A story published here last week warned readers about a vast network of potentially malicious Web sites ending in “.cm” that mimic some of the world’s most popular Internet destinations (e.g. espn[dot]cm, aol[dot]cm and itunes[dot].cm) in a bid to bombard visitors with fake security alerts that can lock up one’s computer. If that piece lacked one key detail it was insight into just how many people were mistyping .com and ending up at one of these so-called “typosquatting” domains.
On March 30, an eagle-eyed reader noted that four years of access logs for the entire network of more than 1,000 dot-cm typosquatting domains were available for download directly from the typosquatting network’s own hosting provider. The logs — which include detailed records of how many people visited the sites over the past three years and from where — were deleted shortly after that comment was posted here, but not before KrebsOnSecurity managed to grab a copy of the entire archive for analysis.
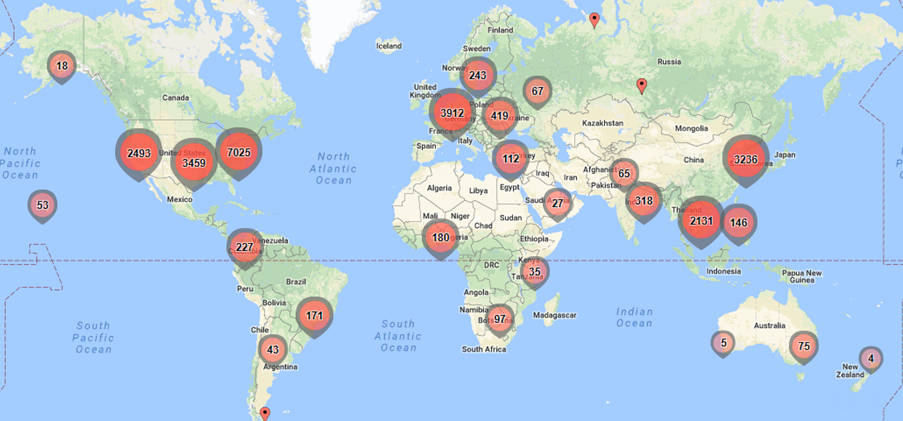
The geographic distribution of 25,000 randomly selected Internet addresses (IP addresses) in the logs seen accessing the dot-cm typosquatting domains in February 2018. Batchgeo, the service used to produce this graphic, limits free lookups to 25,000, but the above image is likely still representative of the overall geographic distribution. Perhaps unsurprisingly, the largest share of traffic is coming from the United States.
Matthew Chambers, a security expert with whom this author worked on the original dot-cm typosquatting story published last week, analyzed the access logs from just the past three months and found the sites were visited approximately 12 million times during the first quarter of 2018.
Chambers said he combed through the logs and weeded out hits from Internet addresses that appeared to be bots or search engine scrapers. Here’s Chambers’ analysis of the 2018 access log data:
January 2018; 3,732,488 visitors
February 2018: 3,799,109 visitors
Mar 2018: 4,275,998 visitors
Total Jan-Mar 2018 is 11.8 million
Those figures suggest that the total number of visits to these typosquatting sites in the first quarter of 2018 was approximately 12 million, or almost 50 million hits per year. Certainly, not everyone visiting these sites will have the experience that Chambers’ users reported (being bombarded with misleading malware alerts and redirected to scammy and spammy Web sites), but it seems clear this network could make its operators a pretty penny regardless of the content that ends up getting served through it.
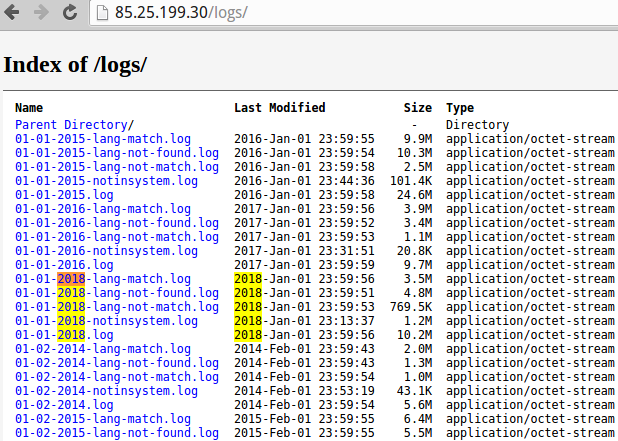
Until very recently, the site access logs for this network of more than 1,000 dot-cm typosquatting sites were available on the same server hosting the network.
Chambers also performed “reverse DNS” lookups on the IP addresses listed in the various dot-cm access logs for the month of February 2018. It’s worth noting here that many of the dot-cm (.cm) typosquatting domains in this network (PDF) are trying to divert traffic away from extremely popular porn sites (e.g. pornhub[dot]cm).
“I’ve been diving thru the data thus far, and came up with some interesting visitors,” Chambers said. “I pulled those when it was easy to observe that a particular agency owned a large range of IPs.”
Chambers queried the logs from 2018 for any hits coming from .gov or .mil sites. Here’s what he found:
-National Aeronautics and Space Administration (JSC, GSFC, JPL, NDC): Accessed one of the .cm typosquatting sites 104 times in February, including 16 porn sites.
–Department of Justice (80 times) [7 porn sites]
–United States House of Representatives (47 times) [17 porn sites]
–Central Intelligence Agency (6 times)
–United State Army (29 times)
–United States Navy (25 times)
–Environmental Protection Agency (15 times)
–New York State Court System (4 times)
Other federal agencies with typosquatting victims visiting these domains include:
Defense Information Systems Agency (DISA)
Sandia National Laboratories
National Oceanic and Atmospheric Administration (NOAA)
United States Department of Agriculture
Berkeley Lab
Pacific Northwest Lab
Last week’s story noted this entire network appears to be rented out by a Colorado-based online marketing firm called Media Breakaway. That company is headed by Scott Richter, a convicted felon and once self-avowed “spam king” who’s been successfully sued for spamming by Microsoft, MySpace and the New York attorney general. Neither Richter nor anyone else at Media Breakaway has responded to requests for comment.
If you’re in the habit of directly navigating to Web sites (i.e. typing the name of the site into a Web browser address bar), consider weaning yourself of this risky practice. As these ubiquitous typosquatting sites show, it’s a good idea to avoid directly navigating to Web sites you frequent. Instead, bookmark the sites you visit most, particularly those that store your personal and financial information, or that require a login for access.
Update, April 5, 8:05 a.m. ET: An earlier version of this story included numbers that didn’t quite add up to almost 12 million hits. That’s because Chambers sent me multiple sets of numbers as he refined his research, and I inadvertently used figures from an early email he shared with KrebsOnSecurity. The monthly figures above have been adjusted to reflect that.




Great write up !
Does anybody know, is there a way to block all .cm domains, maybe using the hosts file? I checked my bookmarks and I don’t go to any .cm websites. I have accidentally typed .cm in the past.
You could probably block them using a Pi-hole (https://pi-hole.net/) or if you have a PFSense router, PFBlockerNG. I haven’t tried this yet but I’m sure there’s a way to get it working. The Pi-hole can be installed on any *nix distro as far as I know. I have it installed and set up on a Raspberry Pi 2-B running Raspbian, and it works great. Since you set it up as a DNS server, you can use it on any device. I’ve had it set up for about a year now and I haven’t had any problems with malware domains, ad domains (apart from youtube video ads, because those are hosted on the same site as normal youtube videos) and scareware domains like Microsoft tech support scams. I hope this helps! Wow now that I read this back this really sounds like a sales pitch! xD
You can on pihole, in the settings there’s an option called “wildcard” that can block the top level domain. I use it to block .tk .bit .top and other malicious domains.
If you use a chromium browser you can block javascript for [*.]cm and [*.]ru or any other TLD’s. Another option is to disable javascript but then “Allow” [*.]com – [*.]net – [*.]org and other TLD’s will have js disabled and then you can allow specific websites that use those different TLD’s.
With FF based browsers I use an addon called No-Script Suite Lite as a javascript whitelist. Not to be confused with the more popular NoScript Security Suite. By default all websites have js disabled and have to be added to the whitelist, takes a couple seconds. New sites always have js disabled. I also use the addon in chromium browsers.
When the bad guys started sending malicious links in email, the fix was “type the address manually in your browser”. Now the bad guys are typo-squatting, making it dangerous to manually type addresses, so the fix is “use bookmarks”. How long until someone comes up with a malware strain that edits favorites/bookmarks and changes “.com” to “.cm”?
Actually book mark hijacking(for lack of a better word) was pretty common about five years ago – but since then, the browsers seem to be resistant to that. I say this because I used to run my honeypot lab quite a bit to do research on this. Believe it or not, the Internet Explorer 11 browser got so good at preventing all kinds of attacks, that I had to turn off most of the security features built in, just to test my other in depth defenses. I can’t vouch for Chrome or Mozilla, but since I use the same security features on each of those now – I’m pretty sure things have become more difficult for the criminals. I probably have three utilities that all block known bad pages now, and I like to use Web Of Trust to preview any sites I might find in search results. It also has a page blocker built in.
Quite frankly, I still don’t completely trust my favorites, and occasionally do a web search instead, and replace them regularly. Even when I look on the web to answer emails, I still like doing a web search instead of clicking on email links. The best thing about search engines, is that you don’t even have to complete the URL name, or spell it anywhere near correct, to get the right results, and it is actually almost faster than looking for a bookmark to go where I want in the first place.
“As these ubiquitous typosquatting sites show, t’s a good idea to avoid directly navigating to Web sites you frequent. Instead, bookmark the sites you visit most”
This will not happen if these are sites like porn sites etc.
Thanks for the clear article
For now for major sites, browser autocomplete usually prevents you from needing to type the “.com”, or even much more than the first several letters of the URL if you’ve visited the site a lot before, so in practice typing it in is less of a problem than one might think. Although I guess actually relying on this could be fragile in its own way.
What’s a bigger threat – someone getting access to my device and seeing the range of financial bookmarks I have (even without U/P being saved), or me typing “chase bank” into google, and using the first returned link?
I would think that there’s more scrutiny (and quick response if ever a breach) on the Google side. Thoughts?
Search for Zeus Panda and SEO
Occasionally the first results got poisoned depending on what search engine you like to use. I haven’t heard of that for a while now – so maybe they are getting better at policing up the links they display now. I do still get surprised when the first or second result has a red WOT rating on it, and then I know it is the wrong URL right off the bat.
We use a managed dnsfilter service (google that) it’s 5 bucks a month and we load our blacklist with every cctld and gtld. It acts basically like a WAN_OUT filter. Can also select categories like adult/vpn/gambling/etc like many other utm products. We review the most abused tld’s at surbl and spamhaus occasionally to make sure we are blocking the most abused. I don’t understand why companies/gov allow porn into their network am I wrong to block those categories outright? Is there some “civil right” to view porn on your employer’s computer that I am missing?
It’s the same reason libraries cannot filter porn. Also, the fact sites like Pornhub now are hosting content Youtube has banned is making it more than porn and even more and a 1A argument.
I’m probably missing something in this news story, but if ICANN has oversight on the TLDs why are they permitting a TLD like ‘cm’ which clearly has no purpose other than for criminal means?
>but if ICANN has oversight on the TLDs why are they
>permitting a TLD like ‘cm’
Take it up with ISO, since cm is the international standard abbreviation for Cameroon, and that’s the list ICANN uses.
.cm is the country TLD for Cameroon.
Simply type in the site name without the .com then use Ctrl + Enter. For example: espn then hit Ctrl+enter.
+1
You beat me to that tip.
Looks like we’re the only ones familiar with that complicated maneuver. Shift + Enter for .net also.
I typed “espm” Ctrl+enter and managed to mess up your hint. (you do NOT want to follow that link).
I lesson is that no matter the shortcut, you can still do a typo and end up where you don’t want to be.
? I went to espm.com in a sandbox and it’s a parked domain. Was it something else when you went there?
My dns filter blocked espm.com and displayed that it was a porn site.
You were told why that is wrong in the last article on the same topic. Why do you repeat yourself, suggesting that people do something so dangerous and unpredictable? It’s not a universal standard.
Control & Enter, as in typing AOL in the URL bar followed by pressing Control & Enter simultaneously, will produce the dot com extension and direct you straight there.
Great article as usual. Are these porn sites cybersquatting or are traffic being sent away from them?
National Aeronautics and Space Administration (JSC, GSFC, JPL, NDC): Accessed one of the .cm typosquatting sites 104 times in February, including 16 porn sites.
–Department of Justice (80 times) [7 porn sites]
–United States House of Representatives (47 times) [17 porn sites]
Do you have a list ?
This seems like a problem with a relatively straightforward solution. Typosquatting should be prohibited and managed out. Why isn’t this built in via a correlation/reference to legit brand names, vs. relying on the (individual) brand name owners to protect their brands and take actions to do so? Address the problem at its root, vs. distributing it out and hoping each individual owner takes action. We can do better than this.
Because there might legitimately be a ford.cm or a yahoo.cm — who’s to say? And since it’s Cameroon, Ford and Yahoo aren’t really equipped to force any action…
Because that would defeat 90% of the purpose of all these recent and novelty TLDs, specifically, the whack-a-mole revenue stream they generate for the industry.
Of course, bookmarking a site is best. But it is often best to type in the url rather than click on a link, especially from an email, since phishing emails often disguise the links to look legit but actually take a person to a different site. I wonder if there is an add-in for firefox and chrome to check a url before going there.
Download a host file, and that will automatically block a lot of that trash just after you hit the enter button. A lot of utilities like AVs and Anti-malware solutions have page or ip address blockers built in as well. Some people like the old venerable Spybot Search and Destroy, as it uses the browsers own blocking configurations to prevent some of this irritation from affecting your browser sessions. However if you use CCleaner, be prepared to uncheck the box next to ‘Site preferences’ for the Mozilla browser, as that is what some of those simple utilities use for passive malware protection.
Googling isn’t always safe either. I’ve seen browser extensions and other malware redirect search results to fake security sites, “you’ve won a gift card”, and other malicious sites. Clicking on a search result first goes to a tracking link – which can be hijacked.
12M is just a tiny fraction compared to how many people mistype websites using one-letter-over on the keyboard, or dropping other characters – 3 I’ve personally seen include youtuve[dot]com, wellafargodealerservices[dot]com, and oogle[dot]com.
Perhaps a browser “preview website” feature would help: “The website you are about to visit looks like this, and was registered to XYZ company just xx days ago. It has been reported by xx number of people as being fraudulent. “
Usually, I manually go to google.com. (maybe type goo-return).
Then I type the site name (maybe krebs), Then I select the appropriate search result.
This seems to weed out most of the flaky typos.
I never click-on-links from email messages, especially while at work.
Wow google.cm is identical to google.com.
If it wasn’t for the security issues raised here most of you would still be clueless about the .cm TLD typo squatting situation that has been in place for, I don’t know, 10 years or more? Same goes for the less popular .om, .ne, .et, etc.
But great points raised here. As I mentioned in the previous post on this topic, domainers have been referring to ICANN as “I Can’t” for a very, very long time. And I blame ICANN directly for the infestation of all the crap TLDs now on the market.
One good thing is that when you see those new TLDs like .xyz you instantly know they are some spam site or clueless new web owner. One of my clients recently got an offer to buy a domain that was [SuperExpensiveKeyword].Attorney. I don’t know what they price was, but I have advised against it if it’s over $100.
I’ve heard that you should not only bookmark the valid site, but that you should actually have two bookmarks: one with just an IP address, and the backup with the domain name. Most likely, the correct IP address will reach the correct destination, but the domain name can be more easily redirected. I have not yet personally implemented this double-bookmarking method.
This reminded me of a trick that MCI used: People did not know how to spell operator. ATT suggested in their advertisements that they dial 1-800-operator. If they dialed operater, they got MCI. ATT should have anticipated it.
I learned that I did not know how to spell hurricane. When I typed hurricane, I got a porn site that would not quite. Likewise people don’t know which domain extension to use: .com or .org comes to mind.
Best to box the domain name with anticipated errors that forward to the actual site.
Martha: Some typos in there, too. Quite –> quit, and “hurricane” spelled correctly both times — how should you not spell it? 🙂
I spelled it Hurricaine. I haven’t tried it again.
Is there a quick code for .net similar to the Control+enter for the .com extension?
The link to the list of “.cm” addresses downloads a pdf file that McAfee detects as a Trojan (“Artemis” + a one-off code).
I submitted the url for that pdf file to VirusTotal and the report shows that the file is detected by Fortinet as “Malware”, so McAfee must use Fortinet when deciding whether something is unsafe.
VirusTotal report here –
https://www.virustotal.com/#/url/f10243c0388e0444c081d75c2ec85dc96487a3ad459046343839d722bc2bf5bb/detection
Hayton, this is what we call a FP or False Positive. The day Krebs hosts malware, I will surely go buy an expensive bottle of wine and ask to shake his hand.
There once was a time when McAfee detected a critical file in Windows as being infected with a virus and quarantined it. After it was quarantined Windows wouldn’t boot. My sister’s employer sent out a company-wide email to their 10,000+ employees telling them not to reboot after a couple thousand peoples systems were turned into ungainly paperweights. This was just one incident – I could relate many, many more, but I suspect Intel would send their legal department after me for airing their dirty laundry.
Hayton, come on, I know you’re smarter than that. The file is nothing more than a list of links that are most decidedly malicious or at least very suspicious. the fact that some AV product detects it as bad is hardly surprising. But I assure you the file itself is not malware.
McAfee. I like to call it McAwful.
False Positives are a possibility in any piece of AV software, but tend to be rampant in McAfee.
And I find it tends to interfere with legitimate installs and other normative operations at a FAR higher rate.
Better than nothing of course, but there’s better things you could be using.
I think (the larger) companies are trying to take the appropriate steps to protect users from “.cn” addresses. Or at the very least, control their brand over the web. Barclay’s being a practical example:
https://www.home.barclays/
This might not be a perfect solution, but it’s a start. There’s a growing list of corporations like Barclay’s too… time will tell if they continue to use the “.com” extension
Whats the issue really. The small amount of visits compared to billions of site visits hourly, or the possible harm because people are not carefull what to type or click and being able to live with that?
Carefull…haha, looks like you may have to live with it too Friday!
Exactly. And I don’t need the Krebs police complaining about others responsibility. I am responsible who to trust. Why do we trust domains by default is the question. We are willing to take the risk by the billions. Brian rather wants us to believe we should be scared and blame others. That’s his business model.
Krebs police? Too funny.
This post was merely a reminder to be more conscientious when typing URLs and to avoid direct navigation where possible. Also, I find it fascinating when shady marketing companies keep getting away with perpetrating massive scams like this and some of the biggest brands and companies in the world are apparently powerless to do anything about it.
The figures from Q1 don’t add up to 12M. More like 8.7M. Where are you getting the 12M figure from?
Thanks, John. Yep, I accidentally used an earlier set of numbers Chambers shared with me. I’ve fixed the data in the story; the overall Q1 number is correct.
Okay good, so it wasn’t just me going insane!
As always, an excellent article. As a fragile human, I’m becoming overly paranoid after reading too many security articles and comments: Don’t type URLs, don’t click links from others, don’t trust favorites/bookmarks against drive-by tampering.
Do I need an encrypted container to store and safeguard URLs ? (eg: password manager — the next target if people start to store significant amounts of cryptocurrency)
How about a Rolodex of QR code URLs?
Then you’re only vulnerable to an attack on BGP routing … Sorry, the paranoia is getting to me, and I’m being 20% nutty on purpose. Probably well-adjusted normal people have such lax security because they can only handle so much paranoia-cost.
“Do I need an encrypted container to store and safeguard URLs ? (eg: password manager — the next target if people start to store significant amounts of cryptocurrency) ”
A good (encrypted) password wallet leaves room for access URLs. Can’t see a reason to not use it.
What about .CO ?
check you http://krebsonsecurity.co
Way more domains are registered in .CO zone
I use no bookmarks, nor favorites. For my often used Internet Adresses, I use shortcuts. I have some 600 of them neatly arranged in a tree of folders with a shortcut from my desktop. Browser independant, simple to use, easy to maintain, I hardly imagine a hacker building a program rumaging through my folders and changing these shortcuts (even then, I sync my disk twice a day or something BUT, before allowing the real movements, I check that the modified files are the ones I expect) … Icing on the cake, to transfer my “favorites” from one computer to an other, or backup them, I just need to copy the tree…
More important than most of the opining here is the question asked by Rex earlier: how can I prevent “.cm” links from being followed? Home PC, Windows 10. Hosts file?
Info like that would really add value to the article.
I don’t think the Windows hosts file supports wildcards (e.g. 127.0.0.1 *.cm). You could achieve this however by using a third-party DNS service like OpenDNS. Alternatively, many Internet Security versions of antivirus products allow you to do this as well. Google is your friend either of these two cases.
+1 for OpenDNS. Has been protecting me and my family for years. And now with the newer versions of Advanced Tomato custom firmware, OpenDNS gets updated with my IP address automatically from my router, as well as my Dynamic DNS service.
Hi.
I am not sure what value there is in your publishing of what .gov/.mil sites presumably went accidentally to a .cm location. Is this just salacious muckraking along the lines of “all government/military are lazy and shiftless and surf porn all day long…”? That trope is kind of played out.
As long as there are domains in areas like .co or .cm, there will be legitimate traffic to it. Using your example, if I wanted to go to say “ford.com” and typed “ford.cm” by mistake and it went to a porn site, would that be me being a bad person, or a mistake? You don’t bother to differentiate in your tattling above.
Thanks,
It was just one of many ways to analyze the data. It’s relevant because visiting porn sites on the taxpayer dime is almost certainly a) a risky behavior and b) something that should probably get the employee reprimanded, if not worse. And to address your hypothetical, the examples cited weren’t people trying to go to ford.com and getting redirected to a porn site. They were trying to go to a porn site and got redirected somewhere else.
My analysis did not suggest government employees surf porn all day long; that was yours. However, this has been a persistent problem for many agencies for many years. See: https://www.nbcwashington.com/investigations/Dozens-of-Federal-Employees-Watched-Abundance-of-Porn-on-the-Job-in-Recent-Years-414743293.html
I’m going to guess you’re an employee with one of the govt orgs mentioned in the story. NOAA maybe?
so how much traffic is on .co , missing the “m” ? there are about 1 million .co registered compared to like 25ooo .CM. Why did you not register your own domain under .co or .cm , if there is so much traffic to be lost ?
Surely this falls under the remit of the Lanham Act? Many of these domains are trademarked in the US, and if Richter is a US citizen then it’s a simple matter for someone to go sueballs on them.
IANAL, but it sure seems like if Microsoft can convince a judge that it should be able to seize botnet domains, then this should be a no-brainer.
https://krebsonsecurity.com/2011/03/homegrown-rustock-botnet-fed-by-u-s-firms/