A 19-year-old man from the United Kingdom who headed a cybercriminal group whose motto was “Feds Can’t Touch Us” pleaded guilty this week to making bomb threats against thousands of schools.
On Aug. 31, officers with the U.K.’s National Crime Agency (NCA) arrested Hertfordshire resident George Duke-Cohan, who admitted making bomb threats to thousands of schools and a United Airlines flight traveling from the U.K. to San Francisco last month.
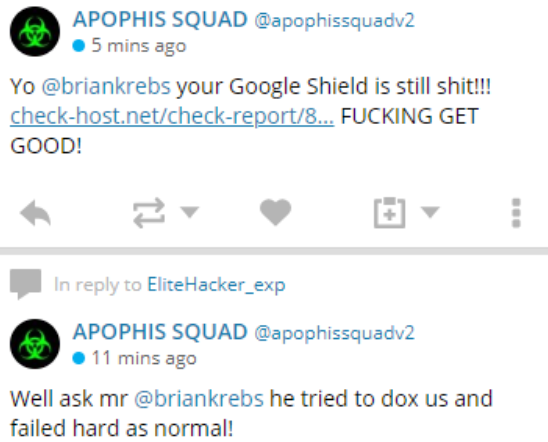
One of many tweets from the attention-starved Apophis Squad, which launched multiple DDoS attacks against KrebsOnsecurity and Protonmail over the past few months.
Duke-Cohan — a.k.a. “7R1D3N7,” “DoubleParallax” and “Optcz1” — was among the most vocal members of a group of Internet hooligans that goes by the name “Apophis Squad,” which for the better part of 2018 has been launching distributed denial-of-service (DDoS) attacks against multiple Web sites, including KrebsOnSecurity and Protonmail.com.
Incredibly, all self-described members of Duke-Cohan’s clique were active users of Protonmail, even as they repeatedly attacked its servers and taunted the company on social media.
“What we found, combined with intelligence provided by renowned cyber security journalist Brian Krebs, allowed us to conclusively identify Duke-Cohan as a member of Apophis Squad in the first week of August, and we promptly informed law enforcement,” Protonmail wrote in a blog post published today. “British police did not move to immediately arrest Duke-Cohan however, and we believe there were good reasons for that. Unfortunately, this meant that through much of August, ProtonMail remained under attack, but due to the efforts of Radware, ProtonMail users saw no impact.”
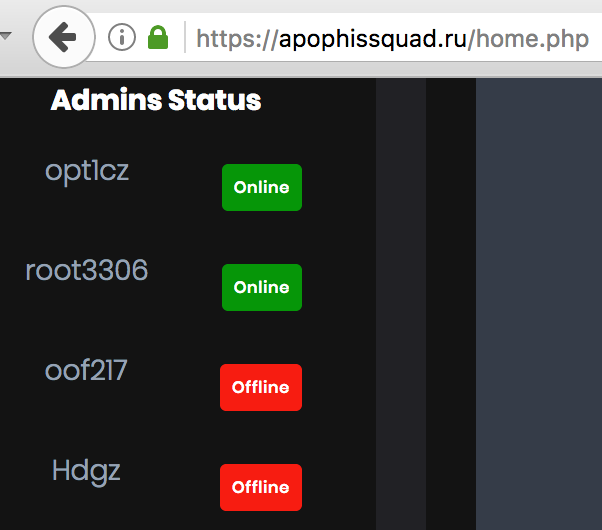
The DDoS-for-hire service run by Apophis Squad listed their members.
On Aug. 9, 2018, the attention-seeking Apophis Squad claimed on their Twitter account that flight UAL 949 had been grounded due to their actions.
“In a recording of one of the phone calls which was made while the plane was in the air, he takes on the persona of a worried father and claims his daughter contacted him from the flight to say it had been hijacked by gunmen, one of whom had a bomb,” the NCA said of Duke-Cohan’s actions in a press release on Sept. 4. “On arrival in San Francisco the plane was the subject of a significant security operation in a quarantined area of the airport. All 295 passengers had to remain on board causing disruption to onward journeys and financial loss to the airline.”
The Apophis Squad modeled itself after the actions of the Lizard Squad, another group of e-fame seeking online hoodlums who also ran a DDoS-for-hire service, called in bomb threats to airlines, DDoSed this Web site repeatedly and whose members were nearly all subsequently arrested and charged with various cybercrimes. Indeed, the Apophis Squad’s Web site and DDoS-for-hire service is hosted on the same Internet server used by a handful of other domains that were tied to the Lizard Squad.
Unsophisticated but otherwise time-wasting and annoying groups like Apophis Squad are a dime a dozen. But as I like to say, each time my site gets attacked by one of them two things usually happen not long after: Those responsible get arrested, and I get at least one decent story out of it. And if Protonmail is right, there are additional charges on the way.
“We believe further charges are pending, along with possible extradition to the US,” the company said. “In recent weeks, we have further identified a number of other individuals engaged in attacks against ProtonMail, and we are working with the appropriate authorities to bring them to justice.”




Good for you, Brian. Your work is appreciated.
It certainly is, thank you!
How does it feel being the lightning rod of the internet?
Great analogy! But I feel there could be a bit more.
Brian Krebs = Internet Lightning Rod
Google Project Shield = Grounding Strap attached to the Internet Lightning Rod
Keep up the great work Brian!
And some great credit to the excellent Google Project Shield team for helping you to keep doing what you do.
Like!
I also greatly appreciate your work and literally stop my work just to read yours every time I see a new post in my inbox. Thanks for all you do!
Bomb threats, now that always works to seek the wrong type of attention for yourself. LOL
I don’t know what’s up with these child hackers these days. Brian literally wrote the book on this stuff, he seems like the last person you’d want to taunt.
One thought I had when I saw the taunting Twitter(?) posts at the top of the story: It is nice when the shoe is on the other foot. That is, when the good guys only have to get lucky once but the bad guys have to get lucky every time or else they get taken down.
Good story, but a question about the last paragraph:
Extradiction of a UK citizen from the UK to the US?
A quick google on these keywords only shows people that won appeals in court not to be extradicted. Committing internet crime from the uk is a fellony as well and he probably will get convicted for that, UK prisons are not known for their “hospitality”, so spending a few months or years in there sounds like a good enough punishment
I hope they mean once the UK government is done with him, they’ll extradite to do the time for the US crimes.
I highly doubt the U.S would work to extradite someone already being prosecuted in U.K. Among other things, it messes with international relationships.
What’s the point, after all?
It does happen. Roger Alan Giese [1] was extradited to the US. The query [2] that ended up baring fruit in case you want to find others (I went through a couple of variations).
[1] https://ktla.com/2018/09/07/bail-dropped-from-60m-to-3m-for-o-c-fugitive-accused-of-sexually-assaulting-choir-boy/
[2] https://www.google.ca/search?q=%22united+kingdom%22+us+%22extradited+to%22+-assange+-canada
Brian, is the “Apophis” reference in their squad name directed toward the ‘Stargate’ baddie (or his real-world Egyptian-god persona) for any particular reason within their particular screed or raison d’être?
No idea.
Apophis was the Egyptian god of chaos.
Young talent wasted, we can only lament and keep watching with shields up.
I’m not sure I’d call DDoSing or prank phone calls “talent”.
I wouldn’t say any of these attacks are skilled.
I would say that If someone finds a particular way to conduct an attack that is DIFFERENT then they are skilled or say they find a way to do it on a large scale etc.
“British police did not move to immediately arrest Duke-Cohan however, and we believe there were good reasons for that.”
What good reasons could those be?
Collecting more evidence?
I don’t know specifically but it is a tactic that can be used in cyber cases.
There’s more to this story than DDoS-ing websites, and that aspect of it has not been mentioned in the UK reports of his arrest and court appearance.
George Duke-Cohan appeared in Luton Magistrates Court on September 3rd and pleaded guilty to three counts of issuing hoax bomb threats. One of those charges related to the United Airlines flight to San Francisco. He will be sentenced on the 21st at Luton Crown Court, so he can expect a prison sentence of more than 12 months – the maximum he would have received if sentencing had been passed at the Magistrates Court.
Two of those three charges against him were for bomb hoaxes sent to a large number of schools in the UK, and one charge also covers hoaxes sent to schools in the US. Unless further charges are brought against him on the 21st before he is sentenced, the issue of attacking websites is being ignored. Now that, perhaps, leaves open the possibility of the FBI making a request for extradition either before he starts a prison sentence in the UK, or on his release.
What is incredible about this saga is that when he was arrested on August 31st for the airline bomb hoax it was the third time the police here had had him in custody. He has been under some sort of surveillance since the end of March, and must have known it. Since April this young fool has been banned from accessing the internet or using mobile phones – “using digital technology” – but he still carried blithely on with his disruptive behaviour, presumably while being monitored by the police.
The first reported wave of bomb hoaxes to schools – all in the UK – were on March 19th. At the time the Sun newspaper reported having spoken to Duke-Cohan, who said that the bomb threats had sprung from a feud between Minecraft users and that he expected to be arrested soon. He was, two days later, but was soon released on bail.
Less than a week later came another wave of bomb threats to schools in the UK – and also this time in the US – and Duke-Cohan was arrested again a few days later for sending these threats. This is when he was banned from using any digital devices.
There were more waves of bomb hoaxes sent to UK schools on 13th April, 8th May and 26th June. There were similarities to Duke-Cohan’s previous hoaxes but these later episodes were not included in the charges against him so I leave that one open to speculation.
There is also here the question of “Apophis”. Supposedly this is a collective, and the UA bomb hoax was claimed in the name of Apophis. But the third of the charges against Duke-Cohan implies that he alone was responsible, and he has certainly pleaded guilty as the person solely responsible. The Apophis Twitter account also went dead at the time he was arrested. So are there more members of Apophis? If so I would expect more arrests to have followed by now; I haven’t seen reports of any more.
What I did see was a report that after the March bomb hoaxes three people were arrested. I haven’t seen anything more than that – no names, no follow-up. There were also reports at the time that suggested someone in the US was involved in sending the hoaxes, but again there’s been nothing more said.
We’re left with a few questions. Why didn’t the police move more quickly against Duke-Cohan in August? Perhaps they were waiting to get evidence against other people. Why didn’t they charge him for sending the March bomb hoaxes after arresting him twice? That looks as if they were using him as bait to catch bigger fish, but if that’s what were hoping for it seems to have failed. And was Duke-Cohan behind the April, May and June bomb hoaxes and if he was, why wasn’t he charged with them?
A rather unsatisfying conclusion to this one. I bet his lawyer pleads autism or Asperger’s or bi-polar disorder and gets a reduced sentence. They all seem to try that one now, and it usually works – even when extradition is involved.
Some good details, here. I would say be careful when using the ‘Sun’ and ‘newspaper’ in the same phrase.
That’s the upsetting thing about this whole saga. The UK is so lenient on cybercriminals with alleged autism that they let them out over and over again, and they re-offend. And they will ignore complaints from companies like Protonmail until this kid attacks a plane and they can’t ignore it any longer.
Get your fucking act together, UK. If you want to be compassionate, fine, but this is not compassion.
And I’ll bet there will be the same contingent of activists campaigning to prevent this ass hat’s extradition to the USA too. Lauri Love 2.0, anyone?
GREAT work Brian! I love your posts!
“Duke-Cohan — a.k.a. “7R1D3N7,” “DoubleParallax” and “Optcz1””
DoubleParallax is a different person.
Why targeting Protonmail ?
I suspect since they were customers themselves, it was to throw the trail off of themselves. Who would attack their own mail source – an idiot lol
For the same reason that kids vandalize their own schools and religious buildings: familiarity with the target and a challenge to what they consider authority.
I recall the Protonmail attack. However, there was an easy workaround for those with Tor, Brave, or other browser capable of accessing onion sites. Use Protonmail’s onion site at https://protonirockerxow.onion/login. For some reason, onion sites are not susceptible to DDoS attacks. I don’t understand why Protonmail and others did not advise users to do this during the attack. After all, that was one of the reasons Protonmail created the onion site in the first place.
Because some tor end nodes are compromised and these could lead to a loss of security.
It wouldn’t matter if an end node is compromised. The session is end to end encrypted. And if you are using 2FA, it would be doubly impossible to compromise your account using the onion site. The only thing a compromised end node would see is that an intermediate node is connected to Proton Mail. They would not see your session, your IP address, or anything else of value. Moreover, if there was a chance that an onion address could be less secure, Proton Mail wouldn’t even offer it.
Ignorance and arrogance will always get you into trouble…
Interesting read. A smart young man, trying to bully others for no reason. Sounds familiar. No moral compass. Durn. But, trying to get noticed by someone for a reason. Like others, I am interested in the why did he do it? Attention, fame, or money?
Asside from it being a crime, there usually is no monetary fine to be paid to the victiums. And the victiums have lost value by service interruptions unknown to them. A sale delayed, is business lost. A ad not seen is business lost, a ad delayed, the same. I would wonder, how long till enforcement considers that in the punishment?
Like I said elsewhere, those who laugh last, laugh best. Good job!
The Times has published a picture of Mr. Duke-Cohan being arrested. It is a treasure. The picture was provided by the National Crime Agency so the letters NCA figure prominently in the foreground and Mr. Duke-Cohan in the background.
No knowledge in these guys what so ever. All they did was use public sources to obtain power that any other stresser can do. I dont understand why you would waste your time writing an article on a bunch of nonsense no brained kids. If you truly want to write a good article message @SlayKings.io
I thought TeOz rooted them all and exposed them all ages ago?
https://hastebin.com/raw/ehifepawir
Lol @ BK hyperlinking himself in his own article.
🙂 nicely done
Thank you! I lost a day of work because of these attention seeking clowns. I didn’t have any high hopes as such cases often end up with blaming russians and nothing more (turned out he was not Russian even), knowing that he’s already is arrested is actually very satisfying. Justice won. Very good work! Thank you!
Why someine with this kind of skills and knowledge will do this ?? Why people waste their time talent and skills to do some nonsense actions ?? With this skills and knowledge you could much better and legit things !!
Now the big question is why people with high skills and knowledge do all the grazy things ?
Why they commit so much evil ? Why not use their knowledhe and skills for good purpose for the world??
All this botnet makers they just waste their talent time and their lifes ! Eaither way they will be busted one way or other.
Even if they use cryptocurrency since its internet everything can traced, and law enforcement will threat the exchangers to give up information about abusers.
There is no hiding in this world everyone know what everybody doing. Your actions are so visible and there no privacy at all. Never had and never will.
To continue if you use cryptocurrency you either way have to transfer this funds to somewhere, so claimed private exchangers will not risk with the prison the law enfircement will knock they door and ask to give information.
If they dont cooperate then they will be the ones who will take punishment. Its 100% sure thrre is no way you can commit crime without leaving any trace !!
The law enforcement will catch you always even if you hide in russia or china no mattter !!
They will get you anyways i still dont undestood how people can be so stupid to do stupid things and they feel they vant be touched !!
Brian this is your job to tell criminals the same what i tell here.
Do not commit crime !!
Its illusion of wealth or money money will be taken from any criminal from the proceeds of crime !!
If you choose to lounder your money in some dirty business then your money will be taken from other criminals.
This is truth !!
two words for the good guy(s) : Great job !
two works for the bad guys: Script Kiddies !
The only issue I have with Brian’s account of this case is his categorization that Duke-Cohan is a “19-year-old man”. His actions clearly indicate his is still a child.
You must be a child as well for not knowing proper grammar.
i wonder why little teenie-boppers would try to hit such a hardened target as Krebs. Isn’t it obvious they’re guppies playing around with the leviathan that’s going to gobble them up. Crazy!!!
Amateur hour. He must have realised he would be caught surely?