In early August 2017, FBI agents in Las Vegas arrested 23-year-old British security researcher Marcus Hutchins on suspicion of authoring and/or selling “Kronos,” a strain of malware designed to steal online banking credentials. Hutchins was virtually unknown to most in the security community until May 2017 when the U.K. media revealed him as the “accidental hero” who inadvertently halted the global spread of WannaCry, a ransomware contagion that had taken the world by storm just days before.
Relatively few knew it before his arrest, but Hutchins has for many years authored the popular cybersecurity blog MalwareTech. When this fact became more widely known — combined with his hero status for halting Wannacry — a great many MalwareTech readers quickly leapt to his defense to denounce his arrest. They reasoned that the government’s case was built on flimsy and scant evidence, noting that Hutchins has worked tirelessly to expose cybercriminals and their malicious tools. To date, some 226 supporters have donated more than $14,000 to his defense fund.

Marcus Hutchins, just after he was revealed as the security expert who stopped the WannaCry worm. Image: twitter.com/malwaretechblog
At first, I did not believe the charges against Hutchins would hold up under scrutiny. But as I began to dig deeper into the history tied to dozens of hacker forum pseudonyms, email addresses and domains he apparently used over the past decade, a very different picture began to emerge.
In this post, I will attempt to describe and illustrate more than three weeks’ worth of connecting the dots from what appear to be Hutchins’ earliest hacker forum accounts to his real-life identity. The clues suggest that Hutchins began developing and selling malware in his mid-teens — only to later develop a change of heart and earnestly endeavor to leave that part of his life squarely in the rearview mirror.
GH0STHOSTING/IARKEY
I began this investigation with a simple search of domain name registration records at domaintools.com [full disclosure: Domain Tools recently was an advertiser on this site]. A search for “Marcus Hutchins” turned up a half dozen domains registered to a U.K. resident by the same name who supplied the email address “surfallday2day@hotmail.co.uk.”
One of those domains — Gh0sthosting[dot]com (the third character in that domain is a zero) — corresponds to a hosting service that was advertised and sold circa 2009-2010 on Hackforums[dot]net, a massively popular forum overrun with young, impressionable men who desperately wish to be elite coders or hackers (or at least recognized as such by their peers).
The surfallday2day@hotmail.co.uk address tied to Gh0sthosting’s initial domain registration records also was used to register a Skype account named Iarkey that listed its alias as “Marcus.” A Twitter account registered in 2009 under the nickname “Iarkey” points to Gh0sthosting[dot]com.
Gh0sthosting was sold by a Hackforums user who used the same Iarkey nickname, and in 2009 Iarkey told fellow Hackforums users in a sales thread for his business that Gh0sthosting was “mainly for blackhats wanting to phish.” In a separate post just a few days apart from that sales thread, Iarkey responds that he is “only 15” years old, and in another he confirms that his email address is surfallday2day@hotmail.co.uk.
A review of the historic reputation tied to the Gh0sthosting domain suggests that at least some customers took Iarkey up on his offer: Malwaredomainlist.com, for example, shows that around this same time in 2009 Gh0sthosting was observed hosting plenty of malware, including trojan horse programs, phishing pages and malware exploits.
A “reverse WHOIS” search at Domaintools.com shows that Iarkey’s surfallday2day email address was used initially to register several other domains, including uploadwith[dot]us and thecodebases[dot]com.
Shortly after registering Gh0sthosting and other domains tied to his surfallday2day@hotmail.co.uk address, Iarkey evidently thought better of including his real name and email address in his domain name registration records. Thecodebases[dot]com, for example, changed its WHOIS ownership to a “James Green” in the U.K., and switched the email to “herpderpderp2@hotmail.co.uk.”
A reverse WHOIS lookup at domaintools.com for that email address shows it was used to register a Hackforums parody (or phishing?) site called Heckforums[dot]net. The domain records showed this address was tied to a Hackforums clique called “Atthackers.” The records also listed a Michael Chanata from Florida as the owner. We’ll come back to Michael Chanata and Atthackers at the end of this post.
DA LOSER/FLIPERTYJOPKINS
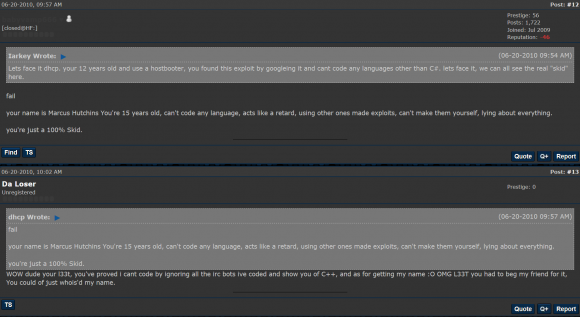
As early as 2009, Iarkey was outed several times on Hackforums as being Marcus Hutchins from the United Kingdom. In most of those instances he makes no effort to deny the association — and in a handful of posts he laments that fellow members felt the need to “dox” him by posting his real address and name in the hacking forum for all to see.
Iarkey, like many other extremely active Hackforums users, changed his nickname on the forum constantly, and two of his early nicknames on Hackforums around 2009 were “Flipertyjopkins” and “Da Loser“.
Happily, Hackforums has a useful feature that allows anyone willing to take the time to dig through a user’s postings to learn when and if that user was previously tied to another account.
This is especially evident in multi-page Hackforums discussion threads that span many days or weeks: If a user changes his nickname during that time, the forum is set up so that it includes the user’s most previous nickname in any replies that quote the original nickname — ostensibly so that users can follow along with who’s who and who said what to whom.
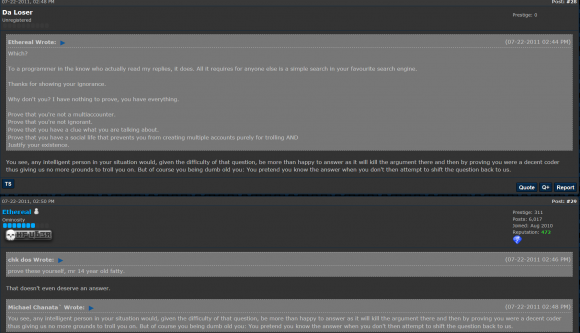
In the screen shot below, for instance, we can see one of Hutchins’ earliest accounts — Da Loser — being quoted under his Flipertyjopkins nickname.
Both the Da Loser and Flipertyjopkins identities on Hackforums referenced the same domains in 2009 as theirs — Gh0sthosting — as well as another domain called “hackblack.co[dot]uk.” Da Loser references the hackblack domain as the place where other Hackforums users can download “the sourcecode of my IE/MSN messenger password stealer (aka M_Stealer).”
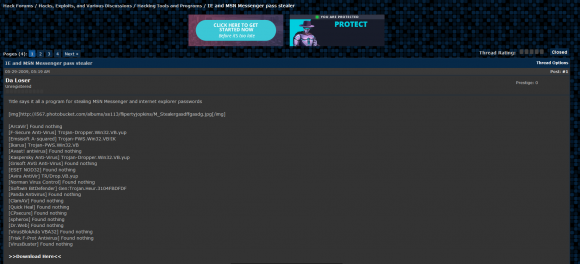
In another post, Da Loser brags about how his password stealing program goes undetected by multiple antivirus scanners, pointing to a (now deleted) screenshot at a Photobucket account for a “flipertyjopkins”:
Another screenshot from Da Loser’s postings in June 2009 shows him advertising the Hackblack domain and the Surfallday2day@hotmail.co.uk address:
Hackforums user “Da Loser” advertises his “Hackblack” hosting and points to the surfallday2day email address.
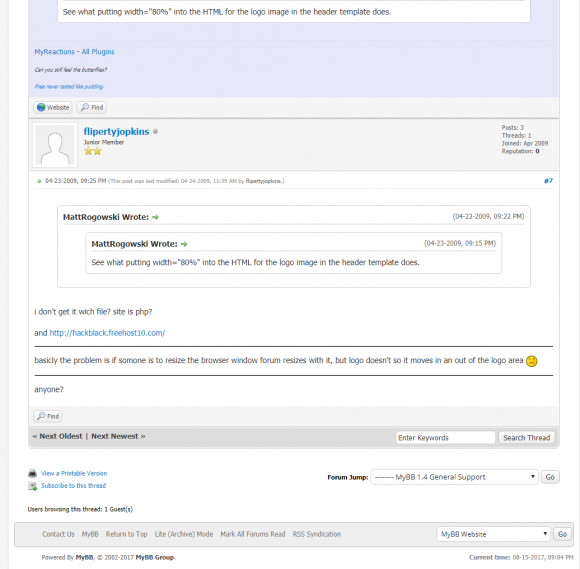
An Internet search for this Hackblack domain reveals a thread on the Web hosting forum MyBB started by a user Flipertyjopkins, who asks other members for help configuring his site, which he lists as http://hackblack.freehost10[dot]com.
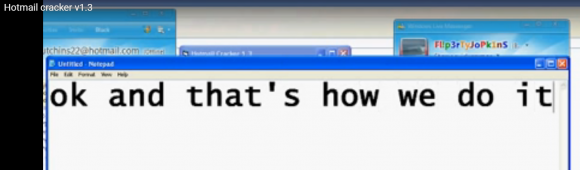
Poking around the Web for these nicknames and domains turned up a Youtube user account named Flipertyjopkins that includes several videos uploaded 7-8 years ago that instruct viewers on how to use various types of password-stealing malware. In one of the videos — titled “Hotmail cracker v1.3” — Flipertyjopkins narrates how to use a piece of malware by the same name to steal passwords from unsuspecting victims.
Approximately two minutes and 48 seconds into the video, we can briefly see an MSN Messenger chat window shown behind the Microsoft Notepad application he is using to narrate the video. The video clearly shows that the MSN Messenger client is logged in to with the address “hutchins22@hotmail.com.”
To close out the discussion of Flipertyjopkins, I should note that this email address showed up multiple times in the database leak from Hostinger.co.uk, a British Web hosting company that got hacked in 2015. A copy of that database can be found in several places online, and it shows that one Hostinger customer named Marcus used an account under the email address flipertyjopkins@gmail.com.
According to the leaked user database, the password for that account — “emmy009” — also was used to register two other accounts at Hostinger, including the usernames “hacker” (email address: flipertyjopkins@googlemail.com) and “flipertyjopkins” (email: surfallday2day@hotmail.co.uk).
ELEMENT PRODUCTS/GONE WITH THE WIND
Most of the activities and actions that can be attributed to Iarkey/Flipertyjopkins/Da Loser et. al on Hackforums are fairly small-time — and hardly rise to the level of coding from scratch a complex banking trojan and selling it to cybercriminals.
However, multiple threads on Hackforums state that Hutchins around 2011-2012 switched to two new nicknames that corresponded to users who were far more heavily involved in coding and selling complex malicious software: “Element Products,” and later, “Gone With The Wind.”
Hackforums’ nickname preservation feature leaves little doubt that the user Element Products at some point in 2012 changed his nickname to Gone With the Wind. However, for almost a week I could not see any signs of a connection between these two accounts and the ones previously and obviously associated with Hutchins (Flipertyjopkins, Iarkey, etc.).
In the meantime, I endeavored to find out as much as possible about Element Products — a suite of software and services including a keystroke logger, a “stresser” or online attack service, as well as a “no-distribute” malware scanner.
Unlike legitimate scanning services such as Virustotal — which scan malicious software against dozens of antivirus tools and then share the output with all participating antivirus companies — no-distribute scanners are made and marketed to malware authors who wish to see how broadly their malware is detected without tipping off the antivirus firms to a new, more stealthy version of the code.
Indeed, Element Scanner — which was sold in subscription packages starting at $40 per month — scanned all customer malware with some 37 different antivirus tools. But according to posts from Gone With the Wind, the scanner merely resold the services of scan4you[dot]net, a multiscanner that was extremely powerful and popular for several years across a variety of underground cybercrime forums.

According to a story at Bleepingcomputer.com, scan4you disappeared in July 2017, around the same time that two Latvian men were arrested for running an unnamed no-distribute scanner.
[Side note: Element Scanner was later incorporated as the default scanning application of “Blackshades,” a remote access trojan that was extremely popular on Hackforums for several years until its developers and dozens of customers were arrested in an international law enforcement sting in May 2014. Incidentally, as the story linked in the previous sentence explains, the administrator and owner of Hackforums would play an integral role in setting up many of his forum’s users for the Blackshades sting operation.]
According to one thread on Hackforums, Element Products was sold in 2012 to another Hackforums user named “Dal33t.” This was the nickname used by Ammar Zuberi, a young man from Dubai who — according to this this January 2017 KrebsOnSecurity story — may have been associated with a group of miscreants on Hackforums that specialized in using botnets to take high-profile Web sites offline. Zuberi could not be immediately reached for comment.
I soon discovered that Element Products was by far the least harmful product that this user sold on Hackforums. In a separate thread in 2012, Element Products announces the availability of a new product he had for sale — dubbed the “Ares Form Grabber” — a program that could be used to surreptitiously steal usernames and passwords from victims.
Element Products/Gone With The Wind also advertised himself on Hackforums as an authorized reseller of the infamous exploit kit known as “Blackhole.” Exploit kits are programs made to be stitched into hacked and malicious Web sites so that when visitors browse to the site with outdated and insecure browser plugins the browser is automatically infected with whatever malware the attacker wishes to foist on the victim.
In addition, Element Products ran a “bot shop,” in which he sold access to bots claimed to have enslaved through his own personal use of Blackhole:
Gone With The Wind’s “Bot Shop,” which sold access to computers hacked with the help of the Blackhole exploit kit.
A bit more digging showed that the Element Products user on Hackforums co-sold his wares along with another Hackforums user named “Kill4Joy,” who advertised his contact address as kill4joy@live.com.
Ironically, Hackforums was itself hacked in 2012, and a leaked copy of the user database from that hack shows this Kill4Joy user initially registered on the forum in 2011 with the email address rohang93@live.com.
A reverse WHOIS search at domaintools.com shows that email address was used to register several domain names, including contegoprint.info. The registration records for that domain show that it was registered by a Rohan Gupta from Illinois.
I learned that Gupta is now attending graduate school at the University of Illinois at Urbana-Champaign, where he is studying computer engineering. Reached via telephone, Gupta confirmed that he worked with the Hackforums user Element Products six years ago, but said he only handled sales for the Element Scanner product, which he says was completely legal.
“I was associated with Element Scanner which was non-malicious,” Gupta said. “It wasn’t black hat, and I wasn’t associated with the programming, I just assisted with the sales.”
Gupta said his partner and developer of the software went by the name Michael Chanata and communicated with him via a Skype account registered to the email address atthackers@hotmail.com.
Recall that we heard at the beginning of this story that the name Michael Chanata was tied to Heckforums.net, a domain closely connected to the Iarkey nickname on Hackforums. Curious to see if this Michael Chanata character showed up somewhere on Hackforums, I used the forum’s search function to find out.
The following screenshot from a July 2011 Hackforums thread suggests that Michael Chanata was yet another nickname used by Da Loser, a Hackforums account associated with Marcus Hutchins’ early email addresses and Web sites.
BV1/ORGY
Interesting connections, to be sure, but I wasn’t satisfied with this finding and wanted more conclusive evidence of the supposed link. So I turned to “passive DNS” tools from Farsight Security — which keeps a historic record of which domain names map to which IP addresses.
Using Farsight’s tools, I found that Element Scanner’s various Web sites (elementscanner[dot]com/net/su/ru) were at one point hosted at the Internet address 184.168.88.189 alongside just a handful of other interesting domains, including bigkeshhosting[dot]com and bvnetworks[dot]com.
At first, I didn’t fully recognize the nicknames buried in each of these domains, but a few minutes of searching on Hackforums reminded me that bigkeshhosting[dot]com was a project run by a Hackforums user named “Orgy.”
I originally wrote about Orgy — whose real name is Robert George Danielson — in a 2012 story about a pair of stresser or “booter” (DDoS-for-hire) sites. As noted in that piece, Danielson has had several brushes with the law, including a guilty plea for stealing multiple firearms from the home of a local police chief.
I also learned that the bvnetworks[dot]com domain belonged to Orgy’s good friend and associate on Hackforums — a user who for many years went by the nickname “BV1.” In real life, BV1 is 27-year-old Brendan Johnston, a California man who went to prison in 2014 for his role in selling the Blackshades trojan.
When I discovered the connection to BV1, I searched my inbox for anything related to this nickname. Lo and behold, I found an anonymous tip I’d received through KrebsOnSecurity.com’s contact form in March 2013 which informed me of BV1’s real identity and said he was close friends with Orgy and the Hackforums user Iarkey.
According to this anonymous informant, Iarkey was an administrator of an Internet relay chat (IRC) forum that BV1 and Orgy frequented called irc.voidptr.cz.
“You already know that Orgy is running a new booter, but BV1 claims to have ‘left’ the hacking business because all the information on his family/himself has been leaked on the internet, but that is a lie,” the anonymous tipster wrote. “If you connect to http://irc.voidptr. cz ran by ‘touchme’ aka ‘iarkey’ from hackforums you can usually find both BV1 and Orgy in there.”
TOUCHME/TOUCH MY MALWARE/MAYBE TOUCHME
Until recently, I was unfamiliar with the nickname TouchMe. Naturally, I started digging into Hackforums again. An exhaustive search on the forum shows that TouchMe — and later “Touch Me Maybe” and “Touch My Malware” — were yet other nicknames for the same account.
In a Hackforums post from July 2012, the user Touch Me Maybe pointed to a writeup that he claimed to have authored on his own Web site: touchmymalware.blogspot.com:
The Hackforums user “Touch Me Maybe” seems to refer to his own blog and malware analysis at touchmymalware.blogspot.com, which now redirects to Marcus Hutchins’ blog — Malwaretech.com
If you visit this domain name now, it redirects to Malwaretech.com, which is the same blog that Hutchins was updating for years until his arrest in August.
There are other facts to support a connection between MalwareTech and the IRC forum voidptr.cz: A passive DNS scan for irc.voidptr.cz at Farsight Security shows that at one time the IRC channel was hosted at the Internet address 52.86.95.180 — where it shared space with just one other domain: irc.malwaretech.com.
All of the connections explained in this blog post — and some that weren’t — can be seen in the following mind map that I created with the excellent MindNode Pro for Mac.
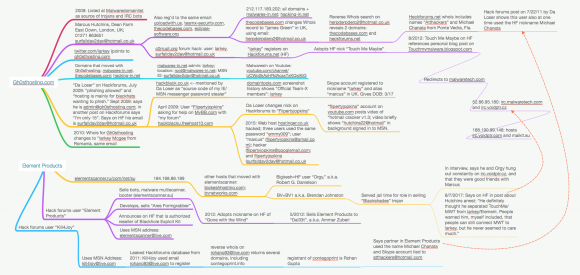
A mind map I created to keep track of the myriad data points mentioned in this story. Click the image to enlarge.
Following Hutchins’ arrest, multiple Hackforums members posted what they suspected about his various presences on the forum. In one post from October 2011, Hackforums founder and administrator Jesse “Omniscient” LaBrocca said Iarkey had hundreds of accounts on Hackforums.
In one of the longest threads on Hackforums about Hutchins’ arrest there are several postings from a user named “Previously Known As” who self-identifies in that post and multiple related threads as BV1. In one such post, dated Aug. 7, 2017, BV1 observes that Hutchins failed to successfully separate his online selves from his real life identity.
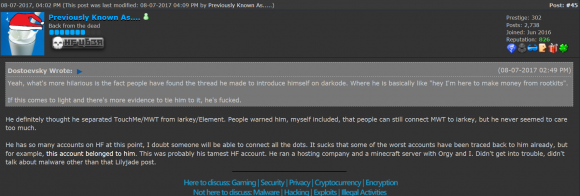
Brendan “BV1” Johnston says he worried his old friend’s operational security mistakes would one day catch up with him.
“He definitely thought he separated TouchMe/MWT from iarkey/Element,” said BV1. “People warned him, myself included, that people can still connect MWT to iarkey, but he never seemed to care too much. He has so many accounts on HF at this point, I doubt someone will be able to connect all the dots. It sucks that some of the worst accounts have been traced back to him already. He ran a hosting company and a Minecraft server with Orgy and I.”
In a brief interview with KrebsOnSecurity, Brendan “BV1” Johnston said Hutchins was a good friend. Johnston said Hutchins had — like many others who later segued into jobs in the information security industry — initially dabbled in the dark side. But Johnston said his old friend sincerely tried to turn things around in late 2012 — when Gone With the Wind sold most of his coding projects to other Hackforums members and began focusing on blogging about poorly-written malware.
“I feel like I know Marcus better than most people do online, and when I heard about the accusations I was completely shocked,” Johnston said. “He tried for such a long time to steer me down a straight and narrow path that seeing this tied to him didn’t make sense to me at all.”
Let me be clear: I have no information to support the claim that Hutchins authored or sold the Kronos banking trojan. According to the government, Hutchins did so in 2014 on the Dark Web marketplace AlphaBay — which was taken down in July 2017 as part of a coordinated, global law enforcement raid on AlphaBay sellers and buyers alike.
However, the findings in this report suggest that for several years Hutchins enjoyed a fairly successful stint coding malicious software for others, said Nicholas Weaver, a security researcher at the International Computer Science Institute and a lecturer at UC Berkeley.
“It appears like Mr. Hutchins had a significant and prosperous blackhat career that he at least mostly gave up in 2013,” Weaver said. “Which might have been forgotten if it wasn’t for the involuntary British press coverage on WannaCry raising his profile and making him out as a ‘hero’.”
Weaver continued:
“I can easily imagine the Feds taking the opportunity to use a penny-ante charge against a known ‘bad guy’ when they can’t charge for more significant crimes,” he said. “But the Feds would have done far less collateral damage if they actually provided a criminal complaint with these sorts of detail rather than a perfunctory indictment.”
Hutchins did not try to hide the fact that he has written and published unique malware strains, which in the United States at least is a form of protected speech.
In December 2014, for example, Hutchins posted to his Github page the source code to TinyXPB, malware he claims to have written that is designed to seize control of a computer so that the malware loads before the operating system can even boot up.
While the publicly available documents related to his case are light on details, it seems clear that prosecutors can make a case against those who attempt to sell malware to cybercriminals — such as on hacker forums like AlphaBay — if they can demonstrate the accused had knowledge and intent that the malware would be used to commit a crime.
The Justice Department’s indictment against Hutchins suggests that the prosecution is relying heavily on the word of an unnamed co-conspirator who became a confidential informant for the government. Update, 9:08 a.m.: Several readers on Twitter disagreed with the previous statement, noting that U.S. prosecutors have said the other unnamed suspect in the Hutchins indictment is still at large.
Original story:
According to a story at BankInfoSecurity, the evidence submitted by prosecutors for the government includes:
- Statements made by Hutchins after he was arrested.
- A CD containing two audio recordings from a county jail in Nevada where he was detained by the FBI.
- 150 pages of Jabber chats between the defendant and an individual.
- Business records from Apple, Google and Yahoo.
- Statements (350 pages) by the defendant from another internet forum, which were seized by the government in another district.
- Three to four samples of malware.
- A search warrant executed on a third party, which may contain some privileged information.
Hutchins declined to comment for this story, citing his ongoing prosecution. He has pleaded not guilty to all four counts against him, including conspiracy to distribute malicious software with the intent to cause damage to 10 or more affected computers without authorization, and conspiracy to distribute malware designed to intercept protected electronic communications. FBI officials have not yet responded to requests for comment.




Real interesting article
Incredible reporting! Brian, your arms must be the size of tree trunks with all the digging you have done. Keep up the great work.
boy the man dam god reporter man plus Hutchinson is good hacker man
To balance this its worth remembering that many in InfoSec ended up in that line of work due to dark past. If everyone one of those folk were arrested for their past the InfoSec community would be in tatters.
The most salient point on here is “Let me be clear: I have no information to support the claim that Hutchins authored or sold the Kronos banking trojan.”
Might be true. But don’t forget that stopping with criminal activity, or turning your life around in a positive way, does not provide any kind of immunity regarding prosecution for past criminal behavior. It will be taken into consideration by most judges during sentencing (if found guilty of course).
And perhaps a better, more ethical Information Security community would come out of the tatters.
“more ethical Information Security community”
Why the hate?
I can think of a lot more UN-ethical communities
-Politicians
-Lawyers
-Bankers
-Sales-anything
Federal law enforcement agents.
Has Hutchins burnt down a church and killed nearly a hundred people?
Did Hutchins shoot a mother in the head while she was holding her baby?
I’m not sure anyone has claimed he’s done those things, or that it even matters. It’s a pretty weak defense of someone to point out much more egregious things they could have done but didn’t.
“But your honor! I only killed _one_ person! I could have killed three!”
It’s weak to endorse organizations which commit crimes like these, and get away with them.
FBI must go, one way or another.
The problem with forgiving hackers with a “dark past” is that the damage has already been done, who knows how many other malicious hackers these people helped nurture and are still out there. Every time one has a “change of heart” and then becomes a successful security consultant, it teaches people that if they’re good at hiding their tracks, or are willing to “change their mind” later in life, they can still break laws and help other people who might never do good with the same technology. I don’t think you can ever fully trust these people, when compared to the full workforce of cybersecurity professionals who never had to break the law to know they wanted to do good for society with their skills. Who’s to say their heart won’t change again?
Just like Frank Abagnale and Kevin Mitnick, right?
“Just like Frank Abagnale and Kevin Mitnick, right?”
I sense the sarcasm, but that’s exactly right – you named 2 people who “maybe” gave back enough to make up for the damage they did in the past, I wonder how many engineers are out there who never had to break the law? Why are those 2 names held so much higher than people who do their job unrecognized every single day? What did they do to deserve fame besides break the law?
I’m pretty sure your view is going to win out in the end. Having a record has always made it hard to get any good jobs, this won’t be any different.
These guys seem to think that their skills will bail them out in the end. They look at the high profile exceptions that succeed anyway and think that will be them. But for most of them no, not really. Companies want people who they don’t think will make trouble. There might be a talent shortage now that works in their favor, but that won’t be the case forever.
And even if they get one good job afterwards, that black mark will still be there in a couple of years once they have to go get another. It never ends. It will follow them around to the end, even after the technology changes.
What about the bankers that destroyed millions of lives in 2008 and will again in the near future?
They never have a change of heart and are never prosecuted for their crimes… why throw 15 yr old script kiddies in jail when you aren’t going to throw scam artists in jail for stealing Trillions from tax payers?
Wait… everyone hates “hackers” when in reality they should hate politicians and bankers.
keep up the hate
What do bankers have to do with hackers? I’m not getting the causal element for the comparison.
I dislike all criminals equally.
if a low-level criminal writes a trojan that steals money from high-level criminals (bankers)… who should they arrest?
In this case, they went after the low hanging fruit/criminal that did little damage compared to the high-level criminals-the bankers.
My point is, go after the politicians, bankers, etc that are causing real harm to the world… script kiddies are not worth chasing down and prosecuting… They should have to show how much has been spent in this “case” vs how much damage has been caused. If A>B=!arrest
That was about all I meant, sorry prob not enough coffee yesterday!
In the case if an obviously repentant sinner, criminal prosecution is not the most appropriate course. He should, however, make restitution, as far as possible, to those whom he has harmed.
Criminal prosecution would be an act of revenge to no useful purpose. Like the old debtors’ prison, it would destroy his ability to make restitution (and might even discourage present day miscreants from reforming).
Also, a lot of the people in infosec, with less than stellar past, did so before a lot of the more stringent laws (at least in the US) were passed. People today need to remember that we are not in the same naive world of some ten plus years ago.
I hope that those that have come to his aid haven’t ended up joining in digging a hole.
They haven’t.
Weev was right.
Hutchins dindu nuffin.
Here we go again . Another Very Good example of ” American justice at work “– script kiddie got busted for nothing .Oh Dear
My only problem is that After all this years it seems to me that Brian can only catch script kiddies and low level cyber crooks .
Im sick and tired of them 3 lines of code people .Where is the bigger fish ?
They are trolling their yachts on the Black Sea… that’s where they are 🙂
Think there’s a minor mistake in the article.
You’re saying Hostinger was hacked and providing this URL https://www.habschned.com/hostinger-hacked-well-their-prices-are/
but the url is just saying that the prices got ‘hacked’ i.e. there’s a discount coupon (they are only talking about the infamous 000webhost.com) hack.
Other than that – very interesting article, hope Hutchins will be able to go home soon.
Thanks. I was trying to avoid linking to Forbes, which makes visitors load like 50 pieces of third-party javascript before viewing any stories. I’ve changed the link to the Forbes piece, but if anyone can find a suitable substitute please let me know here.
for such nuisances as forbes.com, I use privoxy. available free at privoxy.org
this free ad blocker runs as a localhost proxy server.
you can set up firefox to utilize privoxy for surfing with no ads, and let the other browsers on your system ignore it for sites that don’t allow ad blocking.
The Forbes article is archived here, without all the unwanted junk
http://archive.is/G6x05
Brian, all of that said, is there any reason to doubt his “accidental” discovery of WannaCry and, instead, him being somehow on the inside of it?
Yes, there is. Part of his job at Kryptos was sinkholing botnets. You can see lots of examples of these if you follow the email that registered the domain called out in the wannacry malware.
Oh come on, this in no way implies he had anything to do with the creation of WannaCry. I even wrote a post explaining why this is an unfounded claim http://blog.devit.co/on-wannacry-killswitch/
My first instinct when he came out as the savior of WannaCry was “This dude’s a hacker, he knows who wrote/released WannaCry, petty disagreement ensued, so he stopped the hack.”
I don’t think he wrote WannaCry but he knows who did, I bet.
Said domains email is now a randomly generated WhoisGuard email.
It used to be botnetsinkhole [at] gmail [dot] com
Like myself and others have said before. I can’t speak for Marcus’s innocence but finding the WannaCry killswitch domain was trivial.
I firmly believe in due process and transparency in a court of law.
Nice detective work, Brian, as usual.
I wonder, though, wouldn’t anything he may or may not have done back in 2012 have been crimes committed as a minor? Can they still chase him down for such 5 years later?
(IANAL, but you could probably tell.)
”Here we go again . Another Very Good example of ” American justice at work “– script kiddie got busted for nothing .Oh Dear”
Wonder if you would still consider it nothing if you were hit by banking malware, and if your bank account would be plundered. Making such software available to criminals is not nothing. And he does not go to trial for being a ‘script kiddie’. But for facilitating serious criminal activity.
Enjoyed the article.
Nice work (as usual)! Thanks, Brian.
Regards,
Interesting tear down. It’s a shame that if you want to get beyond a certain level in this industry you have to get your hands dirty. Bouncing CTFs and busting VMs only get you so far, at least he attempted to put the knowledge he gained to good use.
Which is why the security industry needs to move away from “hats” in general and more towards designing systems that are resistant to malware and other attacks along with methods to formally verify their effectiveness.
“…designing systems that are resistant to malware and other attacks along with methods to formally verify their effectiveness.”
This won’t happen: There’s no money in it. We don’t have much of a choice at this point. We either:
1. Implement regulations and penalties to hold purveyors of crap software liable for their shoddy work, and force them to fix the problems before continuing to profit.
OR:
2. We wait for the inevitable “Black Swan” where so so many people get hurt that fixing the insecure software infrastructure becomes a categorical imperative. Remember the crash of 1929, Pearl Harbor and 9/11? Well, when all the lights go out and all the bank accounts are emptied, then things will start to change very quickly and it won’t be pretty.
Very good article.
Yes, they went back and got one of the dooers. Yes, that’s how the government finds it do ers. There are classes on how to code, boot and such, but to hack? Ah, yeah, right, but security, and such cannot keep up with independent studies. Oh, there are classes on hacking, but those are tools classes. Someone develops tools, and even tools need to be developed. So, prey tell, does one get ahead of the hackers?
Not exactly. There are excellent classes at some security conferences teaching how to find vulns and author exploits. They are unfortunately quite expensive.
Great work Brian! Even if this guy is innocent, your pursuit of public exposure just further tightens his handcuffs and sways public opinion. #Bellend
An entertaining read, although light on details in relation to his connections with Kronos.
He must have authored this after his 2013 public departure from his known malware identities, understanding the $ he could command, and investing in better opsec to anonymously peddle his valuable warez.
But then came Alphabay, and how it seems he was uncovered according to the feds lacked even basic opsec, that i’m more inclined to now believe its just a typicad fed concocted ‘parallel construction’ to rush through a judges approved indictment.
Thanks for publishing this fascinating story, Brian. I lecture seniors in my community about internet safety, dodgy sites and scams in general. This group of citizens unfortunately tends to be trusting and unable to understand the complexities of computer usage, internet access, etc. Your work goes a long way toward exposing the activities of those who do not care that the innocent senior community can be compromised so easily.
I think people have the right to a second chance. Many of us didn’t get a chance to “do it right” from the beginning, and spent a great deal of effort to “get it right” after growing up. Also remember that a big focus of the criminal justice system is “rehabilitation” – so if rehabilitation has already happened, it’s likely a bad idea to put someone into the CJ system, as it’s well-known to break lots of people who enter it.
Another possibility is that the government will threaten to crush him unless he gives them something in return. Hmmm, now what could a ‘former’ black hat turned white have that the government might want?
I admire the investigative work, but the subject was not all that interesting. This was the story of a bright kid that made mistakes and got in over his head. Until the light side can compete with the dark side to compensate young hackers with money and fame, the dark side will continue to have the powerful draw that it has.
And stories like this may be counter-productive as they provide an outline of what to avoid if you want to give in to the dark side.
Nice piece of work!
You identify BV1 variously as both “Brendan Johnston” and “Brandon Johnston”
Yes, interesting piece. Thanks for all your work, Brian!
I also agree that it would be interesting to tie Marcus’ discovery of the WannaCry kill switch to his “real” reasons to doing so. Was it altruism like it was originally portrayed in the media? Or was it “competitive jealousy”? Or was it his personal involvement in its development when he later tried to kill it because he got scared of how big it became? (Note that I’m merely speculating here.)
The killswitch domain wasn’t THAT hard to find. Running strings or opening the binary in the hex editor, it would be one of the first things you would see.
I think a lot of people are speculating along those lines.
“Let me be clear: I have no information to support the claim that Hutchins authored or sold the Kronos banking trojan.”
Considering legal troubles Marcus is in, I think Kerbs erred by posting this unrelated accounts. US Gov’t would be all happy to throw anything and everything to get a conviction and save face, it is likely Kerbs work will be used as ammunition.
You don’t think they could find that info with the resources they have?
Think the spam filter ate my comment, but this is basically what I said yesterday.
Krebs doesn’t even have a PI license (that we know of), let alone law enforcement credentials. If he can find this using public information, can you imagine what someone who can readily issue subpoenas and warrants obtain?
keep going, you’ll find more recent stuff, and the stuff closely related to the case. Funny thing was, if he didn’t become famous, he’d still be continuing…
I think Marcus will end up doing serious time – just like other skiddies that wade too deep into murky waters.
Opsec basics: It’s no good being paranoid AFTER the fact.
Known Marcus/Iarkey since he was 15. He and I got into a lot of spat with each other, but in the end we were always friends…he’s done a lot of things that would be criminal in the eyes of the law, but I don’t think he was involved with any banking trojan. I know this because when we were having a lot of arguments and hating each other for a while (just how friends do), I had my Liberty Reserve account hacked with $8,000 in it by someone who I worked with who wanted money from me which I had not yet paid. The guy who hacked me was not doing it to steal all my money but more for the sake of hacking me. When he hacked me, the first thing he did was message Marcus (iarkey) and offer to send him half the money because he didn’t even want it all, he was more doing it to get back at me. Marcus refused it all. Even though at that specific moment in time he hated me and disliked me he didn’t want me to lose any of my money. I ended up locking the liberty reserve account minutes after and that money was gone forever because I never unlocked it, but anyway…
https://i.imgur.com/OvlUi5A.jpg
Here’s him a long time ago with a group of us when the hackt/k0de IRC group would all chill on tinychat.
Those were the days.
He’s really changed and I hope they will can cut him some slack for his past.
America overlooked Werner von Braun’s dark role in Germany before 1945 when it head-hunted him for its rocket development. You cannot overlook the valuable and indispensable insights that black hats reveal about their craft. It’s a dirty business.
lulz https://twitter.com/MalwareJake/status/893195471405154305
What a rabbit hole!
And Brian’s detailed exploration manages to expose the rabbit’s black hat, to boot!
More great work.
The first legal defense fund for Hoffman was tainted by donations from fraudulent payment cards.
https://www.buzzfeed.com/kevincollier/beset-by-fraud-wannacry-heros-legal-fund-refunds-all
There is a second legal defense fund:
https://www.crowdjustice.com/case/malwaretech/
It would be cool to find who and how they scammed the cards.