Authorities in the United Kingdom have arrested a 20-year-old man for allegedly operating an online service for sending high-volume phishing campaigns via mobile text messages. The service, marketed in the underground under the name “SMS Bandits,” has been responsible for blasting out huge volumes of phishing lures spoofing everything from COVID-19 pandemic relief efforts to PayPal, telecommunications providers and tax revenue agencies.
The U.K.’s National Crime Agency (NCA) declined to name the suspect, but confirmed that the Metropolitan Police Service’s cyber crime unit had detained an individual from Birmingham in connection to a business that supplied “criminal services related to phishing offenses.”
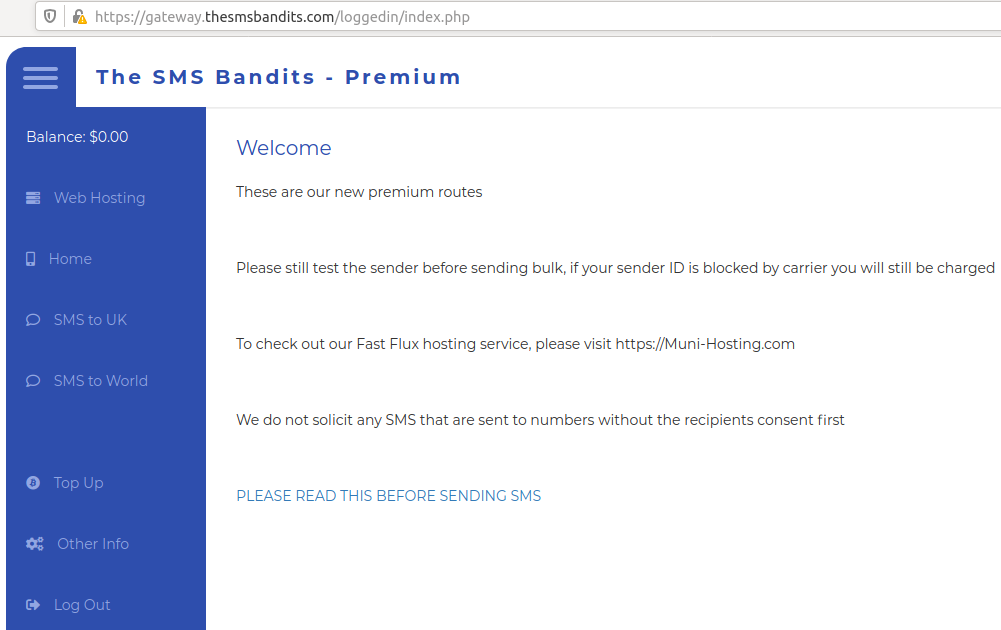
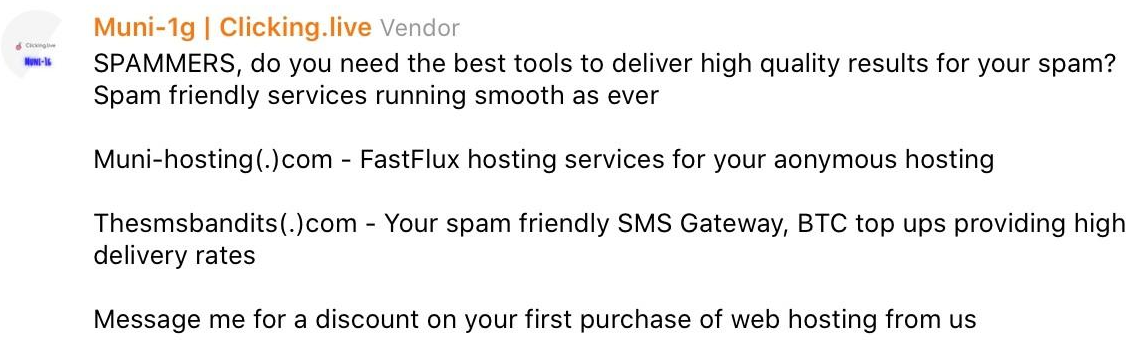
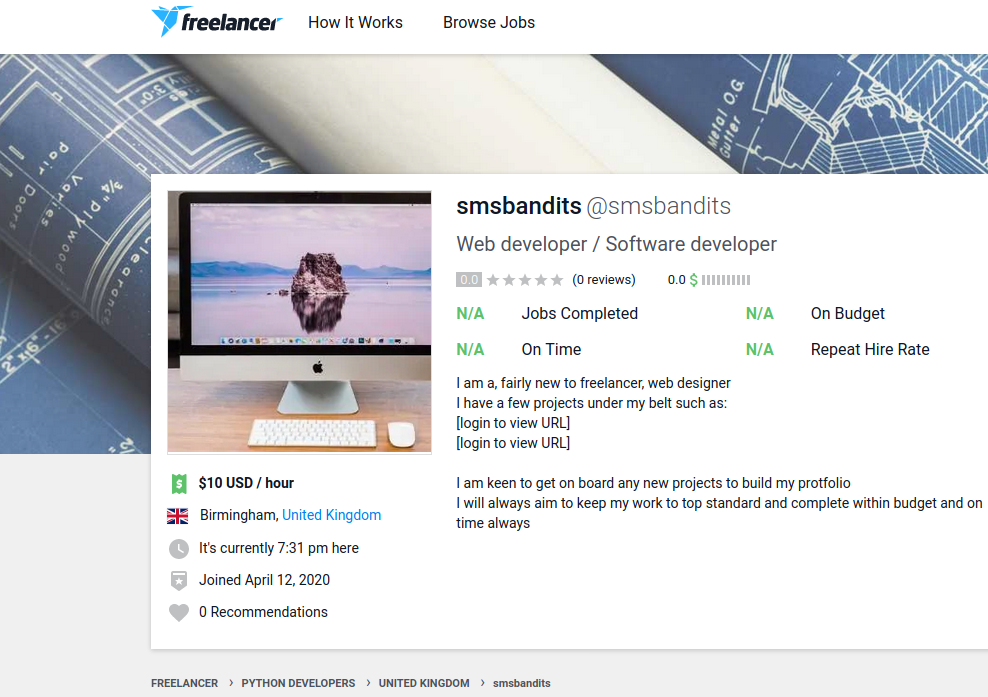
The proprietors of the phishing service were variously known on cybercrime forums under handles such as SMSBandits, “Gmuni,” “Bamit9,” and “Uncle Munis.” SMS Bandits offered an SMS phishing (a.k.a. “smishing”) service for the mass sending of text messages designed to phish account credentials for different popular websites and steal personal and financial data for resale.
Sasha Angus is a partner at Scylla Intel, a cyber intelligence startup that did a great deal of research into the SMS Bandits leading up to the arrest. Angus said the phishing lures sent by the SMS Bandits were unusually well-done and free of grammar and spelling mistakes that often make it easy to spot a phony message.
“Just by virtue of these guys being native English speakers, the quality of their phishing kits and lures were considerably better than most,” Angus said.
According to Scylla, the SMS Bandits made a number of operational security (or “opsec”) mistakes that made it relatively easy to find out who they were in real life, but the technical side SMS Bandits’ operation was rather advanced.
“They were launching fairly high-volume smishing campaigns from SMS gateways, but overall their opsec was fairly lousy,” Angus said. “But on the telecom front they were using fairly sophisticated tactics.”
For example, the SMS Bandits automated systems to check whether the phone number list provided by their customers was indeed tied to actual mobile numbers, and not landlines that might tip off telecommunications companies about mass spam campaigns.
“The telcos are monitoring for malicious SMS messages on a number of fronts,” Angus said. “One way to tip off an SMS gateway or wireless provider is to start blasting text messages to phone numbers that can’t receive them.”
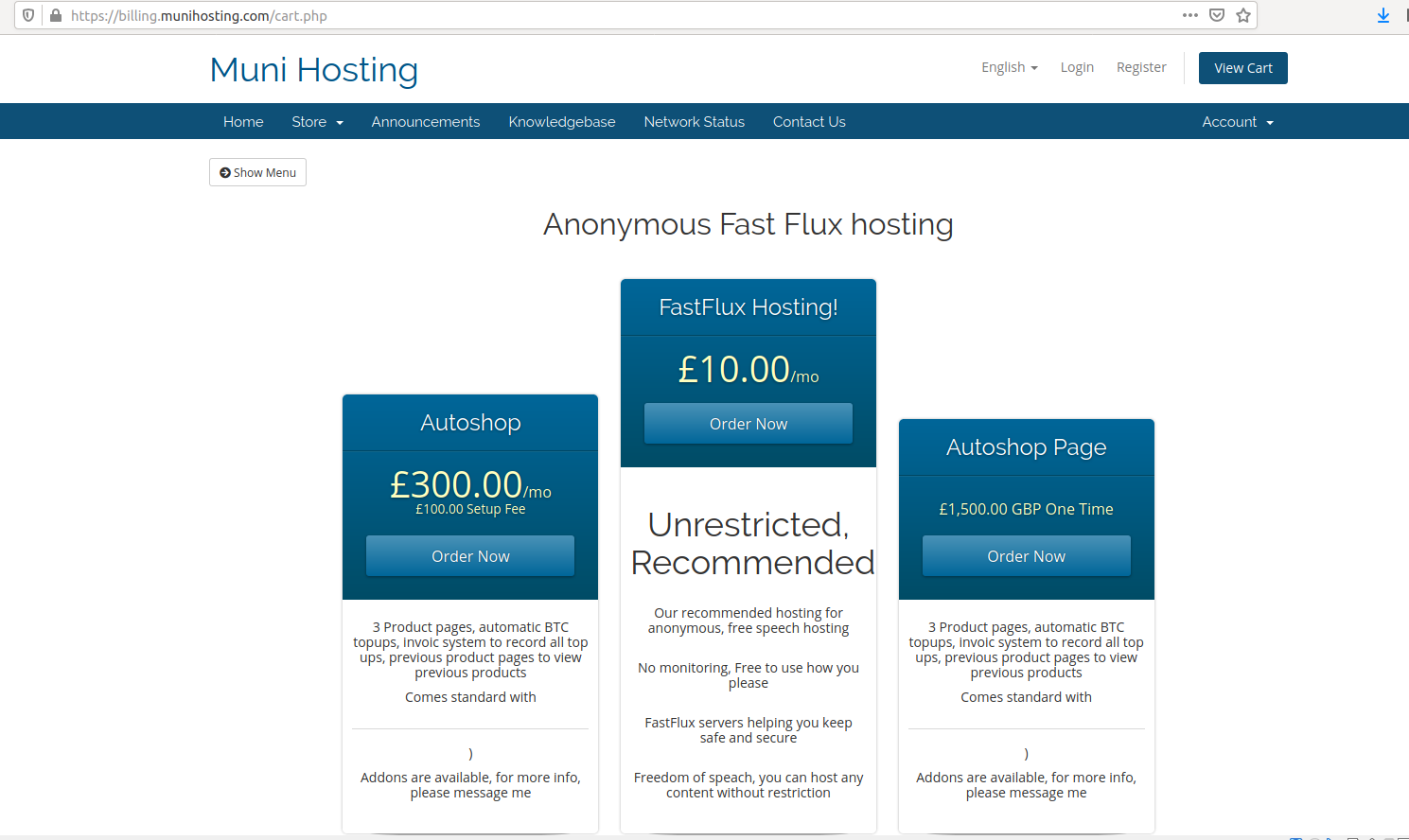
Scylla gathered reams of evidence showing the SMS Bandits used email addresses and passwords stolen through its services to validate a variety of account credentials — from PayPal to bank accounts and utilities providers. They would then offload the working credentials onto marketplaces they controlled, and to third-party vendors. One of SMS Bandits’ key offerings: An “auto-shop” web panel for selling stolen account credentials.
SMS Bandits also provided their own “bulletproof hosting” service advertised as a platform that supported “freedom of speach” [sic] where customers could “host any content without restriction.” Invariably, that content constituted sites designed to phish credentials from users of various online services.
The SMS Bandits phishing service is tied to another crime-friendly service called “OTP Agency,” a bulk SMS provider that appears catered to phishers: The service’s administrator stated on multiple forums that he worked directly with the SMS Bandits.
Otp[.]agency advertises a service designed to help intercept one-time passwords needed to log in to various websites. The customer enters the target’s phone number and name, and OTP Agency will initiate an automated phone call to the target that alerts them about unauthorized activity on their account.
The call prompts the target to enter a one-time password generated by their phone’s mobile app, and that code is then relayed back to the scammer’s user panel at the OTP Agency website.
“We call the holder with an automatic calling bot, with a very believable script, they enter the OTP on the phone, and you’ll see it in real time,” OTP Agency explained on their Telegram channel. The service, which costs anywhere from $40 to $125 per week, advertises unlimited international calling, as well as multiple call scripts and voice accents.
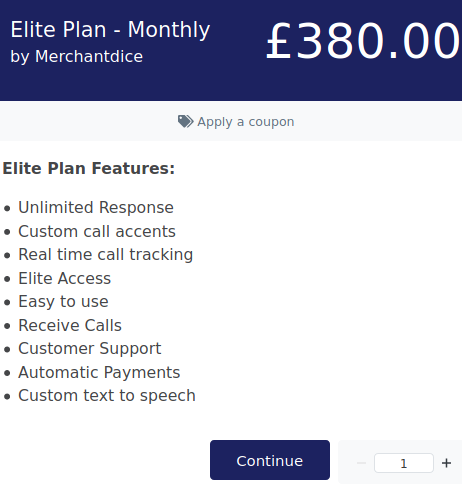
One of the pricing plans available to OTP Agency users.
The volume of SMS-based phishing skyrocketed in 2020 — by more than 328 percent — according to a recent report from Proofpoint, a security firm that processes more than 80 percent of North America’s mobile messages [Full disclosure: Proofpoint is currently an advertiser on this site].




Interesting post as not much attention is given to odd niche services like this. With the majority of the world turning to mobile use now a days i think we will see a flip to more of this type of crime in the future.
I am sure there are many more website offering services like this. Can’t stop them all.
Maybe we should start teaching people how to spot scams like these.
I am curios to see the volumne of sms based phishing in 2021…
While Pre-COVID, here are details of similar arrest linked to a group doing SMS phishing in Australia. https://www.afp.gov.au/news-media/media-releases/sms-phishing-fraudster-charged-sydney
Hi,
We believe that the information contained in this article is slanderous, and we have no affiliation with anyone of the name UncleMuni or SMSBandits.
You stated that we were advertising on multiple forums that we work with SMS Bandits.
This was simply not us, could you please provide us evidence of this evident, and we will take immediate action.
We’re a telephony business, allowing communication across the world. We provide an API, to allow businesses to reach their customers, as well as full on telemarketing sales staff to use our panel to call their clients, without the need of talking to them 1 to 1.
Due to us being in a sensitive industry, and call fraud is at its all time high, we take reports and abuse very seriously here at OTP.Agency, and do our upmost best to combat telephone fraud.
If you have any questions, please contact us at press@otp.agency
Hi. I think you meant to say the article was libelous.
Since you asked, here are a few [links neutered]…
** OTP.AGENCY **⚜️ We’re happy to announce the new revolution of fraud. With the release of OTP Agency, you will never have to worry about a one time password restriction again. ♂️ We promise you that you will make profit with OTP Agency. There is a simple guide on the site which will help you start after you’ve purchased. **What is OTP Agency? **With OTP Agency, you’re capable of grabbing one time passwords with a click of a button. **How does it work? **You’ll need the holders phone number (at least) to proceed with using OTP Agency. Once that’s done, all you need to do is send the OTP, wait 10 seconds, enter it on OTP Agency then wait 30 seconds for your OTP result.** Requirements** **to succeed: **- Account / Fullz. – At least **BASIC** plan on OTP.AGENCY **Purchase a plan now for only £30/week. **Homepage: hxxps://otp.agency Dashboard: hxxps://panel.otp.agency **Get in touch: **✅ ICQ – hxxps://icq.im/AoLFpPhoYMMjGgj-ijA ✅ Telegram – hxxps://t.me/OTP_Agency ✅ Discord Server – hxxps://discord.gg/HgFPJKD
Ataraxia | OTP.Agency
Ever wanted to retrieve OTP, well with OTP Agency bot, you can! : Once you obtain access to our otp bot you will need to have victims details. For ‘Site OTP’ you need to have victims name and phone number only. For ‘VBV OTP’ you will need to have Phone number, Name, Bank name, last 4 digits of CC.
—————————————————————————————
Ataraxia | OTP.Agency
Ever wanted to retrieve OTP, well with OTP Agency bot, you can! : Once you obtain access to our otp bot you will need to have victims details. For ‘Site OTP’ you need to have victims name and phone number only. For ‘VBV OTP’ you will need to have Phone number, Name, Bank name, last 4 digits of CC. Once you fill up the spaces provided click ‘dial’ immediately the bot will ring the victim if it’s reachable and say “ There was unauthorised attempt….” and the bot will ask the victim to enter otp to prevent this. Once the victim enters otp the bot will end the call and show otp on your screen. All depends on holder!
#OTP.Agency on Telegram
21 MAY 2020 16:42:54
Txnveer987
on Nov 25, 2019 19:13:56 UTC
What is OTPAgency?
OTP Agency is the #1 One time Password Retrieval Tool
What do we do?
We call the holder with an automatic calling bot, with a very believable script, they enter the OTP on the phone, and you’ll see it real time!
Key Features
Unlimited one time passwords
International phone calls
Automated calling bot
Real time OTP Results
Professional approach to product
24/7 live support team
Easy to use
What can you do with OTPAgency?
You can reset passwords to websites
You can validate payment for Verified by Visa
===============================================
#OTP.Agency on Telegram
03 APR 2020 07:05:18
Muni-1g | Clicking[.]live
i work with owner of otp agenct go ask him if im a scammer
Hi,
We appreciate the response, we will begin to investigate.
Could you please let us know where these alleged posts are located?
We will do everything in our power to comply, as we do not support fraudulent behaviour, and work towards a safer platform.
Regards
Hi,
We appreciate the response, could you please let us know where these claims are located, and we will begin to investigate the claims.
As to the alleged claim, I am unaware of the terms that you have listed regarding the titles ‘VBV’, ‘holder’.
This could potentially be misuse of our platform, and we will comply completely, as we do everything we can to combat fraud.
We appreciate the raised claims, if you could do this, please let me know.
Mostly on Telegram, but these same advertisements have been promoted on Raidforums[.]com, among others. VBV=Verified by Visa, an authentication system used by many ecommerce websites.
Hi,
Yes, we are aware of the false threads posted on raidforums a few months back, and we asked the owner to remove it, which is why you are unable to see them now, but can most likely see a cached version of them.
Thanks, is there a way we could resolve this as we don’t want to have our company name linked to anything of this content.
Kind regards
I’m not feeling convinced that OTPAgency’s intentions are quite pure. If the claim is libelous your organisation wouldn’t have made such a claim in the comments section of a blog post. We have seen in the past where an organisation convinces investigators to reveal their sources just so they can be disrupted or or the claim refuted – and the activity continues. You’ll have to work a lot harder to convince the community that your intentions are genuine.
You’ll do everything possible to combat fraud…… except publish any type of official business entity name, address or other identifying info on your website. The only info on your company you posted are anonymous links, telegram accounts, or email addresses.
If you arent a scam, you could easily prove you are a legit business by publicly identifying yourself as one. Choosing not to advertise even a business mailing address or PO Box on your supposedly-legitimate website is a strong sign.
Your website says “OTPAgency is a business based in the United Kingdom”…. so, prove it.
You wont.
Hi,
We appreciate your input on this.
I would just like to remind you that there are many different methods of having a business in the United Kingdom, and it doesn’t necessarily mean you need to register it. We are a website operating under a partnership agreement, and do not have a Limited business.
This doesn’t mean we are not a business. Please take a look here on how the United Kingdom deal with businesses:
https://www.gov.uk/set-up-business
This provides basic information on concepts such as websites and web services that don’t need to be incorporated.
Furthermore, we also believe in privacy, and the easy use of access. Hence why our main payment provider is Crypto currency. This is also beneficial because it protects us from chargebacks (that occurred when we accepted mainstream payments such as PayPal and card).
Kind regards.
Asked for proof of legitimacy…you are ducking and covering with a distraction about UK Corporate code.
So cool that OTP has found legal ways to hide not unlike those used by tax evading shell companies. The optics here are very bad for you since OTP’s evasive,”No” can be taken as prima facie evidence that you are a criminal enterprise.
Obfuscate, deflect, duck, jive. OTP van do it all!
oops “can”
Who named them? Harry and Marv?
From their now defunct website:
OTP.Agency has come to an end, and we will not be returning.
We have purged our database, user files and site content.
We appreciate you may not understand the situation, but we have no better options.
We thank everyone for the opportunity, and it was a great run.
OTP.Agency
Methinks someone has finally cracked Tor and they aren’t letting anyone in on their little operational secret…
After some research, I’ve found a site offering similar services (if not worse), offers a spoof call service and OTP interception, seems like a copy? https://ispoof.cc
““The telcos are monitoring for malicious SMS messages on a number of fronts”
Yes, but they’re doing nothing about it !!! This is the same as all those scammers that robocall your number and then try and scam you. Telcos *must* know about this, and I simply can’t believe it’s technically impossible to stop. Someone is obviously making too much money for the Telcos to do anything.
Obfuscate, deflect, duck, jive. OTP van do it all!