Federal prosecutors this week charged a Seattle woman with stealing data from more than 100 million credit applications made with Capital One Financial Corp. Incredibly, much of this breach played out publicly over several months on social media and other open online platforms. What follows is a closer look at the accused, and what this incident may mean for consumers and businesses.

Paige “erratic” Thompson, in an undated photo posted to her Slack channel.
On July 29, FBI agents arrested Paige A. Thompson on suspicion of downloading nearly 30 GB of Capital One credit application data from a rented cloud data server. Capital One said the incident affected approximately 100 million people in the United States and six million in Canada.
That data included approximately 140,000 Social Security numbers and approximately 80,000 bank account numbers on U.S. consumers, and roughly 1 million Social Insurance Numbers (SINs) for Canadian credit card customers.
“Importantly, no credit card account numbers or log-in credentials were compromised and over 99 percent of Social Security numbers were not compromised,” Capital One said in a statement posted to its site.
“The largest category of information accessed was information on consumers and small businesses as of the time they applied for one of our credit card products from 2005 through early 2019,” the statement continues. “This information included personal information Capital One routinely collects at the time it receives credit card applications, including names, addresses, zip codes/postal codes, phone numbers, email addresses, dates of birth, and self-reported income.”
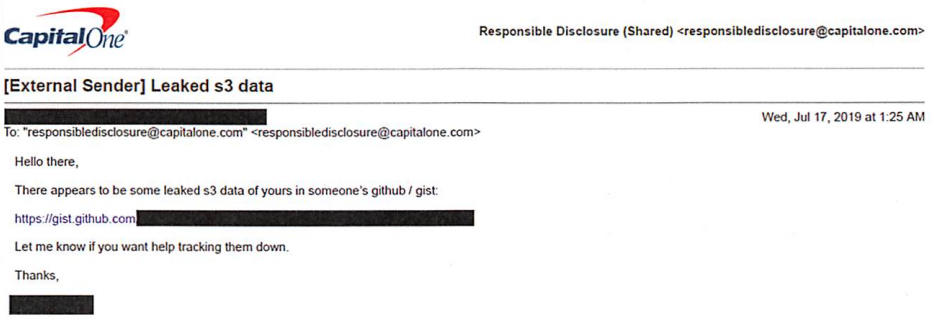
The FBI says Capital One learned about the theft from a tip sent via email on July 17, which alerted the company that some of its leaked data was being stored out in the open on the software development platform Github. That Github account was for a user named “Netcrave,” which includes the resume and name of one Paige A. Thompson.
The complaint doesn’t explicitly name the cloud hosting provider from which the Capital One credit data was taken, but it does say the accused’s resume states that she worked as a systems engineer at the provider between 2015 and 2016. That resume, available on Gitlab here, reveals Thompson’s most recent employer was Amazon Inc.
Further investigation revealed that Thompson used the nickname “erratic” on Twitter, where she spoke openly over several months about finding huge stores of data intended to be secured on various Amazon instances.
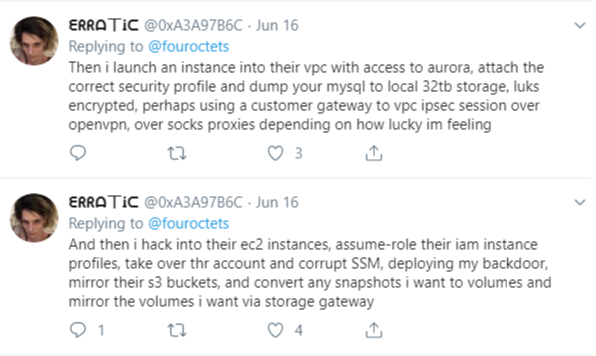
The Twitter user “erratic” posting about tools and processes used to access various Amazon cloud instances.
According to the FBI, Thompson also used a public Meetup group under the same alias, where she invited others to join a Slack channel named “Netcrave Communications.”
KrebsOnSecurity was able to join this open Slack channel Monday evening and review many months of postings apparently made by Erratic about her personal life, interests and online explorations. One of the more interesting posts by Erratic on the Slack channel is a June 27 comment listing various databases she found by hacking into improperly secured Amazon cloud instances.
That posting suggests Erratic may also have located tens of gigabytes of data belonging to other major corporations:
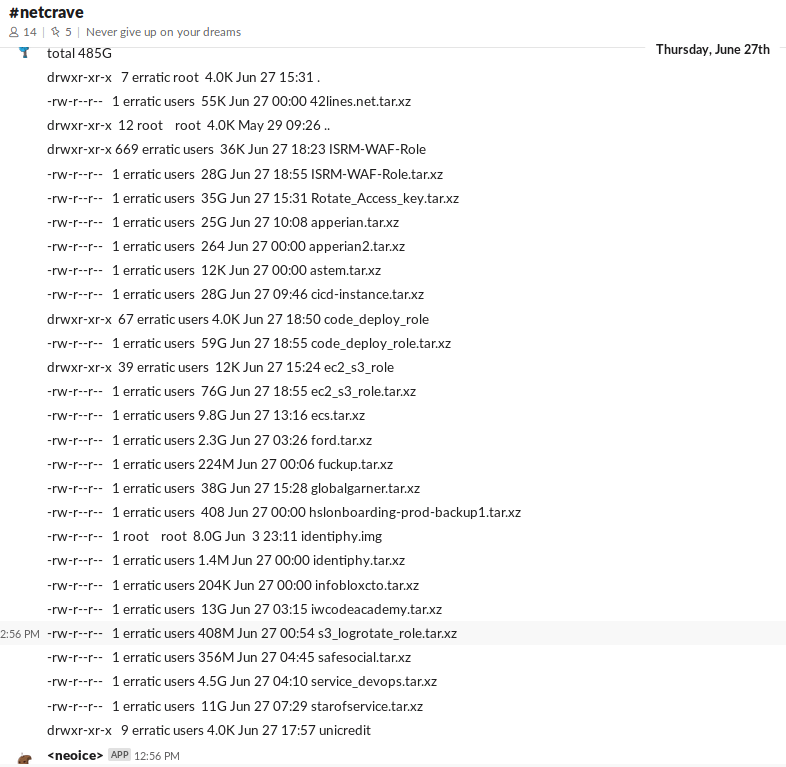
According to Erratic’s posts on Slack, the two items in the list above beginning with “ISRM-WAF” belong to Capital One.
Erratic also posted frequently to Slack about her struggles with gender identity, lack of employment, and persistent suicidal thoughts. In several conversations, Erratic makes references to running a botnet of sorts, although it is unclear how serious those claims were. Specifically, Erratic mentions one botnet involved in cryptojacking, which uses snippets of code installed on Web sites — often surreptitiously — designed to mine cryptocurrencies.
None of Erratic’s postings suggest Thompson sought to profit from selling the data taken from various Amazon cloud instances she was able to access. But it seems likely that at least some of that data could have been obtained by others who may have followed her activities on different social media platforms.
Ray Watson, a cybersecurity researcher at cloud security firm Masergy, said the Capital One incident contains the hallmarks of many other modern data breaches.
“The attacker was a former employee of the web hosting company involved, which is what is often referred to as insider threats,” Watson said. “She allegedly used web application firewall credentials to obtain privilege escalation. Also the use of Tor and an offshore VPN for obfuscation are commonly seen in similar data breaches.”
“The good news, however, is that Capital One Incidence Response was able to move quickly once they were informed of a possible breach via their Responsible Disclosure program, which is something a lot of other companies struggle with,” he continued.
In Capital One’s statement about the breach, company chairman and CEO Richard D. Fairbank said the financial institution fixed the configuration vulnerability that led to the data theft and promptly began working with federal law enforcement.
“Based on our analysis to date, we believe it is unlikely that the information was used for fraud or disseminated by this individual,” Fairbank said. “While I am grateful that the perpetrator has been caught, I am deeply sorry for what has happened. I sincerely apologize for the understandable worry this incident must be causing those affected and I am committed to making it right.”
Capital One says it will notify affected individuals via a variety of channels, and make free credit monitoring and identity protection available to everyone affected.
Bloomberg reports that in court on Monday, Thompson broke down and laid her head on the defense table during the hearing. She is charged with a single count of computer fraud and faces a maximum penalty of five years in prison and a $250,000 fine. Thompson will be held in custody until her bail hearing, which is set for August 1.
A copy of the complaint against Thompson is available here.
Update, 3:38 p.m. ET: I’ve reached out to several companies that appear to be listed in the last screenshot above. Infoblox [an advertiser on this site] responded with the following statement:
“Infoblox is aware of the pending investigation of the Capital One hacking attack, and that Infoblox is among the companies referenced in the suspected hacker’s alleged online communications. Infoblox is continuing to investigate the matter, but at this time there is no indication that Infoblox was in any way involved with the reported Capital One breach. Additionally, there is no indication of an intrusion or data breach involving Infoblox causing any customer data to be exposed.”




Any idea the significance of a3 a9 7b 6c? Does not seem to make much sense in either extended ASCII or EBCDIC. Nor as a 32 bit integer.
Looks like it’s her GPG key ID. It’s in her description of her Twitter account.
It is the GPG public key identifier.
As it says in the headline of the Twitter account,
$ gpg –recv-keys 0xa3a97b6c
Your question had me wondering the same. Best I can figure is it’s her GPG public key. Not sure if there’s more to it.
Hey BK – Is there an implication there that AWS’ WAF has standardized creds available to those in the know?
I don’t think we know those details yet.
I hope the authorities are aware of her mental health issues. She seems at risk for a suicide attempt while in custody.
“His” mental health issues
FIFY
She. A transgender persons pronouns are no more an award for good behavior, or good looks, than yours.
That said this person seems to have problems that may make them THINK they are trans, or want to be trans, without actually being trans at their core.
Did you really just scold someone for misgendering and then set yourself up as a gatekeeper for determining whether or not someones stated identity is valid?
That’s exactly what happened.
They also set up the premise that we can pick and choose what sex we are and everybody has to agree with it or else.
No, it’s a “him”.
Pronounces are defined by your biological sex.
Your biological sex is not defined by what you want to be genius.
Some common sense would be to use a common spelling and punctuation checker, and to get with the times, genius.
I don’t care if SHE calls herself an onion. That is a man.
That is a person who has been charged with a serious crime. The crime is the important part here.
This whole subthread needs moderation
“Insider” and accessed WAF… Was it an AWS WAF? Standardized admin creds left exposed by AWS?
Likely they used the default creds for the Technical-Magic-AWS-WAF-Role account to create a NAT to an internal resource (DB or server etc…) then just escalate from there.
https://aws.amazon.com/solutions/aws-waf-security-automations/
AWS is not responsible for securing WAF credentials. That responsibility lies with Capital One.
So is this really a man who thinks he is a she now? Asking seriously as it looks like there is another persona used in the past where she was posting as a man? Also, was this yet another “misconfigured” S3 bucket or did Erratic use default credentials to access the data? Makes a huge difference in legalities. Either way you can’t let Capital One off the hook here, they obviously are not following a standard such as CIS for security configuration of AWS resources. They are heavily to blame.
Nobody, least of all me, is letting CapOne off the hook. This story is based on information that can be backed up with evidence. I am sure we will learn more about the exact “how” of this breach in the days ahead. Stay tuned.
Brian,
Until the mental health issues get used as a defense, I don’t see how it is relevant to the case. It has become a distraction for some.
I suggest consideration for moderating comment threads that focus on gender identity or mental health… and removing the reference from the article.
Thanks.
You’re such a hall monitor.
Correct. There’s certainly a mental health component to this story, but I haven’t seen that even mentioned in most US-based reporting. Leave it to the Daily Mail UK to reveal this: “A Seattle-based transgender former Amazon engineer has been arrested for allegedly hacking Capital One bank’s systems to steal data it was storing on Amazon’s Web Services cloud.”
My first thoughts after reading this were to “throw the book” at her then I calmed down and thought about her mental state and associated issues that you touched on Brian. It’s not quite the same but similar to what we see with mass shootings these recent years mental health and societal adjustment often times are catalysts that ultimately end in physical harm to the individual and sadly innocent bystanders. With more of our lives and future well-being tied up in the form of electrons perhaps it is time for a corporate discussion on employees who have sensitive access, like this woman did, to be to be scrutinized more closely and provided tools/support to handle mental health issues. It could save a corporation a breach in the future. I am, of course, also interested in the details of potentially poor practices that Capital One has continued up until now that is. Great reporting as always BK.
So what if the he is a transgender and had mental health issues ( transgenerism IS a mental disorder, IMO)? How is that related to an obvious history of data theft and knowlingly exfiltrating user data from Capital One customers and why should they be treated differently than any other criminal?
Lots of people have mental disorders, none of which excuse felony data theft.
Uh oh, get ready for the right wing anti-transgender opinion leakage. Up front: no transgender cares what you think of them.
Firstly, gender dysphoria IS a real mental health issue, and like many others, like depression in the elderly, anxiety in youth, PTSD in veterans, and white male stress at work, our country needs to treat all of these with much more compassion and understanding than we do now because mental health is important OS level software and all political alignments in America are perversely hardware-oriented.
That said, from a technical standpoint someone pointed out that gender identity issues kind of DOES present a security risk because this person could likely have one or more prior aliases that need to be researched.
I also shot an email off to Unicredit to let them know they’re about to have a bad day.
Having multiple aliases to look out for… is a product of being in IT. Nothing to do with gender identity.
Every hacker will have multiple identities. Even straight males, could easily have female personas for one reason or another.
she cared very much about what people thought of her. VERY much.
http://irclogger.arpnetworks.com/irclogger_log/arpnetworks/?date=2018-03-16,Fri
Fortunately the scientific community, including the World Health Organization, the American Psychological Association, as well as a better defined DSM-V don’t care what your personal opinion is on transgender identity being a mental disorder (newsflash: they aren’t mutually inclusive).
Should have just stuck with the less controversial (although still controversial) point that mental health issues don’t excuse crime.
It’s cute that you think being trans is a mental disorder. Well, not cute so much as just flat out wrong (at least according to the AMA and medical science as a whole).
Also, you’re low key contributing to a mindset which results in the brutal physical assaults and murders of trans people. Maybe reconsider
I spend my days developing insider threat products, and my perspective:
From the POV of threat modeling, it matters not if someone is mentally ill or not. The math doesn’t care. One of the models I’ve been working on includes a lot of personality and behavioral characteristics, some of which are mental illnesses — for example, alcoholism — and some aren’t (divorce and bankruptcy).
If something is indicative of elevated risk of being an insider threat, it’ll be included in the model, illness or not. And that’s the way it should be. It’s not a judgment, it’s just the math.
The question is: does being transgendered indicate an elevated risk of bad behavior? Personally I can’t answer that, as I’ve not done the analysis. But that’s the question. Mental illness or not? Irrelevant. The conditions that a transgendered person faces in society? Only relevant insofar as it affects behavior.
The detection of inside threats has nothing to do with intersectionality, so far as I can tell.
Another thread that is a distraction from the primary conversation regarding the actual crime that should be moderated
If you dont think mental health can “excuse” a crime, then you need mental help as you clearly don’t get it and think you do.
Did they not change their web application firewall credentials when she left the company?
that was my thought
why weren’t credentials changed after her departure?
Sean,
Proper use of an IAM policy would have a unique key for each user instead of a system IAM. You would simply revoke her IAM.
System IAM access like Windows system accounts are bad… very bad. I would guess this is what she did.
Reading the complaint it sounds like she had a way to extract the credentials from some server behind the WAF due to a misconfiguration.
Any idea what other companies were targeted? So far only CapOne has been discussed.
You may wish to take a closer look at the screenshots above.
so sad
alexa play despacito
“Suicidal tendencies” and issues with her “gender identity”. Yep, that’s just the type of person I want guarding the keys to the kingdom.
Put her in a cell with Jeffrey Epstein and maybe they’ll kill each other.
No, we REALLY want Epstein to go to trial, and for him to reveal all of what he knows. We want those in his “rolodex” to be brought to account, no matter who they are, no matter where they are.
I’m not sure a policy of murdering suspects before trial is a sound bases for our democracy.
There are alot of assumptions right now. There are many WAF products available in AWS, not just the AWS WAF. If she was able to use credentials to log in to the WAF when she was employed, and protections weren’t put in place, then its entirely possible that she was able to get admin usernames/passwords from the logs on the WAF. The admin creds likely would not have been changed when she left.
Granted this is all speculation right now, but I’ve been reading AWS SOC2 reports for years and wil be to learn that they aren’t rotating admin credentials. Thompson hasn’t worked there for 3 years.
Isn’t it really stupid to post the methods she used to hack? Others can try to do the same thing on other servers.
No – it’s not really stupid to go into detail on the attack method. It’s really smart. We need more of it. And the argument about this kind of stuff is more than 160 years old. I’ll post a link to a talk I gave about this very topic in another comment.
Well, what the heck – I’ll paste it in here too.
https://www.dgregscott.com/a-radical-not-so-new-idea-to-stop-the-daily-barrage-of-data-breaches/
– Greg
Yes, Erratic did bad things and needs to be held accountable, but it seems like we are letting CapOne off the hook and ignoring AWS in terms of accountability.
CapOne will likely pay financially for this breach, but so what? They have a lot of money and have likely factored the cost into their risk management strategy.
AWS won’t pay at all. Even though they market “shared responsibility” for security control in their environment, they don’t take responsibility for breaches in their environment. I’m a bit frustrated that AWS is suffering no real consequences despite breach after breach.
Privacy is a real thing. Consumers need to step up and vote both with their dollars and at and the ballet box.
I don’t like the ballet – do I have to vote there?
Are you a CapOne emeployee? Do you work for AWS?
There, I can be toxic too.
Why would your questions be considered “toxic?”
I don’t work for either organization.
So if …
1. Ford sells me a car that can only be operated with an ignition key
2. I lose those keys
3. Someone finds those keys and steals my car, and
4. Hits someone with it, killing them ….
Ford’s responsible for the hit and run?
No, and rope makers are not responsible for rape or suicides either. But, since amazon has “shared responsibility” with these servers, they should be held responsible for allowing an ex-employee credentials and securing basic e3 buckets and ec2 servers
Every criminal can claim ‘mental health issues.’ She can have time to heal serving her sentence. Every murderer says they had a bad child hood, but no mention of the victim. She is malicious with her intent and doesn’t care how many lives she causes serious problems to. Identity theft can cause lots of serious trouble for us.
I don’t see anywhere, that the accused is attempting to use mental health issues as an excuse for the crime.
All we know is she brokedown in court and put her head on the table. A common response to conviction…. regardless of mental health issues.
This article only mentions her previous struggles because it was also mentioned in the same social media posts.
But it isn’t being used as a defense.
Great cyber-security article as usual !
To the people associating her gender identity and mental health struggles with some sort of proclivity to do crime: shame on you. Seriously, is this the 19th century? Grow up.
God, the infosec community is so toxic and sexist. Who are any of you to judge this person’s struggles or identity, and then make baseless associations with her decision to break the law?
Stay in your lane (which is not psychology), don’t throw stones from glass houses and consider being a better person.
Agreed.
There are plenty of good (white and grey hats) transgender people in infosec. Sandboxescaper comes to mind.
Yet, bigots love to draw conclusions and make assertions based on what they personally find offensive.
To Bonnie,
I don’t think so…. Now that it is out in the open and “in the wild” hopefully this particular hack hopefully will be guarded against.
I am getting really tired of reading about s3 data being exposed though…
From a ZDnet(dot) com article posted today it states
“It further states that Capital One verified Thompson had a list of over 700 of its buckets, and the bank’s logs showed attempted connections from Tor exit nodes that matched an IP address which made irregular use of a firewall account to list buckets. Other commands were also made from IP addresses that belonged to a VPN provider that Thompson is a customer of, the US alleges. “
Capital One customer here ; thank you, Brian, for keeping us informed. You’re the best!
Story keeps getting crazier: when the feds searched her residence, they found a cache of firearms that belonged to her landlord. He was arrested as well because prior felony convictions (for possessing a machine gun and a failed contract murder using a truck bomb) prohibit him from owning guns.
https://www.seattletimes.com/business/seattle-woman-arrested-in-breach-of-capital-one-systems-millions-of-credit-applications/
Brian- great reporting as always – Thank you !
Scott Schober
http://www.ScottSchober.com
Data breaches are just one consequence of corporate attempts to increase profit. The cloud concept was a way to save costs relating to data storage. They were fully aware of the potential dangers associated with having data stored in this manner. Those of us who are now fighting to protect ourselves from complete financial ruin will not accept credit monitoring as restitution. It’s laughable that Experian, Capitol One and others intend to offer credit monitoring and call it good. No, not good. Not good at all.
Well.. everyone saves money with distributed computing.
With the cloud… Krebs might not be able to work. Do you think he’s self hosting?
We might not even have a comment section either.
There are probably a dozen ways you personally save money online thanks to cloud services. Yeah, banks and other demonized corporate entities save money too… but really, the existence of the cloud isn’t the cause of your woes.
I’m sorry, but before actually reading the article and only seeing the picture, I wasn’t sure if the person was a man or woman. To me it looks like a man dressed like a woman. Either way, a crime is a crime for s/he.
Eagle II is a $22 Billion DHS cloud migration project for ICE and TSA. It was supposed to be complete in 2020. But this new RFI (pdf bottom of link) shows that only 5% is complete. This RFI infers there may be issues or doubt with cloud security and migration business continuity. It wants private sector examples of private cloud instances with Zero Trust.
https://www.fbo.gov/index?s=opportunity&mode=form&id=41018c3571e93d8339e5c3349d5bc7c9&tab=core&_cview=0
I hope she makes it through her sentence ok and goes straight. Some great security careers have started with a short jail sentence, and we need more good guys!
That seems highly unlikely.
In the good old days, back when hacks were mostly about curiosity and proving you could do it, that kind of thing happened. Think Kevin Mitnick; you can question the wisdom of what he did, but at the base he stole some source code, looked at it for his own edification. There was never an attempt to hurt people.
Today is different. Today the main objective is to hurt people. On Twitter she said “I’ve basically strapped myself with a bomb vest, fucking dropping capitol ones dox and admitting it. I wanna distribute those buckets i think first. There ssns… with full name and dob.”
This wasn’t curiosity: this was an attempt to lash out, to harm.
Yes, she’ll have an opportunity to see the error in her ways. But I’d be very, very surprised if she availed herself to it.
I don’t care about her problems, just like she doesn’t care about my personal information. Lock her up. If she commits suicide she’ll have done us all a favor.
People that do these and similar thing often get caught because they don’t know to keep their mouths shut. Slam dunk, one for our side!
Lock this nut job (Paige Thompson) up
https://arstechnica.com/information-technology/2019/07/feds-former-cloud-worker-hacks-into-capital-one-and-takes-data-for-106-million-people/
While mental health issues may have prevented this person from knowing the difference between right and wrong, that fact remains that he/she and others who commit these crimes need to be segragated from the rest of society. Detention with no access to the rest of the world is necessary for the protection of humankind.
Huh? Not that kind of mental health issue.
Suicidal thoughts are very common regardless of gender dysphoria.
And 99% of mental health issues are not even remotely in the ballpark of “not knowing right from wrong”.
You may be thinking specifically of sociopaths. But that is not the case here.
That’s a man, baby!
Yep.