A new strain of ransomware dubbed “Petya” is worming its way around the world with alarming speed. The malware is spreading using a vulnerability in Microsoft Windows that the software giant patched in March 2017 — the same bug that was exploited by the recent and prolific WannaCry ransomware strain.
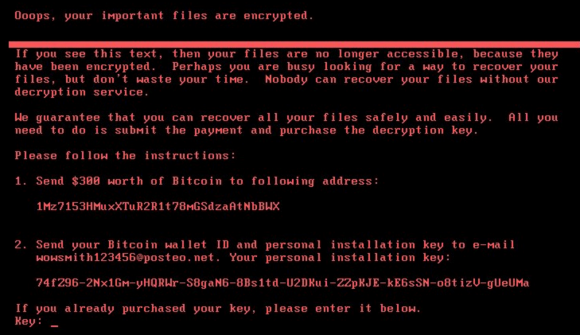
The ransom note that gets displayed on screens of Microsoft Windows computers infected with Petya.
According to multiple news reports, Ukraine appears to be among the hardest hit by Petya. The country’s government, some domestic banks and largest power companies all warned today that they were dealing with fallout from Petya infections.
Danish transport and energy firm Maersk said in a statement on its Web site that “We can confirm that Maersk IT systems are down across multiple sites and business units due to a cyber attack.” In addition, Russian energy giant Rosneft said on Twitter that it was facing a “powerful hacker attack.” However, neither company referenced ransomware or Petya.
Security firm Symantec confirmed that Petya uses the “Eternal Blue” exploit, a digital weapon that was believed to have been developed by the U.S. National Security Agency and in April 2017 leaked online by a hacker group calling itself the Shadow Brokers.
Microsoft released a patch for the Eternal Blue exploit in March (MS17-010), but many businesses put off installing the fix. Many of those that procrastinated were hit with the WannaCry ransomware attacks in May. U.S. intelligence agencies assess with medium confidence that WannaCry was the work of North Korean hackers.
Organizations and individuals who have not yet applied the Windows update for the Eternal Blue exploit should patch now. However, there are indications that Petya may have other tricks up its sleeve to spread inside of large networks.
Russian security firm Group-IB reports that Petya bundles a tool called “LSADump,” which can gather passwords and credential data from Windows computers and domain controllers on the network.
Petya seems to be primarily impacting organizations in Europe, however the malware is starting to show up in the United States. Legal Week reports that global law firm DLA Piper has experienced issues with its systems in the U.S. as a result of the outbreak.
Through its twitter account, the Ukrainian Cyber Police said the attack appears to have been seeded through a software update mechanism built into M.E.Doc, an accounting program that companies working with the Ukranian government need to use.
Nicholas Weaver, a security researcher at the International Computer Science Institute and a lecturer at UC Berkeley, said Petya appears to have been well engineered to be destructive while masquerading as a ransomware strain.
Weaver noted that Petya’s ransom note includes the same Bitcoin address for every victim, whereas most ransomware strains create a custom Bitcoin payment address for each victim.
Also, he said, Petya urges victims to communicate with the extortionists via an email address, while the majority of ransomware strains require victims who wish to pay or communicate with the attackers to use Tor, a global anonymity network that can be used to host Web sites which can be very difficult to take down.
“I’m willing to say with at least moderate confidence that this was a deliberate, malicious, destructive attack or perhaps a test disguised as ransomware,” Weaver said. “The best way to put it is that Petya’s payment infrastructure is a fecal theater.”
Ransomware encrypts important documents and files on infected computers and then demands a ransom (usually in Bitcoin) for a digital key needed to unlock the files. With most ransomware strains, victims who do not have recent backups of their files are faced with a decision to either pay the ransom or kiss their files goodbye.
Ransomware attacks like Petya have become such a common pestilence that many companies are now reportedly stockpiling Bitcoin in case they need to quickly unlock files that are being held hostage by ransomware.
Security experts warn that Petya and other ransomware strains will continue to proliferate as long as companies delay patching and fail to develop a robust response plan for dealing with ransomware infestations.
According to ISACA, a nonprofit that advocates for professionals involved in information security, assurance, risk management and governance, 62 percent of organizations surveyed recently reported experiencing ransomware in 2016, but only 53 percent said they had a formal process in place to address it.
Update: 5:06 p.m. ET: Added quotes from Nicholas Weaver and links to an analysis by the Ukrainian cyber police.




I see on slashdot that the one, single email address to pay the ransom has been blocked by the German ISP, so no one can pay, even if they want to.
And… Rosneft? Ukraine? This is someone who thinks they’re cleverer than they are, and I forsee them in court, with multiple outstanding extradition requests.
That is, if they’re not dead “resisting arrest”.
thanks for the information i have also added new post about it.
you can read here below.
http://allessentialtech.com/2017/06/27/petya-another-ransomware-outbreak-happens-globally-after-wannacry/
You need to update your blog with the latest information about Petya; specifically, that it isn’t ransomware, it destroys the files on your hard drive.
I am surprised there hasn’t been a call to change bitcoin to make it impossible to use for anonymous payments for things like ransomware. If the money can be stopped, then it will reduce ransomware.
Bitcoin can’t really be ‘de-anonymized’. Usually linking an address to a real identity is something that’s left to the exchanges and payment processors.
However, Bitcoin isn’t as anonymous as people think it is. It’s a public ledger system where every coin has a unique identity and its whole history can be tracked. Anyone with the ledger can see where everything goes.
Do a Google search on “bitcoin obfuscation” and you can see how you can hide the money.
No mention of any infections in China?
I rather doubt that they are immune. The Chinese are probably just keeping mum for fear of “losing face” over the fact that their systems are just as unpatched as everybody else’s, if not actually worse (due to the high level of Windoze piracy there).
I think we would have heard from China by now if there was real trouble. They won’t care about pirated personal or small business copies; but the China Rail ticket booking and sales system uses XP terminals. If it got in there the whole country would come to a dead stop. I have no idea what they use for servers or firewalls, but the system is “exposed” for public credit card ticket sales, and private resellers.
If you wanted to, an individual could potentially posses the bitcoins for the futures exchange. That’s the difficulty here, I don’t think petya took that into consideration. There’s also the problem of hedge funding buckaroos.
Brian,
Kaspersky has a nice technical write-up on the new Petya. You may want to include it is also spreading via the NSA’s EternalRomance Vulnerability.
The framework being used to gather credentials and spread across the network is mimikatz, “LSADump” is merely 1 of the mimikatz modules used in the attack.
See: https://securelist.com/schroedingers-petya/78870/
Where Kaspersky is calling this one ‘NotPetya’ Microsoft is playing safe and calls it a Petya variant.
https://blogs.technet.microsoft.com/mmpc/2017/06/27/new-ransomware-old-techniques-petya-adds-worm-capabilities/
This is not news. When are the IT and security professionals going to get off their asses and put policies and procedures in place to really reduce this kind of threat?
There is so much that can be done and many options are inexpensive to implement. We can start by isolating systems that do not need to be exposed to IP addresses outside the USA. Consider using a proxy to read your email. Not just to access your mail, but a proxy on which the email is opened and displayed where you can view it from a second machine. That will isolate users even if they open a bad attachment. It would infect the proxy and not their machine. Come on, this doesn’t have to be all that hard to protect users.
I just don’t understand why more is not being done.
I agree. Why does it seem like so many computers are directly addressable from the Internet? Has everyone forgotten how to set up a DMZ? Use sub-networks with double firewalls?
There are a lot of network isolation techniques. When there are massive infections like this, it tells me that too many organizations are not using network isolation.
Nicholas Weaver has it right.
Can you really call it ransomware if it encrypts with a pseudorandom data unrelated to the corresponding key it provides? Paying out can’t net you a recovery key.
It even encrypts the MBR. Next to impossible to recover it basically. It’s not really ransomware with this “variant”, more of a disk wiper.
Scott is correct, it would appear. The author of Petya has said this is not his doing, and the latest analysis indicates that this “ransomware” was intended to be destructive, not to make money for its authors. Ukraine appears to have been deliberately targeted, with infections in other countries just collateral damage.
https://www.bleepingcomputer.com/news/security/surprise-notpetya-is-a-cyber-weapon-its-not-ransomware/
How to find who did it:
From all the data gathered, there never was any intention to make money off of the ransom part. (one address, one wallet, overly destructive, targeted attack)
It was obviously an attack on Ukraine’s infrastructure. Everyone else is collateral damage.
This makes the question of who did it. There are only two potential villains here: The governments of Russia and the US.
Russia would be the easy pick, but the US CIA has the biggest reputation in the world for false flag events to force policies. Until the next Snowden, we may not know.
However, since there is an “immunization” of having a file “perfc” with no extension in the “c:\windows\” directory, when we find a PC that has the perfc file on it that predates the initial infection, it can lead us to exactly who knew of it prior to deployment and lead us to the bad guys.
fsb hands are dirty im sure.
but even we know,they stay under Russian
juridical protection. even we all know about everything,the question is
what we can do ? I think nothing. I think many people know exacly what is going on,but so what? Everything will be same.
You can protect your system and server by blocking port number 445 and 139
If someone doesn’t have TCP/UDP ports 137-139, 445 and 666 blocked at the perimiter, they deserve what they get.
Also @Mahhn, the “immunization” is not foolproof, and better techniques should be used. Mutations that just add a random number to the file can bypass the check.
From BleepingComputer (again), carefully not naming names –
“Slowly, it’s becoming somewhat clear that someone is slinging ransomware specifically at Ukraine and is trying to pass as a mundane cyber crime operation, hiding other motives.
Putting all clues together, we see four ransomware campaigns that have targeted Ukraine, have tried to pass as other ransomware threats, have quality code, and three of which appear to have used the same server to spread.
There is no clear-cut evidence that the same person or group is behind all campaigns, but there are too many coincidences to ignore.”
From F-Secure blog :
“It has a vendetta against Kaspersky Lab.
If this malware finds running Kaspersky processes on the system, it writes junk to the first 10 sectors of the disk, and then reboots, bricking the machine completely.”
https://labsblog.f-secure.com/2017/06/29/petya-i-want-to-believe/
A few days ago I found a message on pastefs.com (kind of an open letter) from a hacker to a victim, telling him how to send money, and how he will send a decryption key to recover the victim’s files etc.
I think by blocking hacker’s email address, they create more problems for the victims, though yes they cut down hacker’s illegitimate income source, and it is also possible that there’s a terrorist group behind the development of such worms, but email is a way to track down the hacker behind, so I guess they should use it instead of blocking it.
Valuable info. Lucky me I found your website by accident. I bookmarked it.