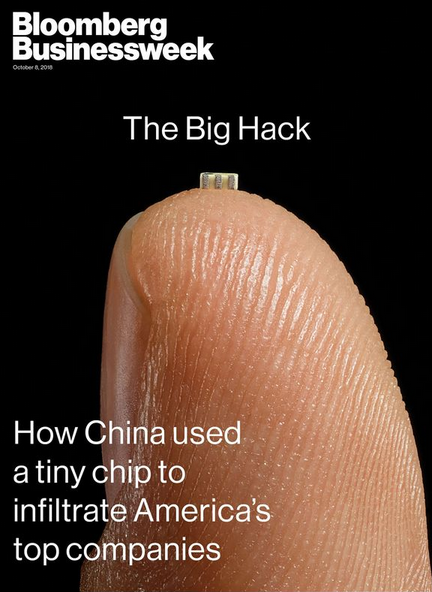
From time to time, there emerge cybersecurity stories of such potential impact that they have the effect of making all other security concerns seem minuscule and trifling by comparison. Yesterday was one of those times. Bloomberg Businessweek on Thursday published a bombshell investigation alleging that Chinese cyber spies had used a U.S.-based tech firm to secretly embed tiny computer chips into electronic devices purchased and used by almost 30 different companies. There aren’t any corroborating accounts of this scoop so far, but it is both fascinating and terrifying to look at why threats to the global technology supply chain can be so difficult to detect, verify and counter.
 In the context of computer and Internet security, supply chain security refers to the challenge of validating that a given piece of electronics — and by extension the software that powers those computing parts — does not include any extraneous or fraudulent components beyond what was specified by the company that paid for the production of said item.
In the context of computer and Internet security, supply chain security refers to the challenge of validating that a given piece of electronics — and by extension the software that powers those computing parts — does not include any extraneous or fraudulent components beyond what was specified by the company that paid for the production of said item.
In a nutshell, the Bloomberg story claims that San Jose, Calif. based tech giant Supermicro was somehow caught up in a plan to quietly insert a rice-sized computer chip on the circuit boards that get put into a variety of servers and electronic components purchased by major vendors, allegedly including Amazon and Apple. The chips were alleged to have spied on users of the devices and sent unspecified data back to the Chinese military.
It’s critical to note up top that Amazon, Apple and Supermicro have categorically denied most of the claims in the Bloomberg piece. That is, their positions refuting core components of the story would appear to leave little wiggle room for future backtracking on those statements. Amazon also penned a blog post that more emphatically stated their objections to the Bloomberg piece.
Nevertheless, Bloomberg reporters write that “the companies’ denials are countered by six current and former senior national security officials, who—in conversations that began during the Obama administration and continued under the Trump administration—detailed the discovery of the chips and the government’s investigation.”
The story continues:
Today, Supermicro sells more server motherboards than almost anyone else. It also dominates the $1 billion market for boards used in special-purpose computers, from MRI machines to weapons systems. Its motherboards can be found in made-to-order server setups at banks, hedge funds, cloud computing providers, and web-hosting services, among other places. Supermicro has assembly facilities in California, the Netherlands, and Taiwan, but its motherboards—its core product—are nearly all manufactured by contractors in China.
Many readers have asked for my take on this piece. I heard similar allegations earlier this year about Supermicro and tried mightily to verify them but could not. That in itself should be zero gauge of the story’s potential merit. After all, I am just one guy, whereas this is the type of scoop that usually takes entire portions of a newsroom to research, report and vet. By Bloomberg’s own account, the story took more than a year to report and write, and cites 17 anonymous sources as confirming the activity.
Most of what I have to share here is based on conversations with some clueful people over the years who would probably find themselves confined to a tiny, windowless room for an extended period if their names or quotes ever showed up in a story like this, so I will tread carefully around this subject.
The U.S. Government isn’t eager to admit it, but there has long been an unofficial inventory of tech components and vendors that are forbidden to buy from if you’re in charge of procuring products or services on behalf of the U.S. Government. Call it the “brown list, “black list,” “entity list” or what have you, but it’s basically an indelible index of companies that are on the permanent Shit List of Uncle Sam for having been caught pulling some kind of supply chain shenanigans.
More than a decade ago when I was a reporter with The Washington Post, I heard from an extremely well-placed source that one Chinese tech company had made it onto Uncle Sam’s entity list because they sold a custom hardware component for many Internet-enabled printers that secretly made a copy of every document or image sent to the printer and forwarded that to a server allegedly controlled by hackers aligned with the Chinese government.
That example gives a whole new meaning to the term “supply chain,” doesn’t it? If Bloomberg’s reporting is accurate, that’s more or less what we’re dealing with here in Supermicro as well.
But here’s the thing: Even if you identify which technology vendors are guilty of supply-chain hacks, it can be difficult to enforce their banishment from the procurement chain. One reason is that it is often tough to tell from the brand name of a given gizmo who actually makes all the multifarious components that go into any one electronic device sold today.
Take, for instance, the problem right now with insecure Internet of Things (IoT) devices — cheapo security cameras, Internet routers and digital video recorders — sold at places like Amazon and Walmart. Many of these IoT devices have become a major security problem because they are massively insecure by default and difficult if not also impractical to secure after they are sold and put into use.
For every company in China that produces these IoT devices, there are dozens of “white label” firms that market and/or sell the core electronic components as their own. So while security researchers might identify a set of security holes in IoT products made by one company whose products are white labeled by others, actually informing consumers about which third-party products include those vulnerabilities can be extremely challenging. In some cases, a technology vendor responsible for some part of this mess may simply go out of business or close its doors and re-emerge under different names and managers.
Mind you, there is no indication anyone is purposefully engineering so many of these IoT products to be insecure; a more likely explanation is that building in more security tends to make devices considerably more expensive and slower to market. In many cases, their insecurity stems from a combination of factors: They ship with every imaginable feature turned on by default; they bundle outdated software and firmware components; and their default settings are difficult or impossible for users to change.
We don’t often hear about intentional efforts to subvert the security of the technology supply chain simply because these incidents tend to get quickly classified by the military when they are discovered. But the U.S. Congress has held multiple hearings about supply chain security challenges, and the U.S. government has taken steps on several occasions to block Chinese tech companies from doing business with the federal government and/or U.S.-based firms.
Most recently, the Pentagon banned the sale of Chinese-made ZTE and Huawei phones on military bases, according to a Defense Department directive that cites security risks posed by the devices. The U.S. Department of Commerce also has instituted a seven-year export restriction for ZTE, resulting in a ban on U.S. component makers selling to ZTE.
Still, the issue here isn’t that we can’t trust technology products made in China. Indeed there are numerous examples of other countries — including the United States and its allies — slipping their own “backdoors” into hardware and software products.
Like it or not, the vast majority of electronics are made in China, and this is unlikely to change anytime soon. The central issue is that we don’t have any other choice right now. The reason is that by nearly all accounts it would be punishingly expensive to replicate that manufacturing process here in the United States.
Even if the U.S. government and Silicon Valley somehow mustered the funding and political will to do that, insisting that products sold to U.S. consumers or the U.S. government be made only with components made here in the U.S.A. would massively drive up the cost of all forms of technology. Consumers would almost certainly balk at buying these way more expensive devices. Years of experience has shown that consumers aren’t interested in paying a huge premium for security when a comparable product with the features they want is available much more cheaply.
Indeed, noted security expert Bruce Schneier calls supply-chain security “an insurmountably hard problem.”
“Our IT industry is inexorably international, and anyone involved in the process can subvert the security of the end product,” Schneier wrote in an opinion piece published earlier this year in The Washington Post. “No one wants to even think about a US-only anything; prices would multiply many times over. We cannot trust anyone, yet we have no choice but to trust everyone. No one is ready for the costs that solving this would entail.”
The Bloomberg piece also addresses this elephant in the room:
“The problem under discussion wasn’t just technological. It spoke to decisions made decades ago to send advanced production work to Southeast Asia. In the intervening years, low-cost Chinese manufacturing had come to underpin the business models of many of America’s largest technology companies. Early on, Apple, for instance, made many of its most sophisticated electronics domestically. Then in 1992, it closed a state-of-the-art plant for motherboard and computer assembly in Fremont, Calif., and sent much of that work overseas.
Over the decades, the security of the supply chain became an article of faith despite repeated warnings by Western officials. A belief formed that China was unlikely to jeopardize its position as workshop to the world by letting its spies meddle in its factories. That left the decision about where to build commercial systems resting largely on where capacity was greatest and cheapest. “You end up with a classic Satan’s bargain,” one former U.S. official says. “You can have less supply than you want and guarantee it’s secure, or you can have the supply you need, but there will be risk. Every organization has accepted the second proposition.”
Another huge challenge of securing the technology supply chain is that it’s quite time consuming and expensive to detect when products may have been intentionally compromised during some part of the manufacturing process. Your typical motherboard of the kind produced by a company like Supermicro can include hundreds of chips, but it only takes one hinky chip to subvert the security of the entire product.
Also, most of the U.S. government’s efforts to police the global technology supply chain seem to be focused on preventing counterfeits — not finding secretly added spying components.
Finally, it’s not clear that private industry is up to the job, either. At least not yet.
“In the three years since the briefing in McLean, no commercially viable way to detect attacks like the one on Supermicro’s motherboards has emerged—or has looked likely to emerge,” the Bloomberg story concludes. “Few companies have the resources of Apple and Amazon, and it took some luck even for them to spot the problem. ‘This stuff is at the cutting edge of the cutting edge, and there is no easy technological solution,’ one of the people present in McLean says. ‘You have to invest in things that the world wants. You cannot invest in things that the world is not ready to accept yet.'”
For my part, I try not to spin my wheels worrying about things I can’t change, and the supply chain challenges definitely fit into that category. I’ll have some more thoughts on the supply chain problem and what we can do about it in an interview to be published next week.
But for the time being, there are some things worth thinking about that can help mitigate the threat from stealthy supply chain hacks. Writing for this week’s newsletter put out by the SANS Institute, a security training company based in Bethesda, Md., editorial board member William Hugh Murray has a few provocative thoughts:
- Abandon the password for all but trivial applications. Steve Jobs and the ubiquitous mobile computer have lowered the cost and improved the convenience of strong authentication enough to overcome all arguments against it.
- Abandon the flat network. Secure and trusted communication now trump ease of any-to-any communication.
- Move traffic monitoring from encouraged to essential.
- Establish and maintain end-to-end encryption for all applications. Think TLS, VPNs, VLANs and physically segmented networks. Software Defined Networks put this within the budget of most enterprises.
- Abandon the convenient but dangerously permissive default access control rule of “read/write/execute” in favor of restrictive “read/execute-only” or even better, “Least privilege.” Least privilege is expensive to administer but it is effective. Our current strategy of “ship low-quality early/patch late” is proving to be ineffective and more expensive in maintenance and breaches than we could ever have imagined.




This is a cool take on ‘spy vs spy’ and all, but isn’t the real threat for bad guys to just hide the malignant code somewhere in firmware? It’s been done before, when Dell shipped a batch of computers containing a virus that was hidden in firmware. That hurt Dell for a period after it was revealed (Sorry Brian, before your time :)). Such techniques have only been improved, I’m sure. One person, or one team, writing firmware code off site, off island, or whatever. That’s all it would take. Foreign governments, or sophisticated hackers, they would all like to control the worlds computing power……
It would take more than one person writing code offsite. It would take everyone else in the chain who reviews and validates code to either not do their jobs or not notice.
Unlike hardware, which can be modified after design to add (or remove though spies would likely not go this route) components and still end up with something that performs exactly as designed (at least, to the degree that tests exists to validate this), firmware is different. You can’t even corrupt one bit without detection, much less introduce meaningful code.
Unfortunately, the likely way a virus makes its way into something like firmware from Dell or Apple is from sloppy engineering than deliberate action by a malicious actor.
And yet we know the Equation Group (using firmware source shared with the US Government as a requirement of a contract) have created at least one such implant for drive firmware….
“The U.S. Government isn’t eager to admit it, but there has long been an unofficial inventory of tech components and vendors that are forbidden to buy from if you’re in charge of procuring products or services on behalf of the U.S. Government.”
I work for a US Govt. agency and recently procured a Dell laptop and when it took months to be delivered, I inquired about other Dell model as an alternative, only to be told that the other models were made in China and, therefore, couldn’t be procured. So it’s not just specific vendors on the grey/blacklist, it’s specific models and devices! My work is not classified, and it’s not a DoD agency.
I always wonder if Apple does deep inspection of their iPhone circuitboards/microchips to ensure that China’s not slipping chips/circuits like this into their mix. Or, for that matter, ensuring that competitors or the US govt. isn’t slipping in mods like this. Their reputation is built on the security of their handsets.
I always wonder if Apple does deep inspection of their iPhone circuitboards/microchips to ensure that China’s not slipping chips/circuits like this into their mix. Or, for that matter, ensuring that competitors or the US govt. isn’t slipping in mods like this. Their reputation is built on the security of their handsets.
Have you seen the teardowns on the latest iPhones (and last year’s X)? You can’t fit an extra chip the size of a grain of rice on those PCBs (considering that it would need signal lines, etc.)… there’s no room. 🙂
https://www.ifixit.com/Teardown/iPhone+XS+and+XS+Max+Teardown/113021
I was wondering why there was a sudden surge in Supply Chain Security jobs at Dell Careers. (SRO)
Not surprised. Thanks for the coverage. Love from ATX.
Excellent article.
A repeat of the zerox incident. Love it. But, even the dept of defence, doesn’t yet realize, the spies are everywhere. Especially if the logistical chain is compromised. You have to assume every uncontrolled piece could be a dual use item. Could a memory chip be comprised? Could a diode be dual use? With the shrinking of circuitry, what else could be added. If there can be a million diodes and transistors in a chip, how can you be sure all are actually working for you, and not for someone else?
yup
While I believe China does this I think his story is bunk. Why would they add a chip? Couldn’t they have embedded malicious software within an existing component. This I believe is nothing more than Trump administration building a case for discrediting 2018 and 2020 elections. We will be seeing a constant trickle of stories about China, culminating with “they rigged our election”
*this story NOT “his” story.
There are some credible explanations over at The Register site on this matter as to why a separate component could be needed.
https://www.theregister.co.uk/2018/10/04/supermicro_bloomberg/
That’s a good read. However I am left not knowing what to think. Something just feels fishy about this. I find it hard to believe that companies this size would not have robust SEIM systems that would set off alarms. but then again..
Did you miss the part where Krebs mentioned a quote that supply chain security is a nearly insurmountable problem? I agree Apple probably does have robust validation testing for all their products, but when you enter the realm of espionage, intelligence, and military operations for hacking, I think the most advanced electronics companies out there (Apple included) would struggle with finding all of these backdoors..
This comment shows that you are blind to the past.
how so?
So you think it’s more likely that turnip had Bloomberg start working on a fake story over a year ago about china spying on the US, than china actually spying on the US. I have a song just for you; Destroyer by the Kinks.
If you’re seeing situations where a separate non-BOM chip is attached to the face of a board, how many other situations are there where the functionality is buried inside a multi-layer PCB?
egress filtering. That is the answer.
Many companies are using firewalls to limit inbound traffic only. That is completely stupid.
Segment servers into segments with only required network openings between.
Require that all servers that access the Internet uses a proxy server for HTTP/HTTPS traffic (preferable one using authentication), and block all direct outgoing traffic at firewall level. Only allow servers to access domain names that are whitelisted. For other protocols, create specific rules to specific destinations (requires fixed IP).
That is all basic low level security, and it would block most malware from communicating out (VPN over DNS requests an exception, other measures needed here).
From the Bloomberg description, Apple discovered it by looking at outgoing traffic.
I have outgoing to china from my chinese IP cams at home as well. I blocked their Internet access, but need to move them to another VLAN, as otherwise they could basicly change IP address, or clone MAC address to try and bypass my firewall. Such things should be on a no-internet-access VLAN as a minimum.
The big problem is people forgetting about egress filtering.
“basic low level security”
And, basic logging would show unauthorized connection attempts.
This. This. This.
We segment network traffic by VLANs to the point where outside of certain end-user devices we are able to have a very good understanding of what packets are flying across the network. And then we treat all end-user devices as potentially compromised.
DHCP is de debbil!!!!
Seriously, the idea that you can randomly plug stuff together and it will figure out what works is totally unrealistic in the face of modern security threats. Networks need to be properly designed, properly gatewayed, properly secured, and properly monitored — and DHCP ain’t that.
For some time I’ve been more concerned about the potential risk of seeding backdoors into the roll out of 5G networks – largely being contracted with major Chinese manufacturers like Huawei and ZTE – versus the potential years of delay if the Chinese are simply banned as suppliers and smaller, less experienced companies grin and sell their own dubious ways into the job. One thing the Chinese big boys have is money and scale, and it seems to me that this situation raises contractual and insurance liability IFF the terms are carefully set out. One thing for hundreds of thousands of product units are deployed with malware or malchips, quite another if a major supplier is held liable for $billions of repair and replacement costs if / when building in a knowable vulnerability is proved. The biggest problem with the supplier(s) in question here is they are corporate bit players that can go bankrupt without a ripple – the short answer is appropriate insurance coverage.
So, are Bloomberg or Amazon/Apple lying ?
Yes, No ??
Lying is probably not the right word. If, as the Bloomberg article says, this is subject to a Top-Secret probe by the DoD, then they are obeying the law by not disclosing classified information.
As was mentioned in another comment, I think the most valuable, and least detectable, would be an embedded kill switch. Imagine how many devices, not only governmental, but devices in home, financial sector, public utility, etc etc, could be bricked by a single command sequence. Devastatingly effective.
This story should not surprise anyone. And as several commenters already pointed out, it’s sobering to consider what *else* may be hiding – particularly in places you can’t shine a light into like firmware.
Put yourself in the shoes of the Chinese government or military and consider this: Your western adversaries (as you view them) have astonishingly trusted you to manufacture all of the electronics that their entire infrastructure is based on. It’s simply too good an opportunity to pass up. If you were the Chinese Government/Military, what would you do with such an opportunity? How about a a kill switch in communications hardware that would brick the device? Knocking out endpoint communications would be disruptive enough but they have manufacturing access to *every* level of our communications infrastructure. Turn off the cell towers. Turn off the fiber relays in backbone infrastructure. Why not all three?
Hopefully stories like this will demonstrate the need to seriously consider the threat to national security that cheap, overseas manufacturing creates.
This doesn’t make sense. The only case where such a capability would be useful is an all-out war. And the costs of western production leaving China if discovered is far from negligible.
If you’re in the military, it makes perfect sense. You don’t wait until a crisis (war, massive insurrection, whatever) is upon you to start planning and provisioning. And “all out war” is definitely a scenario that they plan for. So do we.
“And the costs of western production leaving China if discovered is far from negligible.” Very true, until you balance the costs against national security. Security isn’t provided by the cheapest supplier. And the solution does not have to be a all-or-nothing proposition of relocation western production; though it’s ironic that that is exactly what we have now: all production in China and nothing produced here.
Great article and been a long time subscriber to your amazing research. Just wondering if you can link/share any additional information relating to your comment ‘that one Chinese tech company had made it onto Uncle Sam’s entity list because they sold a custom hardware component for many Internet-enabled printers that secretly made a copy of every document or image sent to the printer and forwarded that to a server allegedly controlled by hackers aligned with the Chinese government.’
Well……”trust no one”……
Though not a part of this story, I’ve always had concerns about IBM’s sale of their PC biz to China. https://www.cloudinsidr.com/content/ibms-china-connection-and-the-betrayal-of-america-how-chinese-government-hackers-manage-to-remain-undetectable/
Excellent video from the Youtube Blackhat channel about hardware backdoors, X86 processors that have a sibling RISC processor that once enabled makes available a God mode instruction that can bypass all security checks in the main processor. Highly technical.
https://www.youtube.com/watch?v=_eSAF_qT_FY
This talk will demonstrate what everyone has long feared but never proven: there are hardware backdoors in some x86 processors, and they’re buried deeper than we ever imagined possible. While this research specifically examines a third-party processor, we use this as a stepping stone to explore the feasibility of more widespread hardware backdoors.
On the topic of hidden chips or software in commercial products, I’ve heard the same concerns from around the world about US made Microsoft and Cisco products.
It’s widely thought that the US government exerts a lot of influence on US commercial companies (see PRISM surveillance program). Many people don’t trust US made computer products.
I know the worldwide reaction to our new distrust of China made products: welcome to the party.
I forgot to include Intel products. They are also distrusted by many from around the world for being a US product .
And US-based cloud computing is not trusted at all either.
It would be difficult to figure out who does more spying between the US and China. The world is mad, and certainly not become a better place.
There is the (possibly apocryphal) story that Microsoft was demonstrating security features in Windows at a conference and had a slide with a piece of code featuring “def NSA_KEY” in the header.
If the Bloomberg article is right, then the journalist had the wrong priority in going after clickbait/stock market moving Apple and Amazon. If 30 companies now had a massive pile of very expensive motherboards they really really didn`t want with a problem that isn`t exactly solved by a supermicro warranty replacement then one of the smaller companies would be happy to talk to journalists and share technical details if not an actual motherboard for independent analyses.
Also the chips between the layers of a PCB would be technically hard, would probably require compromising a different factory to a much greater extend… and, well this part of the story would need more sources than the normal surface mounted chip but instead it is just an off handed mention, so was the fact checking and sourcing really all that great, why wasn’t that more advanced or iffy sounding claim just left out?
30 very pissed of companies full of pissed off technical people and this is all the detail Bloomberg got? Also the more senior intel people the less tech-savy and the more xenophobic they are, source it to “one low level x-ray electronics reversing lab technician” and I would be sold.
If the denials are right then Amazon really messed up in having their own categorical denial on their own website the same day but in all the time the Bloomberg journalists asked them for their comments all they could come up with was a very specifically worded denial that just happen to avoid the core story?
Technically a narrow and a broad denial don’t contradict each other, but Amazon PR people WTF happened there?
Historically I have tracked down every public detail of three supply chain stories and I believe the one with the biggest denial actually happened. I looked at Kaspersky, Gemalto and a Chinese CCTV cam story (IIRC hikvision).
A lot of the Kaspersky FUD stems from the Israeli Intelligence hack of Kasperky and their tendentious leak to US newspapers.
I don’t believe Kaspersky is proven to be consciously backdoored but that Israeli intelligence countered Kaspersky`s constant revelations of Israeli spying including in the US by hacking Kaspersky and then leaking to a US paper (why else was that leak?). The strong feelings of supply chain paranoia, anti Russia sentiment and rising protectionism took it from there. Kaspersky`s detailed technical explanation for having gotten NSA exploits holds water.
Because Kaspersky offers a lot of very imperfect antivirus protection better than some competitors a government wide Kaspersky ban decreases overall security and misses the big opportunities for a more secure supply chain. it would be so much more effective to take the existing government sourcecode audit opportunities that Huawei, Microsoft and soon Kaspersky offer and just invest a couple of millions to fly in smart people too look at the code an keep looking. It would also find accidental security bugs.
With reproducable builds, application whitelisting and code signing there is so much relatively low hanging fruit that in many places isn`t even being plucked. Its not perfect, but it ups the game so much more.
The Gemalto (and Gieseke and deVriendt) response to the Snowden leak that every sim-card in the world could be compromised by GCHQ was terrible. Gemalto basically took an old phishing attack not on themselves but on their customers and said “Security incident already dealt with, lets move on, we did a two day investigation and we had already found every last trace of the advanced GCHQ hackers”.
“Dear investors/customers nothing to see here” denials from the victims of intelligence services attacks do happen, they salvage stock prices and let customers off the hook from an ridiculously tough problem.
Thanks to Gemaltos completely unserious attitude I am now sure GCHQ got in and the keys to many SIM cards are in 5eye hands.
Broad misunderstood xenophobic supply chain panics set off by true but small contained events also happen.
The Chinese CCTV cameras being banned from US military bases in Afghanistan was paranoia stoked by a competing US vendor of Chinese manufactured Korean cameras on a CCTV camera forum or blog the guy ran or something?
This stuff goes back to the days of Crypto AG. The supply chain problem is not perfectly solvable but so much of this is about the counterfeiting, protectionism and xenophobia worries of people who just just don’t understand how absurdly complex and globalized modern technology is.
I think writing this I switched from “team bloomberg” to “team everyone with big interests in denials”. Whatever the truth, some people have really set themselfs up to loose all credibility ever again if evidence of the origin of this story right in the middle of “the sum of all fears” bubbles up. This really sucks, trust and credibility were really all we had on this issue. I really want to thank the register for pointing out Bloomberg reporters get bonuses based on how much they move the stock market.
I tried.
I really tried. But I had to stop after your eighth paragraph.
When there are paragraphs like that, it’s a pro. Someone’s agent or paid PR stooge. Beware of the disinfo discrediting the story.
nah it would have been better written. The post reads more la rant from somebody trying to say too much in one post
Yes currently supply chain is broken and infeasible to fix in the current IT marketplace. Whether or not the attack in the Bloomberg article actually occurred as reported, that type of attack is, I suggest, absolutely feasible.
Way forward:
Use the IT with this broken supply chain in mind – plan for mission/business execution with compromised IT.
Forget, discard, throwaway any notion that penetrate and patch is a way forward (recognizing that much of current cybersecurity is really just penetrate and patch).
Look to ‘trusted foundry’ for specific IT components if there is no viable ‘wise use’ of the existing IT.
Open the Pandora’s box of IT reality and neither run away screaming nor pretend that we did not see what we did.
Bottom line: Stop managing security controls and start managing risk.
Another analysis by bloom, it’s bigger then thought. You see, the new deal, is government age cies on the cloud? All your secrets exposed to the competition. Neat uh? First released to the public in 13, I thought their were articles about infiltrated circuitry about 2000. And research on it in the 80’s. And conceptual marketing not shortly after that. So it’s not new, oh, ah , yeah, first reported on, by foreign press, early 00’s as don’t by us.
A consideration and then a personal experience:
Consider that if this is true (and I’m inclined to believe it is, due to the cost/benefit gains by an adversary and the assymetric costs of placement vs detection), and a federal investigation has been in place for quite some time and extends to national security levels, then you can bet that Amazon and Apple (as canaries in a coal mine, due to the sheer number of servers and IP at play, not to mention the commerce and communications that could be involved via their customers), the federal government could be providing marketing cover to these affected companies through the use of National Security Letters, where the companies are FORBIDDEN from stating that they have been affected.
My own experience – I purchased a “table-lamp” type of book scanner that is easily found on Amazon that began as an indiegogo campaign.
Due to some odd behavior of the product (wouldn’t work while an antivirus tool was operating), and some inappropriate actions on the part of their tech support personnel on my computer (dumping and running an infected program on it, and also improperly accessing other files while connected), I began using some of the sysinternals tools from Microsoft to watch the behavior of the scanner software as it scanned some documents.
I saw it looking at areas of my computer that this book scanner software had no business looking, such as my surfing history, various directories of interest to users producing documents, etc. I also discovered it making an outbound connection to a server in China.
I questioned them several times on this, and never received an answer on some of my questions, and they tried to dismiss other questions which I was able to disprove.
I reported this to the FBI, and they didn’t seem that interested at first, and then later expressed a mild interest, but didn’t follow up.
Personally, I wish I knew how to reverse engineer code so that I could find some of this activity coded in, and bypass it, as I was otherwise pleased with the product. But I have not used it since.
The software and hardware is node-locked, so that you MUST enter the hardware key as part of the registration, so they have a good idea who is using what hardware and software. It also appears that it disables itself from working after some time to force the end user to get an updated copy of the software on a regular basis. (These are not licensing requirements nor is it leased equipment. It was a purchased product.)
The irony is that this company is currently ramping up a new version of their product, and offering early customers a discount. Yeah, I gotta have me more of that! (sarcastically)
Lack of reply by the FBI or anybody else does not always indicate there is no interest. Frequently your POC doesn’t have the experience to handle what you are giving them so they pass the information on to somebody higher up the chain. Sometimes it just gets bogged down and lost in the transfer process. That is a communication problem.
The feds ignored FSB warnings about the Boston bombing jerks.
The feds (and locals) ignored warnings about the jerk who killed his schoolmates in Parkland Florida.
The feds ignored warnings by the father of the jerk who killed dozens in the Orlando Florida nightclub.
The feds ignored the brothers who stole computers and network credentials from many congressmen/women, then sent family out of country.
And the feds ignored that lady politician who forwarded classified emails to an aide’s laptop and stored more data in a bathroom closet.
Hopefully, the FBI found out you’re right about the spying scanner and weren’t allowed to thank you. Maybe it made its way to Homeland Security and the desk of the president.
Or they ignored it. :-/
Supply chain investigations are nearly impossible, because there is no information sharing. Our own government (US) has a do-not-buy list by the pentagon, but it is secret secret, so the let the rest of us continue to allow products on the do-not-buy list to be sold to protect ourselves and our businesses etc. The only reason I can surmise for doing this is that they want to exploit any potential backdoors themselves, even against our own populace. The lack of any authority on what software and devices are “safe” creates a giant he said she said type situation, and it’s security professionals like us that suffer, because we really can’t assure anyone that the products we are recommending to protect against free-lance hackers aren’t compromised by state-sponsored hackers.
Couldn’t monitoring for anomalous network traffic produced by the composite product for a reasonable period of time prior to deployment give reasonable assurances that none of the constituent components are being used for spying? Continuing such monitoring after deployment would enable incident response if the spying began later which depended on timing or other conditions.
There is something very odd about this story. Not only are all the alleged sources anonymous, not only is there no actual physical evidence that can be produced of these implanted chips, but Apple, Amazon, the DHS and GCHQ in the UK are all saying the story is, basically, fake. Have the investigative journalists at Bloomberg been hoaxed?
Here’s the latest on it, from Graham Cluley.
http://www.grahamcluley.com/department-of-homeland-security-and-gchq-back-apple-and-amazons-denials-they-were-hacked-by-china/
The whole story smells of snakeoil lobbying.
“serverless code that runs on the structure of the internet”????
There is a large possibility of this being real issue.
If it was fake, then layers from the affected parties would be standing in the reception of Bloomberg and requiring a correction, now! This has not happened.
The affected parties do all deny that it has happened, but Bloomberg has not withdrawn the article.
> Call it the “brown list, “black list,” “entity list” or what have you.
What I have is the term “Denial List”. US headquartered multinationals have had to check all orders for certain technology against a supplied “denial list” of potential customers before accepting the order and making delivery. The list was regularly updated.
I blame it all on Nixon and ping-pong!
The irony is the commie bashers of old have sold their souls to them.
Anything for a buck.
More over the original server motherboards are designed by an American company Super Micro. However, the malicious chips had been inserted during the manufacturing processes in China. According to the report, the chips were founded in servers used by U.S. military, intelligence agencies, and tech companies including Apple and Amazon. https://reviewedbypro.com/china-spies-on-the-u-s-companies-using-tiny-chips/ Can you imageine?
This is another source of this case. Bloomberg also notes that Apple and Amazon have detected chips on the servers motherboards back in 2015. The incident was reported to the U.S. authorities. However, the companies deny the claims.
I see you don’t monetize your website, don’t waste your traffic, you can earn extra bucks every month.
You can use the best adsense alternative for any type of website (they approve all websites), for more info simply search in gooogle: boorfe’s tips monetize your website