The U.S. Department of Homeland Security (DHS) has been quietly launching stealthy cyber attacks against a range of private U.S. companies — mostly banks and energy firms. These digital intrusion attempts, commissioned in advance by the private sector targets themselves, are part of a little-known program at DHS designed to help “critical infrastructure” companies shore up their computer and network defenses against real-world adversaries. And it’s all free of charge (well, on the U.S. taxpayer’s dime).
KrebsOnSecurity first learned about DHS’s National Cybersecurity Assessment and Technical Services (NCATS) program after hearing from a risk manager at a small financial institution in the eastern United States. The manager was comparing the free services offered by NCATS with private sector offerings and was seeking my opinion. I asked around to a number of otherwise clueful sources who had no idea this DHS program even existed.
DHS declined requests for an interview about NCATS, but the agency has published some information about the program. According to DHS, the NCATS program offers full-scope penetration testing capabilities in the form of two separate programs: a “Risk and Vulnerability Assessment,” (RVA) and a “Cyber Hygiene” evaluation. Both are designed to help the partner organization better understand how external systems and infrastructure appear to potential attackers.
“The Department of Homeland Security (DHS) works closely with public and private sector partners to strengthen the security and resilience of their systems against evolving threats in cyberspace,” DHS spokesperson Sy Lee wrote in an email response to an interview request. “The National Cybersecurity Assessments and Technical Services (NCATS) team focuses on proactively engaging with federal, state, local, tribal, territorial and private sector stakeholders to assist them in improving their cybersecurity posture, limit exposure to risks and threats, and reduce rates of exploitation. As part of this effort, the NCATS team offers cybersecurity services such as red team and penetration testing and vulnerability scanning at no cost.”
The RVA program reportedly scans the target’s operating systems, databases, and Web applications for known vulnerabilities, and then tests to see if any of the weaknesses found can be used to successfully compromise the target’s systems. In addition, RVA program participants receive scans for rogue wireless devices, and their employees are tested with “social engineering” attempts to see how employees respond to targeted phishing attacks.
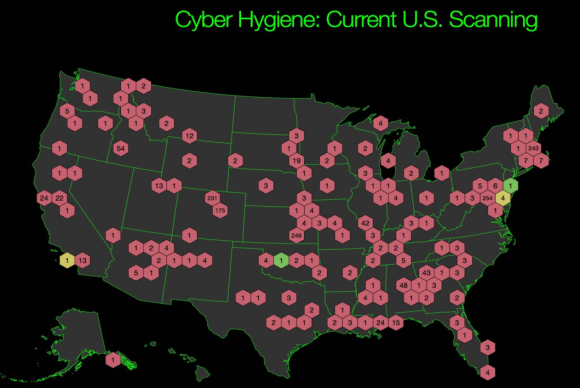
The Cyber Hygiene program — which is currently mandatory for agencies in the federal civilian executive branch but optional for private sector and state, local and tribal stakeholders — includes both internal and external vulnerability and Web application scanning.
The reports show detailed information about the organization’s vulnerabilities, including suggested steps to mitigate the flaws. DHS uses the aggregate information from each client and creates a yearly non-attributable report. The FY14 End of Year report created with data from the Cyber Hygiene and RVA program is here (PDF).
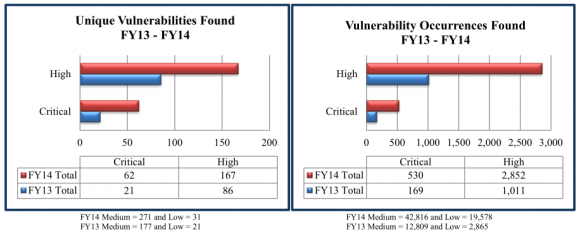
Among the findings in that report, which drew information from more than 100 engagements last year:
-Manual testing was required to identify 67 percent of the RVA vulnerability findings (as opposed to off-the-shelf, automated vulnerability scans);
-More than 50 percent of the total 344 vulnerabilities found during the scans last year earned a severity rating of “high” (4o percent) or “critical” (13 percent).
-RVA phishing emails resulted in a click rate of 25 percent.
ANALYSIS
I was curious to know how many private sector companies had taken DHS up on its rather generous offers, since these services can be quite expensive if conducted by private companies. In response to questions from this author, DHS said that in Fiscal Year 2015 NCATS provided support to 53 private sector partners. According to data provided by DHS, the majority of the program’s private sector participation come from the energy and financial services industries — with the latter typically at regional or smaller institutions such as credit unions.
DHS has taken its lumps over the years for not doing enough to gets its own cybersecurity house in order, let alone helping industry fix its problems. In light of the agency’s past cybersecurity foibles, the NCATS program on the surface would seem like a concrete step toward blunting those criticisms.
I wondered how someone in the penetration testing industry would feel about the government throwing its free services into the ring. Dave Aitel is chief technology officer at Immunity Inc., a Miami Beach, Fla. based security firm that offers many of the same services NCATS bundles in its product.
Aitel said one of the major benefits for DHS in offering NCATS is that it can use the program to learn about real-world vulnerabilities in critical infrastructure companies.
“DHS is a big player in the ‘regulation’ policy area, and the last thing we need is an uninformed DHS that has little technical expertise in the areas that penetration testing covers,” Aitel said. “The more DHS understands about the realities of information security on the ground – the more it treats American companies as their customers – the better and less impactful their policy recommendations will be. We always say that Offense is the professor of Defense, and in this case, without having gone on the offense DHS would be helpless to suggest remedies to critical infrastructure companies.”
Of course, the downsides are that sometimes you get what you pay for, and the NCATS offering raises some interesting questions, Aitel said.
“Even if the DHS team doing the work is great, part of the value of an expensive penetration test is that companies feel obligated to follow the recommendations and improve their security,” he said. “Does the data found by a DHS testing team affect a company’s SEC liabilities in any way? What if the Government gets access to customer data during a penetration test – what legal ramifications does that have? This is a common event and pre-CISPA it may carry significant liability.”
As far as the potential legal ramifications of any mistakes DHS may or may not make in its assessments, the acceptance letter (PDF) that all NCATS customers must sign says DHS provides no warranties of any kind related to the free services. The rules of engagement letter from DHS further lays out ground rules and specifics of the NCATS testing services.
Aitel, a former research scientist at the National Security Agency (NSA), raised another issue: Any vulnerabilities found anywhere within the government — for example, in a piece of third party software — are supposed to go to the NSA for triage, and sometimes the NSA is later able to use those vulnerabilities in clandestine cyber offensive operations.
But what about previously unknown vulnerabilities found by DHS examiners?
“This may be less of an issue when DHS uses a third party team, but if they use a DHS team, and they find a bug in Microsoft IIS (Web server), that’s not going to the customer – that’s going to the NSA,” Aitel said.
And then there are potential legal issues with the government competing with private industry.
Alan Paller, director of research at the SANS Institute, a Bethesda, Md. based security training group, isn’t so much concerned about the government competing with the private sector for security audits. But he said DHS is giving away something big with its free assessments: An excuse for the leadership at scanned organizations for not doing anything after the assessment and using the results as a way to actually spend less on security.
“The NCATS program could be an excellent service that does a lot of good but it isn’t,” Paller said. “The problem is that it measures only a very limited subset of of the vulnerability space but comes with a gold plated get out of jail free card: ‘The US government came and checked us.’ They say they are doing it only for organizations that cannot afford commercial assessments, but they often go to organizations that have deep enough pockets.”
According to Paller, despite what the NCATS documents say, the testers do not do active penetration tasks against the network. Rather, he said, they are constrained by their rules of engagement.
“Mostly they do architectural assessments and traffic analysis,” he said. “They get a big packet capture and they baseline and profile and do some protocol analysis (wireless).”
Paller said the sort of network architecture review offered by DHS’s scans can only tell you so much, and that the folks doing it do not have deep experience with one of the more arcane aspects of critical infrastructure systems: Industrial control systems of the sort that might be present in an energy firm that turns to NCATS for its cybersecurity assessment.
“In general the architectural reviews are done by younger folks with little real world experience,” Paller said. “The big problem is that the customer is not fully briefed on the limitations of what is being done in their assessment and testing.”
Does your organization have experience with NCATS assessments? Are you part of a critical infrastructure company that might use these services? Would you? Sound off in the comments below.




There is also the concern that if you look at the recently discovered back door installs that happened during the Olympics under the guise of helping secure the system that this also provides pretty open access to corporations in the US for the same type of subterfuge. Free security scanning all for the low price of a well placed back door.
Citation requested, pls
He is talking about this
http://www.dailykos.com/story/2015/2/17/1364910/-Breaking-Kaspersky-Exposes-NSA-s-Worldwide-Backdoor-Hacking-of-Virtually-All-Hard-Drive-Firmware
Are these the same guys that would have done assessments for OPM? If so, that’s all I need to know.
I can see a lot of good, and a lot of bad coming from this type of service. Personally, I would rather pay the 10-20k out of my annual security budget, and have someone on the hook if something goes wrong, and for confidentiality. Not to mention, the majority of good penetration testing IS manual work, and the US govt is hardly known for retaining the top talents, at least for these types of engagements.
Also most sounds like planned recon to know what the best ways in to private corporations are, so that they can turn those results over to those doing covert offensive attacks on foreign corps…..but that may just be my tinfoil hat showing.
OPM’s issue wasn’t the lack of assessments, rather Management’s failure to act on the assessments.
The word “Test” was mistakenly added to the title of this article..
please fix
I concur.
I hope one of the first questions the companies or utilities ask themselves is “Why is this system/this data on a network segment which might be accessible from the public Internet?”.
I believe that too often data and systems are connected to the Internets just because they can be, or for simple convenience. There is too little thought given to the tradeoff between the risk of unwanted access and the extra effort that isolation would require but the protection it would afford.
*Why* are these systems and data even exposed to possible unwanted access in the first place? If remote access is required, why not use dedicated, secure, isolated circuits?
I have been affiliated with, and known the team members on, this program for several years and I’d like to thank Brian for a pretty fair article. I can definitively say that active exploitation is conducted on these assessments and they are actually pretty robust penetration tests (as much as possible). The vast majority of their assessments are conducted against Federal systems, or to a lesser extent state and local government systems.
They do assessments for some private companies, but only when it’s judged to be in the public interest. I realize that’s a fuzzy line, but they are not looking to compete with private industry (and couldn’t anyway, legally or because of scale). Generally private companies are critical infrastructure related or financial. Both of which the government has an interest in seeing protected from a public good standpoint. While findings are anonymized, aggregated and reported on; client information is kept confidential. They don’t hand any findings over to other agencies (for those of you with tinfoil hats on).
I’d say this is one of the few programs that actually provides active analysis of system strengths and weaknesses from trained experts. For its cost, I think it’s one of the more beneficial security services the government can provide. They’ve put some public material out (Brian referenced some of it) and I’d encourage you to read it if you’re interested and form your own opinion.
Uh huh.
You can keep your doctor and you’ll save money with the the ACA. That attack on the Benghazi consulate was caused by a movie on youtube.
There was no targeting of Conservative groups by the IRS….
You mean to imply that there are people reading this article WITHOUT their tinfoil hats on?!?
This is a good thing – but extremely way too late.
The ones you have to worry about won’t participate since they know their junk is vulnerable. problem is, if they have any sort of trust with anyone else, all it takes is one bad apple to get into a shiny compliant corporation and have keys to the kingdom.
Since the news in general has churned up so much crap about the SCADA systems, this effort should be directed towards the highest, most critical places first. Then, unscrew the governement networks, since this IS a government entity. Start with the State Department and get all the funk out of that place. That will probably take a decade or two to unscrew.
Security by Obscurity is bad. Its even worse when people come out into the light and show exactly how old their vulnerabilities are. Then somehow, these corporations are going to get some one else to pay for their feebleminded attempts at network security.
The scans are better than nothing. A crook has to get in initially somehow, be it via vulnerability, phishing, social engineering or personal penetration of the facility. Don’t hold your hopes too high with this. If they are already in, they have installed things that typically do not get detected for years – or until some amateur puts something on that network that is detected by the security programs and lights off sensors to a problem on the network.
Network diligence that protects the Department of Defense is pretty decent. Until that level of effort is duplicated on the civilian sector, this problem will exist day to day. Its going to always be an uphill battle.
I wonder if that is what caused massive problems for some government agencies Monday and Tuesday last week. Sure looked as though there was some sort of DOS attack causing dns failures and reachability issues for a smattering of federal web sites.
We are seriously considering the services as a supplement to controls testing we already have in place. We have already paid for it in taxes so we may as well engage and get the benefits.
Who is Alan Palmer? SANS could be a great training institute, but it isn’t.
Brian… where is the link to the ROE letter, that’s the same link as the Authorization & Acceptance Letter.
Perhaps DHS should work with OPM, State and White House first?
Don’t forget IRS
Virtually all their systems are crud.
They can’t take care of themselves, what should make me trust they’ll take care of me? Sometimes a pricetag is well-worth it for the caution, long-term and to avoid trouble. Besides as it’s been said so far, they’re offering it to the companies which CAN and DO pay for PRIVATE pentesting, so they’re taking out taxpayer bling for a service that only the cheapskates, the lazy, or no one at all will ever use. It’s like how they spent so much money on obamacare only to have it not even reach the mark of membership by a long shot.
Why should we pay taxes for something that’s symbolic and nothing above and beyond that? The gov should stay out of cybersecurity. The private industry is not only better equipped for it, but also better fit for the circumstance, concern-wise. I wouldn’t let a DHS crony touch my PC.
Given the overall pathetic state of security at many government agencies, wouldn’t it make more sense for them to be focusing on improving government security? It seems like they’re grandstanding a bit for the commercial crowd (and probably not competing effectively with commercial penetration testers except that they’re taxpayer-subsidized)
I’m really tired of seeing the feds going “improve your security” to the corporate world, when you have generally pathetic security and inter-agency non-cooperation throughout the government. When we hear no more stories about system administrators leaving NSA with tons of documents, or OPM being wide open for years, etc ad nauseam, then maybe it’ll be time for the feds to start offering advice to the corporate world.
Bohica. The government has been ‘penetration testing’ us for years.
DHS and the Chinese government both are giving “free penetration tests”.
I have about the same level of trust in either of them.