In April 2016, security firm Trend Micro published a damning report about a Web hosting provider referred to only as a “cyber-attack facilitator in the Netherlands.” If the Trend analysis lacked any real punch that might have been because — shortly after the report was published — names were redacted so that it was no longer immediately clear who the bad hosting provider was. This post aims to shine a bit more light on the individuals apparently behind this mysterious rogue hosting firm — a company called HostSailor[dot]com.
The Trend report observes that the unnamed, Netherlands-based virtual private sever (VPS) hosting provider appears to have few legitimate customers, and that the amount of abuse emanating from it “is so staggering that this company will remain on our watchlist in the next few months.”
What exactly is the awfulness spewing from the company that Trend takes great pains not to name as HostSailor.com? For starters, according to Trend’s data (PDF) HostSailor has long been a home for attacks tied to a Russian cyber espionage campaign dubbed “Pawn Storm.” From the report:
“Pawn Storm seems to feel quite at home. They used the VPS hosting company for at least 80 attacks since May 2015. Their attacks utilized C&C servers, exploit sites, spear-phishing campaigns, free Webmail phishing sites targeting high profile users, and very specific credential phishing sites against Government agencies of countries like Bulgaria, Greece, Malaysia, Montenegro, Poland, Qatar, Romania, Saudi Arabia, Turkey, Ukraine, and United Arab Emirates. Pawn Storm also uses the VPS provider in the Netherlands for domestic espionage in Russia regularly.”
“Apart from Pawn Storm, a less sophisticated group of threat actors called DustySky (PDF link added) is using the VPS provider. These actors target Israel, companies who do business in Israel, Egypt and some other Middle Eastern governments.”
WHO IS HOSTSAILOR?
Trend’s report on HostSailor points to a LinkedIn profile for an Alexander Freeman at HostSailor who lists his location as Dubai. HostSailor’s Web site says the company has servers in The Netherlands and in Romania, and that it is based in Dubai. The company first came online in early 2013.
Ron Guilmette, an anti-spam researcher who tipped me off to the Trend report and whose research has been featured several times on this blog, reached out to Freeman via email. Guilmette later posted at the Ripe.net mailing list the vitriolic and threatening response he said he received in reply.
A snippet from the response that Guilmette said he received from a HostSailor employee named Alexander Freeman.
Perhaps Mr. Freeman’s ire was previously leveled at Trend Micro, which could explain their redaction of the name “HostSailor” from its report. A spokesperson for Trend Micro declined to explain why the company redacted its own report post-publication, saying only that “at the time of publication, we were following our standard disclosure protocol.”
In any case, I began to suspect that “Alexander Freeman” was just a pseudonym (Trend noted this suspicion in its report as well). In combing through the historic WHOIS registration records for the domain hostsailor.com, I noticed that the domain name changed hands sometime in late 2012. Sure enough, a simple Google search popped up this thread at Webhostingtalk.com back in Dec. 2012, which was started by a Jordan Peterson who says he’s looking to sell hostsailor.com.
Contacted by KrebsOnSecurity, Mr. Peterson said the person who responded about purchasing the domain was named Ali Al-Attiyah, and that this individual used the following email addresses:
ali.alattiyah@yahoo.com
ali.alattiyah@mail.com
hostsailor@hush.com
“I remember Ali telling me he didn’t have a paypal so a friend sent me the money for the domain, I looked up the paypal info for you and [Ali’s friend’s] name is Khalid Cook, masrawyz@yahoo.com,” Peterson told me. “The legal information for the domain transfer was given as:
152-160 City Road
London ec1v 2nx
UK”
That street address corresponds to a business named “yourvirtualofficelondon.co.uk,” which offers call answering services for companies that wish to list a prestigious London address without actually having a physical presence there.
Ali Al-Attiyah is listed as the official registrant of hostsailor.com and several other very similar domains. More interesting, however, is that email address given for Mr. Khalid Cook: masrawyz@yahoo.com. According to a “reverse WHOIS” search ordered from DomainTools.com, that Yahoo email address was used in the original registration records for exactly one domain: santrex.net.
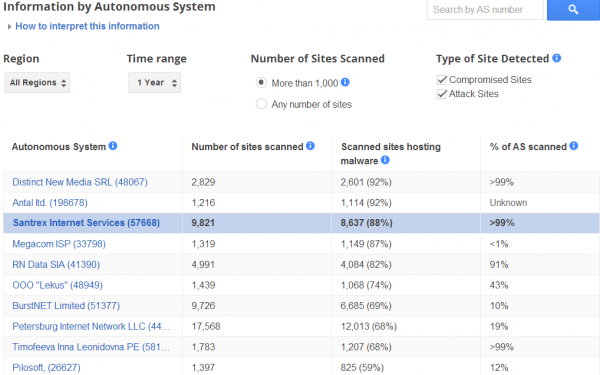
Santrex (better known on Webhostingtalk.com as “Scamtrex“) was an extremely dodgy “bulletproof hosting” company — essentially a mini-ISP that specializes in offering services that are largely immune from takedown requests and pressure from Western law enforcement agencies. At the time, Google’s Safebrowsing database warned that almost 90 percent of the sites on Santrex’s network were attempting to foist malicious software on visitors or were hosting malware used in online attacks.
Santrex was forced out of business in early 2013, after the company’s core servers were massively hacked and the PayPal and credit card accounts it used to accept payments from customers were reportedly seized by unknown parties. In its final days as a hosting provider, Santrex’s main voice on Webhostingtalk.com — a user named “khalouda” — posted many rants that eerily echo the invective leveled at Guilmette by HostSailor’s Mr. Freeman.
WHO IS KHALID COOK?
I began to suspect that Khalid Cook may also be a pseudonym. A few minutes of digging online unearthed this February 2013 Santrex profile at gidforums[dot]net, which states that Santrex first appeared in 2001 as a hosting company called connectpower[dot]net.
Alas, the original WHOIS registration records for connectpower[dot]net indicate that it was registered November 2001 to a Khalid Hemida, an individual who gave a physical address in Egypt and the email address botland@masrawy.com. This archive.org cache of connectpower[dot]net’s “Staff” page seems to confirm the organization’s presence in Egypt, saying ConnectPower customers living in Egypt can pay through one of the staff members, in cash. This page also reveals Hemida’s ICQ number.
A Google search on Khalid Hemida turns up at least two different connectpower[dot]net business listings which include the email address khalidhemida@hotmail.com, and which claim the Web site “botland.org.”
That Hotmail address appears to have been used to register a Facebook account for a user from Doha, Qatar who registered under the name Khalid Hemida but who is now using the name “Karam Khalid.” The account’s profile picture apparently was lifted from an issue of BusinessWeek, according to the image search service Tineye.com. A different Khalid Hemida account on Facebook belongs to an older individual who says he’s from Egypt and that his current town is Dubai.
But what of that “botland” reference — both the botland@masrawy.com address claimed by Hemida and the domain botland[dot]org? This cached page of botland[dot]org recorded by the Internet Archive in June 2011 references “an automated BotLending Channel,” run by at least four main users from Romania.
Botland was a channel on Undernet, a vast sea of text-based communities called Internet Relay Chat (IRC) networks. Botland was a place where people could download special bots designed to manage users and preserve order on an IRC server, but mainly to guard the channel from being hijacked by other users or bots. The reason I mention it is that Undernet in 2001 would have been the perfect place to meet new customers seeking dodgy Web hosting businesses.
To bring this full circle back to the Trend Report: I should note that if HostSailor is being truthful about where the company is incorporated — in Dubai — then it has long been facilitating the aforementioned Pawn Storm cyber espionage attacks against its own host country. For that reason, I imagine some government authorities within the United Arab Emirates might be interested in looking more closely into HostSailor and its operations.
For the record, I requested comment from HostSailor and from the various addresses listed in this story for Messrs. Freeman, Cook and Hemida. I’ll update this story in the event that any of these pings generate a reply.





Fabulous work as usual.
Best regards
Thank you for always being there to show us what is really going on out there!!!!
Honestly, though, what has ever come out of Trend Micro that has been worthwhile? I’ve never considered them a reliable source for anything given the quality of their products.
Apparently Khalid’s new pseudonym is “Amy Iracrop”.
My thoughts as well. I’ve used Trend to good effect before, so I think there is something going on with the poster rather than the anti-virus. I love the fact that malefactors get on here to defend their actions. Makes me feel even better about readying Mr. Kreb’s reports.
Makes a halfway decent anagram for “I am crappy.”
Anagrams to “Roam Piracy” (and “Pricy Aroma”)
Great work as usual Brian
Good work Brian. Also Trend Micro is terrible, they’ve always been terrible. This is not news to anyone who’s been in the IT field for any length of time. The only good thing about that software is the uninstall icon. Also, I love these Russian (or whatever) keyboard warriors. I imagine them in a smoke filled room, all gray and dreary looking, all of them have bad hair cuts, and there’s vodka and cigarettes everywhere.
Some of us drink tea
And from glasses, not teacups….with lots of sugar, sometimes its almost like syrup.
I’ll stick with the Vodka, thank you. You can drink that from a glass.
Awesome article, Brian. Thank you for your research and insights!
Great work Brian!!!
It is perhaps worth noting that Host Sailor, Ltd. (AS60117) is only connected to the Internet via its connections to just two other Internet companies, i.e. NForce Entertainment B.V. (AS43350) of Roosendaal, The Netherlands and M247, Ltd (AS9009) of Manchester, United Kingdom. I’d like to believe that each of these two companies has just been entirely ignorant of the goings-on at their customer, Host Sailor, but my own research has suggested to me that Host Sailor may not be the only dodgy customer of either of these two upstream providers. There may perhaps be a pattern here.
I’ve known M247 Ltd (in a professional sense) for many years. They are a reputable organisation – I’m sure one of their team will pipe up on here eventually but I’m absolutely certain that they aren’t ‘dodgy’ in the way that you describe.
It took them about 48 hours to kick me off a HostSailor VPS for port scanning a few months ago, so they’re not as bulletproof as all that. They’re no Ecatel, if you ask me.
How did they know? Abuse reports or?
unlucky! i’ve scanned 0.0.0.0/0 on Azure, AWS and DigitalOcean with not a peep.
@Brian In the tags of the article, you got the email address of Khalid wrong: masrawzy@yahoo.com. It should be masrawyz@yahoo.com, so the y and the z are the wrong way around.
ok thanks, Sandra.
Nice digging Brian, always worth the time to read your work!
Wow. Undernet in 2001. Talk about a blast from the past….
One might say that was the golden era of IRC.
Windows XP was released that year.
I hope everyone appreciates the personal safety risk you take every time you out someone like this. Let’s pray that SWAT does not show up again.
cool……more addresses to filter out.
Oh popcorn! I cant wait for a follow up of the “legal team” which hopefully comes and involves some bigshot lawyers.
The practice has a name SLAPP:
https://en.wikipedia.org/wiki/Strategic_lawsuit_against_public_participation
And I wonder how a US company like TrendMicro can give in and censor their own publication instead of fighting. (unless they dont have enough proof?)
I had a gangster do this to me for 3 years and it cost him 250.000 € and in the end he lost 🙂 Injunctions, private detectives, lawyers, all because he didnt like what was written…and true.
Very nice investigative work, Brian. I do the same thing from time to time for my clients.
Anyway, crime-friendly hosting providers are not really anything so rare and special, are they? The web of deception and the angry rant are exactly what we can expect from such characters. We should track them down and administer the professional help they need and deserve…
And by the way, I have used House Call from Trend Micro many times in the past so I know a little about them. But this reminded me that I have had to block a large number of IP ranges that appear to be assigned to them because we were getting a lot of PPC click fraud from them.
Yeah, we are blocking all of 150.0.0.0/8. I know not all of that is assigned to them, but 150.70.188.* is one example connected to trendnet.org. In my database I have about 505 examples of attempted or successful click fraud from the past year. From looking at their site it seems like what they provide to protect users may be functioning as a proxy service and that may explain the abuse. Funny. What’s that saying, “Tend to your own garden”?
I hope you will provide more coverage of PPC click and conversion fraud in the future. It doesn’t get much press these days.
I first found out about HostSailor from my SSH honeypot logs 😛
Irony
Host Sailor also recently had whole network blocks largely or entirely given over to hosting the Angler exploit kit..
131.72.136.0/24
http://pastebin.com/pDbhvsNE
131.72.139.0/24
http://pastebin.com/xzam5g2W
185.45.193.0/24
http://pastebin.com/spVuwdSU
185.117.73.0/24
http://pastebin.com/G1CrNYcm
185.117.75.0/24
http://pastebin.com/Nuc7mv9p
185.118.66.0/24
http://pastebin.com/Cb0q2XJE
185.141.25.0/24
http://pastebin.com/mHu7S8Ak
Thank you for this article. Now it makes more sense.
Hostsailor is also hosting terror group ISIS/ISL material on at least 3 servers and they refuse to suspend.
Not another blog post about cyber-attack facilitators in the Netherlands. I think you should change your website to Krebs on cyber-attack facilitators in the Netherlands. ….zzzzzzz
Show how often you show up here. =Þ
Pay to move the crooks, or pay to make the Netherlands a more safe cyber arena.
=X
Fortunately, or unfortunately, Reality is what it is. All we can hope for is a better understanding of facts.
FBI: Smart Meter Hacks Likely to Spread. Are there any tools available for the novice to detect smart meter exploits? There is someone who using the smartmeter at my home and work to cause all type of problems. I can not convince the IT staff of it maybe they don’t have the IT security skills to unstand and TAKE IT SERIOUSLY. They locate the place go into the smart meter and then advance to the HVAC system increase the voltage which is not being obeserved, and then connect to ANYTHING with VOLTAGE supplied to it. They’ll run the devices till it burns out or put it in continous loop mode to see what other things they can cause problems with.
“I can not convince the IT staff …”
In other words, you aren’t the boss ?
You need an electrical engineer to diagnose what is going on; power-monitoring equipment will be installed to see what is on the power lines. Voltage fluctuations are not unusual; your location might need surge suppressors installed, and/or voltage-regulating equipment, and that is expensive. The controls for your HVAC might need replacing.
“They locate the place go into the smart meter and then advance to the HVAC system increase the voltage which is not being obeserved, and then connect to ANYTHING with VOLTAGE supplied to it.”
Uh, no, they don’t. They could connect to the smart meter. Their connection would end there. Unless your HVAC system is owned & managed by your power company and has been connected to the same network that your smart meter has been connected to (translation: a snowball’s chance in hell), then there’s no way for them to jump from the meter to it.
Even if your HVAC has an IoT connection, that’s going to use your internet connection, not the power company’s IP-over-powerline connection.
Look at it this way: Why would the power company to provide free bandwidth for HVAC units they don’t own and operate?
Can a smart meter adjust line voltage? That seems more a function further upstream. Unless your org has its own generation system i suppose.
You have no idea what you are talking about. Smart Meters have the ability to open or close the circuit, and monitor usage, nothing more. They cannot alter the voltage in any way.
Some utilities do offer a discount for allowing them to install disconnect devices on HVAC systems. These work by switching off the condenser for a given amount of time (typically 15 minutes every hour). These can be triggered via many methods – old fashioned one-way pager networks, or various Smart Grid-connected methods, either direct or via ZigBee protocols. But again, neither one of these methods allow for anything other than a method to open and close the circuit.
Source – I work in IT for a utility with all of the above and directly support the comms for these devices as well as their security.
This is not adding up. Lot’s of people are apparently happy with the HostSailor service. If they were as bad as this story makes out, I can’t see how that could be. They’d have dirty IPs which would eventually make legitimate users unhappy and word would get around. In other words, something smells funny here.
I have no personal experience as I’ve never used HostSailor, but would note that all providers are constantly battling with bad clients because it causes them problems. It’s an ongoing problem in the business and unless there’s some other flow of money that we can’t see, it’s generally not profitable to have spammers on your servers.
Anyway, I’m looking forward to seeing how this unfolds. I do have some faith that Brian will be diligent in sorting it out.
As a current user of their services, I must say that I’ve been extremely happy with their customer support. They happily migrated me to different virtualization and bigger plans with cost of only the difference between the plans. Billing cycle also began from start each time I upgraded.
Negative about their service is the somewhat slow internet speed and that they turned off my services several times and because it was too resource hungry. I got notification of the shutoff only afterwards.
Fantastic article. Fantastic. The cheek of these crooks is just appalling
In regard to the HVAC comment(s), everyone who reads this blog is likely more informed than I am. That said, take a look at these links:
https://www.pge.com/en_US/business/save-energy-money/energy-management-programs/smartac/smartac.page?
https://www.pge.com/en/mybusiness/save/smbblog/article/boost-your-hvac-systems-brain-with-advanced-digital-economizer-controls.page?redirect=yes
Sorry, didn’t see get Krebs, but interesting news story on cbsdfw, about skimmer there. Bluetooth.
How hard is it to form a coherent thought that is based on the subject matter at hand?
And again, right on point with the subject of bullet proof hosting, comes this story from Jim; http://dfw.cbslocal.com/2016/08/04/crooks-using-bluetooth-to-steal-at-gas-pumps/
And these would be the same kind of skimmers Brian was reporting on back in 2014.
Love the piece and the detailed exposure…not to mention the serious cojones you have Brian. Well done!
HELLO NFORCE.
When will you wake up and kick these guys out?
WAKE UP NFORCE.
Accepting money from people making dirty money makes you earn dirty money.
Also i wanted to add that lots of booters on hackforums have servers from hostsailor.
Krebs: this comment form submits to http. Should fix other urls as well in the content.
I suspect that, while part of this research is based on things that are/were true, it might be targeting the operators of the hosting provider a bit too hard.
I am a client of hostsailor.com, and I can tell you they *definitely* forward abuse complaints, and they *definitely* shut down your VM if you do not deal with it properly.
If you look at their pricing, you will see they are dirt cheap, even cheaper than digitalocean in a lot of cases. These dirt cheap providers are magnets for criminal activity because, not surprisingly, the criminal actors are not going to sink a bunch of money into something that is ephemeral.
If I’m wrong, and these guys are facilitating illegal activities, by all means, hook me up with who to contact because it has *not* been the case for me thus far.