Not long ago, phishing attacks were fairly easy for the average Internet user to spot: Full of grammatical and spelling errors, and linking to phony bank or email logins at unencrypted (http:// vs. https://) Web pages. Increasingly, however, phishers are upping their game, polishing their copy and hosting scam pages over https:// connections — complete with the green lock icon in the browser address bar to make the fake sites appear more legitimate.
According to stats released this week by anti-phishing firm PhishLabs, nearly 25 percent of all phishing sites in the third quarter of this year were hosted on HTTPS domains — almost double the percentage seen in the previous quarter.
“A year ago, less than three percent of phish were hosted on websites using SSL certificates,” wrote Crane Hassold, the company’s threat intelligence manager. “Two years ago, this figure was less than one percent.”
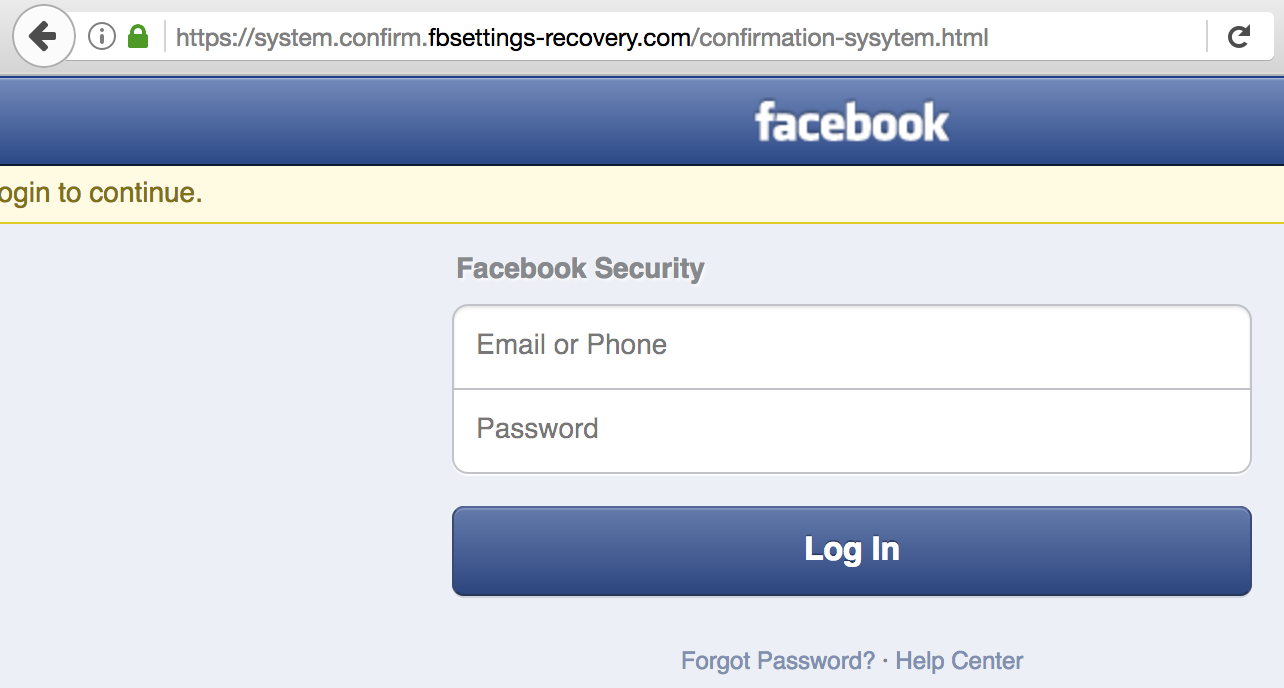
A currently live Facebook phishing page that uses https.
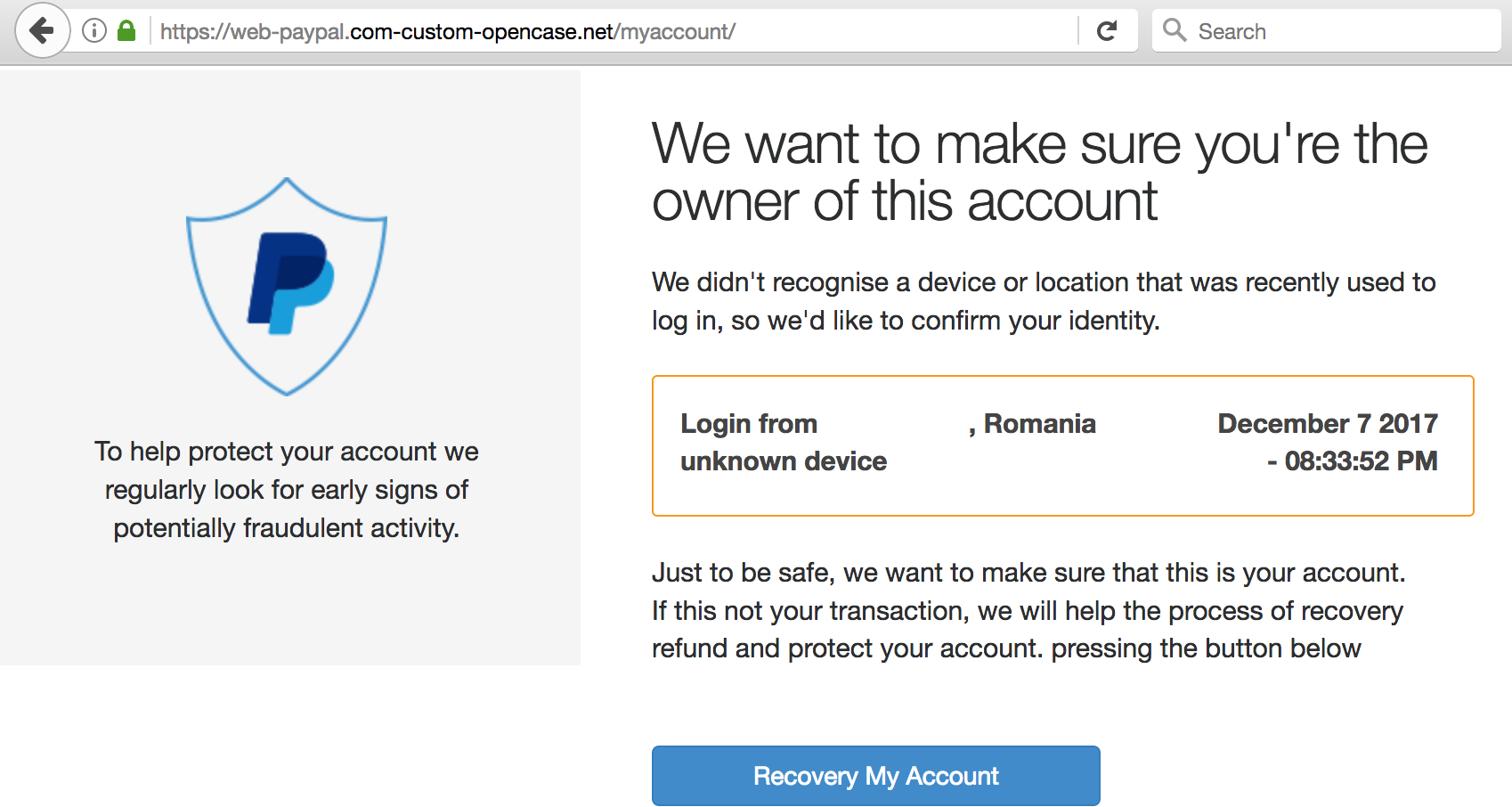
As shown in the examples above (which KrebsOnSecurity found in just a few minutes of searching via phish site reporting service Phishtank.com), the most successful phishing sites tend to include not only their own SSL certificates but also a portion of the phished domain in the fake address.
Why are phishers more aggressively adopting HTTPS Web sites? Traditionally, many phishing pages are hosted on hacked, legitimate Web sites, in which case the attackers can leverage both the site’s good reputation and its SSL certificate.
Yet this, too, is changing, says PhishLabs’ Hassold.
“An analysis of Q3 HTTPS phishing attacks against PayPal and Apple, the two primary targets of these attacks, indicates that nearly three-quarters of HTTPS phishing sites targeting them were hosted on maliciously-registered domains rather than compromised websites, which is substantially higher than the overall global rate,” he wrote. “Based on data from 2016, slightly less than half of all phishing sites were hosted on domains registered by a threat actor.”
Hassold posits that more phishers are moving to HTTPS because it helps increase the likelihood that users will trust that the site is legitimate. After all, your average Internet user has been taught for years to simply “look for the lock icon” in the browser address bar as assurance that a site is safe.
Perhaps this once was useful advice, but if so its reliability has waned over the years. In November, PhishLabs conducted a poll to see how many people actually knew the meaning of the green padlock that is associated with HTTPS websites.
“More than 80% of the respondents believed the green lock indicated that a website was either legitimate and/or safe, neither of which is true,” he wrote.
What the green lock icon indicates is that the communication between your browser and the Web site in question is encrypted; it does little to ensure that you really are communicating with the site you believe you are visiting.
At a higher level, another reason phishers are more broadly adopting HTTPS is because more sites in general are using encryption: According to Let’s Encrypt, 65% of web pages loaded by Firefox in November used HTTPS, compared to 45% at the end of 2016.
Also, phishers no longer need to cough up a nominal fee each time they wish to obtain a new SSL certificate. Indeed, Let’s Encrypt now gives them away for free.
The major Web browser makers all work diligently to index and block known phishing sites, but you can’t count on the browser to save you:
So what can you do to make sure you’re not the next phishing victim?
Don’t take the bait: Most phishing attacks try to convince you that you need to act quickly to avoid some kind of loss, cost or pain, usually by clicking a link and “verifying” your account information, user name, password, etc. at a fake site. Emails that emphasize urgency should be always considered extremely suspect, and under no circumstances should you do anything suggested in the email.
Phishers count on spooking people into acting rashly because they know their scam sites have a finite lifetime; they may be shuttered at any moment. The best approach is to bookmark the sites that store your sensitive information; that way, if you receive an urgent communication that you’re unsure about, you can visit the site in question manually and log in that way. In general, it’s a bad idea to click on links in email.
Links Lie: You’re a sucker if you take links at face value. For example, this might look like a link to Bank of America, but I assure you it is not. To get an idea of where a link goes, hover over it with your mouse and then look in the bottom left corner of the browser window.
Yet, even this information often tells only part of the story, and some links can be trickier to decipher. For instance, many banks like to send links that include ridiculously long URLs which stretch far beyond the browser’s ability to show the entire thing when you hover over the link.
The most important part of a link is the “root” domain. To find that, look for the first slash (/) after the “http://” part, and then work backwards through the link until you reach the second dot; the part immediately to the right is the real domain to which that link will take you.
“From” Fields can be forged: Just because the message says in the “From:” field that it was sent by your bank doesn’t mean that it’s true. This information can be and frequently is forged.
If you want to discover who (or what) sent a message, you’ll need to examine the email’s “headers,” important data included in all email. The headers contain a lot of information that can be overwhelming for the untrained eye, so they are often hidden by your email client or service provider, each of which may have different methods for letting users view or enable headers.
Describing succinctly how to read email headers with an eye toward thwarting spammers would require a separate tutorial, so I will link to a decent one already written at About.com. Just know that taking the time to learn how to read headers is a useful skill that is well worth the effort.
Keep in mind that phishing can take many forms: Why steal one set of login credentials for a single brand when you can steal them all? Increasingly, attackers are opting for approaches that allow them to install a password-snarfing Trojan that steals all of the sensitive data on victim PCs.
So be careful about clicking links, and don’t open attachments in emails you weren’t expecting, even if they appear to come from someone you know. Send a note back to the sender to verify the contents and that they really meant to send it. This step can be a pain, but I’m a stickler for it; I’ve been known to lecture people who send me press releases and other items as unrequested attachments.
If you didn’t go looking for it, don’t install it: Password stealing malware doesn’t only come via email; quite often, it is distributed as a Facebook video that claims you need a special “codec” to view the embedded content. There are tons of variations of this scam. The point to remember is: If it wasn’t your idea to install something from the get-go, don’t do it.
Lay traps: When you’ve mastered the basics above, consider setting traps for phishers, scammers and unscrupulous marketers. Some email providers — most notably Gmail — make this especially easy.
When you sign up at a site that requires an email address, think of a word or phrase that represents that site for you, and then add that with a “+” sign just to the left of the “@” sign in your email address. For example, if I were signing up at example.com, I might give my email address as krebsonsecurity+example@gmail.com. Then, I simply go back to Gmail and create a folder called “Example,” along with a new filter that sends any email addressed to that variation of my address to the Example folder.
That way, if anyone other than the company I gave this custom address to starts spamming or phishing it, that may be a clue that example.com shared my address with others (or that it got hacked!). I should note two caveats here. First, although this functionality is part of the email standard, not all email providers will recognize address variations like these. Also, many commercial Web sites freak out if they see anything other than numerals or letters, and may not permit the inclusion of a “+” sign in the email address field.




I would be cautious about recommending ‘Send a note back to the sender to verify the contents and that they really meant to send it.’
In many cases I’ve worked on recently, the threat actor will indeed respond back stating that it is legitimate.
Best to use the telephone, as even using an instant messenger linked to the email address could also be controlled by the threat actor.
I can confirm Chris H.’s caution, this is how it happened in my situation:
1. I received an email from an established colleague, whose place of business is in the same metropolitan area.
2. The email was a phish mimicking a docusign “click on the link” request. We had not established any prior communication regarding my needing to docusign anything.
3. I emailed him back, asking for more detail on the nature of the document that was supposedly needing a signature. “He” emailed back immediately, stating that the link was for transmitting a business report.
4. I replied via email requesting that he describe in detail the content and nature of the report, and requesting that he send it as a pdf attachment.
5. After two days of not receiving a response from “him”, I called and left him a voicemail, then called and talked with his director of IT (smaller organization).
It turns out the email response I had received was somebody on the phisher’s side, who had gained the ability to send/receive emails from my colleague’s address.
My advice would be to ask for confirmation of the email request using a phone number from a source that did not originate from the suspicious email – like from the “contact us” page on their verified legitimate website (that you navigated to independently of the email), or the phone number printed on the back of your credit card, etc.
Not bad advice to use the phone or ask for a phone number, but that, too, can be part of a scheme.
Usually when you get a reply from a scammer it is in regards to a phishing scam involving the targeted compromise of a high-dollar target — such as a realtor, real estate closing firm, or executive at a company — where the goal is to trick the recipient into wiring huge sums of money to the fraudsters.
I’ve written extensively about these schemes and their many miserable victims. Getting verbal and redundant confirmation in these cases is extremely important.
https://krebsonsecurity.com/?s=ceo+fraud&x=0&y=0
https://krebsonsecurity.com/?s=real+estate+wire&x=0&y=0
I find it best to use Out-of-Band Authentication/Verification – like picking up the phone and calling. I know it’s been said – use contact information that you have outside of the suspicious message (even applies to phone scams). The crooks are getting more devious and we all need to stay on our toes.
Stay sharp!
Good advice Jon.
We had a similar email at work a few months ago. It was an email from a customer asking us to click a link to download some technical drawings. As a suspicious bugger, I email back ask the customer to confirm. An hour later i received an email saying that they had meant to send it, but i could use this other link if i wanted. I called the customer after this and they confirmed that they did not send out the first message and it was just spam. ( I had to tell them they might have a bigger problems than someone sending spam emails in their name. After a close look at the emails I noticed the phone number was slightly different from the correct one also.
I must say a lot of this suspicion is down to Brian. Well done.
Dear Brian, regarding links and examining the link destination in the browser expansion, this also is not a certainty. A webpage link can be redefined by javascript and jump somewhere completely different, when it is clicked.
The phishing scheme I see most often is targeted at dropbox. I’m puzzled by this. Are people storing highly fungible content there? Can hackers convert my powerpoint presentations into hard $$?
I wish I could.
People store documents and more on Dropbox that are necessary for persistence. Off-site backups and all that. These can be important financial documents, notes containing usernames/passwords/account numbers/etc. These things would be a treasure trove for someone looking to leverage them to gain unwarranted access to financial or other accounts.
they store booby-trapped office files on dropbox usually.. not really going after your drop box or your powerpoints on X,Y,Z.
Thank was good read, hopefully, we will continue to get more security while reducing cost allowing small business to have secure has large entitlements
Thanks Brian for sharing your insights on this important topic, especially on the last one – where you can register on websites with the “+” symbol.
I was aware about the padlock for https enabled websites and was assumption that the phishers will not go for an https based website as the certificate would cost them. But now i understand that you could get it for free as well. Need to be bit more cautious then i guess cause as you mentioned we can’t say that the site is secure/legitimate anymore.
Apart from these, I guess currently on the enterprise level you can see a lot of spear phishing attacks happening – targeting a particular section of people.
1. It’s pretty much impossible to predict where you’ll end up with links:
* The url could be https://t.co/I109pfEmCH — it’s secure, but you have no idea where it’s going to go.
* Sure, most url shorteners have magic that will let you get a preview — e.g. https://preview.tinyurl.com
* For a while, hovering was unreliable because of onmouseover, e.g. [a href=”…” onmouseover=”window.status=’https://krebsonsecurity.com’;”]click me[/a] — that might not be relevant today, but!
* [a href=”https://krebsonsecurity.com” onclick=”window.location=’https://example.com'”]click me[/a] this won’t go where you expect
At the end of the day, the only way to know where you’re going to go is to go there. You can try to open a link in an incognito window, that will give you some protection.
2. When you get an email from someone, you shouldn’t trust anything in the email, including the return address. Either:
* compose a new email based on your contacts
* reach out by phone to confirm (don’t rely on the content of the email)
* go to the main web site for the entity that reached out and browse through contacts
Lots of short URL openers out there, just pick one and use it. It will open the short URL and give you the full one + preview.
Polishing their copy…? Sure! “…Recovery My Account…” “…confirmation-sysytem…
Of course, grammatical errors don’t always tell there’s something wrong with the email. My son gets frequently prize money paid from international tournaments he attends through Western Union. There is a grammatical error (or a typo if you prefer that word) in their emails:
“…Association (Prize Money) has initiated a EFT payment to xxx yyyyy, on 2017-03-15 14:24:58Z (UTC)…”
Should be “…an EFT payment…”
As long as we continue to ignore the fact that the internet, right down to TCP/IP and HTTP, were never meant to be used in the way we use them this will always be a problem. We’re using band-aids to treat internal bleeding.
I’m glad you mentioned this, because you hit on the key truth.
The Internet was never intended for secure or secret communications. It was meant to be a way to transmit data, openly and quickly, among researchers.
Won’t YOU feel silly once .DOT comes a top-level domain and someone registers backwardsfromtheretothesecond.dot !
I’m interested in how Let’s Encrypt got inserted as a trusted root – thereby becoming a peer of certification authorities that have traditionally issued banking site certificates. I don’t recall hearing any public discussion of the merits.
There was much indignation when a subsidiary of Symantec issued a couple dozen bogus certificates, which was justified. However, the same folks said nothing about Let’s Encrypt issuing 15,000 obviously fraudulent certificates for PayPal, a problem that continues and expands to this day. (web search for “15,000 Paypal”)
Jethro, each Trust Store gets to make its own decisions about which CAs to trust, although all the major ones insist upon the Baseline Requirements which you can read at https://cabforum.org/baseline-requirements-documents/
Most Trust Stores make their decisions behind closed doors. Mozilla (for Firefox, and indirectly for all the Free Unixes and various other things) makes theirs in public in the group m.d.s.policy. Each new CA is discussed with opportunities for public feedback, a review of their policies, and often a back-and-forth with a representative from the CA.
ISRG (the charity of which Let’s Encrypt is the main function) went through this process for Mozilla back in 2016, and has also been trusted by Apple (for macOS/ iOS / Safari etcetera), Google (for Android) and Oracle (for Java). Microsoft is notoriously slow to make decisions about this stuff, taking months to react to urgent security incidents, but presumably they too will eventually sign off on this.
However, the reason Let’s Encrypt certificates work today is that the Let’s Encrypt has an unrestricted subCA issued by IdenTrust, and your systems all trust IdenTrust. This is how new entrants to the business normally get on board, the trust process takes years and obviously can’t go back in time and make obsolete and no longer supported systems (e.g. Windows XP) trust your CA.
Before clicking on any link (unless you are COMPLETELY certain it is safe), I’d recommend copy/pasting it into one of the free, online sandboxes that will give you a preview and details of the path to the site.
urlquery[dot]net and urlscan[dot]io are both fantastic resources.
As for the Bank of America link in the “Links Lie” section, using Chrome, I hovered over it, right clicked and then used the Inspect function. That URL was the “Mother Of All URLs”.
“don’t open attachments in emails you weren’t expecting”
That’s actually the most dangerous phishing : attachments from emails you are expecting but are not legitimate. Something like : “Your amazon purchase ..”, given that many people purchase things every week, you would always expect such an email.
So never open attachment from emails unless you really need to and scrutinize them carefully.
Hi Brian,
I think this should be viewed more as an opportunity for Sec people than a threat! The good thing is that in order to get that certificate that site must apply to it which means some kind of an early warning system is being created, which is extremely good for us. Using tools like CertStream (https://certstream.calidog.io/) with the correct automation (Like phishing catcher – https://github.com/x0rz/phishing_catcher) gives a really good heads up on new phishing sites which uses these certificates.
Gmail seems to offer quite a few protections against phishing and malicious attachments.
New built-in Gmail protections to combat malware in attachments
5/31/2017
“Today we announced new security features for Gmail customers, including early phishing detection using machine learning, click-time warnings for malicious links, and unintended external reply warnings. In addition, we have also updated our defenses against malicious attachments.”
https://gsuiteupdates.googleblog.com/2017/05/new-built-in-gmail-protections-to.html