The U.S. Justice Department today announced a series of actions against more than 100 people accused of purchasing and using “Blackshades,” a password-stealing Trojan horse program designed to infect computers throughout the world to spy on victims through their web cameras, steal files and account information, and log victims’ key strokes. While any effort that discourages the use of point-and-click tools for ill-gotten gains is a welcome development, the most remarkable aspect of this crackdown is that those who were targeted in this operation lacked any clue that it was forthcoming.
To be sure, Blackshades is an effective and easy-to-use tool for remotely compromising and spying on your targets. Early on in its development, researchers at CitzenLab discovered that Blackshades was being used to spy on activists seeking to overthrow the regime in Syria.
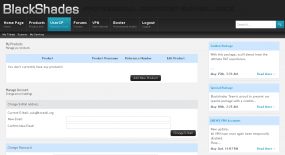
The product was sold via well-traveled and fairly open hacker forums, and even included an active user forum where customers could get help configuring and wielding the powerful surveillance tool. Although in recent years a license to Blackshades sold for several hundred Euros, early versions of the product were sold via PayPal for just USD $40.
In short, Blackshades was a tool created and marketed principally for buyers who wouldn’t know how to hack their way out of a paper bag. From the Justice Department’s press release today:
“After purchasing a copy of the RAT, a user had to install the RAT on a victim’s computer – i.e., “infect” a victim’s computer. The infection of a victim’s computer could be accomplished in several ways, including by tricking victims into clicking on malicious links or by hiring others to install the RAT on victims’ computers.
The RAT contained tools known as ‘spreaders’ that helped users of the RAT maximize the number of infections. The spreader tools generally worked by using computers that had already been infected to help spread the RAT further to other computers. For instance, in order to lure additional victims to click on malicious links that would install the RAT on their computers, the RAT allowed cybercriminals to send those malicious links to others via the initial victim’s social media service, making it appear as if the message had come from the initial victim.”
News that the FBI and other national law enforcement organizations had begun rounding up Blackshades customers started surfacing online last week, when multiple denizens of the noob-friendly hacker forum Hackforums[dot]net began posting firsthand experiences of receiving a visit from local authorities related to their prior alleged Blackshades use. See the image gallery at the end of this post for a glimpse into the angst that accompanied that development.
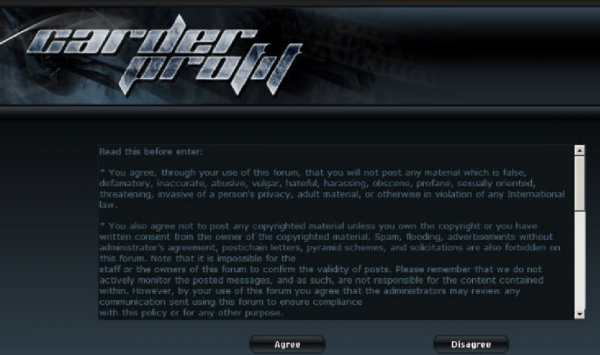
While there is a certain amount of schadenfreude in today’s action, the truth is that any longtime Blackshades customer who didn’t know this day would be coming should turn in his hacker card immediately. In June 2012, the Justice Department announced a series of indictments against at least two dozen individuals who had taken the bait and signed up to be active members of “Carderprofit,” a fraud forum that was created and maintained by the Federal Bureau of Investigation.
Among those arrested in the CarderProfit sting was Michael Hogue, the alleged co-creator of Blackshades. That so many of the customers of this product are teenagers who wouldn’t know a command line prompt from a hole in the ground is evident by the large number of users who vented their outrage over their arrests and/or visits by the local authorities on Hackforums, which by the way was the genesis of the CarderProfit sting from Day One.
In June 2010, Hackforums administrator Jesse Labrocca — a.k.a. “Omniscient” — posted a message to all users of the forum, notifying them that the forum would no longer tolerate the posting of messages about ways to buy and use the ZeuS Trojan, a far more sophisticated remote-access Trojan that is heavily used by cybercriminals worldwide and has been implicated in the theft of hundreds of millions of dollars from small- to mid-sized businesses worldwide.
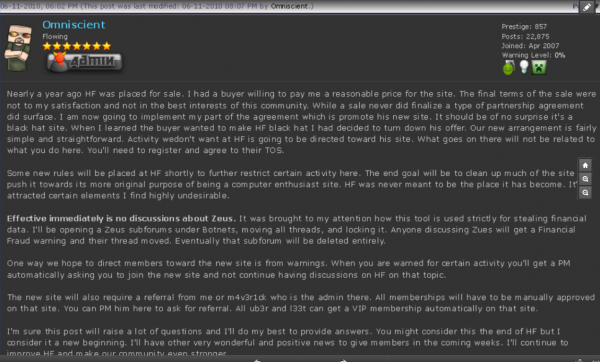
Hackforums admin Jesse “Omniscient” LaBrocca urging users to register at a new forum — Carderprofit.cc — a sting Web site set up by the FBI.
That warning, shown in the screen shot above, alerted Hackforums users that henceforth any discussion about using or buying ZeuS was verboten on the site, and that those who wished to carry on conversations about this topic should avail themselves of a brand new forum that was being set up to accommodate them. And, of course, that forum was carderprofit[dot]eu.
Interestingly, a large number of the individuals rounded up as part of the FBI’s CardProfit sting included several key leaders of LulzSec (including the 16-year-old individual responsible for sending a heavily armed police response to my home in March 2013).
In a press conference today, the FBI said its investigation has shown that Blackshades was purchased by at least several thousand users in more than 100 countries and used to infect more than half a million computers worldwide. The government alleges that one co-creator of Blackshades generated sales of more than $350,000 between September 2010 and April 2014. Information about that individual and others charged in this case can be found at this link.
For a glimpse at what the recipients of all this attention went through these past few days, check out the images below.









Sounds cool, right?
” infect computers throughout the world to spy on victims through their web cameras, steal files and account information, and log victims’ key strokes.”
Does it need an access to the computers? Like micro keylogger?
Might I suggest some caution?
I seem to remember something by Martin Niemoller…
“Then they came for me–and there was no one left to speak for me. ”
I am seeing a lot of schadenfreude here. Yes we have laws. Yes they need to be enforced sensibly. Yes we take delight in seeing script kiddies hauled off to jail. However I am not seeing a lot of discernment here between someone who buys a tool and someone who buys a tool and uses it with malicious intent. Without that discernment none of us will like the results.
@paul courry, that’s why they take their computers, to prove malicious intent.
Sir, you may assume I am older than you and have more than a passing familiarity with police procedure.
Having seen up close the results of FBI raids, the lives put on hold for months, the destruction of businesses; I am not in favor of granting police officers, the FBI or any federal agency unfettered discretion in these matters.
BTW, you cannot seize a computer to “prove” malicious intent. Here is a link to a court case you may find interesting. http://www.in.gov/judiciary/opinions/pdf/04291401mgr.pdf (it gets interesting at page 15). You need “probable cause” before you can seize the computer.
May I request those more learned than I to comment on “that’s why they take their computers, to prove malicious intent” and why on its’ face it is insufficient to support a warrant?
IANAL and have no idea what the legal precedents are on probable cause in the various jurisdictions involved, but from a common sense perspective it seems to me that probable cause exists in this case.
If someone buys a tool from a black-hat web site, and the tool’s primary purpose, the only features that distinguish it from the many free tools available, is to commit crimes – well, it isn’t hard to guess that they probably weren’t really planning to use it “only on their internal network”.
It would be interesting to see the statistics, though; what proportion of these warrants resulted in enough evidence to prosecute. Perhaps there are more wannabe security researchers than we might think.
The question here is, exactly how many people actually bought this tool would use it without malicious intent.
There are legal expectations of privacy. Unless I’ve signed a contract with you and are being warned on a regular basis that my actions will be monitored in the incredibly invasive ways this “tool” provides, even people who think they’re using it legitimately could be using it with malicious intent, at least from a legal perspective.
An employer installing this software on his workstations and using it to monitor employees could easily end up on very shaky legal ground. Not every locale has Texas-level expectations of employers being able to do anything and everything they want without constraint.
Like it or not, your computers are seized, not as a penalty, but as a means of allowing the government to build a legal case against you based on your activities. If the charges are found to be baseless you will get your equipment back. If they find evidence, then the equipment is kept to be used against you at trial. Chain of evidence rules require it to work this way.
Another thing is about a year ago BlackShades coder had built in a backdoor so the coder had access to everyone who bought it victims’ too. A lot of people noticed that their victims were getting a pop up saying they needed to buy a Microsoft license.
When it was reverse engineered it was seen to be coming from the coder. After he was caught on he just renamed the function and carried on with the credit card fraud of victims that thought the message was genuinely from Microsoft.
Anyone who bought it after that deserves everything they get for their general stupidity.
There might be a few people who had legitimate reasons to use it without malicious intent, but think about it. We’re talking about a tool that was advertised in HackForums and other places like it. They did what all tools of this sort do, put a white hat cover on their sight of saying it can be used for legit purposes, but proceeding to advertise it in a blackhat manner.
Seymour,
Employees at a workplace have no reasonable expectation of privacy when using an employer’s equipment. Employee phone calls can be monitored and recorded by the employer, and an employee’s use of an employer’s computer systems can also legitimately be tracked. Many IT departments at workplaces do exactly that. Courts of law have generally held that employees have no reasonable expectation of privacy AT WORK while on the job. However, where employers may very well cross the line is if they try to monitor their employees off-site while off work — this then crosses the line into monitoring employees’ private lives, which is not permissible because people do have an expectation of privacy at home.
A few things. Employers rights to monitor varies by locale, you’ll find this in about any security book you buy that talks about ethics.
As far as the authorities seizing computers, they should. Even if the tool was purchased and used for authorized activity, the authorities have a duty to investigate the claim. So yes, I want them to sieze the computer, and your other equipment so they can see if you are stealing/hacking. And purchasing/using the tool is probable cause.
There are people who bought it just to check out how it works and what it can do or to reverse engineer it etc. You can’t have police just going around seizing peoples computers on a whim. They need to know it was being used illegally. What’s the difference between a hacker intruding on your privacy or the police?
If I discovered someone had hacked my computer I’d be absolutely furious and want whoever was responsible to be caught and prosecuted. But also if the police just came and seized my computer because I bought a tool to experiment on my own equipment with, I’d be equally as cross. Actually probably more so as I’d probably not get them back for weeks or months.