Three men in the United Kingdom have pleaded guilty to operating otp[.]agency, a once popular online service that helped attackers intercept the one-time passcodes (OTPs) that many websites require as a second authentication factor in addition to passwords.
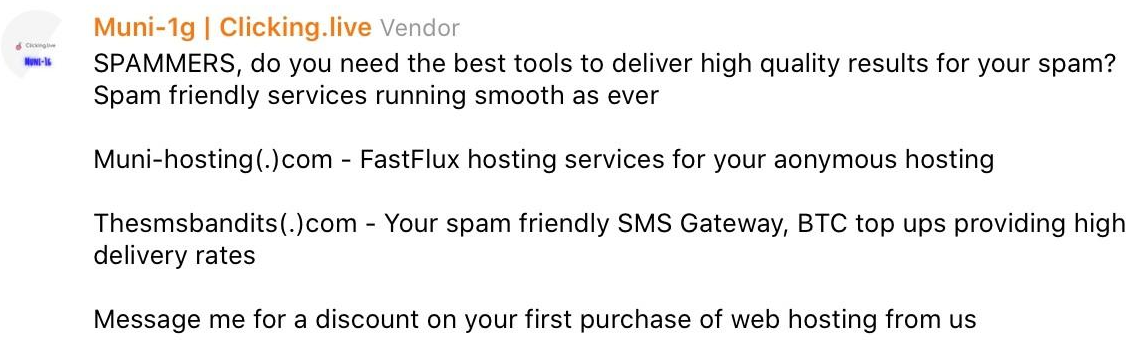
Launched in November 2019, OTP Agency was a service for intercepting one-time passwords needed to log in to various websites. Scammers would enter the target’s phone number and name, and the service would initiate an automated phone call to the target that alerts them about unauthorized activity on their account.