A little-known feature of many modern smartphones is their ability to duplicate video on the device’s screen so that it also shows up on a much larger display — like a TV. However, new research shows that this feature may quietly expose users to a simple and cheap new form of digital eavesdropping.
Dubbed “video jacking” by its masterminds, the attack uses custom electronics hidden inside what appears to be a USB charging station. As soon as you connect a vulnerable phone to the appropriate USB charging cord, the spy machine splits the phone’s video display and records a video of everything you tap, type or view on it as long as it’s plugged in — including PINs, passwords, account numbers, emails, texts, pictures and videos.
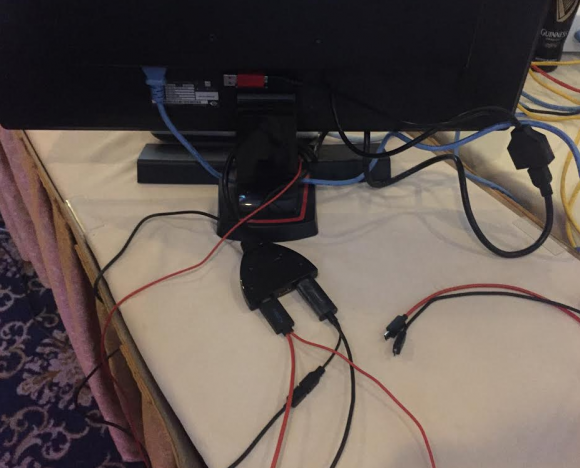
Some of the equipment used in the “video jacking” demonstration at the DEF CON security conference last week in Las Vegas. Source: Brian Markus.
[Click here if you’re the TL;DR type and just want to know if your phone is at risk from this attack.]
Demonstrations of this simple but effective mobile spying technique were on full display at the DEF CON security conference in Las Vegas last week. I was busy chasing a story at DEF CON unrelated to the conference this year, so I missed many people and talks that I wanted to see. But I’m glad I caught up with the team behind DEF CON’s annual and infamous “Wall of Sheep,” a public shaming exercise aimed at educating people about the dangers of sending email and other plain text online communications over open wireless networks.
Brian Markus, co-founder and chief executive officer for Aries Security, said he and fellow researchers Joseph Mlodzianowski and Robert Rowley came up with the idea for video jacking when they were brainstorming about ways to expand on their “juice jacking” experiments at DEF CON in 2011.
“Juice jacking” refers to the ability to hijack stored data when the user unwittingly plugs his phone into a custom USB charging station filled with computers that are ready to suck down and record said data (both Android and iOS phones now ask users whether they trust the computer before allowing data transfers).
In contrast, video jacking lets the attacker record every key and finger stroke the user makes on the phone, so that the owner of the evil charging station can later replay the videos and see any numbers or keys pressed on the smart phone.
That’s because those numbers or keys will be raised briefly on the victim’s screen with each key press. Here’s an example: While the user may have enabled a special PIN that needs to be entered before the phone unlocks to the home screen, this method captures even that PIN as long as the device is vulnerable and plugged in before the phone is unlocked.
GREAT. IS MY PHONE VULNERABLE?
Most of the phones vulnerable to video jacking are Android or other HDMI-ready smartphones from Asus, Blackberry, HTC, LG, Samsung, and ZTE. This page of HDMI enabled smartphones at phonerated.com should not be considered all-inclusive. Here’s another list. When in doubt, search online for your phone’s make and model to find out if it is HDMI or MHL ready.
Video jacking is a problem for users of HDMI-ready phones mainly because it’s very difficult to tell a USB cord that merely charges the phone versus one that also taps the phone’s video-out capability. Also, there’s generally no warning on the phone to alert the user that the device’s video is being piped to another source, Markus said.
“All of those phones have an HDMI access feature that is turned on by default,” he said. “A few HDMI-ready phones will briefly flash something like ‘HDMI Connected’ whenever they’re plugged into a power connection that is also drawing on the HDMI feature, but most will display no warning at all. This worked on all the phones we tested with no prompting.”
Both Markus and Rowley said they did not test the attack against Apple iPhones prior to DEF CON, but today Markus said he tested it at an Apple store and the video of the iPhone 6’s home screen popped up on the display in the store without any prompt. Getting it to work on the display required a special lightning digital AV adapter from Apple, which could easily be hidden inside an evil charging station and fed an extension adapter and then a regular lightning cable in front of that.
WHAT’S A FAKE CHARGING STATION?
Markus had to explain to curious DEF CON attendees who wandered near the Wall of Sheep this year exactly what would happen if they plugged their phone into his phony charging station. As you can imagine, not a ton of people volunteered but there were enough to prove a point, Markus said.
The demonstration unit that Markus and his team showed at DEF CON (pictured above) was fairly crude. Behind a $40 monitor purchased at a local Vegas pawn shop is a simple device that takes HDMI output from a video splitter. That splitter is connected to two micro USB to HDMI cables that are cheaply available in electronics stores.
Those two cords were connected to standard USB charging cables for mobiles — including the universal micro USB to HDMI adapter (a.k.a. Mobile High Definition Link or MHL connector), and a slimport HDMI adapter. Both look very similar to standard USB charging cables. The raw video files are recorded by a simple inline recording device to a small USB storage device taped to the back of the monitor.
Markus said the entire rig (minus the TV monitor) cost about $220, and that the parts could be bought at hundreds of places online.
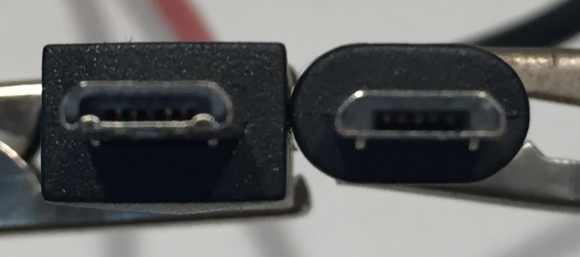
Although it may be difficult to tell the difference at this angle, the Mobile High Definition Link (MHL) USB connector on the left has a set of six extra pins that enable it to read HDMI video and whatever is being viewed on the user’s screen. Both cords will charge the same phone.
SHOULD YOU CARE?
My take on video jacking? It’s an interesting and very real threat — particularly if you own an HDMI ready phone and are in the habit of connecting it to any old USB port. Do I consider it likely that any of us will have to worry about this in real life? The answer may have a lot to do with what line of work you’re in and how paranoid you are, but it doesn’t strike me as very likely that most mere mortals would have reason to worry about video jacking.
On the other hand, it would be a fairly cheap and reasonably effective (if random) way to gather secrets from a group of otherwise unsuspecting people in a specific location, such as a hotel, airport, pub, or even a workplace.
An evil mobile charging station would be far more powerful when paired with a camera (hidden or not) trained on the charger. Imagine how much data one could hoover up with a fake charging station used to gather intellectual property or trade secrets from, say….attendees of a niche trade show or convention.
Now that I think about it, since access to electric power is not a constraint with these fake charging stations, there’s no reason it couldn’t just beam all of its video wirelessly. That way, the people who planted the spying equipment could retrieve or record the victim videos in real time and never have to return to the scene of the crime to collect any of it. Okay, I’ll stop now.
What can vulnerable users do to protect themselves from video jacking?
Hopefully, your phone came with a 2-prong charging cord that plugs straight into a standard wall jack. If not, look into using a USB phone charger adapter that has a regular AC/DC power plug on one end and a female USB port on the other (just make sure you don’t buy this keystroke logger disguised as a USB phone charger). Carry an extra charging dock for your mobile device when you travel.
Also, check the settings of your mobile and see if it allows you to disable screen mirroring. Note that even if you do this, the mirroring capability might not actually turn off.
What should mobile device makers do to minimize the threat from video jacking?
“The problem here is that device manufacturers continue to add features and not give us prompting,” Markus said. “With this feature, it automatically connects no matter what. HDMI-out should be off by default, and if turned on it should require prompting the user.”
Update: 4:52 p.m. ET: Updated paragraph about Apple iPhones to clarify that this same attack works against the latest iPhone 6.




Would the paranoid way in unknown territory be to charge a powerbank from available USB chargers and then charge your own device from that external battery pack?
Could just go with a USB condom, I’d assume.
This article focuses on the now-deprecated micro USB connector. Do modern phones with the Type-C connector have the same issue? Presumably, there wouldn’t be any extra pins or a special connector for that.
The USB-C protocol supports video out by default, however! Luckily Android has not yet implemented this feature of USB-C into their OS’s kernel
Pat,
It may be deprecated, but there are a lot of phones out there that use it. Not everyone buys a new phone every time a new model comes out. My phone is going on 4 years old and won’t be replaced until next year at the earliest.
I doubt the small inexpensive phones sold by no-contract cellular service providers will have Type C connectors for a very long time. It’s a more expensive connector.
Another reason I’m glad I went back to a flip phone
I can see a battery pack being sold that extracts the HDMI data from the screen, stores it and sends it off wirelessly once capable/in range. Carries it’s own power source, actually charged by the unwitting victim, allows people to use their device in relative safety (not out in the open for the more paranoid users) yet still siphon data off without anyone being alerted. Anyone willing to build a prototype?
That wouldn’t be good enough why not use Intel Wireless Display to send the data to a remote screen out side of the view of the person using said battery pack. You could then record their activities and replay it later. I could see this being used in conjunction with a rouge RaspPI device being dumped in say a Starbucks.
Please replace “battery pack” by “power bank” in the above post to be clear.
A “dumb usb” adapter, such as the portapaw, might prevent this exploit since those are suppose to only draw power and no data. You plug one side in to the charger and the phone in to the dumb part. Those have been around for a few years and actually haven’t seen much about them. (or tested them)
Problem with this type of device is that it limits charging speed to the original spec – 500 – 750 mA/H, rather than the up-to 2.5A/H charging speeds that most modern phones enjoy. There has to be a data handshake to identify the fastest speed allowed by the device, otherwise it falls back to the slow speed.
Absolutely right, this is the biggest draw-back of the proposed solution to charge via a non-data cable or using a dongle that removes the data pins.
Strangely the cost of these cable neutering devices which range around $10 +/- is also the cost of a small USB backup battery. You will get more utility from a backup battery than hanging around a kiosk for hours while your device slowly charges at only 500mah
This is only true of some apple chargers, and some QC 2.0/3.0 chargers (those that use QC with no normal fast charging fallback). Plenty of cheap generic chargers will provide up to 2.5a without any sort of handshake.
Good heads up article.
Brian in addition to the suggestions on power adapters listed above, I have another you may want to add:
Get a USB plug adaptor that converts USB data cables, into charge only cables.
The main benefit is that it is small and if you attach it to your own cable you will always be in charge only mode and can remove it only when you trust the other device and actually need data. If you leave it in your travel bag attached to your cable you will always be ready.
In the case that all you have access to is the male end of the plug (due to the setup of the charging station), you would have to fall back to carrying a power bank or carrying female micro/lightning/usbc to female usb adapters so you can place your charge only usb adapter in the middle.
I will post some sample Amazon links in a comment below (delete it if you see fit Brian, I am not into pushing products).
here are some examples of lightweight ways to protect yourself:
USB charge only adapter:
https://smile.amazon.com/PortaPow-Charge-Block-Adaptor-SmartCharge/dp/B00QRRZ2QM/
female USB micro to female USB (in the case you can’t access a usb port at a charging station):
https://smile.amazon.com/Electop-Female-Micro-Adapter-Converter/dp/B015PG6VU6/
Unfortunately, if you only have access to a male lightning or male usbc cable end, I don’t think you can use a female to female adaptor as those 2 specifications allow for 2 way charging and I think female to female adaptors violate the spec.
Or you could use the guys who kinda started the game 😉 …also cheaper! http://usbcondoms.com
Yikes. Me? Headed for my cave. Wake me when it’s over.
If I’m reading this article correctly one has to plug one’s phone into a specially-crafted public charging station for this exploit to work. Since I never use those and I only charge my phone from a wall outlet I feel like I’m not at risk.
That’s the jist of it! Don’t plug your phone’s data (and charge) port directly into untrusteded USB outlets.
If you have to charge in a public place, use the AC to DC power adapter that came with your phone. An alternative is to charge USB “backup batteries” instead of your phone directly (then later charge your phone from the backup battery.)
Could you also use a neutered usb power cable, as i read it only the data lines are of concern…barring that handshake to determine amperage.
Phones running the Blackberry 10 operating system will not be vulnerable to this,
since release the first release of the os the frame-buffer for the video output is not updated effectively pausing the video when a password box is selected
That’s great at preventing password leakage, but not useful against corporate data leakage the password is supposed to be stopping.
The first generation of BlackBerry 10 devices are also immune since the Z10, Q10, and Z30 all had a separate microHDMI port. Only the SlimPort compatible Classic and Passport would likely be affected.
The easiest solution is to just avoid public charging stations: after all is there any difference between them and taking candy from a stranger?
Just buy a “USB condom.” It’s a small adapter that has only power connections. So even if the port you plug into is set up for data, only the power gets through. Simple and completely effective.
iOS update in 3,2,1…
A few people suggested “charge-only” chargers, that disconnect the data wires.
Problem with this type of device is that it limits charging speed to the original spec – 500 – 750 mA/H, rather than the up-to 2.5A/H charging speeds that most modern phones enjoy. There has to be a data handshake to identify the fastest speed allowed by the device, otherwise it falls back to the slow speed.
Speed or security? Which way do you want to do this? Which one do you care about more?
There are a few other differences between MHL and regular USB micro plugs, including the depth, hook positions, and bulk surrounding the plug.
Just carry a power bank with you and never hook your device up to a random USB connector.
Tell me again how safe, secure, and invulnerable iphones are.
Tell me again how secure any smart phone is.
Tell me again how Clintons’ email server situation really doesn’t matter (while accessing it over her smart phone).
Tell me again about how 2fa or any os update can retro-actively secure my data from this problem and stop ID theft via diseased chargers.
As with sex, it’s best to use protection when plugging into an unknown port…
Option 1 when in doubt of charging station, power the phone off first.
Brian, wish I would have known you were at Def Con, would have bought you a beer. Met you in Portsmouth NH before. Maybe next year.
I am seeing convenient USB charging ports at many places around the community college i attend. I read that management is considering putting them into desks at redesigned lecture hall. Not too many secrets with college students but sometimes those facilities are rented out to big business during summer months and over winter holiday period.
I think this should be considered a non issue.
The phone explicitly asks you if you trust your charger to transmit sensitive data to.
From the message it’s very clear that if you press trust, the charger will gain access to your personal data.
Now anyone looking to charge their phone should know a charger does not need to access sensitive device data for power..
That’s exactly the issue with this attack vector though – it doesn’t ask at all!
Never had that message on my phones, iphone feature?
We will always be one step ahead.
Hi Brian
could this thing be also enabled in those new WIFI/Surveillance kiosks they are setting up all over NYC?
Seems to me a perfect deployment of those evil charging stations.
It is possible already to buy USB prophylactic devices which sit between a charger and the phone. These tap the power lines, but intercept the data lines on the charging cable such that data communication is rendered impossible… but yes, it’s always better to use one’s own charger.
A lot of folks have purchased generic chargers for their equipment. I suppose that is where one threat enters, although likely rare?
In addition to standard data (mass storage, MTP, PTP), video (MHL etc.), some phones also have additional diagnostic functions available via their data ports.
The ports on most modern phones go into a multiplexing device, and then this device switches which port gets connected inside the phone. Manufacturers can then, with a special cable, get access to diagnostic information and sometimes even a command shell.
If you can identify the handset, you could leverage these diagnostic functions as well.