”, “comment” : “My question is concerning the mspy for an iPhone. I would like to know if private browsing on the phone is enabled when searching the internet, and it doesn’t save in the phones history to be deleted at all, then can this software still pick up on the websites being searched in private browsing mode? “, “locale” : “en-US” }, “locale” : “en”, “attachments” : [] }, “result” : { “status” : true } }
{ “_id” : ObjectId( “54cfe75f2d3cd687268b46cb” ), “_app” : “mailer/api”, “_type” : “api”, “_ok” : true, “_time” : NumberLong(264), “_start” : Date( 1422911326681 ), “_ip” : “104.193.175.75”, “_hostname” : “prod-mobi2-initial1.host.int”, “_txn” : “send”, “request” : { “template” : “mspycom_feedback”, “name” : “support@mspy.com”, “address” : “support@mspy.com”, “fields” : { “name” : “ana”, “email” : “ana.READACTED@hotmail.com”, “comment” : “I would like to Pay mi bill with a diferent credit card “, “locale” : “en-US” }, “locale” : “en”, “attachments” : [] }, “result” : { “status” : true } }
{ “_id” : ObjectId( “54d004d72d3cd646278b472d” ), “_app” : “mailer/api”, “_type” : “api”, “_ok” : true, “_time” : NumberLong(248), “_start” : Date( 1422918870719 ), “_ip” : “104.193.175.75”, “_hostname” : “prod-mobi2-initial1.host.int”, “_txn” : “send”, “request” : { “template” : “mspycom_feedback”, “name” : “support@mspy.com”, “address” : “support@mspy.com”, “fields” : { “name” : “wilson berBoanREADACTEDs junior”, “email” : “wilson.bmj@gmail.com”, “comment” : “boa noite, são voces que fizeram o programa SPYOBRIGADOMASTERPRO ?\r\n\r\n\r\n “, “locale” : “en-US” }, “locale” : “en”, “attachments” : [] }, “result” : { “status” : true } }
{ “_id” : ObjectId( “54d07a7f2d3cd680268b487e” ), “_app” : “mailer/api”, “_type” : “api”, “_ok” : true, “_time” : NumberLong(264), “_start” : Date( 1422948990260 ), “_ip” : “104.193.175.75”, “_hostname” : “prod-mobi2-initial1.host.int”, “_txn” : “send”, “request” : { “template” : “mspycom_feedback”, “name” : “support@mspy.com”, “address” : “support@mspy.com”, “fields” : { “name” : “Vibha”, “email” : “sharmaREADACTED@yahoo.com”, “comment” : “Does an iPhone has to be jailbroken to install mspy? How can I tell if somebody has installed mspy on my computer or \r\nun jailbroken iphone?”, “locale” : “en-US” }, “locale” : “en”, “attachments” : [] }, “result” : { “status” : true } }
bSpy exemployer company join to Squad Lizard or aother hack development team
Couldn’t have happend to a nicer bunch of guys!! 😉
Sheesh. We never dreamed of this when we first watched the internet, and then the web, being constructed. Crazy. Which direction is all this going?
Olga Bright: mSpy provides a 100% secure solution for your smartphone monitoring. The activity logs transferred to our server are encrypted and stored anonymously to prevent third-party snooping and interception. We guarantee that no one else can access your data. The information that you’ve seen is just black marketing. You can check our Privacy policy: mspy.com/privacy-policy.html
Me: http://krebsonsecurity.com/2015/05/mobile-spy-software-maker-mspy-hacked-customer-data-leaked/
It says that the data got leaked and I checked the link and it did have information.
Olga Bright: The information that you’ve seen is just black marketing. You can check our Privacy policy: mspy.com/privacy-policy.html