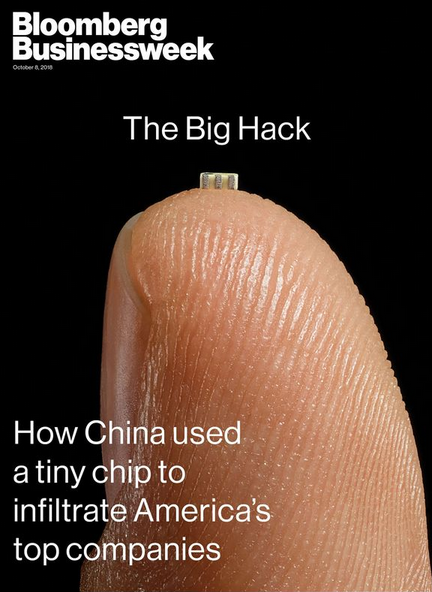
From time to time, there emerge cybersecurity stories of such potential impact that they have the effect of making all other security concerns seem minuscule and trifling by comparison. Yesterday was one of those times. Bloomberg Businessweek on Thursday published a bombshell investigation alleging that Chinese cyber spies had used a U.S.-based tech firm to secretly embed tiny computer chips into electronic devices purchased and used by almost 30 different companies. There aren’t any corroborating accounts of this scoop so far, but it is both fascinating and terrifying to look at why threats to the global technology supply chain can be so difficult to detect, verify and counter.
 In the context of computer and Internet security, supply chain security refers to the challenge of validating that a given piece of electronics — and by extension the software that powers those computing parts — does not include any extraneous or fraudulent components beyond what was specified by the company that paid for the production of said item.
In the context of computer and Internet security, supply chain security refers to the challenge of validating that a given piece of electronics — and by extension the software that powers those computing parts — does not include any extraneous or fraudulent components beyond what was specified by the company that paid for the production of said item.
In a nutshell, the Bloomberg story claims that San Jose, Calif. based tech giant Supermicro was somehow caught up in a plan to quietly insert a rice-sized computer chip on the circuit boards that get put into a variety of servers and electronic components purchased by major vendors, allegedly including Amazon and Apple. The chips were alleged to have spied on users of the devices and sent unspecified data back to the Chinese military.
It’s critical to note up top that Amazon, Apple and Supermicro have categorically denied most of the claims in the Bloomberg piece. That is, their positions refuting core components of the story would appear to leave little wiggle room for future backtracking on those statements. Amazon also penned a blog post that more emphatically stated their objections to the Bloomberg piece.
Nevertheless, Bloomberg reporters write that “the companies’ denials are countered by six current and former senior national security officials, who—in conversations that began during the Obama administration and continued under the Trump administration—detailed the discovery of the chips and the government’s investigation.”
The story continues:
Today, Supermicro sells more server motherboards than almost anyone else. It also dominates the $1 billion market for boards used in special-purpose computers, from MRI machines to weapons systems. Its motherboards can be found in made-to-order server setups at banks, hedge funds, cloud computing providers, and web-hosting services, among other places. Supermicro has assembly facilities in California, the Netherlands, and Taiwan, but its motherboards—its core product—are nearly all manufactured by contractors in China.
Many readers have asked for my take on this piece. I heard similar allegations earlier this year about Supermicro and tried mightily to verify them but could not. That in itself should be zero gauge of the story’s potential merit. After all, I am just one guy, whereas this is the type of scoop that usually takes entire portions of a newsroom to research, report and vet. By Bloomberg’s own account, the story took more than a year to report and write, and cites 17 anonymous sources as confirming the activity.
Most of what I have to share here is based on conversations with some clueful people over the years who would probably find themselves confined to a tiny, windowless room for an extended period if their names or quotes ever showed up in a story like this, so I will tread carefully around this subject.
The U.S. Government isn’t eager to admit it, but there has long been an unofficial inventory of tech components and vendors that are forbidden to buy from if you’re in charge of procuring products or services on behalf of the U.S. Government. Call it the “brown list, “black list,” “entity list” or what have you, but it’s basically an indelible index of companies that are on the permanent Shit List of Uncle Sam for having been caught pulling some kind of supply chain shenanigans.
More than a decade ago when I was a reporter with The Washington Post, I heard from an extremely well-placed source that one Chinese tech company had made it onto Uncle Sam’s entity list because they sold a custom hardware component for many Internet-enabled printers that secretly made a copy of every document or image sent to the printer and forwarded that to a server allegedly controlled by hackers aligned with the Chinese government.
That example gives a whole new meaning to the term “supply chain,” doesn’t it? If Bloomberg’s reporting is accurate, that’s more or less what we’re dealing with here in Supermicro as well.
But here’s the thing: Even if you identify which technology vendors are guilty of supply-chain hacks, it can be difficult to enforce their banishment from the procurement chain. One reason is that it is often tough to tell from the brand name of a given gizmo who actually makes all the multifarious components that go into any one electronic device sold today.
Take, for instance, the problem right now with insecure Internet of Things (IoT) devices — cheapo security cameras, Internet routers and digital video recorders — sold at places like Amazon and Walmart. Many of these IoT devices have become a major security problem because they are massively insecure by default and difficult if not also impractical to secure after they are sold and put into use.
For every company in China that produces these IoT devices, there are dozens of “white label” firms that market and/or sell the core electronic components as their own. So while security researchers might identify a set of security holes in IoT products made by one company whose products are white labeled by others, actually informing consumers about which third-party products include those vulnerabilities can be extremely challenging. In some cases, a technology vendor responsible for some part of this mess may simply go out of business or close its doors and re-emerge under different names and managers.
Mind you, there is no indication anyone is purposefully engineering so many of these IoT products to be insecure; a more likely explanation is that building in more security tends to make devices considerably more expensive and slower to market. In many cases, their insecurity stems from a combination of factors: They ship with every imaginable feature turned on by default; they bundle outdated software and firmware components; and their default settings are difficult or impossible for users to change.
We don’t often hear about intentional efforts to subvert the security of the technology supply chain simply because these incidents tend to get quickly classified by the military when they are discovered. But the U.S. Congress has held multiple hearings about supply chain security challenges, and the U.S. government has taken steps on several occasions to block Chinese tech companies from doing business with the federal government and/or U.S.-based firms.
Most recently, the Pentagon banned the sale of Chinese-made ZTE and Huawei phones on military bases, according to a Defense Department directive that cites security risks posed by the devices. The U.S. Department of Commerce also has instituted a seven-year export restriction for ZTE, resulting in a ban on U.S. component makers selling to ZTE.
Still, the issue here isn’t that we can’t trust technology products made in China. Indeed there are numerous examples of other countries — including the United States and its allies — slipping their own “backdoors” into hardware and software products.
Like it or not, the vast majority of electronics are made in China, and this is unlikely to change anytime soon. The central issue is that we don’t have any other choice right now. The reason is that by nearly all accounts it would be punishingly expensive to replicate that manufacturing process here in the United States.
Even if the U.S. government and Silicon Valley somehow mustered the funding and political will to do that, insisting that products sold to U.S. consumers or the U.S. government be made only with components made here in the U.S.A. would massively drive up the cost of all forms of technology. Consumers would almost certainly balk at buying these way more expensive devices. Years of experience has shown that consumers aren’t interested in paying a huge premium for security when a comparable product with the features they want is available much more cheaply.
Indeed, noted security expert Bruce Schneier calls supply-chain security “an insurmountably hard problem.”
“Our IT industry is inexorably international, and anyone involved in the process can subvert the security of the end product,” Schneier wrote in an opinion piece published earlier this year in The Washington Post. “No one wants to even think about a US-only anything; prices would multiply many times over. We cannot trust anyone, yet we have no choice but to trust everyone. No one is ready for the costs that solving this would entail.”
The Bloomberg piece also addresses this elephant in the room:
“The problem under discussion wasn’t just technological. It spoke to decisions made decades ago to send advanced production work to Southeast Asia. In the intervening years, low-cost Chinese manufacturing had come to underpin the business models of many of America’s largest technology companies. Early on, Apple, for instance, made many of its most sophisticated electronics domestically. Then in 1992, it closed a state-of-the-art plant for motherboard and computer assembly in Fremont, Calif., and sent much of that work overseas.
Over the decades, the security of the supply chain became an article of faith despite repeated warnings by Western officials. A belief formed that China was unlikely to jeopardize its position as workshop to the world by letting its spies meddle in its factories. That left the decision about where to build commercial systems resting largely on where capacity was greatest and cheapest. “You end up with a classic Satan’s bargain,” one former U.S. official says. “You can have less supply than you want and guarantee it’s secure, or you can have the supply you need, but there will be risk. Every organization has accepted the second proposition.”
Another huge challenge of securing the technology supply chain is that it’s quite time consuming and expensive to detect when products may have been intentionally compromised during some part of the manufacturing process. Your typical motherboard of the kind produced by a company like Supermicro can include hundreds of chips, but it only takes one hinky chip to subvert the security of the entire product.
Also, most of the U.S. government’s efforts to police the global technology supply chain seem to be focused on preventing counterfeits — not finding secretly added spying components.
Finally, it’s not clear that private industry is up to the job, either. At least not yet.
“In the three years since the briefing in McLean, no commercially viable way to detect attacks like the one on Supermicro’s motherboards has emerged—or has looked likely to emerge,” the Bloomberg story concludes. “Few companies have the resources of Apple and Amazon, and it took some luck even for them to spot the problem. ‘This stuff is at the cutting edge of the cutting edge, and there is no easy technological solution,’ one of the people present in McLean says. ‘You have to invest in things that the world wants. You cannot invest in things that the world is not ready to accept yet.'”
For my part, I try not to spin my wheels worrying about things I can’t change, and the supply chain challenges definitely fit into that category. I’ll have some more thoughts on the supply chain problem and what we can do about it in an interview to be published next week.
But for the time being, there are some things worth thinking about that can help mitigate the threat from stealthy supply chain hacks. Writing for this week’s newsletter put out by the SANS Institute, a security training company based in Bethesda, Md., editorial board member William Hugh Murray has a few provocative thoughts:
- Abandon the password for all but trivial applications. Steve Jobs and the ubiquitous mobile computer have lowered the cost and improved the convenience of strong authentication enough to overcome all arguments against it.
- Abandon the flat network. Secure and trusted communication now trump ease of any-to-any communication.
- Move traffic monitoring from encouraged to essential.
- Establish and maintain end-to-end encryption for all applications. Think TLS, VPNs, VLANs and physically segmented networks. Software Defined Networks put this within the budget of most enterprises.
- Abandon the convenient but dangerously permissive default access control rule of “read/write/execute” in favor of restrictive “read/execute-only” or even better, “Least privilege.” Least privilege is expensive to administer but it is effective. Our current strategy of “ship low-quality early/patch late” is proving to be ineffective and more expensive in maintenance and breaches than we could ever have imagined.




I think DARPA is working on this. Such as “kill switches” embedded with HF antennas.
You can have it fast, cheap, or secure — pick any two.
Yeah, as long as “secure” isn’t one of your choices.
Gary, Well Said! And haven’t we all experienced it first hand?
Fast and Cheap is not Secure
Cheap and Secure is never Fast
Fast and Secure is never Cheap
Sure those might not be the tagline of many security products but you cant deny this is more often the case than not.
If the allegations are true,why is it better to deny the problem?
This sentence from the article is amazing: The issue here isn’t that we can’t trust technology products made in China. Indeed there are numerous examples of other countries — including the United States and its allies — slipping their own “backdoors” into hardware and software products. Where is this all going to lead?
Deny, deny, deny is the traditional response of large tech companies to any negative rumors and press reports, especially when publicly traded. They’re afraid of customer reaction, lower stock prices, and the possibility of new attempts at shareholder and government oversight.
Why deny? Because it works well, unless the evidence is overwhelming and can be revealed publicly.
These particular giant companies are further fearful of the cancellation of government contracts, worth billions.
Examples of big tech deals with US government agencies include: an existing CIA-Amazon cloud storage agreement, Microsoft’s child abuse photography/video contract with the US DOJ, Facebook’s propaganda work for the US State Department, IBM’s data analytics deal for DHS, Apple’s deal with DHS-ICE to provide secure tablets and phones, the DLT-Navy deal for Oracle products, and the proposed US DOD JEDI project.
There’s more, but I don’t have time for it now. 🙂
https://defensesystems.com/articles/2018/07/26/jedi-hits-the-street.aspx?m=1
National Security Letters (NSL) can include a gag order… just sayin’
FOSS.
We’ve already accepted “security” processors with more privilege than the main CPU in all modern processors. I think the battle is already lost.
I read this and think about drones, cars without steering wheels, and the newest fad of AI.
So I guess it is time to pull out the old Apple II and blow the dust off the Amiga 500….
I have thought about fleets of driverless bot cars / trucks blocking key interstates and demanding ransoms, or botjacking important medical / pharmaceutical shipments to hideaways in remote locations.
This thing about a microchip the size of a piece of rice is total B.S. I have never seen a microprocessor, micro-controller, F.P.G.A or a ASIC that size where it could be put between the layers of a P.C. board.
The Bloomberg Businessweek article is TOTAL B.S.
A lot of things go between the layers of a motherboard.
Mostly, it’s just pathways for circuit connections, but there’s no technical reason a bare chip wouldn’t fit.
The only thing that can go between the layers of a PC boards is copper traces that are connected by way of via’s that run through to the outside layers and surface mount components .
Statements like that are what inspire my more creative impulses! I love designing things that were ‘impossible’
Any layer of a multi-layer board can be CNC milled according to computer-aided design files, so as to have precisely sized holes that allow fitting any physical object. Vias can be placed which only run partially through a board, and connect any choice of board layers. Boards can be populated before all of the board layers are laminated into place, perhaps using a top half/bottom half approach to begin with. In fact, it ought to be possible to put all of the board components, including batteries, on the inside of a thick board so as to produce something like a ‘end-product on a chip’ and just not have the outer plastic case. Somewhat like a hardware device that has been potted solid
Google pcb embedded components and look at the results. It is not common to place components inside a pcb, but it can be done. As for tiny components. I have personally used bare-silicon diodes that are 0201 sized: that is 0.6 mm by 0.3 mm by 0.15 mm. If you want to get a feel for that size, that chip can fit in between the arms of the capital E on a dime. Making a custom IC at this size and capability is certainly possible with modern technology.
After actually reading the article, it doesn’t look like they embedded the chip, they just replaced an existing passive component… even easier!
It looks like a chip coupling capacitor or a ferrite bead for RF suppression
Are you referrring to the chips in the newest Chip’n’Pin credit cards? Those seem like they’d fit ‘inside’ a circuit board.
The Bloomberg article has a picture of the chip and its location on the motherboard.
The “chip” looks like a ferrite filter or similar. It’s not an integrated circuit.
Exactly. The color of the chip does not have to be black. The part was made in a white ceramic package on purpose.
It would have been easier for the investigation if the laser marking on the part said “SPY CHIP”, yes agreed.
If you had bothered to read the actual article, you’d know that the device found was made to look like an RF signal conditioning chip, otherwise known as a directional coupler.
Missing from the Bloomberg article: Evidence and Proof.
Bloomberg has an established reputation for reliable journalism (as does this blog), and that’s worth something; actually, quite a bit. But readers are left with “…17 anonymous sources as confirming the activity.”
“Extraordinary claims require extraordinary evidence.” — Carl Sagan (and others)
All of the DOD contractors were told to immediately stop using their laptop computers and turn them in.
This happened after Lenovo bought the PC business from IBM years ago and started manufacturing them in China.
IBM Thinkpads were always made overseas – all Lenovo did was buy and re-brand.
PSST:
It is indeed possible to embed a chip between board layers; you just can’t give it a conventional epoxy package.
Thanks again, Brian, for another timely story.
I sure hope Bloomberg is wrong!
Yes, lets stop wasting time debating if chips can be placed inside boards. Lets instead look into how to do it
The actual guts of many chips is very small and wafer versions are readily available for many of them.
It does not seem an insuperable problem if something is added that should not be there. A light or x ray inspection should be possible and could be automated if anything is suspected and compared against a known good board.
You deserve what you get if you let your enemies make decisions about software, parts placement, etc.
If you build in checks which you can run on the board, you increase the cost to where it may not be worth it. A multi pronged approach, including digging into finances and who is there at your off shore factory could be revealing.
But that is not the American way. Hot, fast and loose is what is rewarded by Wall St.
Agree completely. I’ve often said that in our “capitalist” nation, the motto is get your product to market first, fix the problems later.
Yes, lets not worry about if someone were to x-ray our boards. Just build-in the hidden circuits & kick them out the door before someone else beats us to it!
Can a microchip the size of a grain a rice really do that much? The chinese must have some amazing engineers then to be able to hack into thousands of motherboards using that
IMHO — They are stealing the engineering with the goal of “Made in China 2025”
Do the servers using these motherboards actually call home (contact suspicious addresses) at any time? The Bloomberg article seems to concentrate on how tiny they are, leaving little space for code **Red Flag!**.
Of course, this could be another current administration spin. wouldn’t surprise me none.. nosir..
It would take a very, very small amount of code to split a data stream and send packets through the (likely already established) network connection to another destination.
The article addresses this:
The chips call home, but rarely. That’s what raised initial concerns.
The article said that, mostly, the chips sit and wait for a signal. They need only interrupt instructions that secure the rest of the board, allowing an intruder’s signals to reprogram it to grant more access.
The chips inject software into the baseband management processor when it boots. All they have to do is sit on the EEPROM I2C line and inject some data at the appropriate time.
Calling home could be done via the BMC (Baseboard Management Controller). Ordinarily the BMC provides data on Fan speed, thermal of critical components etc. – The BMC would not have access to user file space unless the BMC firmware were modified for that purpose.
That BMC data generally has an isolated ethernet connection.
Do you really think that Apple or Amazon are dim enough to not monitor the BMC traffic?
I think the Bloomberg story is not of value for it’s lack of specific ‘how it was done’ information.
I quite agree, Tom. Very sketchy. I think that the story’s a spin.
as someone that used to work with servers in a large data center that had supermicro motherboards and their ipmi baseband, while they were typically put onto their own vlans/switches, that traffic was not monitored. since they were typically isolated they did not have direct external access but coupled with another security issue (such as modifying the vlan rules) and you could have a big problem.
Every objection I’ve seen is about “omg how could they do that, too complicated, big, would take re-engineering, would need to tap into every component, etc”
Nope sorry, invalid objections.
This about a tiny chip tapping into ALREADY EXISTING monitoring built into the motherboard. For instance, dell has idrac, HP has ilo, and there’s the Intel IME built into all intel chips. Supermicro has BMC.
If you are tapping into an existing monitoring solution just to subvert it, the job becomes vastly easier, and not much size is needed. The already existing solution is out of band, already setup to be accessed remotely through IP, can often be accessed even if power is off to the server, etc.
Take a look, supermicro brags about their monitoring system and how it’s integrated into their motherboards.
https://www.supermicro.com/products/nfo/IPMI.cfm
https://www.supermicro.com/products/nfo/ManagementSoftware.cfm
One could argue that the presence of Android on any manufacturer’s phones could constitute a security risk.
How expensive would it be for the supplier to supply Supermicro with enough of those little buggers for every board Supermicro makes?
If this hack is true, then perhaps it is confined to a few boards Supermicro makes that are used by important organizations.
Also, wouldn’t the Chinese need a rather large manpower unit to receive and process all the information it receives from the little buggers?
Just thinking….
Regards,
According to the Bloomberg article the tiny chips simply provide access for Chinese hackers to all other features of the motherboard. Apparently they are being seeded into Supermicro motherboards for later use, and are not, as a rule being activated now.
Update!
An Avira blog article (Avira is a German AV) says about 30 organizations/companies were hacked–the likes of Apple, Amazon, DOD, warships, etc.). Like Brian/s article, Avira wasn’t completely sure about the hack, but it mentioned that about 7 different security sources (some government) had verified the hack.
Regards,
I see no update over Kreb’s article. Both mention 30 orgs/companies. 17 sources, not 7, mentioned by both articles.
Update from Bloomberg: “It wasn’t just hardware. An online portal for firmware updates hid and distributed malware.”
https://www.bloomberg.com/news/articles/2018-10-04/the-big-hack-the-software-side-of-china-s-supply-chain-attack
China is on the path to stealing just about anything on the wire….”Made in China 2025, approved by China’s State Council “
Even if the Bloomberg article does not stand up this time, why are we not considering the strategic potential danger?
Trump puts up tariffs on goods sold by China, and subsequently servers in the US start throwing sufficient wobblies that ecommerce and network controlled utilities become unreliable, tariffs reduced and the wobblies cease. I am sure that such problems would be hushed up, but then who is controlling the US – and by implication its allies?
It’s not just a matter of the security of data being compromised by it all being copied over the internet to some domain that may be controlled by the Chinese Army. Competitive advantage can be secured by being more reliable that your competition.
We (no matter which country we live in) need to review whether it is even possible to audit the hardware and software on which our society depends. If the answer is we can’t, we seriously need to consider the impact of the Faustian pact that we seem to have entered into with the likes of China.
The UK are having a nuclear power station built to a Chinese design; UK telecommunications include Huawei kit in the exchanges. What could go wrong?
Will the UK take a robust attitude to Chinese expansion in the South China Sea – does it even dare to consider such an action? What price defending third party countries from aggression on the other side of the world?
(Typed on a laptop made in China)
This is just one method – imagine them fabricating a counterfeit chip that looks and is marked just like the original. Now just bribe someone in the assembly line to substitute a tape reel of these components for the original. The device can host more capability since it rides in a larger chip. It can lay dormant for months or years by counting power cycles until activation, thus escaping the scrutiny of product qualification testing.
– and then listen for packets that contain the secret activation key. Then all sorts of fun things like enable remote access to flash a BIOS which only require altering the state of a single pin
The forward all the data to an IP that is .gov, Have a spy there redirecting the data to china. Maybe a former NSA contractor…………..
Even if this is true, the breached data still needs to be exfiltrated. With the high Cyber Security defenses and 24/7 Cyber Security Analysts monitoring the government networks (NSA, CIA, FBI, DoD, etc…), I don’t see much classified data getting out. A device that small won’t have much power for long rage radio/wireless, and the lower layers of the OSI are monitored closely. Organizations where IT security is an after-thought may be in danger. Thoughts?
I can think of a few ways a 6 pin chip could corrupt a whole mother board.
The BIOS code is kept in an SPI flash rom part. Put the chip in the SPI (3 wire access protocol) path. As the machine boots, it is as simple as corrupting or changing specific bytes. If those are keys or signatures, the system is then open to further attack.
They could also change BIOS settings. This could turn off security measures, then the system is open to further attack.
Many servers use management systems to control/monitor the system remotely. The server management is on if their is power to the board, not if the main processor is turned on. The system is used to update the BIOS. Again, it could change settings and stop upgrades to close security holes.
Having physical access on a system wins.
I agree, there has to be a lot more to make the chip into a real security breach. Odds are, if you are willing to make a chip (a very difficult task) you would be able to exploit the rest of the software.
It’s not necessarily about breaching data, although it can be done as Doug responded.
Think instead about what could happen when thousands of servers across a broad range of industries and military targets all receive the message to shut down. Or a signal to compute something illogical that slows down networked machines everywhere. Or cause fires.
https://youtube.com/watch?v=ZuYbDP2kDfg
That explains why China illegalized bitcoin and other miners; it was overwhelming the government’s own spy networks.
Are you serious? The Chinese uploaded about 100 GB of stolen data from the OPM, a government agency, without anyone noticing.
You guys are correct. I wasn’t thinking of the consequences due to DoS attacks.
Part of the cost advantage China had was when they tied their currency to the dollar and made it 25% cheaper. That was probably the start of their trade war.
They continue to have local content mandates, cybersecurity “reviews”, leak IP to domestic manufacturers, and use other ways to fight the trade war.
The US did not start a trade war with China. They might be willing to start fighting back. Unfortunately any effective response will increase the prices of secure devices.
We have no choice; we must use foreign vendors, because COST. We have no choice; we have to buy foreign-made, because COST.
Why is COST always measured *only* in terms of &local-currency? It’s as if the COST of little/no security doesn’t matter at all.
If US$ COST were the deciding factor in U.S. military spending, then U.S. would buy every bullet, gun, missile and bomb from other countries. Thank goodness that is not reality.
But for reasons that I cannot suss, critical infrastructure gets different treatment. We are whistling in the dark on security COST.
Our govt needs to stop the BS politics that fill our headlines everyday, and put together a strategy to get US companies the help needed to pull manufacturing for technology back into our own country.
Maybe “make America great again” isn’t such a bad idea. Let’s stop the BS in Washington and vote for representatives that will work together for a he greater cause!
“those silly americans, chasing their tails looking for physical devices inside their boards! Our quantuum-pairing technology lets us monitor any data-stream no matter how they try to hide!
Ha… if that was only a joke.
The DOD has been paying it through the Trusted Foundry Program. Probably not enough use of that, though. 😉
https://www.dmea.osd.mil/trustedic.html
A few thoughts :
A chip can not be plugged to a board like a needle to a banana , it needs a physical holes and electricity and connections to other parts . So , someone in the design of the board made the option for a functional board without the chip (to pass inspection) and an upgraded option (including holes and connections) when the chip is inserted . I understand SuperMicro is based in California , and the design is made in the U.S.A , so i don’t think it will be much of a problem for the F.B.I to find the designers and qustion them .
The designers (and their inspectors and managers) must have a VERY good explanation …
m
What annoys me about these article is the sanctimoniousness of the United States when it’s hacked or spied on considering it does the exact same thing to other countries.
Example. How the United States spied on the phone calls of the German Chancellery for 10 years and tapped over 125 government officials phones.
Countries that are officially allied have always spied on each other. They often put more resources to that effort than to spy on their perceived enemies. Spying in allies is necessary to ensure that everyone is complying to agreements and they know that at the end of the day a country”s leadership will follow their own self interest when it conflicts with their allies.
And the very next day Bruce Schneier reported on John McAfee’s tweet:
[The “Presidential alerts”: they are capable of accessing the E911 chip in your phones – giving them full access to your location, microphone, camera and every function of your phone. This not a rant, this is from me, still one of the leading cybersecurity experts. Wake up people!]
and wrote “This is, of course, ridiculous”.
I’m not defending McAfee, but who among us *really* knows what our PCs, laptops, cell phones, are doing?
Quoting John McAfee for any reason other than public ridicule just makes yourself look pretty dim and uninformed. Usually what he says has no basis in fact, and is designed to mislead and/or frighten people. This example is no exception. The guy is a fraud and a quack, and quite frankly a dangerous person all around.
-1
John McAfee is totally cool.
Thinking about setting up a comment filter on anything John McAfee related going forward.
Lol. Your sense of humor is so dry, but so effective.
I remember watching a news show in the 80’s (I think 60 minutes) and it was doing a report about a law that all US military hardware had to be domestic. It specifically called out a concern that computer components sourced from overseas could be altered with kill chips that would turn US equipment to worthless steel during a war. Foreign arms manufacturers funded lobbying efforts that paid congress to block those laws.
The lobbyists and the paid-off congressmen used the argument that companies in allied countries, that our military would be defending against the communists should be trusted. It is all about the money.
Only the designers of these computer boards know exactly which chips belong on the boards. How many of those designers look at each of those boards that come off the assembly lines in China? Since those boards are designed by multiple individuals its easy for a chip to be seen by a designer and assumed it was put on the board by another designer.
I read that there is technology that scans boards to ensure they match the design, but that technology is worthless when the design schematics have been altered to include the nefarious chip.
A quick glance at the interwebs turned up several reports of problems the US has with outsourcing weapons production.
Terms searched: outsource, outsourcing, defense, weapons, usa, 60 minutes
I didn’t find the report you referenced, but this one in 2015 sums up a bit of the problem and references further sources. China has been screwing around with our circuitry for years:
https://www.breitbart.com/national-security/2012/05/31/american-defense-outsourcing/
“…elsewhere, the author was quoted as saying: ‘the Cyber is YUGE’…”
It diminishes your credibility to make an untrue statement that can be so easily checked with modern search tools.
He never said that.
“It diminishes your credibility-”
*chuckle*
(10 minutes of using “widely available search tools” later)
Virginia Beach rally september 6 2016:
https://www.c-span.org/video/?414825-1/donald-trump-holds-town-hall-meeting-virginia-beach-virginia&start=1440
(24:00 minutes in)
Technically the quote is: “the cyber is… so big”
So I suppose I was paraphrasing a bit there I guess. Honestly the rest of it is just as rambling, superficial and insubstantial.
The author of the article I cited wasn’t DJT.
It’s Jason Bradley.
And?