Imagine buying an internet-enabled surveillance camera, network attached storage device, or home automation gizmo, only to find that it secretly and constantly phones home to a vast peer-to-peer (P2P) network run by the Chinese manufacturer of the hardware. Now imagine that the geek gear you bought doesn’t actually let you block this P2P communication without some serious networking expertise or hardware surgery that few users would attempt.

The FI9286P, a Foscam camera that includes P2P communication by default.
This is the nightmare “Internet of Things” (IoT) scenario for any system administrator: The IP cameras that you bought to secure your physical space suddenly turn into a vast cloud network designed to share your pictures and videos far and wide. The best part? It’s all plug-and-play, no configuration necessary!
I first became aware of this bizarre experiment in how not to do IoT last week when a reader sent a link to a lengthy discussion thread on the support forum for Foscam, a Chinese firm that makes and sells security cameras. The thread was started by a Foscam user who noticed his IP camera was noisily and incessantly calling out to more than a dozen online hosts in almost as many countries.
Turns out, this Focscam camera was one of several newer models the company makes that comes with peer-to-peer networking capabilities baked in. This fact is not exactly spelled out for the user (although some of the models listed do say “P2P” in the product name, others do not).
But the bigger issue with these P2P -based cameras is that while the user interface for the camera has a setting to disable P2P traffic (it is enabled by default), Foscam admits that disabling the P2P option doesn’t actually do anything to stop the device from seeking out other P2P hosts online (see screenshot below).
This is a concern because the P2P function built into Foscam P2P cameras is designed to punch through firewalls and can’t be switched off without applying a firmware update plus an additional patch that the company only released after repeated pleas from users on its support forum.
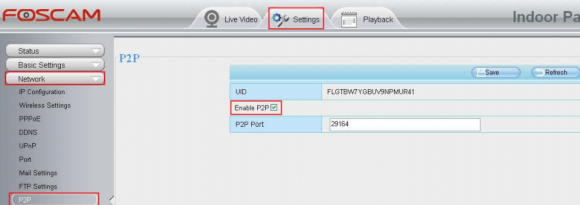
Yeah, this setting doesn’t work. P2P is still enabled even after you uncheck the box.
One of the many hosts that Foscam users reported seeing in their firewall logs was iotcplatform.com, a domain registered to Chinese communications firm ThroughTek Co., Ltd. Turns out, this domain has shown up in firewall logs for a number of other curious tinkerers who cared to take a closer look at what their network attached storage and home automation toys were doing on their network.
In January 2015, a contributing writer for the threat-tracking SANS Internet Storm Center wrote in IoT: The Rise of the Machines that he found the same iotcplatform.com domain called out in network traffic generated by a Maginon SmartPlug he’d purchased (smart plugs are power receptacles into which you plug lights and other appliances you may wish to control remotely).
What is the IOTC Plaform? According to ThroughTek, it’s a service developed to establish P2P communications between devices.
“I read the documentation provided with the device as well as all the website pages and there is no mention of this service,” wrote Xavier Mertens, an incident handler and blogger for SANS. “Manufacturers should include some technical documentation about the network requirements (ex: to download firmware updates).”
In another instance from May 2015, this blogger noted similar communications traffic emanating from a digital video recorder (DVR) device that’s sold in tandem with Internet-enabled surveillance cameras made by a company called Swann.
Likewise, postings from Dec. 2014 on the QNAP network attached storage (NAS) user forum indicate that some QNAP customers discovered mysterious traffic to iotcplatform.com and other Internet address requests that also were found in the Swann and Smart Plug traffic.
What do all of these things have in common? A visit to ThroughTek’s Web lists several “case studies” for its products, including Swann, QNAP and a home automation company based in Taiwan called AboCom.
ThroughTek did not respond to requests for comment. A ThroughTek press release from October 2015 announced that the company’s P2P network — which it calls the Kalay Network — had grown to support more than seven million connected devices and 100 million “IoT connections.”
I contacted Foscam to better understand the company’s relationship to ThroughTek, and to learn just how many Foscam devices now ship with ThroughTek’s built-in, always-on P2P technology. Foscam declined to say how many different models bundled the P2P technology, but it’s at least a dozen by my count of the models mentioned in the Foscam user manual and discussion thread.
Foscam customer service representative David Qu wrote in reply to requests for comment that “ThroughTek provides P2P technical support service for us.” He also said the P2P cameras merely keep a “heartbeat” connection to Foscam’s P2P server to check the connection status with the servers, and that no camera data will be stored on the company’s servers.
“The details about how P2P feature works which will be helpful for you understand why the camera need communicate with P2P servers,” Qu explained. “Our company deploy many servers in some regions of global world.” Qu further explained:
1. When the camera is powered on and connected to the internet, the camera will log in our main P2P server with fastest response and get the IP address of other server with low load and log in it. Then the camera will not connect the main P2P server.
2. When log in the camera via P2P with Foscam App, the app will also log in our main P2P server with fastest response and get the IP address of the server the camera connect to.
3. The App will ask the server create an independent tunnel between the app and the camera. The data and video will transfers directly between them and will not pass through the server. If the server fail to create the tunnel, the data and video will be forwarded by the server and all of them are encrypted.
4. Finally the camera will keep hearbeat connection with our P2P server in order to check the connection status with the servers so that the app can visit the camera directly via the server. Only when the camera power off/on or change another network, it will replicate the steps above.”
As I noted in a recent column IoT Reality: Smart Devices, Dumb Defaults, the problem with so many IoT devices is not necessarily that they’re ill-conceived, it’s that their default settings often ignore security and/or privacy concerns. I’m baffled as to why such a well-known brand as Foscam would enable P2P communications on a product that is primarily used to monitor and secure homes and offices.
Apparently I’m not alone in my bafflement. Nicholas Weaver, a senior researcher in networking and security for the International Computer Science Institute (ICSI), called the embedded P2P feature “an insanely bad idea” all around.
“It opens up all Foscam users not only to attacks on their cameras themselves (which may be very sensitive), but an exploit of the camera also enables further intrusions into the home network,” Weaver said.
“Given the seemingly cavalier attitude and the almost certain lack of automatic updates, it is almost certain that these devices are remotely exploitable,” he added. “It is no wonder that Director of National Intelligence James Clapper is worried about the Internet of Things, how many government officials have or may unwittingly install potential spies like this in their home.”
If you’re curious about an IoT device you purchased and what it might do after you connect it to a network, the information is there if you know how and where to look. This Lifehacker post walks through some of the basic software tools and steps that even a novice can follow to learn more about what’s going on across a local network.




@robert brown you are right children in danger in addition toys that comes from china are so dangerous because of substances really its kinda we going to real bad world
Brian –
Thanks for this article on the P2P challenges. We at OWLR have been working on a P2P-less solution for how to access the cameras without requiring an external call to some other service unless given permission.
The greatest challenge seems to be overcoming the default settings on the multitude of routers that exist in the world – and to ensure that when the user wishes to access their feed from outside, the hassle of port forwarding or the fear of UPNP vulnerabilities tends to cause more and more manufacturers to attempt to solve the problem with these types of solutions.
We believe that the purchase of devices like IP Cameras and any IoT Security solutions NEED to have the same completeness as a physical key or on-premises lock – only the key owner should be able to unlock and share the key if need be.
With Apple doing its fight with the FBI, with people’s cameras being hacked left, right and center – we need another solution. And we are working on providing a solution.
And – just to let you know – FOscam is not alone in the P2P pingback on IP Cameras. There are many other players doing the exact same. The real challenge: how to make this communication traffic effective and safe for users.
Take a look at TR-069
http://www.google.com/search?q=tr069&hl=en&btnG=Search
your QNAP part in the article is dribble.
if you had actually read the forum post, and had any knowledge of QNAP devices, the download station was enabled on this device (p2p file sharing).
This is hardly the same as it requires the owner of the qnap device to enable and setup the download station software.
maybe more research is required by the author of this article.
I think you mean drivel, not dribble.
For many people one of the important features of home security cameras is to be able to pull them up from work, from your phone, etc. Isn’t something like this (unfortunately) necessary so that mobile apps can get through NAT firewalls to communicate with these devices?
Things such as this are why the better ISP’s don’t block port 80. Any decent router will allow port forwarding and even a DMZ for setting up these things. The truth is, an app really isn’t needed (although companies will push for one). A smart phone will surf and since http comes in on port 80, you have options. HTTPS can also be setup.
The bottom line is….there are ways of doing things. You are not locked into what a salesman wants to sell ya.
While port forwarding is certainly a way to do this, we’re talking about a consumer product with consumer expectations. Installation instructions beyond “plug it in and go to this web site” are a non-starter for the *vast* majority of people who will buy this, and “find out the IP address your camera has and log into your router and configure port forwarding, then figure out what IP address your ISP has assigned you (today) and go to that in your browser” will get the vendor a 99% return rate.
Brian, I think you don’t understand what P2P means in this scenario.
The connections Foscam makes to IRS servers actually are required for the client application to know what IP the camera has at any given time, since many SMB and home users are on dynamic IPs.
When the app contacts Foscam’s provider’s servers, it gets that IP and then tries to establish a peer to peer connection with the camera.
The first peer in that connection is your phone with the client app and the second peer is the camera itself. Foscam’s servers is only making it possible for those two peers to connect to each other.
This is it. No public P2P network. No torrents. Nothing more.
Maybe investigate a bit more next time before posting FUD…
To its servers. Not to IRS servers… Damn you autocorrect.
Regardless of the definition of P2P, why do it this way? What your talking about can be done without going to non-foscam sites and acting very much like a potential DDOS attack. This whole thing just seems rather unprofessional to me. Krebs is absolutely right, these kinds of things ARE exactly what creates so much fear and anxiety with IoT
Unfortunately, we can only take them at their word. They are not very transparent regarding their use of ThroughTek’s “P2P” service. See the post below outlining the additional capabilities of ThroughTek’s Kalay Cloud.
In fact, when this issue first came to light, Foscam denied that the device would continue to make outgoing connections to their “P2P” servers if “P2P” was disabled http://foscam.us/forum/foscam-dialing-out-to-suspect-hosts-t17699.html#p69889. Then Foscam dismissed user concerns over unwanted outgoing connections, because “these communications are encryption, higher security.” http://foscam.us/forum/foscam-dialing-out-to-suspect-hosts-t17699-30.html#p70729. Eventually, Foscam admitted that disabling “P2P” through the web interface is fruitless and the only way to block those unwanted outgoing connections is at the router/firewall level http://foscam.us/forum/foscam-dialing-out-to-suspect-hosts-t17699-40.html#p70740.
I don’t think having users audit their connections or having user-friendly firewalls are the solution. I already dread having to configure and tweak firewalls every time I add a new device or install a new application. We need something completely automatic.
Thinking out of the box for a moment: If you install a camera, suppose your router automatically encrypted everything coming out of the camera such that it could only be decrypted on your smartphone, or whatever you’re using to view the feed from your camera. The encryption, decryption, and keys are completely independent of and outside of the control of camera manufacturer. The encryption is unavoidable; even if they get a secret feed of the video, they cannot decrypt it.
Instead of the router, perhaps it’s the device driver that does the encryption. The point is that this is something automatically done whenever you plug in a camera and which the camera manufacturer cannot subvert. (This idea is for cameras and such. For other kinds of IoT devices, this particular idea may or may not help.)
something completely automatic to traverse your firewall… is that anything like replacing your front door lock with an automatic door opener that opens when anyone walks up the path ?
I bought one of these Zmodo cameras which as far as I can tell are some of the most popular chinese tech home security cameras out now as they have a sleek modern design, very well priced and are being heavily pushed on all online chinese to US/Europe sites as well as ebay.
http://www.banggood.com/Zmodo-Wireless-WiFi-Home-CCTV-Security-720P-HD-Mini-IP-Camera-p-972170.html
The thing that surprised me about these is that go a step above the foscams in terms of connecting to mystery clouds in China as in that they don’t allow any kind of direct connection to them at all, you use it via mystery cloud or not at all.
These also appear to be rebranded by popular online tech retailers like Kogan.com.au
anyone that has cameras phoning home to china gets what they deserve. same thing with any device.
You assume the average user knows that the devices phone home to China. You’re either an @ss, stupid, or both.
When I purchased my GW security cameras I noticed a 100x increase in blocked packets to/from China on my PFsense system. Within 3 days the count was well over a million blocked packets.
It scares me to think what would happen in a regular person’s home or office.
GW, by the way, stands for Great Wall. I didn’t find that out until after.
Doesn’t this “P2P” stuff really just amount to a Bonjour-like naming/locating service?
That is one of it’s features, to locate a specific device on the internet.
However, ThroughTek’s product page bills the technology as much more featureful, check it out http://www.throughtek.com/kalay_cloud.html.
Additional features include:
-Data Analytics
–Valuable insight on real-time analytics with visualization.
–Recognize patterns to improve business operations.
-Device Management
–Locate and manage all devices by group or individually.
–Collect and record device data for further analysis.
-Streaming Server
–Monitor and record videos on demand anytime.
–Supports live streaming, full time or event specific recordings.
With Foscam keeping mum on the issue, there is no way to tell whether or not the additional features are being utilized. However, I cannot see any reason for them to leave money on the table…
All that crap to punch a hole through a NAT. HIgh time for IPv6, no?
Doesn’t change anything. I wouldn’t put a camera on a public v6 IP.
Well, and if a camera DOES connect to its manufacturer’s site, think about this:
How many units are out there? What would be the purpose of monitoring ALL of them? Sure you could think of some nefarious purpose if you put your mind to it, but what’re you going to do with 2 million pictures per half-second of some half-asleep people’s nostrils, elbows, and shoulders while they stare at a computer screen and picking their noses and ears for 4 hours?
Also: A camera is a WONDERFUL example of why this is an irrational fear – because it’s a device for seeing a place.
Given, you want to limit WHO can see it, but either you WANT a place watched or you DON’T. If lots of private stuff goes on there, maybe you shouldn’t be sticking a cam there in the first place, and if it’s NECESSARY to watch it securely, you’ll want to stick with an actual security system and not a webcam.
That is some of the best logic I’ve seen put to this so far. I find it very interesting though that few people seem to understand any of this when it comes to the xbox kinect and the massive server farms that MS owns.
Naive. As to purposes behind monitoring, they monitor and pick. The ones where the camera is attached to the house to monitor the driveway, for dork in ghettoland, ignore. For the one installed in a factory floor, economic spying. For one installed at a CEO’s house, monitor the comings and goings. Same for a celebrity’s house. Political figure? Same, with an eye to influence in addition to spying. They grab footage of a hooker coming to the house while spouse is away, leverage.
If they are truly interested in just P2P, why is there so much traffic transiting the router when no one is wanting the feed? The remote server’s owners would not want the traffic, it costs them money, and it would be child’s play to have the device check to see if someone was using the feed when it does it’s heartbeat check to the P2P server, only then sending the camera feed.
Misguided. The examples you give are things that create big security nightmares when using cheaper webcam type cameras. Anyone worth their weight in salt monitoring high profile locations should know better. When companies just want to monitor ‘the floor’, I can see going with this stuff….maybe. But even then, cameras that are to be more permanent need to be better than this Foscam P2P nonsense. This is precisely why so many companies are getting hacked now.
Your webcam will not work without a server pretty much 99% of the time dude. There’s this thing called NAT…
No IP Camera’s do not _require_ a third-party server, or even “P2P” servers to operate. IP Cameras, can be connected to and managed directly (locally and/or remotely). In order to connect and manage the IP Camera remotely (without the need for a VPN, SSH tunnel or anything of the sort), the user needs to open a port on the WAN interface and forward it to the local address and web interface port of the IP Camera.
However, at no point is a third-party server or “P2P” server _REQUIRED_. Any device that _REQUIRES_ the use of a third-party server or “P2P” servers in order to access, control and operate is a security incident waiting to happen.
Thank you. What is the IOTC Plaform? According to ThroughTek, it’s a service developed to establish P2P communications between devices. Mac Stickers
GE is in the process of selling its GE Appliances to Haier, a Chinese state-controlled company. In a Wall Street Journal article, Robert Bosch GmbH, the owner of Bosch-Siemens appliances, is quoted: “(Bosch) said around 230 million households, or 15% world-wide, will be equipped with smart-home technology by 2020.” This would include appliances and other devices connnected via the internet to monitoring centers.
Why would the US government allow a Chinese state-controlled company to have access into US homes?
Thank you for this post, Brian. We’re all guilty at some point of just letting the device do its work and just see it from its surface, but in fact, it’s a DEVICE that can be powerful enough to divulge whatever data you got. That’s why scandals won’t stop spreading in the internet. I encourage everyone to not stop exploring IoT and its security.
This is a NORMAL and correct way to function. If your home and office are both behind NAT, you *must* have some other peer help you to connect, otherwise you can’t watch your cat sleeping!
Whoever turned this feature into a bogus scare campaign is clueless about networking.
No, a peer is not required to watch your cat sleeping. However, a little research on how to port forward may be in order. In which case, http://portforward.com/ exists to help novice users through the steps of properly forwarding a port. If there is any “bogus scare campaign”, it is being perpetuated by anyone attempting to rationalize ThroughTek’s “P2P” service as compulsory. There is clearly a purpose and use-case for the “P2P” feature, but it should not be the go-to method of provisioning remote access.
The open source community is working on pieces of this – what will eventually come together as establishing standards and reference code for home IOT servers.
You’ll be able to get them from Linksys, etc, as well as rpms and such for Linux. I’d further bet built in to routers (doing too much often a risk though).
Most of the industry will support this effort – Philips has already had pushback on a firmware update that restricted their lights to their servers and excluded apple’s controllers. They’ve reversed this. To perhaps partial credit they indicated some concerns on securirty (though their protocols proven used SSL only part of the time).
Really two things need to come together
1) Home based servers
2) Integration or easy connection to routers and wireless communications.
While I’m not a big fan of devices trying to do too much – the guest type accounts (open or separate password & SSID, and firewalled from home network) on these routers is a great connection spot (for simple home users) that could be nearly autoconfigured. It could have hole punching turned off by default – where it’d be separately controllable on non IOT network (so your XBOX would work et all).
I don’t think the future is dire if the open source community picks up the pace and also the router / AP companies seek to work to integrate.
These cameras and such as they are now are morally wrong. The Chinese have been very industrious in electronics – even somewhat recently caught adding and modifying silicon chips used by the government and IT to add back doors and additional “features”
Nobody is expecting their cameras to be calling into China and anybody who things they can’t change a server setting and intercept the camera video is wrong.
This also goes far past the cell phone (and unfortunately now Microsoft 8/10 et all) data gathering coalescing apps.
Those are bad enough – but most people know they’re doing some of that – and a lot of peope like what they get back (even if they don’t understand the risk).
These devices totally hide that totally.
And think about it – this is an NSA dream – that remains a dream while trumped by the Chinese.
Thank you for providing additional insight into the state of opensource IP Cameras. I agree that as opensource IP Camera firmware and other software becomes more ubiquitous, the state of security for those devices will improve significantly.
Foscam’s attitude toward security and user concerns will be their own demise.
For instance, check out these PM’s
http://pastebin.com/dNjBnUQP
I received on the Foscam forums. All from “TheUberOverLord”, the sole tyrannical moderator of the community forums. After the persistent harassment, I pretty much gave up trying to help other users.
By the way, I’m not the only one that feels this way, http://www.amazon.com/gp/review/R3N3HG51UDIX5Y
Simply just needed to mention I’m just lucky that i happened upon your web site.|