Some financial institutions are now offering so-called “cardless ATM” transactions that allow customers to withdraw cash using nothing more than their mobile phones. But as the following story illustrates, this new technology also creates an avenue for thieves to quickly and quietly convert stolen customer bank account usernames and passwords into cold hard cash. Worse still, fraudulent cardless ATM withdrawals may prove more difficult for customers to dispute because they place the victim at the scene of the crime.
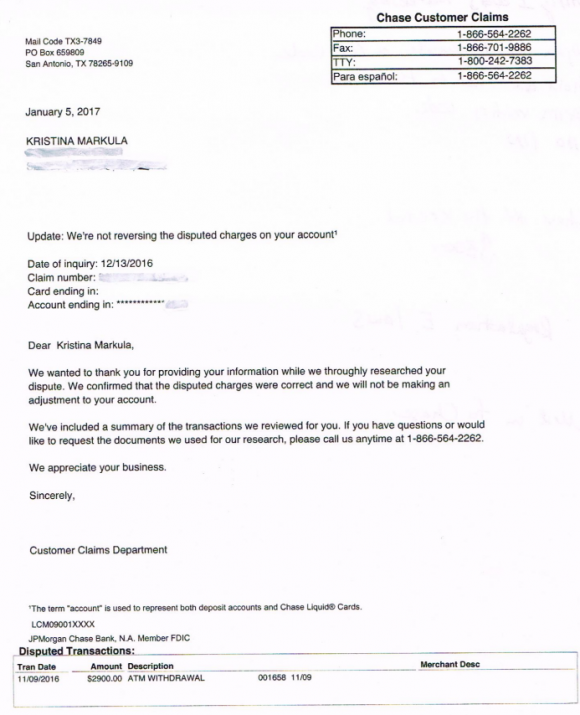
A portion of the third rejection letter that Markula received from Chase about her $2,900 fraud claim.
San Francisco resident Kristina Markula told KrebsOnSecurity that it wasn’t until shortly after a vacation in Cancun, Mexico in early November 2016 that she first learned that Chase Bank even offered cardless ATM access. Markula said that while she was still in Mexico she tried to view her bank balance using a Chase app on her smartphone, but that the app blocked her from accessing her account.
Markula said she thought at the time that Chase had blocked her from using the app because the request came from an unusual location. After all, she didn’t have an international calling or data plan and was trying to access the account via Wi-Fi at her hotel in Mexico.
Upon returning to the United States, Markula called the number on the back of her card and was told she needed to visit the nearest Chase bank branch and present two forms of identification. At a Chase branch in San Francisco, she handed the teller a California driver’s license and her passport. The branch manager told her that someone had used her Chase online banking username and password to add a new mobile phone number to her account, and then move $2,900 from her savings to her checking account.
The manager told Markula that whoever made the change then requested that a new mobile device be added to the account, and changed the contact email address for the account. Very soon after, that same new mobile device was used to withdraw $2,900 in cash from her checking account at the Chase Bank ATM in Pembroke Pines, Fla.
A handful of U.S. banks, including Chase, have deployed ATMs that are capable of dispensing cash without requiring an ATM card. In the case of Chase ATMs, the customer approaches the cash machine with a smart phone that is already associated with a Chase account. Associating an account with the mobile app merely requires the customer to supply the app with their online banking username and password.
Users then tell the Chase app how much they want to withdraw, and the app creates a unique 7-digit code that needs to be entered at the Chase ATM (instead of numeric code, some banks offering cardless ATM withdrawals will have the app display a QR code that needs to be read by a scanner on the ATM). Assuming the code checks out, the machine dispenses the requested cash and the transaction is complete. At no time is the Chase customer asked to enter his or her 4-digit ATM card PIN.
Most financial institutions will limit traditional ATM customers to withdrawing $300-$600 per transaction, but some banks have set cardless transaction limits at much higher amounts under certain circumstances. For example, at the time Markula’s fraud occurred, the limit was set at $3,000 for withdrawals during normal bank business hours and made at Chase ATMs located at Chase branches.
Markula said the bank employees helped her close the account and file a claim to dispute the withdrawal. She said the teller and the bank manager reviewed her passport and confirmed that the disputed transaction took place during the time between which her passport was stamped by U.S. and Mexican immigration authorities. However, Markula said Chase repeatedly denied her claims.
“We wanted to thank you for providing your information while we thoroughly researched your dispute,” Chase’s customer claims department wrote in the third rejection letter sent to Markula, dated January 5, 2017. “We confirmed that the disputed charges were correct and we will not be making an adjustment to your account.”
Markula said she was dumbfounded by the rejection letter because the last time she spoke with a fraud claims manager at Chase, the manager told her that the transaction had all of the hallmarks of an account takeover.
“I’m pretty frustrated at the process so far,” said Markula, who shared with this author a detailed timeline of events before and after the disputed transaction. “Not captured in this timeline are the countless phone calls to the fraud department which is routed overseas. The time it takes to reach someone and poor communication seems designed to make one want to give up.”
KrebsOnSecurity contacted Chase today about Markula’s case. Chase spokesman Mike Fusco said Markula’s rejection letter was incorrect, and that further investigation revealed she had been victimized by a group of a half-dozen fraudsters who were caught using the above-described technique to empty out Chase bank accounts.
Fusco forwarded this author a link to a Fox28 story about six men from Miami, Fla. who were arrested late last year in Columbus, Ohio in connection with what authorities there called a “multi-state crime spree” targeting Chase accounts.
“We escalated it and reviewed her issue and determined she did have fraud on her account,” Fusco said. “We’re reimbursing her and we’re really sorry. This small pilot we ran allowed a limited number of customers to access cash at Chase ATMs without a card. During the pilot we detected some fraudulent activity where a group of people were able to go online and change the customer’s information and get the one-time access code, and we immediately notified the authorities.”
Chase declined to say how many like Markula were victimized by this gang. Unfortunately, somehow Chase neglected to notify victims, as Markula’s case shows.
“It makes you wonder how many other people didn’t dispute the charges,” she said. “Thankfully, I don’t give up easily.”
Fusco said Chase had made changes to better detect these types of fraudulent transactions going forward, and that it had lowered the withdrawal limit for these types of transactions — although for security reasons Fusco declined to say what the new limit was.
Fusco also said the bank’s system should have sent out an email alert to the original email on file in the event that the email on the account is changed, but Markula said she’s confident no such email ever landed in her inbox.
Avivah Litan, a fraud analyst at Gartner Inc., says many banks see mobile authentication as the way of the future for online banking and ATM transactions. She said most banks would love to be able to move away from physical bank cards, which often need to be replaced several times a year in response to data breaches at various retailers.
“A lot of banks see cardless transactions as a great way to reduce fraud and speed up transactions, but not many are offering it yet as a feature to customers,” Litan said.
Litan said Markula’s case echoes the spike in fraud that some banks saw after Apple debuted its Apple Pay platform. Many banks chose to adopt Apple Pay without also beefing up security around how they validate new customers and new mobile devices. As a result, this allowed fraudsters to take stolen credit card numbers and expiration dates — data that previously was only good for fraudulent online transactions — tie those cards to iPhones, and use the phones to commit card fraud at brick-and-mortar stores that accepted Apple Pay.
“Identity proofing remains the weakest point in mobile banking,” Litan said. “Asking for the customer’s username and password to on-board a new mobile device isn’t enough.”
Litan said Chase should require customers who wish to conduct cardless ATM transactions to enter their PIN in addition to the one-time code. But she said even that was not enough.
Litan said Chase should have flagged the transaction as highly suspicious from the get-go, given that the fraudsters accessed her account from a new location, changed her contact email address, added a new device and withdrew just under the daily maximum — all in a very short span of time.
“ATM transactions should have much stronger fraud controls because consumers don’t have as strong protections as they do with other transactions,” Litan said. “If a customer’s card is used fraudulently at a retailer, for example, the consumer is protected by Visa and MasterCard’s zero liability rule, and they can generally expect to get their money back. But when you withdraw cash from an ATM, you’re not protected by those rules. It’s down to Regulation E and your bank’s policies.”
Under the Federal Regulation E, if a retail banking customer reports fraud, the bank must investigate the first statement of the activity plus 60 days from the date the statement was mailed by the financial institution. Unless the institution can prove the transaction wasn’t fraud, it must reimburse the consumer. However, any activity that takes place outside of the aforementioned timeframe carries unlimited liability to the consumer, as the financial institution may have been able to prevent the loss had it been reported in a timely manner.
Fusco added that consumers should beware of phishing scams, and consider asking their financial institution to secure their accounts with a special passphrase or code that needs to be supplied when authenticating with the bank over the telephone (a precaution I have long advised).
Also, if your bank offers two-step or two-factor authentication — such as the requirement to send a text-message with a one-time code to your mobile device if someone attempts to log in from an unknown device or location — please take advantage of that feature. Twofactorauth.org has a list of banks that offer this additional security feature.
Also, as the Regulation E paragraph I hope makes clear, do not count on your bank to block fraudulent transfers, and remember that ultimately you are responsible for spotting and reporting fraudulent transactions.
Litan said she won’t be surprised if this incident gives more banks pause about moving to cardless ATM transactions.
“This is the first case I’m aware of in the United States where this type of fraud has been an issue,” she said. “I’m guessing this will slow the banks down a bit in adopting the technology because they’ll see now how easy it is for criminals to take advantage of it.”
Update, Jan. 6, 9:44 a.m. ET: Looks like Chase could have learned from the experience of NatWest, a big bank in the U.K. that experienced much the same fraud five years ago after enabling a cardless “get cash” feature.




I love how it’s a clear case of fraud but Chase make Markula jump through multiple hoops and then expect her to eat the cost … until the media gets involved.
Banks are managed by idiots and hire idiots for IT support. sad, very very sad.
I find this very offensive, as I am one of the ‘IT idiots’ that you speak of.
Most, if not all of the time, unless you are the size of Wells Fargo, this is not an IT issue, the software is not created in house, and IT is not even consulted until after the decision is made.
The software is purchased from a provider, who falsely touts their software as the most secure thing in the world.
I find your being offended offensive.
This comment offends my offensiveness.
“The software is purchased from a provider, who falsely touts their software as the most secure thing in the world.”
Just like:
2FA
OS updates
email
smart phones (and their OS)
Facebook
Ashley Madison
Credit card transaction systems
Yahoo
Sony
Cloud services
IoT
Anti-virus/anti-malware
Microsoft
———————————————-
They all sound like gameshow hosts and traveling pitch-men to me. With their “no one can monitor all transactions at all businesses” way of trying to convince me that I can trust them approach.
Damage Control…their clients are cannon fodder….
Jesus H Krebs, every time I think it’s safe to go back in the water…. something like this happens.
It would seem to me if that Chase bank app had a mandatory use 2FA with a password protected app like “Authy”then this women would have not been taken advantage of so easily
Once the second mobile phone number is added, what keeps them from setting up Authenticator on that second phone number? I think the weak link in this case is the ease someone had of adding the second mobile phone number.
Adding a new mobile phone number would have no effect. The authenticator application like Authy or Google Authenticator is tied to a device via a private/public key pair, and is not tied to a specific phone number.
Actually, the bank do use the mobile phone number to authenticate transactions on AP/AP. I see this on my account related to the virtual card I have when I load the credit card to Android Pay. This acts as a security measure. When I changed to another provider, I had to go on my account to delete the virtual card attached to my old phone number because of the new number associated with it.
Here’s an example why:
When Apple Pay and Android Pay came out, a reporter was tasked to test it out by using a phone provided by fintech company (they had installed it prior to it being released in the wild) and she loaded her debit/credit card onto the app and went about her day testing it. After about approximately 3 or 4 transactions later, she tried to do one last time, it failed forcing her to use her card to complete the transaction.
She went back to the office and had to call the bank to find out why it failed and learned from the bank fraud dept saw that another mobile phone number, that is not listed, on her file was being used to purchase things. After she explained that she was given another phone as part of writing a story about AP. After that, the bank unlocked her card.
This is why we can’t have nice things.
Since when do I need to withdraw $2,900 from an ATM?
Since when? Ever since the limit was set to $3000.
After all, a withdrawal of $2999 might have been noticed 🙂
When you want to buy that giant screen smart TV, but you don’t want to use your credit card at the big box store for fear it might be skimmed, so you need to have the necessary cash in hand.
lol….
yeah, right, gotcha, yep….
Compromise the account here instead of there.
——————————————————–
“Chase what matters”
These devices are not safe to use in this way. 2fa is not going to change that and updates wont either.
Do what you will. You have been warned.
And then that TV will watch you rather than the other way around.
This is totally configurable. One quick call to the bank or sometimes in an on-line account and the customer can easily set a limit. $3000 seems excessive, but if the attacker has the username and password to the bank account they might have changed the limit first then confirmed with the OOB token or e-mail sent to the same device. Losing your phone now means losing a lot more…and if my theory is even slightly correct bank’s should model this as a fraud case to monitor if they don’t already; ATM withdrawal limit increased + immediate withdrawal = do something, call batman, whateva. I’ll keep using my card and I’ll retain my low withdrawal limit and continue monitoring my transactions frequently, thanks.
“Chase should require customers who wish to conduct cardless ATM transactions to enter their PIN in addition to the one-time code. ”
One of the use cases for cardless ATM transactions is to send the one-time transaction code to another party via email or message, to enable them to collect the funds from the ATM, your daughter, your wife, in cases where they have lost their card or dont otherwise have access to their account, and need cash, or to an ebay seller, etc.
Providing your card PIN for the transaction would clearly be unwise.
Additionally, subject to the bank’s implementation, this is a cardless transaction, ie. there is no card to associate the transaction to, so no PIN to validate. Rather the transaction is associated to the account number via their app login customer number… Again, there’s no PIN.
/just a thought.
I’ve never seen a bank pass up an opportunity to ship me a debit card when they can. Never. I probably have 4 or 5 of these from different banks in a drawer with the sticker still on them.
Serious question: What american with a bank account doesn’t also have a card and PIN that allows them to withdraw money at an ATM?
Another serious question: You don’t by any chance work for Chase, do you Ben?
Pins (password by another name) work fine so long as the symbol set the credentials are selected from is unique to the user.
Other than my iPhone, I have never seen a PIN use anything but digits and no more than four digits (10,000 combinations).
My Wells Fargo PIN is ten numbers.
I used to have a longer PIN as well, until I ran into the whole issue of machines that just assume the pin is exactly 4 digits. It doesn’t let you enter in your whole pin, which is then of course rejected. This isn’t a problem with newer machines but if you’re traveling somewhere and don’t have easy access to your regular bank’s ATM machines, or are purchasing something in a store with debit it becomes a problem.
Of course I could choose not to use any of these machines or stores, but ultimately I chose convenience. The situation has likely improved by now as well. The last time I had a longer than 4 digit pin was more than 10 years ago.
No, I don’t work for Chase.
I do not have a bank card and can not withdraw money from an ATM. I don’t know, maybe it got lost and I never replaced it. Just get cash when I deposit my check.
I do not have an ATM card.
I refuse my bank’s strong suggestion, “Let us issue you a debit card.”, pretty much every time I go into the bank.
I haven’t used an ATM since the late 1980s or early 1990s.
The only financial transactions I deal with online are stock trades and an occasional online purchase. I get what appears to be a couple of pounds of paper statements every month.
My neighbors, coworkers and financial advisors are mostly flabbergasted when I tell them that I avoid online banking.
It’s probably a side effect of working in the IT industry (and reading this and other security blogs).
I’m in IT and do just about everything online. Am I just lucky? My family and friends are always facebooking (well, it has been a while) about having withdrawals on their account they did not make. I’m just going to go with lucky.
Cash is king. In order to steal it you will have to physically been near me or have something I want bad enough to come after it. Either way you must work harder and take more risk.
I discovered this the hard way when I had to fight financial institutions after having my money evaporate into the ether. Bits bite
My wife. Seriously. No ATM cards. Never uses cash.
I purposely have main Checking/Savings account without any Debit or ATM card.
Instead, I have a separate Savings account which has an ATM-only card (no debit). We just keep $100 in this account for a quick minor emergency.
When we do want to get more money out, this requires me to transfer funds online from my Main Checking/Savings account to the ATM-only account. The ATM-only account has no access into my Checking/Savings account.
So, to hack me, an attacker would have to know my Checking/Savings username/password (bank requires OOB 2FA to set up a new devices), and then transfer funds out to the ATM-only account, and then physically go to an ATM to withdraw.
Yes, the tinfoil is strong with me. Customer service still couldn’t get why I didn’t want a card associated with my account and why we went through the hassle to open a unique Savings-only account for ATM access. BTW, as of the new Reg D changes, you cannot have an ATM-only account if it has a checking account. To have an ATM-only account (meaning no debit card), the account must only be a savings account, or so says my Credit Union.
You asked what American does not have an ATM card….here’s one that doesn’t. Yes I know that makes me a dinosaur.
Whatever happened to managing ones funds in a manner that does not require regular ATM runs to get cash? A periodic visit to a brick and mortar bank with live tellers is not all that inconvenient in most areas.
When was the last time Brian you ran a story of someone’s account being compromised by a visit to a bank branch and a live teller?
Touche.
> this is a cardless transaction, ie. there is no card to associate the
> transaction to, so no PIN to validate.
The PIN is associated with the card number or account, not the card itself. Even a cardless transaction has some sort of account number behind it. The PIN is not encoded on the card itself as it would be trivial to break a 4 digit PIN by reading the track if it were. It is instead maintained at the bank’s data center and therefor would be available to compare in a cardless transaction. In short, there’s no reason they can’t use the PIN with cardless transactions.
As to the argument that they want to make it so you can send money to friends/family and the PIN would be problematic, I agree that’s true if that’s what wants to be accomplished. That said, it seems a small edge case for the to put all account holders at risk over. So far in my entire life I have never felt the need to wire money like this and even if I did, I’m not sure I’d weigh that convenience worth anywhere near this extra risk. At best this would seem to be something that should be an “opt in” with plenty of warning required to be given to the consumer.
Great icon. Great breed.
Dear Mr. Krebs,
In reading your “Krebs on Security” emailed article that I received on 01/05/2017 with a subject line of “Stolen Passwords Fuel Cardless ATM Fraud”, I had one issue: As I always like to read everything you say so that I learn as much as I can, on the right side of your posting layout there was a area that had some info on “Badguy Uses for Your Email” which was a graphic or chart with about 4 different lists. I copied it with the snipping tool, but your form would not allow me to paste it on this comment. Bottom line, even when I used the Win 7 magnifier to be able to make it bigger [so that I could read it] the type was of such marginal resolution that it wasn’t legible. I understand that you want to make use of your limited area, but when you offer something and then print it at such low resolution that it can’t even be read when magnified, it is frustrating at best! I don’t know what you can do about it, but maybe you should give a little less info since you tried to present more info than your space and graphical resolution could support.
Thanks for your info and time in reading this! I remain,
Respectfully,
Joseph Williams
*********************************************************************
Hi Joe. The original image you seek is available to be viewed in a fairly large format from the story itself…
https://krebsonsecurity.com/2013/06/the-value-of-a-hacked-email-account/
If you wish to make the image bigger in your browser, just hit the Ctrl key and the + sign at the same time (no shift needed)
Am I missing something?
I think he wants the fullsize pic. Which he can get from clicking on the article.
Or it’s also here:
https://krebsonsecurity.com/wp-content/uploads/2013/06/HE-1.jpg
That works for me.
Chase sends an email to the new address not the old one when you change it. I’ve still got the ones they sent to my account when I took over doing my dad’s fiances. Stupid.
And two factor of a text to your mobile is not going to help if they had to change your mobile number to be able to do this.
“Chase sends an email to the new address not the old one when you change it.”
Tom, are you certain about this? That would seem to be the wrong way to do that. What good would such an alert do?
For what it’s worth, I tried changing my email address on Chase.com to a new address and it notified both the old address and the new address.
I’m still not understanding how a fraudster would be able to access the account with just the stolen username and password. From unrecognized PC or mobile devices, Chase will not allow a user to simply log into the account. Chase requires an identity code be issued via text/voice to the mobile device on record or to email adddess on record to verify the new device. Without having access to the email account or mobile device on record, how would you gain access to the account? The same holds true when resetting passwords. I could see a scenario where fraudsters create a new account with skimmed debit info as well as a few other pieces of data but that would require additional work.
Chase should enable a permanent opt out of this feature that would require a customer to reenable only after providing proper identification. This could work similar to a credit freeze and could be extensively vetted. This would allow customers to protect themselves from this scheme. At the current time, we apparently have no defense against it.
When logging in with a new computer or browser (i.e. one without cookies that you haven’t used before with chase.com), it will prompt to either call you or text you with the number on file or email you. If the attacker were able to get access to the customer’s email through whatever means (password reuse, for example), it would be trivial to get that authentication code, access the Chase.com account, change the information to theirs, and then delete the email. I would suspect that there would be an alert on the user’s email that a login took place from a different location but those are can be easily overlooked, if even available on all email providers.
Quite possible (not saying that is what happened) and that just reiterates that password reuse and the lack of 2FA is a bad idea.
I think you must also consider cloud hacking in this scenario. Its a method in which you can see a great deal of what a consumer receives without ever fully taking control of their device, email, phone and such.
Two factor authentication should be implemented in such a case the moment the 7 digit code in entered at the Atm to the original phone number or email address otherwise this was just an account takeover and chase should have better security to avoid the future takeovers
Chase security is an oxymoron. I dumped them years ago. ‘Nuf said.
Chase has been very good about notifying me of fraudulent use of my Sapphire credit card. Within minutes I get an automated call saying “Your card was used at a Kroger in Atlanta, if this is not you press 2”. I live in another state, so I press 2 and talk to a human. It’s happened several times.
The simplest non technical operation needed to prevent this fraud was the requirement of the System to send an SMS to the first authenticated phone number of the account holder, notifying them of any form of operation occurring in their accounts. If this was implemented abnitio, the lady would have known before the fraud happened that something fishy was on, and alerted the bank.
The technology no doubt is safer, and offers more transaction scopes than using physical cards. However, I feel that in securing it, both the Banks and Customers should be highly involved.
It’s really strange to see the U.S. banking system through another country perspective (Italy).
I don’t know how they can handle anything without mandatory two factor authentication. In Italy from the beginning of online home banking (end of 90s) every bank built their system with 2FA in mind, so now is the de-facto standard, and if a bank would propose a system without it, customers would probably avoid it thinking it would be insecure.
I think maybe difference between the two countries is due to culture (banks are less trusted in Italy), or maybe in Italy without 2FA there would be too much fraud.
In don’t think informative email/SMS would be useful,
An one-time-code SMS should be sent to the old number and verified to register a new number.
I thought 2fa via SMS was considered not to be secure due to spoofing.
When it comes to a phone, fecal matter happens. I prefer to use cards. No batteries required.
Allright, 2000$ atm witraw limit is nothing.
People use even 10000$ cash per day.
Cash is always needed.
Anyways business is always business
And business is need for cash.
To be honest everybody knows whats going on
In the world but why everybody still make face
Like everything is fair and we live in nice world.
Well until people accept all this,nothing changes.
Who we blame. People take what u asked for!
Dont complain!
In the U.S., cash transactions of $10,000 or more are required to be reported to the IRS and you may be investigated. There is an exemption available for stores that normally deposit $10,000 or more in cash.
All cash transaction of more than $10K (it was reduced to no more than $2,500 as it can be structured below the $10K limit to avoid filing) is reported on a form required by the Bank Secrecy Act and reported to Treasury (FINCEN) not the IRS.
However, for all exception requires the bank undergo monitoring customer’s activity for a period of time to justify having to deposit large sum of cash. Not many business qualify for that. I know because I used to work in the bank and I have required businesses file the BSA form. I asked about it and they told me that the bank would not approve it largely it was not justifiable.
Since the explosion of debit and credit cards, many stores are starting to require using it rather than cash because it is expensive for the store to count and deposit the cash and it is more apt to be stolen by thieves just by waiting for someone walk out of the store to the drop box.
Now the base take away is that Markula didn’t have 2fa enabled, right? She only had the app present on her phone for checking her banking activity. 2fa isn’t perfect, but it is a lot better than nothing.
Since she had the app, one would have thought/hoped that Chase would have used that to provide 2fa. Or at the least, unusual activity (such as adding a new number, or changing one’s email address) would prompt a notification to the app.
I’m in favor of a pin along with the cardless code. The code obviously makes use of the phone (something you have) while the pin would provide the something you know part and allow this to remain a 2fa method. But pins are terribly weak (4 digits, really?), and I imagine anything more complex will probably be saved on the phone. Which, you guessed it, if it is in the hands of a miscreant now means they have both what you used to have and what you used to know. But it would save you from these kinds of cases where they’ve simply added themselves to the account but don’t have access to the original device.
That aside, I imagine Brian’s quite right. Maintaining and updating software will probably be preferable in the long run to having to replace physical cards.
Can you open an bank account and not have electronic access enabled? No web or app access?
I would feel lot comfortable moving savings to one of these accounts. The other option is 6-month or one-year CD. As long as those can’t be cashed out over web.
As Brian has noted in past banking-related posts, in the US, different regulations apply to personal and business accounts.
With that proviso in mind, I maintain more than one US-domiciled business account with no web or ATM access.
Is the same deal available for personal accounts? Dunno; proof is left to the student.
I’d like to enable 2FA on more accounts, but many financial institutions put it in front of ALL account access after you do it, thereby breaking other useful tools that I also largely trust like Personal Capital, etc. This is certainly the case for Vanguard anyhow.
I’d hope that companies could work out a better system than 2FA for aggregation services that is stronger.
I can understand the bank’s initial reluctance to refund the money. In this case, my first assumption would be to think that this lady gave her username/password to someone in an “emergency” since she was out of the country. How else would the third party have logged in to her account and further passed the “new device/location” test?
Knowing the banking username/password does not give anyone the mobile number or email address associated with the account. So how would SMS or email hacking work to get the “new device/location” code? Unless someone was actually using her mobile phone or home computer, this account takeover seems unlikely. Not impossible, just unlikely.
Of course, if she was phished with an urgent”we need to verify your account” maybe she was foolish enough to give up everything needed for this hack. This user, not the Chase banking system, is the weakest link in this story.
Another likely scenario would be that she, like so many other people, use the same username / password combination across many different accounts, and it was breached in one of the many Yahoo/LinkedIn/etc. breaches. That could be enough to access an email account as well as her bank account.
And if she also, like so many other people, told the world on her Facebook page that she was going on vacation to Mexico, what better time to fraudulently access her account and steal her money, when she may not notice it because she is out of the country?
These scenarios also make her the weakest link.
The world uses a 30 year old OS that is still bleeding security exploits and we expect to use cell phone technology securely?
I don’t put anything on my cell phone that I wouldn’t put on the stall wall in a public restroom.
Wonder if Chase mailed (snail mail) a notification about the eATM pilot. Considering that this is a bigger deal than upgrading a card to Visa Signature (for which I got plenty of mail)…well, I dunno.
Considering how good Chase’s fraud detection is (it’s pretty good), I’m quite surprised that they didn’t see this string of account hijacking activity as it was happening and, you know, lock down access. But maybe the banking side is different than the credit card side.
Also, a $3k limit on an ATM is rather silly, when most online payments systems (e.g. PopMoney and Square Cash) won’t let you move that much.
Thanks for this and keeping me informed. Much appreciated!
I have a banking “recipe” that I’m pretty happy with.
I have 4 different accounts that are used via online banking, and I pay all my bills online. One savings account, with a small balance, and my checking account are the only ones linked to my ATM card. I have a high balance saving account and line of credit that are not accessible with the card (this was an option I requested). Around the start of the month, I transfer a few hundred dollars to be gradually withdrawn from the savings account. I NEVER withdraw from the checking account, preferring to have the fewest transactions possible (easy to miss things with lots of small transactions).
I don’t use Facebook, seeing it as a cesspool of fraud and scammery. I have repeatedly refused Debit cards, and yes, they do always hassle people about getting them. They sound like a bad deal-a minimum number of uses to avoid charges, etc. I am skeptical of using my phone for anything financial. It always seems to open up many possible bad outcomes, with the only upside being perceived convenience.
And remember-it’s JP Morgan/Chase…the ones who just got caught massively cheating their customers. They also poorly handled a large breach a few years back. I dumped them recently when I refinanced with my local bank. I am now Chase-free, and happy about it.
As always, thanks Brian!
Interesting conversations regarding the ATM portion of the authentication. What is interesting though is the customer was compromised online. The ATM transaction was just the goal of the compromise and at that point the authentication you require may no longer matter because the new device was added. The key here is moving your detection to the enrollment portion to prevent the fraudster to getting to their goal of the ATM at all. The fact that the same credentials could be used in all three channels essentially is a lack of diversified authentication controls. This really shows a failure in fraud strategies (which someone captured earlier) when you have activity happening in the US and Mexico as well as new device, contact information updates. I played around with changing email and phone on Chase’ website. You can pause alerts. So if that is the first step that occurred after the fraud logged in, customer would have only received one alert activation email and then when all other information was added/changed there would be no alerts sent out. If there had been a phone number and email address validation at the time of change, that could be an addition layer (albeit costly) to help detect the suspicious activity. This is an excellent use case to see how easy this was to compromise and shows that banks need to add more variables to the equation. Change up the criteria that is asked for and used cross channel. The mobile device can be a useful tool when you have call diversion detection, validation of demographic/contact changes and robust fraud detection strategies in place.
10.000 $ reporting.allright anyonecan fill the papers you can write there anything you like.
Anyways so many un educated poor people in usa earning money from fraud. Even now you can easily buy things with credit cards. So many ways in usa how poor immigrants can earn money usa is land of opportunities.
This low educated people turn in to fraud business field
Becouse violant crimes not pay well anymore. So usa is full of uneducated unemployed people so they all work in fraud fields
Even drug dealers in usa turning into fraud field becouse its just well payed so many people in usa working with all kind fraud fields guess what its new generation hustle thing. And popping bottles in club weekend. So this is reality in usa.
People why you keep your money in banks? Keep it on bitcoins its more secured.
Things like online wallets are more safe then any banks.
Bitcoins more secure?!?! Sounds like someone has to do some serious research. Entire Bitcoin brokerages for want of a better term have disappeared. Who backs the funds in a bitcoin account??? No FDIC of Bitcoins that I have ever heard of.
Try going to your local dry cleaner or supermarket and explain that you want to pay for transaction with bitcoins….sure it might work at a few but doubt it will work at many.
Mr. Kreb,
I see in the article that Markula was using the hotel’s Wi-Fi to access her bank account. That should be a no no because anyone can capture it because it is public place.
Since the transmission is https end-to-end encrypted I don’t see much of a problem with public wifi.
It turns out that changing account settings for an American Express account sets a fraud warning on the account. I added the address of a retired friend to my AmEx account because he’s at home and can sign for things. Then I tried to charge a somewhat expensive item. The transaction was blocked until I had a chat with the fraud people at AmEx. Good; that’s what they ought to do.
Presumably the fraud warning that’s set by a change to the account expires after a reasonable period of time, like one statement cycle. I can’t tell, and that’s also good.
Are you listening, Chase?
“Fusco also said the bank’s system should have sent out an email alert to the original email on file in the event that the email on the account is changed, but Markula said she’s confident no such email ever landed in her inbox.”
I’d put money on it that an email WAS sent to the old email address, but the victim used the same password for both her bank account and email account, allowing the theives to log into her email and delete the notification.
One of my banks, Key bank, is not listed at Twofactorauth.org. I wanted to submit a “pull request” but first I would have to become a member, providing yet another site with a username and password. Key bank i s a fairly large bank, so I was surprised that it wasn’t listed. But then maybe others are put off by the “You must be a member” crap. Shame on you Twofactorauth.org — one should not need to be a member.
Chase sends me an email every time I sneeze – I like that. However – I had to go to Chase online to set the alerts myself. Sounds like this victim might not have done that.
Personally, I’m not interested in ‘card not present’ transactions – and this incident is pretty much why I’m not.