The source code that powers the “Internet of Things” (IoT) botnet responsible for launching the historically large distributed denial-of-service (DDoS) attack against KrebsOnSecurity last month has been publicly released, virtually guaranteeing that the Internet will soon be flooded with attacks from many new botnets powered by insecure routers, IP cameras, digital video recorders and other easily hackable devices.
The leak of the source code was announced Friday on the English-language hacking community Hackforums. The malware, dubbed “Mirai,” spreads to vulnerable devices by continuously scanning the Internet for IoT systems protected by factory default or hard-coded usernames and passwords.
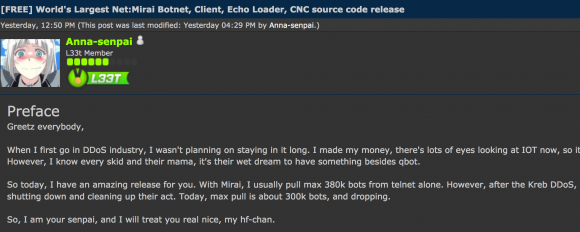
The Hackforums post that includes links to the Mirai source code.
Vulnerable devices are then seeded with malicious software that turns them into “bots,” forcing them to report to a central control server that can be used as a staging ground for launching powerful DDoS attacks designed to knock Web sites offline.
The Hackforums user who released the code, using the nickname “Anna-senpai,” told forum members the source code was being released in response to increased scrutiny from the security industry.
“When I first go in DDoS industry, I wasn’t planning on staying in it long,” Anna-senpai wrote. “I made my money, there’s lots of eyes looking at IOT now, so it’s time to GTFO [link added]. So today, I have an amazing release for you. With Mirai, I usually pull max 380k bots from telnet alone. However, after the Kreb [sic] DDoS, ISPs been slowly shutting down and cleaning up their act. Today, max pull is about 300k bots, and dropping.”
Sources tell KrebsOnSecurity that Mirai is one of at least two malware families that are currently being used to quickly assemble very large IoT-based DDoS armies. The other dominant strain of IoT malware, dubbed “Bashlight,” functions similarly to Mirai in that it also infects systems via default usernames and passwords on IoT devices.
According to research from security firm Level3 Communications, the Bashlight botnet currently is responsible for enslaving nearly a million IoT devices and is in direct competition with botnets based on Mirai.
“Both [are] going after the same IoT device exposure and, in a lot of cases, the same devices,” said Dale Drew, Level3’s chief security officer.
Infected systems can be cleaned up by simply rebooting them — thus wiping the malicious code from memory. But experts say there is so much constant scanning going on for vulnerable systems that vulnerable IoT devices can be re-infected within minutes of a reboot. Only changing the default password protects them from rapidly being reinfected on reboot.
In the days since the record 620 Gbps DDoS on KrebsOnSecurity.com, this author has been able to confirm that the attack was launched by a Mirai botnet. As I wrote last month, preliminary analysis of the attack traffic suggested that perhaps the biggest chunk of the attack came in the form of traffic designed to look like it was generic routing encapsulation (GRE) data packets, a communication protocol used to establish a direct, point-to-point connection between network nodes. GRE lets two peers share data they wouldn’t be able to share over the public network itself.
One security expert who asked to remain anonymous said he examined the Mirai source code following its publication online and confirmed that it includes a section responsible for coordinating GRE attacks.
It’s an open question why anna-senpai released the source code for Mirai, but it’s unlikely to have been an altruistic gesture: Miscreants who develop malicious software often dump their source code publicly when law enforcement investigators and security firms start sniffing around a little too close to home. Publishing the code online for all to see and download ensures that the code’s original authors aren’t the only ones found possessing it if and when the authorities come knocking with search warrants.
My guess is that (if it’s not already happening) there will soon be many Internet users complaining to their ISPs about slow Internet speeds as a result of hacked IoT devices on their network hogging all the bandwidth. On the bright side, if that happens it may help to lessen the number of vulnerable systems.
On the not-so-cheerful side, there are plenty of new, default-insecure IoT devices being plugged into the Internet each day. Gartner Inc. forecasts that 6.4 billion connected things will be in use worldwide in 2016, up 30 percent from 2015, and will reach 20.8 billion by 2020. In 2016, 5.5 million new things will get connected each day, Gartner estimates.
For more on what we can and must do about the dawning IoT nightmare, see the second half of this week’s story, The Democratization of Censorship. In the meantime, this post from Sucuri Inc. points to some of the hardware makers whose default-insecure products are powering this IoT mess.




Wow, that’s some smart stuff to hit. Those IP cameras are usually on pretty good uplink pipes to support them. The Axis ones in particular are capable of HD 10mbps video output at least. Turn off the camera, or aim the TCP/UDP traffic at someone else and you’re in trouble. IP VIdeo platforms are so perfect for this, wouldn’t mind chatting about that with you sometime.
Could someone please post a link to the source. Maybe the code can be used for good purposes as well such as chat botnets in a distributed fashion.
Thank you very much in advance.
https://github.com/jgamblin/Mirai-Source-Code/blob/6a5941be681b839eeff8ece1de8b245bcd5ffb02/mirai/bot/scanner.c#L123
does anyone have a link it source code? Can be posted here
thank you very much in advance
How come this post was posted on Oct 16th? O.o
Back to the Future
The date format follow the DD MMM YY format which is an international standard.
The big number is the day.
I do understand his confusion. Date displayed on article using the words. Little room for error in the interpretation. Copy/Paste presented below.
01
Oct 16
Source Code for IoT Botnet ‘Mirai’ Released
The source code that powers the “Internet of Things” (IoT) botnet responsible for launching
Also disregard as the date format could be interpreted as Oct in Year 2016 which was probably intended.
The only international standard for date is YYYY-MM-DD.
This is almost unequivocally a good thing for web security. Everyone’s acting like it’s the end of the world, the evil botnet is now open source, but that’s an incredibly naive perspective.
Grey-hats everwhere are going to be using this to log into these vulnerable devices and (1) brick them, or (2) change the credentials, and at that point those devices will no longer be a threat to the public internet. Sure, option 1 sucks for the owner, but they’ll yell at the manufacturer and demand a refund, and the manufacturer will (1) go under, or (2) fix their crappy product.
No matter how that goes, it’s a win for security and a loss for DDoSers.
The person who posted the src to the source code really likes Shimoneta…
And the person who named the bot “Mirai” probably really likes Mirai Nikki! Which makes me think that Anna-senpai might also be the creator of Mirai! Unless this is a reference to the visual novel “Mirai Nostalgia”, where there is also a character called Anna! All in all, those involved more or less directly with Mirai are probably fans of Japanese pop cultures, but not Japanese themselves (I doubt a Japanese would refer to himself or herself as “senpai” out of context, since you are senpai or kohai with respect to someone else).
Mirai translates to “Future” in Japanese. I’d wager it’s for coolness factor.
Another couple notable things named Mirai:
Kuriyama Mirai of Beyond the Boundary
Mirai, the Toyota Hydrogen Cell car in development
I think it’s just named as “The Future.” As in it’s the future of botnets. Aptly named, as my favorite thing to call IoT is “Internet of Targets”
That avatar’s definitely Nishikinomiya Anna-senpai from Shimoneta in the hackforums screenshot above.
Probably a few frames off from https://myanimelist.cdn-dena.com/s/common/uploaded_files/1450554922-4dc4de5fad0ec602eede30cb6dbd7d0b.jpeg
There is a mention of hardware default passwords being used. Are these changeable to protect your device (or are they permanent back doors of vulnerability)
and if so how?
Or maybe the person who named the bot “Mirai” is simply saying that this is our “Future” if we don’t smarten up on securing our devices.
“People steal—that’s why we invented locks.” –Jason Statham, Parker
Secure your stuff down or someone will take it from you.
It is a timeless truism in the story of human nature.
“On the not-so-cheerful side, there are plenty of new, default-insecure IoT devices being plugged into the Internet each day.”
It gets even worse. There are a number of tablet manufacturers (most, if not all, of them CHinese) that ship tablets with preinstalled, preconfigured and almost-impossible to remove malware.
Can you give more info on this? Link or news source? Scary.
thank you
So now that the source has been released why not develop a payload that blocks all future connection attempts , sort of a grey hat patch …
Seems that the IOT devices were running Linux.
#include
#include
What’s sad is that the majority of these IOT devices don’t need Linux. Hell, most don’t really need an OS. I can see something like DVR’s and heavy vid processing, but something like a fridge or thermostat could use something without an OS. Most could just be simple loop or interrupt driven.
Or maybe something like FreeRTOS – anything that can’t easily be fingerprinted.
When we did some of the first things that resembled IOT in 1994, (see patent https://www.google.com/patents/US6208266 ) we were using simple single thread code on the embedded side. I recall when doing embedded stuff that had TCP-IP stacks back in the mid-2000’s having our VAD guys scan the things for vulnerabilities. One came back and said “CP/M?” (interesting rant on this http://www.retrotechnology.com/dri/cpm_tcpip.html )
When the larger ARM 32 bit stuff came out with MMU and that could run a paired-down general purpose OS ported to it, I had a feeling this would become a nightmare.
Easy for developers to get to market, not a whole lot of skill required with regard to creating efficient code for things like hardware drivers for MAC/PHY’s and userland programs. Reliance on GP OS’s will be as vulnerable as any desktop running the basically the same kernel and drivers.
print “] [Remote ddos address” +sys.ton[7]
Club sets tend to be primarily made of Graphite in addition to Metal. There is substitute materials likewise, just like graphite in addition to titanium and composite other metals, nevertheless it is most beneficial to stay on the tested and relied on steel plus graphite.
How ABOUT CERT or BHS posts a list of these devices that are vulnerable immediatly????
IoT & web security!
Are these things directly exposed to the internet, or are they behind a NAT box and being compromised somehow else?
Who’s to say the NAT box itself isn’t compromised? Routers running embedded Linux or OpenWRT are just as hackable as the machines they serve running Windows or Android. In fact, seizing the router is the most reliable way to bypass (or traverse) NAT.
Alert ! ! !
Why not just have manufacturers release products with random passwords? That is, on the devices themselves, the makers could just put a tag with a randomly generated string, which the user could then change. Seems like an easy fix for the issue.
The answer is here: https://krebsonsecurity.com/2016/10/hacked-cameras-dvrs-powered-todays-massive-internet-outage/
many of these products from XiongMai and other makers of inexpensive, mass-produced IoT devices are essentially unfixable, and will remain a danger to others unless and until they are completely unplugged from the Internet.
That’s because while many of these devices allow users to change the default usernames and passwords on a Web-based administration panel that ships with the products, those machines can still be reached via more obscure, less user-friendly communications services called “Telnet” and “SSH.”
Telnet and SSH are command-line, text-based interfaces that are typically accessed via a command prompt (e.g., in Microsoft Windows, a user could click Start, and in the search box type “cmd.exe” to launch a command prompt, and then type “telnet” to reach a username and password prompt at the target host).
“The issue with these particular devices is that a user cannot feasibly change this password,” Flashpoint’s Zach Wikholm told KrebsOnSecurity. “The password is hardcoded into the firmware, and the tools necessary to disable it are not present. Even worse, the web interface is not aware that these credentials even exist.”
the obfuscation code in this source seems pretty simple — XOR. Is that still sufficient? Probably so on most IOT devices since they do not have any antivirus software running scans?
Also, if an entire manufacture’s line of products is permanently hackable, can something be done to blacklist the MAC address range of those devices(assuming the MAC address is hard-coded and cannot be changed ) at the access router stage?
Thanks for this article. After reading it, I went and searched the source for “GRE” and found https://sourcegraph.com/github.com/jgamblin/Mirai-Source-Code/-/blob/mirai/bot/attack_gre.c#L20. I’m not a security expert, but it was fascinating to poke around to see how some of the attack logic works (how the headers are constructed, etc.)
Source code with jump-to-def and find-references in the browser here: https://sourcegraph.com/github.com/jgamblin/Mirai-Source-Code/-/blob/mirai/bot/scanner.c#L124
Hello,
I am the founder and CEO of https://AthenaLayer.com
Recently our website was attacked by the same botnet. Our new cloud based mitigation system (the same one which our clients use) soaked up the attack no problem! And what is great about this is that we were also able to capture a good amount of data from the attack.
I have some very accurate data from the attack.
Here is the post documenting not only the existence of the attack – but the time of the attack.
https://twitter.com/MiraiAttacks/status/791022243480530945
As you can now see in just a moment there was a huge amount of incoming requests per second (exceeding 50,000 RPS)
As shown here: https://image.prntscr.com/image/23744504a4d44582969f71223eafd3d9.png
This also resulted in a total network transfer of about 280,000 packets per second!
https://image.prntscr.com/image/406816eb6be544c8bb4ea4fdb0dcbc76.png
Total bit rate exceeded 2.2Gb/s which is extremely huge – keep in mind this a layer 7 attack so this is real content delivery of 2.2Gb/s which our network had no problem doing under a quick burst.
That is shown here: https://image.prntscr.com/image/0734c5aa87864bfd84bf664df18d7e9e.png
Here you can see a visualization of the geographical distribution of the attack.
https://image.prntscr.com/image/d057acd9406c44a08c6e13ee864bcb14.png
This can tell you what parts of the globe have the most bots.
For press inquires email press@athenalayer.com
Everything savvy with wi-fi capacity IoT are making this world shaky. Engineers are not searching for security vulnerabilities when coding equipment drivers – on account of 802.11ac for gigabit+ speed over wi-fi makes it simple for DDoS daredevil. I can’t fathom why somebody would not use that ability to create something Useful for the world as opposed to assaulting the natives of the general public, simply mind boggling.