The U.S. Secret Service is warning banks and ATM owners about a new technological advance in cash machine skimming known as “periscope skimming,” which involves a specialized skimming probe that connects directly to the ATM’s internal circuit board to steal card data.
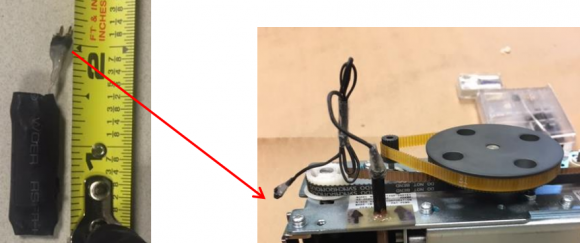
At left, the skimming control device. Pictured right is the skimming control device with wires protruding from the periscope. These were recovered from a cash machine in Connecticut.
According to a non-public alert released to bank industry sources by a financial crimes task force in Connecticut, this is thought to be the first time periscope skimming devices have been detected in the United States. The task force warned that the devices may have the capability to remain powered within the ATM for up to 14 days and can store up to 32,000 card numbers before exhausting the skimmer’s battery strength and data storage capacity.
The alert documents the first known case of periscope skimming in the United States, discovered Aug. 19, 2016 at an ATM in Greenwich, Conn. A second periscope skimmer was reportedly found hidden inside a cash machine in Pennsylvania on Sept. 3.
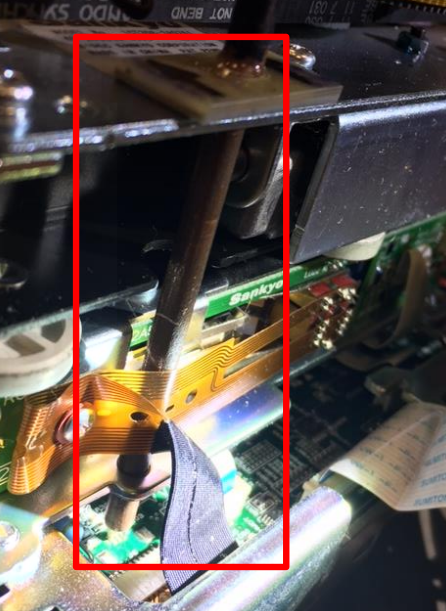
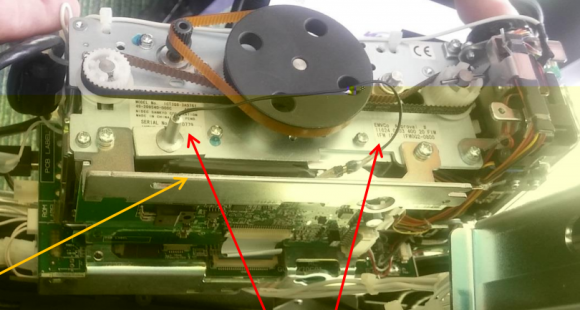
The task force alert notes that in both cases the crooks were able to gain direct access to the insides of the ATMs (referred to as “top-hat” entry) with a key. The suspects then installed two devices connected together by wiring. The first device — the periscope skimming probe — is installed through a pre-existing hole on the frame of the motorized card reader.
The probe is set in place to connect to the circuit board and directly onto the pad that transfers cardholder data stored on the magnetic stripe on the backs of customer payment cards. The probe is then held in place with fast-drying superglue to the card reader frame.
According to the Secret Service, the only visible part of this skimming device once the top-hat is opened will be the wire extending from the periscope probe that leads to the second part of this skimmer — called a “skimming control device.” This second device contains the battery source and data storage unit, and looks similar to a small external hard drive.
As I’ve noted in previous stories in my series All About Skimmers, the emergence of this type of skimming attack is thought to be response to the widespread availability of third party anti-skimming technology which is successful at preventing the operation of a traditional skimmer placed on the outside of the ATM.
The Connecticut task task force notes that authorities there did not find hidden cameras or other methods of capturing customer PINs at the ATMs compromised by periscope skimmers, suggesting these attacks involved mere prototypes and that the thieves responsible are in the process of refining their technology.
Nevertheless, crooks who are serious about this type of crime eventually will want to capture your PIN so they can later drain your debit account at another ATM. So it’s important to remember that covering the PIN pad with your hand defeats the hidden camera from capturing your PIN. Occasionally, skimmer thieves will use PIN pad overlays, but these are comparatively rare and quite a bit more expensive; hidden cameras are used on the vast majority of the more than three dozen ATM skimming incidents that I’ve documented here.
Shockingly, few people bother to take this simple, effective step, as detailed in this skimmer tale from 2012, wherein I obtained hours worth of video seized from two ATM skimming operations and saw customer after customer walk up, insert their cards and punch in their digits — all in the clear.
Many readers have asked whether the incidence of such skimming scams will decrease as more banks begin issuing more secure chip-based payment cards. The answer is probably not. That’s because even after most U.S. banks put in place chip-capable ATMs, the magnetic stripe will still be needed because it’s an integral part of the way ATMs work: Most ATMs in use today require a magnetic stripe for the card to be accepted into the machine.
The principal reason for this is to ensure that customers are putting the card into the slot correctly, as embossed letters and numbers running across odd spots in the card reader can take their toll on the machines over time. As long as the cardholder’s data remains stored on a chip card’s magnetic stripe, thieves will continue building and placing these types of skimmers.
Also, the thieves conducting these periscope skimming attacks don’t necessarily need a key to access the ATMs. As I’ve noted in past skimming stories, crooks who specialize in compromising ATMs with malicious software often target stand-alone cash machines that may be easier to access from the top-hat. My advice? Stick to ATMs that are installed in the wall at a bank or otherwise not exposed from the top.
Most importantly, watch out for your own physical safety while using an ATM. Keep your wits about you as you transact in and leave the area, and try to be keenly aware of your immediate surroundings. Use only machines in public, well-lit areas, and avoid ATMs in secluded spots.




If I had been this talented while studying engineering, I’d still be an engineer. I guess where there’s a will there’s a way – thanks for keeping us update brian
I guess that once ATMs are converted for chip-use rather than reading the mag stripe, then I can demagnetize my stripe.
My local bank ATM already handles chip cards. But, somewhat weirdly, it still wants you to insert and remove your card first – so it can read the stripe. Then it tells you to reinsert and leave it in. I haven’t yet figured out why they do that.
It will be years before the Chip-N-Pin system dumps the mag stripe. Until absolutely ALL point of sale devices no long use mag stripe this will still be with us.
I’m not sure that will ever happen, where plastics would have no mag stripe. Unlike the rest of the world, U.S. payments infrastructure is not broadly wired to accept real time chip and pin payments for all credit cards and the banks instead opted for chip and signature system where you do not necessarily need the live network connection between the POS terminal, the acquirer, the association and all the way back to the issuer (bank), like you’d need for a true real time pin authentication. Tokenization could help here, where the buck woful stop with the clearing house, without the need to go to the bank, but would not resolve the issue for all payments.
With the advent of contactless mobile payments, I doubt anyone will bother building this infrastructure out. By the time they would complete this, mobile payments would be much more prevalent and most of us would have our cards loaded into our phones (or whatever comes next in the post-iPhone era) and have our plastics somewhere in the drawer at home, collecting dust.
Actually, from what I understand, the Chip and Pin process was designed to work over in Europe long ago when real time connection to a bank could not be counted on (even more behind the time at the time than us).
The unique thing about the Chip n Pin process is that the PIN is not sent over the network and validated directly with the bank for each transaction. The PIN actually resides on the chip on the card and when you enter your PIN the machine is verifying against the card itself where the PIN is stored.
The reason we have Chip and Signature here in the U.S. is that PIN based transactions don’t take as big a service fee on the transaction as Signature based transactions. And given the choice between significantly increasing security by going with PIN or getting better profits with Signature (all happening after the Target fiasco), the banks went with Signature (and profits).
Not accurate for ATMs. An ATM authorisation is always online and the PIN is sent encrypted and validated at the host.
Considering they still emboss the name and numbers so people can impress the cards onto paper…that mag stripe may be here for a very long time.
(I was pondering my new chip-equipped ATM card still having embossed characters when I activated it this morning.)
My Costco citi card does not have raised numbers and letters. My understanding is that the paper credit card machines were outlawed years ago.
Outlawed? What do you think they use when the net goes down?
Keypad to enter the data
No keypad, just good old pen. At least, that’s what happened when the power went out in my favorite restaurant and they needed my non-embossed card number for a paper slip.
Barter. When the net goes down the supposed money in your account will have no real value.
That’s why it’s always best to have trade goods available. I like to have close by some high quality 16 to 20 yo scotch for just such emergencies.
A place I was at was forced to use an old impress machine when their normal terminal was damaged. Merchants are discouraged from using them because it shifts all liability to them, not just for disputes, but for invalid cards and declined transactions.
I work for a retail chain that delivers large loads of product to a work site. Sometimes the drivers take payment via a card-imprint device they carry with them. So, yeah. It happens. (They may do a manual card entry on the POS terminal back at the store. I’ve never witnessed the transaction, only heard of it.)
With the wide availability of smartphone based card readers, this seems rather primitive.
Relatively few shops or stores have smartphones owned BY the store or shop or whatever. They have employees who have personal smartphones, of course. But in no way shape or form would any smart business begin running financial transactions across an employee-owned device, and no employee of such a place should allow it. The liability risk is way too high.
And if I was a customer there, I would not want my card anywhere near a card reader attached to the phone that belongs to some anonymous employee.
I can see how that would discourage them, but what’s the alternative – especially if the network goes down in the middle of a busy lunch/dinner at a restaurant?
I was at Applebee’s when it happened. No cash on me, so I couldn’t pay for the meal via any other means than plastic. And for “new” customers walking in during the outage, what’s less damaging to profit: turning away card customers so you don’t lose out on some food costs, or copy the card in hopes it clears when everything’s back up and running?
If 5% of the customers’ cards were bad, would they still have made more money than if they’d turned them away? Genuine series of questions, I’m not well-versed on statistics, business economy, etc.
No, they are not outlawed. Many businesses still have the old imprint devices for use in the event that their credit card link via the phone line goes down, which does happen. It’s pretty scary, but it’s still out there.
Last year, I ate at Applebee’s. They were having network issues, couldn’t accept card payments. They got out the old-school carbon paper card copier. It was hilarious!
Or, they’ll phase magnetic stripes out even with some stragglers. We should not have to wait for a few idiots to catch up.
If you have a chip card, the magnetic stripe is useless and only contains a message that you have to use the chip.
The other big issue is the hopelessly outdated and insecure operating system deployed by people who would never imagine that someone could try to hack the OS…
Walmart did not make the change to chip readers at its locations all at once. For a while, I had to swipe at one location while I had to use the chip at another location less than 10 miles away.
I believe there is a field on the magstripe that can be set that tells the terminal that the card must be used with the chip if the terminal is chip-enabled.
The stripe has no idea whether or not there is a chip on the card. Has/does not have a chip determination is made by the switch responsible for authorizing the transaction. The bank’s switch knows which cards have chips. Otherwise people would just write magstripe cards that claim to have no chip.
Not true, even chip cards can be swiped. There is a ton of fraud going on right now with people counterfeiting chip cards onto mag cards without a chip, then swiping (after a fake attempt at reading a chip that isn’t there).
Yes, you are correct. You can swipe any chip card without using the chip.
It is not clear what you are trying to say.
If a card reader is chip enabled and setup properly, it should decline a swipe and force you to insert your card for the chip read. This is how everyone I’ve used and seen has been setup.
On the other hand, if a card reader has not had its chip feature enabled, then yes you can swipe your card.
Me,
That has also been my experience.
Perhaps you should read the thread of messages so that you understand what is being discussed.
Problem is that reading the card data is not the issue here. A crook must be able to use it, and they won’t, as the data on the magnetic strip is not enough to create a chip-clone as some information is only in the chip and not on the strip.
Also as discussed new terminals won’t accept a swipe when the card has a chip. So a crook would have to use your data to make a chipless clone card so terminals won’t reject the swipe. It is not clear though whether that is possible, as even if you can fool the terminal in thinking that the card does not support chip (and hence not just clone, but modify the magnetic data by removing the original indicator this card has/had a chip), the bank itself can also reject the transaction as it knows the card had a chip.
It is not unlikely that these attackes are merley exploiting the fact that it takes time for merchants to switch and will use the cloned cards at terminals that they know won’t support chip yet. That however also means, this type of attacks will fade out.
Last, placing these readers at an ATM is an inside job and hence very risky. It requires both insiders at the ATM vendor and ATM service company. It is likely they will rather use their ‘skills’ for a different attack.
What you’re looking for is called a Fallback transaction. If a chip transaction fails, AND the issuing bank specifically allows fallback, then the bank will allow the merchant to ‘fall back’ on magstripe for a card the bank knows has a chip if the PAYMENT NETWORK sends the transaction to the bank with a Fallback transaction code.
This is a short term solution to lots of merchants having enabled EMV but lots of them having poor solutions that either truly don’t work or still have bugs to work out.
You won’t see fallback allowed forever. It’s an intentional temporary loophole to ease the transition.
“Also as discussed new terminals won’t accept a swipe when the card has a chip.”
Not entirely true for all terminals. At Lowes, I had to insert my card, hit the option saying US MasterCard. Then the machine instructed me to remove the card and swipe it.
It completely depends on the credit card terminal, if it is programmed to authorize EMV transactions or not. Just because it has a chip reader to insert cards, does not mean the CC terminal is programmed to use it.
If it is programmed and EMV ready, it will ask you to insert “dip” your chip card every time. Even if the CVM changes.
There is a hack on the mag stripe that tells the reader this card does not have a chip and processes the transaction as a mag strip transaction…. subject to tampering…..
You are incorrect. The full data is still on the stripe. If you have a chip AND the reader is chip enabled then the payment network switch will tell the reader that it must use the chip. If the reader is not chip enabled then it will run as a normal magstripe transaction. The stripe has no idea whether or not there is a chip on the card. That decision is made further up the line when the bank is asked to authorize the transaction.
The reason you have to insert it first is that with dip readers it first reads the stripe, attempts an authorization, fails because the payment network returns ‘this card has a chip so use it’, and with that knowledge in hand the ATM tells you to insert the card again and this time it deploys the chip reader. Motorized readers that pull the card in do not have this issue because they still have possession of the card after they have run the stripe over the reader. I’m sure we’ll see smarter dip readers that detect the presence of a chip in the near future.
Why do ATMs still require that you insert your card where it is held inside during the transaction. Some of the small freestanding independent ATMs just have a swipe slot that does not require relinquishing your card. I am not suggesting that these cannot be fitted with skimmers, but users are less likely to walk away from the ATM, leaving it for the next person to make a withdrawal from their account.
5/3 Bank recently reprogrammed all of their ATM machines to require that you remove the card before getting cash. In the past, if you didn’t take your card, it would suck it into the machine and typically shredded later. Once the card is ejected, you need a PIN to get cash.
I have seen some ATMs designed with Contactless interface to avoid the insertion, I suppose they can do this because PINs are sent online to the Bank for ATM transactions (vs. POS where the card checks and validates the PIN).
I remember when ATMs first came out – the process was:
-insert card
-key in PIN
-request cash
-remove cash
(many people then walk away)
-return card
It didn’t take them much more than a year to change the order so that the card was returned prior to the cash being dispensed.
In any case, when I pay for parking, I wave my card at the machine, I don’t have to insert it. This is how ATMs should work.
I disagree, Craig. I will never use nor accept from an institution a card with non-contact capabilities. If someone is going to steal my information, they have to access the physical card rather than walking by me at a range of 1-8 feet.
I agreen with William. Who needs a skimmer when all you need is a radio antenna?
That just isn’t how EMV chips work. They do not transmit your card data. The chip does not contain the same information as the magstripe. If the chip is hooked up to an authorized payment terminal that has a secure connection to the bank’s authorization switch then the chip spits out a ONE TIME USE cryptogram, which is encrypted obviously, and can only be read by the bank. The bank returns a ‘yes we will process this payment’ or ‘no this is no good’ answer, not the card info.
EMV chips will not just talk to some dude with a radio receiver.
I swear 99% of the reasons people give for fearing EMV in all its forms, they just made up on the spot.
Someone with a contactless reader in a “ready to read” transaction started state can pull information from a contactless card in clear but not the CV2 number so IMO it’s not all that useful unless you can find a website that doesn’t require that (and there aren’t many). The chip can’t be cloned effectively AFAIK so even if you pull the card number (PAN), expiry and issue number plus a few other EMV tag values, I still can’t see a real world problem. Plus, any skimmer would most likely fail due to card collisions (only one contactless card can be read at a time), unless they write their own reader firmware – and that is very far from trivial.
I don’t see why having a magstripe is an issue once a bank finishes their chip rollout. Sure, the stripe with the card data is there, as is the magstripe reader, but they should be able to disallow transactions from chip-capable ATMs if a chip isn’t present/validated. This would force cloners to use an ever-shrinking pool of non-chip ATMs (or hack a chip-capable ATM to report it’s not chip-capable, something which should be cryptographically protected too). Once there’s a critical mass of chip-enabled ATMs, issuers can simply reject transactions w/o chip.
Ever bought anything online? No magstripe or chip required. Not allowing purchases where there is no chip would cause major issues for retailers. May work for ATMs but not for all use cases….
When you buy something online it requires the cvv2 which is printed on the back of the card but is not part of the data in the magstripe.
Not always the case. I personally interact monthly with two over the telephone payments monthly where a clerk manually inputs my cc number and expiration date, that require NOT want the cvv but DO require some specific address information.
Yeah, the cc number is a bit like a PIN except it is helpfully printed on the back of your card.
Genius.
Got a to-go order of pizza last week from a major US pizza chain. Paid with a Debit Visa. The clerk took the card, swiped it, keyed in the total due, handed the card back to me and ASKED me to read the CVV to him.
I’ve never ever been asked before to read off my CVV. Apparently they are running these sales as “card not present” even when they ARE present.
Freaked me out.
it’s funny how they can hijack your card and pin and then go and “drain” your account but while I’m out traveling, my bank freaks out if I try to pull out over 100 bucks!
I hear that…
I purchased a cup of coffee at a well known Pro Audio center here in Indiana. It was 50 cents. Within 5 minutes I received a call from my bank verifying the transaction. Can’t imagine what flagged it.
Some card companies have an anti scam system based on past behavioral patterns; until someone invents an artificial intelligence machine that can tell the difference, these alerts will happen with those systems – Personally I like it when it happens, because I know they have my back!
I once had a teller tell me the POS would not take my card until the card bank on the telephone would clear me. They handed me the phone, and surprisingly the bank person could recognize my voice and knew it was me, and that is all she wanted. I just love small town banks!! Everyone knows everybody else!! I must admit, I was in a store I normally never shop in, and was buying some unusual items, so I think that was the flag for the alert.
I would say that is usually the case, but I’ve seen and heard many stories where the thief was able to take out large sums of money in the hometown where the victim lived or shopped. Maybe they have an inside source that assists?
So….my mate went to a bucks’ night party in Vegas. He spent about 3 days going wild.
The day he got home, he got a call from his bank – “our analysis shows that recent transactions on your card were fraudulent, somebody has been misusing your credit card number in Vegas, we’ve reversed all the transactions”.
Brilliant. He took the “bank error in your favour” approach from Monopoly to that little dilemma…
That’ll last until they get the signed slips showing it was indeed your friend.
The reason for this is because audio shops are some of the first place low lifes go to cash in their crime rewards. The first thing these idiots do is put gigantic subwoofers in their car. I am all for a good subwoofer like a JL audio, but these guys are just going for quantity over quality with your stolen money. That makes me angry that people would even put anything less than JL audio in their cars!
It usually happens because scammers usually test cards with auths for a few cents to verify that the card works before going to town on it. Perhaps it appeared to the system as one of those testing trans.
Your bank interpreted the tiny amount as a test of a stolen card to see if it was any good.
When I use my credit union debit card, I get an immediate text message from them informing me of the transaction. In a restaurant, I can tell when the waiter has slid the card.
My BofA card will let me know after three or four hours. Not quite as helpful.
My card was skimmed by a taxi driver once.
He then started charging medium amounts ($60-$100) to it on an infrequent basis. It took me about 3 months to realise because the charges looked exactly like regular ones as per my normal use.
The bank eventually agreed to reverse the charges, but they asked me, “why would he only steal small amounts?”.
Surprised they’d ask that question. Smaller amounts are easily missed as you stated yourself, so if they can pull a consistent $60/month out, you might not think anything of it, and meanwhile they’re having a good time with your money (but perhaps not “great” haha).
50 cents is a flag. Often crooks try numbers with small numbers first before going for big bucks.
I once had the bank (credit union actually) tell me that for values less than $10 (I think this is correct) the bank can’t reverse the charge – so if the crooks take enough of those the bank can’t take them back – happened to my mother-in-law.
I vote for skipping the US integration of the chip card that requires the mag strip in lieu of contactless atm access… who doesnt have a smartphone these days
Then they would have to allow Android Pay on rooted phones…
All my phones are rooted, and as a result, Google does not allow the use of Android Pay.
And disallowing rooting of a device that I own is of course never acceptable.
Ah, me, for instance.
My bank implemented something nice. You place the ATM card into a slot sideways from normal (long side of card flat against the front) and it draws it into the machine. Then, while it’s inside, it mechanically moves a reader sideways across the stripe. There doesn’t seem to be any place to put a stationary skimmer that will “see” the entire magnetic stripe – unless the scammer can attach it to the moving mechanism inside.
Since the machine is mounted into the brick wall of the bank, I feel pretty safe using it.
If you look at the photos, the skimmer mentioned in this story hooks up in-line with the card reader, between the component reading the stripe and the ATM itself. As a result it has access to the raw data coming off the stripe and you can insert the card any direction and so long as the card reader in the machine can read the stripe the skimmer can read the data.
For skimmers that rely on their own read head to skim the card for data, the sideways card insert defeats it. But for something like this it wouldn’t.
Correct, but against inside jobs you cannot really defend.
To me, that is the real story: insiders at the ATM service or money refill company and people from the ATM business themselves that create these skimmers.
Once inside, you can probably find out dozens of other ways to get the data. The real story is how it is possible these insiders don’t get caugth more frequent.
Or maybe they do but it is kept quiet for obvious reasons …
Anyway that is what I ‘m eager to get storries on!
Brian, ATMs have to secure spaces, the top, which is where a lot of the electronic and mechanical components are located, and the bottom, or vault, where currency is stored.
I do not believe the area accessed by these crooks was just an enclosure above the ATM, but rather, the “top” section described above. This would indicate that the bad guys did have a key to access this part of the machine.
I don’t even remember the last time I used an ATM machine. I’m reading things that give me a sense that I’m not alone. Even after getting a little cash from a branch which is rare in itself for me(just in case), a $20 bill could sit in my wallet for weeks at a time. Won’t people stop using cash as much before ATMs stop requiring mag stripes on cards?
My card was eaten once, and I didn’t bother getting it replaced for about 2 years.
My current card expired 3 months ago.
I can’t even remember last time I had used it anyway.
Petrol, smokes, food, road tolls, hookers, it’s all on cards, no reason to have any cash, unless you want to encourage panhandlers who are the only ones left these days to not take payment by card.
So, you never use your card at all, but you use it all the time? I am very confused how you can go “2 years” without a card while at the same time using it for all your shopping (avoiding cash).
Why do none of these ATMs have tamper sensors? My $100 home alarm panel has a tamper sensor that sets off an alarm anyone tries to open the case.
People are alot more concerned about wether or not the ATM runs WinXP. No one can be bothered with something so simple.
These things are almost certainly an inside job. Either at the service company, refill company or at least the vendors that create teh hardware/software.
E.g. the ATM service guys need to be able to get in so can disable the tamper alarm. Then they can also connect the spy-device. And on the next service, they remove it again.
I’m not claiming it is the service guy, but it almost certainly must be an insider job unless the only raided terminals are the open ones at gas stations. But then still someone must have knowledge that model A hardware is used at terminal X, so they know it will work with their spy-device.
You might be right on this. If your correct, then it really makes no difference what OS it runs. But then, the world goes nuts if they are told about ATM machines running XP. But then, it doesn’t matter. But then the world goes nuts over it. As if it would be any different if every ATM on the planet ran on Mac.
If your correct on this……
They surely do have tamper sensors, but from that starting point it depends a lot on whether the ATM is a cheap free standing cash dispenser or a thru-wall at your bank. After that, the only question that matters is whether anyone is monitoring the tamper notifications.
Brian, thanks for this update!
What if banks add a one-time sms pin option? It wouldn’t necessarily require new hardware while increasing the bad guys’ cost.
that’ll happen right after the banks are held directly accountable for losses instead of passing them off to someone else
My bank has a thing where you use your phone to log online to their virtual ATM, tell it where you are, tell it how much you want, and it sends you an AccessCode.
Then, you go to the ATM, select the “no card withdrawal” option, enter your access code, and take your cash.
I haven’t tried it yet, but it seems like the way to go.
Do you mind providing the name of your bank?
When I worked for Diebold doing maintenance on their under-contract ATMs, the only electronics outside of the safe was the cabling, video monitor, and of course the card scanner.
If one could breach the door, the scanner was in plain sight and easy to quickly access. Every door to each building or shed was keyed alike.
An attacker would have about 3 minutes before the police responded to the motion-detecting alarm breaching a door would cause.
We had one tech on his honeymoon in the islands and to satisfy his curiosity, he tried the key in the door’s lock of the building that contained an ATM. The key worked.
For the curious, we did have a “duress” code.
I think two things are relevant. US Issuers need to update their authorization systems quickly. An EMV chip card tells the Issuer that it’s an EMV card. So if Issuers take that additional data into consideration, then any mag stripe transaction on an EMV terminal should be declined. For non-EMV terminals Issuers should carefully watch the data they get. Does the merchant location coincide with the last known location? If a cardholder suddenly only performs magstripe transactions they can prompt the merchant to inform cardholder to reach out to the Issuer.
the second thing is. US public should start to get used to a cashless society. The less cash money, the less need for ATM’s. And ATM owners should configure ATM’s in such a way that they prefer EMV card over magstripe. The less fallback to magstripe, the better.
I am falling back to cash as much as possible, not the other way around. Every time you use your credit card there is the risk of someone capturing the number due to an infected POS system.
And for that matter, the credit card companies each collect a percentage of each transaction, and this just doesn’t seem right to me. For that matter, they also sell information about you to whomever they wish.
Cashless seems like a huge nuisance to me. I can’t count the number of times I have been stuck in line behind someone who wants to pay for a bottle of soda with a credit card, and they have to run the card, print the slip, have the customer sign, and then stick it in the register, and hand the customer the real receipt.
that’s all well and good, until you lose your wallet or you want to make a large purchase. I’d much rather carry around a zero fraud liability credit card than a couple grand on my person.
Cashless Society?
So we should force every merchant to absorb fees, even for the smallest transactions?
And how do I buy anything from a private party without cash? Cars, garage sale fodder, or anything else.
The cost of accepting CC is the cost of doing business. Plain and simple. If you want to transact payments online, build that into your business plan.
When all ATM-operators have adopted chip only and abandon the magnetic stripe this problem will be reduced greatly. The true and long term problem is the use credit cards and the unsecure card number as a means of obtaining cash or online purchases.
When we have an all chips based system, the bandit will work to find other ways of tampering with the ATM and or our credit cards. It is important to move away from cash and the present card infrastructure where all necessary information to make online purchases is on our credit cards.
We should move towards a payment infrastructure where cash is not the predominate means of payment and build a infrastructure that will substitute the unsecure credit card number with secure one time digital tokens. The tech is out there – we only need to adopt it.
Yes, it is a long way to go, but that only stresses the importance of beginning the journey now. Less cash- less crime.
I’m lucky enough to go to the bank every two to three weeks to deposit checks, transfer money and get cash with a teller during regular banking hours. Old fashioned but really nice to maintain a community feel in a large city. Separate credit cards linked to online shopping sites like Amazon & the now closing drugstore.com, another one for taxi and share ride apps on phone and one for ‘walk-around’ use. Cash is still necessary for tipping delivery people and when the digital devices go down or one wants to ‘lend a helping hand’. Brian, you’ve got one of the most informative and sobering blogs!
Thanks Brian ! Fabulous job, before these hit main stream, we get to know. Thanks again for keeping us informed.
Used to be cash (Yes, I am that old).
Danger of being robbed, so paper checks but they cost tha banks $$$ to process.
Then Credit Cards were introduced. You were told to “Destroy the Carbons” of the multi-part forms that went over your credit card and to emboss your name and account number for manual processing.
Then the Internet made internet shopping “The Way” and your data was transmitted across the web. “Man in the Middle” attacks and poor security practices exposed that data – and you were not safe once again.
“Chipped” cards are introduced for improved safety but the crooks figured out how to “Man in the Middle” get that data and use it quickly.
Now – your safest bet is back to brick and mortar stores, with cash. Untraceable, untrackable and you can only spend it once.
The Circle of Life is complete!
ISTR that the original reason for the magnetic stripe detector was that the first ATM had a real problem with people inserting foreign objects. So now the drive doesn’t work unless the sensor detects a magnetized area.
I have seen a few ATMs and Pin Pads at checkouts that have a shield over the pin pads. Google Image search “ATM keypad cover” and you’ll see a few examples of what I mean. It seems like a really bad (though well intended) idea to me. If the cover is legitimately placed by the ATM manufacturer or bank, it gives criminals an easy place to hide a camera where you aren’t looking and while you assume you are safe to enter your digits. Plus, on a few I’ve seen it is hard to get a second hand under the cover to block the view. Also, it gets you used to seeing such covers so that a criminal could stick a cover containing a camera on an ATM that a manufacturer didn’t put one on. I guess if they went that far, they could do a keypad overlay, but it is probably easier to make a cover with a camera that just sticks down onto the pad.
I’ve seen more Pin Pad covers/shields in my area (Google Image search “ATM keypad covers” for examples, this even pulls up some cases of cameras mounted in them and plenty of places to buy stick on covers in case you wanted one!). They may be legitimate, but it seems like a bad, though-well meaning, design idea. If they are legitimately placed by the manufacturer/bank, it gives thieves the opportunity to place a camera underneath teh cover where you aren’t looking. It can be hard to get your other hand under it to cover your entry. Also, having some legitimate covers may make you less suspicious of non-legitimate covers.
I’ve seen more Pin Pad covers/shields in my area (Google Image search “ATM keypad covers” for examples, this even pulls up some cases of cameras mounted in them and plenty of places to buy stick on covers in case you wanted one!). They may be legitimate, but it seems like a bad, though-well meaning, design idea. If they are legitimately placed by the manufacturer/bank, it gives thieves the opportunity to place a camera underneath the cover where you aren’t looking. It can be hard to get your other hand under it to cover your entry. Also, having some legitimate covers may make you less suspicious of possible non-legitimate covers.
Why go to all the trouble of setting up a fancy skimmer and camera when you can just use a slightly nicer camera and read the data off the card on the video surveillance? That’s what I would do if I were a criminal. Remove the camera before fencing the cards, keep moving to different locations. Sometimes I wonder why I still haven’t switched sides…
That’s not likely to yield very good results. I’ve got a surveillance camera that records 25 FPS at 1080P resolution. It’s highly rated, yet nothing like the cameras used to film TV shows and movies.
The motion of the card would blur the digits, if it’s the least bit dark, the image is going to be grainy, and even if you did see one side of the card, what about the other side?
Ok, I might be missing something, but what is all the fuss all about those “periscope” skimmers ?
If the crooks have physical access to the inner parts of the ATM all bets are off – periscope or not. They could actually entirely replace the whole thing as far as I am concerned. THAT is the issue at hand as I see it…
So Mr. Krebs, you were given non-public information and decided to release it… to the public, where attackers will now know it has been detected and will undoubtedly pivot, rather than letting the financial companies monitor and prevent these attacks?
Ok, if the magnetic strip is required by ATMs to ensure the card is inserted correctly then fine. Just don’t use it for data. Why is that hard?