More online services than ever now offer two-step authentication — requiring customers to complete a login using their phone or other mobile device after supplying a username and password. But with so many services relying on your mobile for that second factor, there has never been more riding on the security of your mobile account. Below are some tips to ensure your mobile device (or, more specifically, your mobile carrier) isn’t the weakest link in your security chain.
For reasons explored more in The Value of a Hacked Email Account, many people become so preoccupied with securing online access to their financial accounts that they overlook or forget the fact that all of those precautions may be moot if hackers can access your email inbox. From that 2013 piece:
“Sign up with any service online, and it will almost certainly require you to supply an email address. In nearly all cases, the person who is in control of that address can reset the password of any associated services or accounts –merely by requesting a password reset email.”
Many webmail providers now encourage users to take advantage of two-step (a.k.a. “two factor”) authentication methods in addition to passwords for securing access to email. This usually involves the user adding a mobile phone number to their account that gets sent a one-time code that needs to be entered after supplying the account password. The idea here is that even if thieves somehow manage to phish or otherwise glean your account password, they still need access to your phone to discover the one-time code.
Depending on how you’ve set up two-step authentication, however, this may be far from airtight security. What’s more, not all two-step authentication methods are equally secure. Probably the most common form of secondary authentication — a one-time code sent to your mobile device via SMS/text message — is also the least secure.
That’s because thieves who manage to phish or otherwise filch your password can then simply ring your mobile provider pretending to be you, claiming that your phone is lost and that you need to activate a new phone and corresponding new SIM card. Or, they convince a gullible or inexperienced customer support rep to temporarily forward all of your calls and texts to a different number (this happened to me in 2013).
A harrowing story in The New York Times last week showcased several such hacks against Bitcoin enthusiasts, but in truth these types of social engineering attacks have been going on for years.
True, not everyone will attract the kind of interest from cybercrooks as someone holding large amounts of a non-repudiable virtual currency. But it’s still a good idea to take a few minutes and check whether some of the services you use that offer two-step authentication might offer an app-based method — such as Google Authenticator or Authy — as opposed to a text-based method.
By the way, I’m not the only one bugging people to move away from texting for codes: The National Institute of Standards and Technology (NIST) recently issued new proposed digital authentication guidelines urging organizations to favor other forms of two-factor — such as time-base one-time passwords generated by mobile apps — over text messaging.
Fortunately, some of the more popular online services offer multiple options for two-step authentication, although many of those that offer alternatives to texting one-time codes still steer users toward this option. I took stock of my own exposure to text-based two-step authentication and found three services I rely upon daily for my work still had the SMS option selected when a more secure app-based option was available.
Take a moment to review the authentication options available for the services you use on a regular basis. To do this, head on over to twofactorauth.org. A simple search for “Facebook,” for example, shows that the social networking site offers secondary authentication options via SMS, hardware token (such as a physical USB security key) and software token (Google Authenticator, e.g.).
In the case of Facebook, if you previously received one-time tokens via SMS, you may have to temporarily disable two-step authentication via text message before enabling the security key and software token approaches.
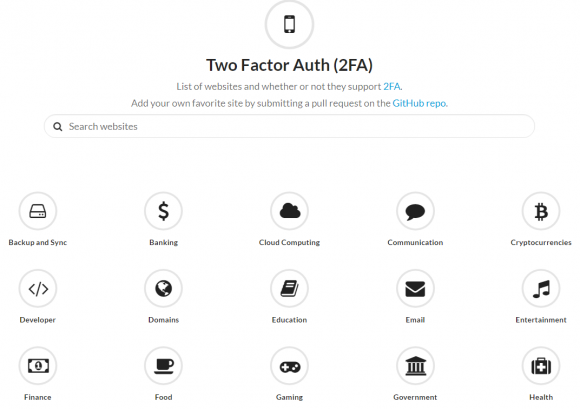
Lots of companies now offer multiple options for two-step authentication that go beyond SMS. Image: twofactorauth.org
Also, some people (present company included) need extra security and may be willing to put up with additional minor inconveniences in exchange for added peace of mind that thieves aren’t going to just waltz in and steal everything. This is particularly true for people with serious assets tied up in online sites and services that may not offer more robust authentication options.
This piece over at Techcrunch last week tells the story of another Bitcoin enthusiast who took some pretty extreme measures after someone tricked his mobile provider into switching his account to a new phone. Like requesting that the provider lock your phone’s SIM card to your device and prevent the phone from being used with another SIM card (the downside of this is if you really do lose your phone it could be much more complicated with this option turned on).
The story also recommends calling your telecommunications provider and asking them to set a passcode or PIN on your account that needs to be supplied before a customer service representative will discuss the account details.
“Make sure it applies to ALL account changes,” the Techcrunch pieces advises. “Make sure it applies to all numbers on the account. Ask them what happens if you forget the passcode. Ask them what happens if you lose that too.”
I should note that just because SMS is less secure than other forms of two-step authentication, that should not disqualify it as a worthwhile security step when more secure alternatives are unavailable. Any form of two-factor authentication is better than relying solely on usernames and passwords.
Some online services allow people to receive one-time codes via an automated phonecall. I hope it goes without saying this, but this method also is vulnerable to an attacker tricking a customer support person at your mobile provider into doing something they shouldn’t. Read the penultimate update to this 2012 blog post about how the CEO of Cloudflare had his account hacked after someone social engineered an AT&T representative into forwarding his second factor by automated phone call to a number the attackers controlled.
Finally, be judicious about what you install on your mobile device, and spend a few minutes researching the reputation and longevity of any app you wish to install before you install it. Also, pay close attention the permissions being requested by apps that you install: A mobile device compromised by mobile malware may not be the most reliable or secure second factor.




How many TFA systems allow the use of SMS tokens if an authentication app fails or is not available? I believe Google does. While that’s handy, it seems to set the security level back to that of the weakest link. Why bother using an authenticator at all if it just drops to SMS in a crunch?
Even if they hack the 2FA, you still have your password. That is why SMS is better than nothing.
You really are no safer than your password recovery scheme.
I still have Verisign “footballs.” Amazing how long they last.
Brian, I would like to research the reputation and longevity of my apps. How/where do you do that?
Also, the permissions demanded by apps that came pre-installed on my android phone horrify me as much as the ones demanded by apps I install. Why on earth do so many need access to my contacts? But if I try to deny them access, then they won’t update and will become security risks. If I try to delete the app (not the ones I install, but the pre-installed ones) I get messages from my phone that “things may malfunction.”
What do you suggest we do with them?
Read the reviews of the apps on their respective marketplaces. See what people are saying about them — if one of them is spying on you, someone savvy will call them out on it.
Check the permissions on them. See what they want access to. A calculator app, for example, should not need access to your contact list or the ability to make/receive phone calls or texts. Many security suites, like Avast, will check these things and alert you to programs that have high permission requirements.
I completely agree with Jim on this one – stick to android phones that are as close to stock Google as possible. Nokia has also promised to keep their android phones ‘pure’. Aside from not being loaded with a bunch of proprietary crap, you’ll get security and OS updates much quicker than waiting on the likes of Samsung to ‘adapt’ them to their flavor. Loving 8.0 by the way – so much easier to audit those rogue permissions than having to go from app to app.
Most apps have a version number and version history, as well as number of downloads listed. Avoid apps from unknown publishers at version 1.0 with downloads in the hundreds.
2 things.. First keep in mind the next phone you get.. buy a phone that doesn’t have bloat-ware.. look at Google Pixel (I have the Nexus 6P) try to stay away from provider offered phones, Samsung, LG.. Etc.. I would suggestion talking to your provider to see what can be removed safely.
Brian,
Also, don’t forget about the SS7 flaw that finally was exploited. Another reason to not use SMS.
http://www.darkreading.com/mobile/ss7-flaws-exploited-in-attacks-against-mobile-users-bank-accounts/d/d-id/1328805
WOW! Didn’t know that SS7 was, finally, hacked!
Nonetheless, it’s better to have 2WA with SMS than not having it.
Let me tell you what happened to me last week.
I’ve got two emails from Gmail (in Spanish, which is weird, since I never EVER use it for anything online, well, the only exception being amazon.es), sending me a code to reset my password.
I didn’t care that much since, being in Gmail since 3rd day of Beta, I know I have an address that many folks want to have and so, they mistaken it and so I get from hotel receipts to all sort of you name the service emails.
But, after four hours or so, I’ve see that my mobile is requesting me to approve a log in from a new computer.
Obviously, I declined and, seconds after my 14 char password was changed.
But, what if I hadn’t 2WA activated. They would have stolen my Gmail account (and, thus, all the rest of services I have from Bank to PayPal to all of them).
I don’t know who someone guess a 14 char password that had NOTHING TO do with me, but… that’s another story; what I want to say here is that, no matter what, is better to have 2WA, even with SMS, than not having it at all….
I’m guessing they didn’t guess your password
How could they have changed your password if you denied them access?
Is there any benefit to using paid GSuite as opposed to ‘free’ Gmail?
I am thinking about the scenario where one’s account is hijacked and it is difficult to get access to it, Gmail has no human customer support around account management.
Also, why were USB authenticators not mentioned in the article? Are they not as secure as 2FA.
Thanks!
USB auth devices are fixed objects and have a finite lifespan. They can also be stolen and used by a bad actor. Several of them also have had security vulnerabilities with them, like some of the RSA tokens, and because they’re a physical component they can’t be updated so easily, unlike a soft token. They’re great if you’re needing 2FA and don’t/can’t deal with SMS, but there’s better solutions out there like Google Auth, Duo, etc.
One benefit I have found using GSuite is that I can give every company & service I do business with a different email address, which forwards to a catchall@mydomain.com This is more secure than having a single email address which every hacked company and spammer has access to. It also makes it easier to identify phishing email or password reset requests sent to my email address jokesfrombob@mydomain.com – and helped me identify when a large online images for sale company got hacked a few years ago because I started getting spam at the address that I had only given to them.
Are USB authenticators worth considering – I was surprised they were not mentioned in the article.
Also, is GSuite a step-up in security from ‘free’ Gmail, if only for the fact that there might be human account support available.
If you lose access to your gmail you are pretty much on your own. …
Thanks
“… To do this, head on over to twofactorauth.org. A simple search for “Facebook,” for example, shows that the social networking site offers secondary authentication options via SMS, hardware token (such as a physical USB security key) and software token (Google Authenticator, e.g.).”
Link to Yubico provided.
I never use my cell phone for financial transactions. I also have Kaspersky installed for additional protection. I pay all bills with a dedicated email address from my PC not my cell phone. That email address is used ONLY for financial transactions. If I purchase something from the Google Play Store which is rare, I do it from home behind a well protected network. Once the transaction is complete, I disable it. So far, no problems.
Some carriers better than others or all equally gullible?
Ting wireless has the time-based pseudo-random-number generator, ie. like Google Authenticator/Authy.
They seem to serious about security and service.
Ting’s pricing is similar to how Google Fi does it. They charge only for usage, not fixed rate. If you can be on wi-fi most of the time it’s good.
They use TMobile (GSM) and Sprint (CDMA). The wi-fi calling works with GSM. They say “soon” wi-fi calling will work with CDMA.
It’s an interesting company, owned by Two Cows, like Hover.
Is TFA offered by all these providers really “two-factor”? I’ve been considering enabling TFA for my accounts, but I’ve so far not done so because I’m afraid that it’ll allow people to reset my account using just my phone… And I’ve got more confidence in the security of my computer than that of my phone, with the whole mess that is Android updates.
How about using a GVoice, RingCentral or other type of secondary phone number service for your 2FA instead of relying on mobile carriers? Could that be setup to be any safer? Any thoughts?
Yes, I definitely believe you/we will be more secure, if we use a phone number that nobody else knows for SMS 2FA.
If there is no way to correlate your real-world identity with the phone number, you will be safe.
I have a GV number that I only use for one 2FA. Nobody else has that number.
One of the problems with a VOIP-based number is that the SMS messages sometimes are not able to be received.
I haven’t completely figured out what is going on, but it seems there are multiple “types” of SMS messages, a short-form and a long-form. Some VOIP systems can’t receive short-form messages.
*** Reply, if you have more info about this? ***
Mobile operators could help here perhaps?
For example, when setting up SMS authentication the operators SMS platform could then forward on a part the IMSI as part of the message. Intelligence could then be put in place to check any authentication code sent against the list or registered IMIS’s. Should your account get moved to a different handset or sim this would fail as the IMSI is unique to the original SIM Card.
Also given the ammount of inteligenc onboard SIM’s thedays some sort of embeded authetication could be used moving forward.
Keep in mind, with VoIP 2FA, that can reduce back down to 1FA – multilayered as it is.
If someone gains access to your VoIP account, then they get your codes. It’s no longer about password + possession, it’s now just password.
Another thing to consider for 2FA security: if you’re in the presence of someone who’s interested in getting into your accounts (coffee shop, perhaps?), they could look over your shoulder for the code. And many phones default to displaying the content of newly received text messages on their lock screen.
Last time I tried to disable SMS authentication on Facebook, it locked me out and disabled my account, even though I had enabled software token (Google Auth).
You have to enable a hardware token to use FB 2FA without a phone. After that you can use either the token or TOTP app to login.
All,
The article mashes together multi-step and multi-factor types of authentication.
Multi-factor authentication: a method of logon verification where at least two different factors of proof are provided, and jointly verified. There are three generally recognized types of authentication factors:
• Type 1 – Something You Know. Type 1 includes, but is not limited to, passwords, PINs, combinations, code words, or secret handshakes. Anything that a user can remember and then type, say, do, perform, or otherwise recall when needed falls into this category.
• Type 2 – Something You Have. Type 2 includes all items that are physical objects, such as, but not limited to, keys, smart phones, smart cards, USB drives, and token devices. (A token device produces a time-based PIN or can compute a response from a challenge number issued by the server.)
• Type 3 – Something You Are. Type 3 includes any part of the human body that can be offered for verification, such as, but not limited to, fingerprints, palm scanning, facial recognition, retina scans, iris scans, and voice verification.
Multi-step authentication: a method of logon verification where the authentication can take several steps or phases to complete. Multi-step authentication differs from multi-factor authentication in that it does not strictly require that each authentication factor be different, or that multiple factors are evaluated in conjunction.
Very often, the existing schemes utilizing SMS are actually providing Multi-Step Authentication rather than Multi-Factor one.
In addition, let’s not forget that the use of False Base Station would allow the attacker to intercept the verification SMS, rendering the whole security scheme useless.
What is also interesting with regards to 2FA, there is FIDO U2F scheme which protects even against hacks at provider (e.g. Google, Facebook, et al), but… There is bunch of small buts there and here. For starters there are only few of them who do care – Google, Facebook, Github, and that might be all among popular ones. Then comes “specific of implementations” – most of them abhor at Firefox while plugin for Firefox actually implements U2F quite well, and push you to use Chrome. And if you substitute user-agent line in request with another plugin, Facebook let you actually use it, while Google makes error. which suggests their implementation is not necessarily following U2F specs. Github also uses U2F. I suggest you try to dive in yourself – there are few makers of U2F dongles, with risks to never get down to bottom. But I presume those who needed it – had it done already, this or that way.
It seems like a great idea where nearly everyone is waiting for someone else to do something.
Only some browsers work right now. Firefox and IE do not, although they talk about it. Come to think about it, there seems to be some progress (at a glacial pace) from Firefox, but I don’t know whether it is usable or not.
Not many websites support it – probably because not many browsers support it, and once that is fixed, not many people would have the tokens.
Not many users have it – I have one, but only because the Yubikey that I have happens to support it. Ultimately lots of users would be turned off by any scheme that requires them to go out and buy something – far too many people are far too lazy.
So we are in this world where nobody wants to do anything, and when push comes to shove websites do the SMS 2FA because it is quick and easy and nearly everyone has a phone.
Doesn’t SMS phishing come from spoofed 10-digit numbers, rather than 5 or 6-digit short codes that are purchased by most billion dollar companies that are more serious about security? Or have hackers figured out a way spoof short codes?
Re: twofactorauth[dot]org
“It looks like you have JavaScript disabled!
You are so right! That’s what I expected NoScript to do when I installed it. Good job!
“Without JavaScript, this page probably won’t work very well.”
No “probably” about it. It does not work at all. (sigh)
“thieves… ring your mobile provider pretending to be you” – this doesn’t work if you’ve changed cell phone providers and ported the number. Every search of my phone number shows my old provider, not my current one.
That’s interesting! Wonder if the old provider knows who the number was ported to. I’d hate for a social engineering attack to find out they’re calling the old one, and convince them to give up the info so they can call the new one.
Apple’s 2FA scheme for iCloud uses SMS only for initial establishment. Once that’s done and you have a “trusted device” then there’s no longer any reliance on the (in)security of SMS.
Another issue with SMS and phone calls: fraudsters can also get your telco credentials with phishing. Then they can set up call redirects or order a new SIM. Where I work we require these kind of OTPs for all sensitive operations, and some customers get defrauded this way. We’ve seen different scenarios: either they fall for 2 different phishing emails, or only one which asks our credentials, then requires customer to confirm some personal info including phone/ISP (typically bundled in Europe) email address & password.
So, with 2FA, suppose I buy a cheap phone that only has voice and text, and (as someone else pointed out) use it for nothing but 2FA.
Combine that with a dedicated e-mail address used only for financial sites, and nothing else.
How secure is that?
Maybe use a dedicated computer only for financial purposes, and left turned off, except to get updates and to work financial transactions?
It sounds pretty paranoid, but the more I read this blog the more paranoid I get…
Good, except I wonder about the phone piece. If it’s a rarely-used phone, it’s less likely you’ll notice that you’re not getting calls / texts like you should due to it being redirected to the thief.
Then again, maybe one of those ultra cheap pay as you go phones that you pay with cash would work. That way it’s not tied to your name, and you leave it locked in a safe, so literally no one knows it exists.
Microsoft Authenticator is used by my company on multiple entry points, and I have to say, it works really well!
Maybe and lucky you. This is not across the board.
There appears to be NO interoperability between sites and authenticators. I looked at implementing 2FA with MS and it **appears** Outlook/Hotmail will NOT accept any authenticator app other than MS’ own authenticator. And I guess Google is the same way. And NEITHER seem to accept Auth or any other 3rd party authenticator.
I can understand and appreciate MS’ need to promote their products, same as Google and FB and others, but this is ridiculous. But I DON’T want to install and manage so many different authenticators. My life, as I am sure of most people here, is already tooooo complicated. If I use Google Authenticator to log into Outlook, MS should still be happy pushing ads my way in order to make money.
Not only that, you have to dig down into every site to find out if and how they implement 2FA; there does not appear to be a central database on the Net providing links.
And how many sites do I need to log into each day/week/month? Multiply that out. Geez.
There’s gotta be a simpler way. SIGH!
I have all my accounts that support 2FA applications working on Authy including dropbox, gmail and MS onedrive. I haven’t tried to setup my hotmail accounts as they are burn accounts that i don’t really care about (all made up identity information).
Are secure e2e-encrypted messaging apps like Signal and WhatsApp (that are based on a phone number) vulnerable to social engineering hacks? Thanks!
Depends on how the codes are sent. I’m guessing the sending party won’t be encrypting (and if they did, how would Signal decrypt without prior notice?), so it wouldn’t be E2E encryption. If the bad people can intercept the message before it hits your phone, it’s still game over, and that’s what Krebs was talking about – getting the telco to redirect messages to their phone.
I get the idea that this is the draw for authenticators – Google sends an encrypted code, which is only decrypted upon being displayed on your phone. Total guess from my part, as I’ve not used one yet, but I’m considering it.