The cybercriminals behind the GandCrab ransomware-as-a-service (RaaS) offering recently announced they were closing up shop and retiring after having allegedly earned more than $2 billion in extortion payments from victims. But a growing body of evidence suggests the GandCrab team have instead quietly regrouped behind a more exclusive and advanced ransomware program known variously as “REvil,” “Sodin,” and “Sodinokibi.”
“We are getting a well-deserved retirement,” the GandCrab administrator(s) wrote in their farewell message on May 31. “We are a living proof that you can do evil and get off scot-free.”
However, it now appears the GandCrab team had already begun preparations to re-brand under a far more private ransomware-as-a-service offering months before their official “retirement.”
In late April, researchers at Cisco Talos spotted a new ransomware strain dubbed Sodinokibi that was used to deploy GandCrab, which encrypts files on infected systems unless and until the victim pays the demanded sum. A month later, GandCrab would announce its closure.
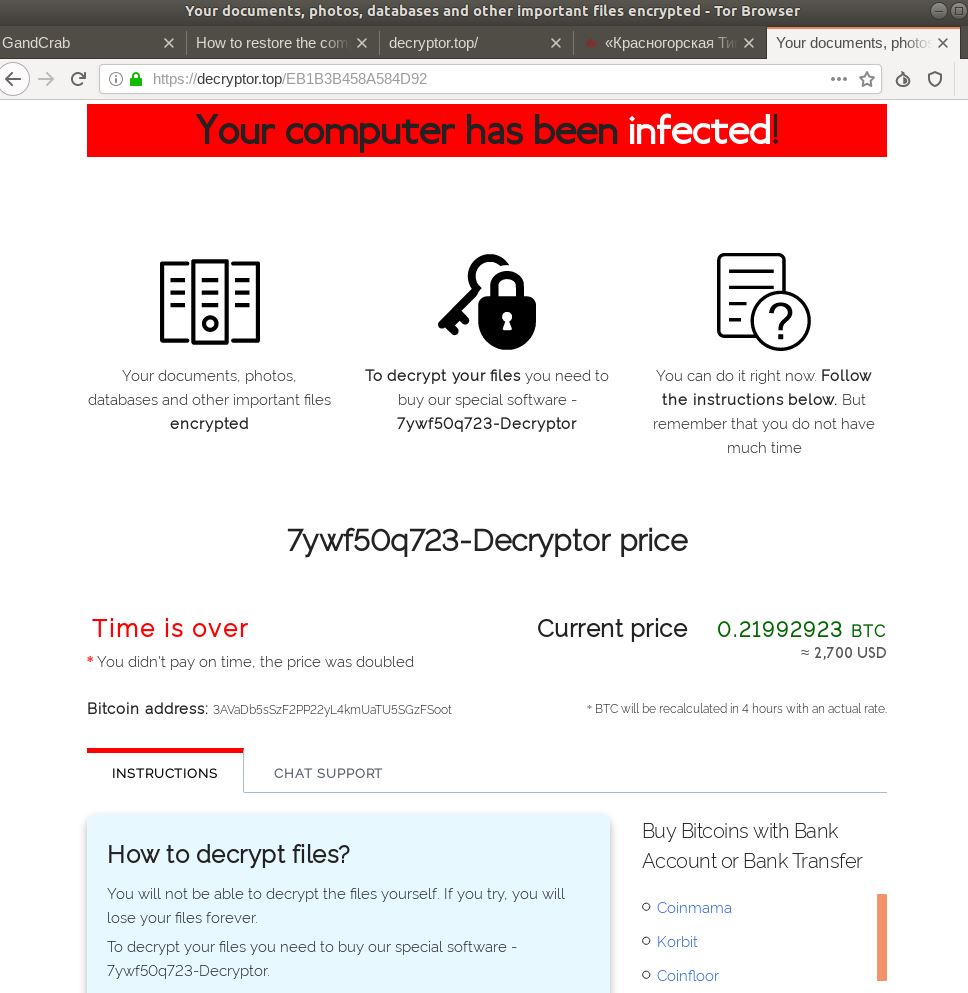
A payment page for a victim of REvil, a.k.a. Sodin and Sodinokibi.
Meanwhile, in the first half of May an individual using the nickname “Unknown” began making deposits totaling more than USD $130,000 worth of virtual currencies on two top cybercrime forums. The down payments were meant to demonstrate the actor meant business in his offer to hire just a handful of affiliates to drive a new, as-yet unnamed ransomware-as-a-service offering.
“We are not going to hire as many people as possible,” Unknown told forum members in announcing the new RaaS program. “Five affiliates more can join the program and then we’ll go under the radar. Each affiliate is guaranteed USD 10,000. Your cut is 60 percent at the beginning and 70 percent after the first three payments are made. Five affiliates are guaranteed [USD] 50,000 in total. We have been working for several years, specifically five years in this field. We are interested in professionals.”
Asked by forum members to name the ransomware service, Unknown said it had been mentioned in media reports but that he wouldn’t be disclosing technical details of the program or its name for the time being.
Unknown said it was forbidden to install the new ransomware strain on any computers in the Commonwealth of Independent States (CIS), which includes Armenia, Belarus, Kazakhstan, Kyrgyzstan, Moldova, Russia, Tajikistan, Turkmenistan, Ukraine and Uzbekistan.
The prohibition against spreading malware in CIS countries has long been a staple of various pay-per-install affiliate programs that are operated by crooks residing in those nations. The idea here is not to attract attention from local law enforcement responding to victim complaints (and/or perhaps to stay off the radar of tax authorities and extortionists in their hometowns).
But Kaspersky Lab discovered that Sodinokobi/REvil also includes one other nation on its list of countries that affiliates should avoid infecting: Syria. Interestingly, latter versions of GandCrab took the same unusual step.
What’s the significance of the Syria connection? In October 2018, a Syrian man tweeted that he had lost access to all pictures of his deceased children after his computer got infected with GandCrab.
“They want 600 dollars to give me back my children, that’s what they’ve done, they’ve taken my boys away from me for a some filthy money,” the victim wrote. “How can I pay them 600 dollars if I barely have enough money to put food on the table for me and my wife?”
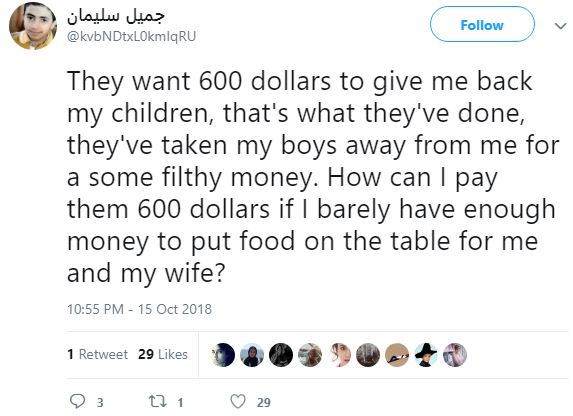
That heartfelt appeal apparently struck a chord with the developer(s) of GandCrab, who soon after released a decryption key that let all GandCrab victims in Syria unlock their files for free.
But this rare display of mercy probably cost the GandCrab administrators and its affiliates a pretty penny. That’s because a week after GandCrab released decryption keys for all victims in Syria, the No More Ransom project released a free GandCrab decryption tool developed by Romanian police in collaboration with law enforcement offices from a number of countries and security firm Bitdefender.
The GandCrab operators later told affiliates that the release of the decryption keys for Syrian victims allowed the entropy used by the random number generator for the ransomware’s master key to be calculated. Approximately 24 hours after NoMoreRansom released its free tool, the GandCrab team shipped an update that rendered it unable to decrypt files.
There are also similarities between the ways that both GandCrab and REvil generate URLs that are used as part of the infection process, according a recent report from Dutch security firm Tesorion.
“Even though the code bases differ significantly, the lists of strings that are used to generate the URLs are very similar (although not identical), and there are some striking similarities in how this specific part of the code works, e.g., in the somewhat far-fetched way that the random length of the filename is repeatedly recalculated,” Tesorion observed.
My guess is the GandCrab team has not retired, and has simply regrouped and re-branded due to the significant amount of attention from security researchers and law enforcement investigators. It seems highly unlikely that such a successful group of cybercriminals would just walk away from such an insanely profitable enterprise.




If only there really was some sort of “magic e-bullet” for such maleficent cretins.
The magic bullet is simple. Do your backups regularly and keep them secure. If you get hit, just wipe and restore. I am stunned by the number of large institutions that don’t seem to get this. Maybe I am just weird but I keep backups of full server images for 18 months and data files for 5 years and in multiple locations that include clouds and fire safes in 3 different zip codes.
Mike, that’s sage advice for protecting data. (And no, you’re not weird! )
But your solution doesn’t address what happens when critical operations (e.g., health care facilities, first responders) are hit and their systems are totally frozen.
Even if victims pay immediately and receive the decryption code immediately, it can still take hours and even days to restore full operations. In life-and-death situations, that’s deadly.
Hopefully, at some point, law enforcement will have some success in capturing some of these crooks (I’m using gentle language here) and giving them the ultimate sentence: life in maximum security with NO computer or internet access.
no, thats the point of backups. Not outdated file based backups but BDR solutions that can spin up virtual systems within minutes.
Exactly. An effective and well tested Business Continuity / Disaster Recovery strategy will indeed restore operations within minutes. On premise, or in the cloud.
VEEAM correctly configured can get you back up in minutes, hours at most..
I always thought if you had good backups you were fairly safe, but some are saying it wasn’t as simple as you put it. If its a case of just having good backups, why don’t most companies implement better backup strategy ?
Restoring dozens or hundreds of servers from backup is not always an easy nor a quick task. It is absolutely preferable to paying a ransom, but that does not mean that the attack has no effect on you. It still presents a major undertaking to get everything cleaned and restored and can still cost your business quite a lot of money.
Also, “better backup strategy” means more money invested in IT. For local municipalities and SMB’s, this is often money they dont have. Sometimes, the security issues at companies are due to bad management, but its also just as common the result of lack of funding. Enterprise level security tools are expensive, REALLY expensive. As in a proper security stack for a company with less than 1000 endpoints can cost more than $100,000 per year in ongoing license fees. Or more. An entry level SIEM solution alone from IBM is $60,000 per year or more, and that’s just a single tool.
This is probably a really stupid question (so please forgive me), but wouldn’t virtual drives help? For example, if one user got infected and the ransomware spread to 99 other people, if those 100 people all were using the same shared virtual drive, couldn’t you just restore the virtual drive and once the users reboot, they’ll be good? Realistically, a virtual drive is just carved out from some form of RAID (hopefully RAID 5 or RAID 6 for redundancy), and I would imagine you could just rip and replace and let the RAID group rebuild — but again, I’m not entirely sure. It just seems that would be feasible in my opinion.
Not if they can gain access to the underlying volume that virtual drive is stored on, at which point they encrypt that volume. It’s a little more complicated than that because in-use files typically can’t be altered if they’re locked by a process (as is typically the case with a virtual drive), although it can encrypt all the surrounding files on the volume.
Backups are how you combat ransomware but the key part I think nobody has mentioned is that you have to have offline backups. So many backup systems today are geared towards always having access to the sole backup method available, so they just mount the volume it uses, encrypt it, and voila, all your backups are gone. Cloud backup doesn’t really help you unless you’ve paid extra for the cloud provider to be able to roll your storage back to an earlier state – this typically isn’t free. DropBox, Google Drive, etc. aren’t backup systems because if I encrypt your computer I can also encrypt Google Drive and at that point both your computer and your backup are encrypted. If you had an older backup on a drive that hadn’t been connected in a week, two weeks, two months, etc. then you’re mostly safe from ransomware (important to restore to a time before the first penetration), at least for whatever systems that backup is protecting.
Personally I have a fairly hardened network that doesn’t allow any executables to run from within the user’s folder and none of the users are administrators. Downside to this method is spotify, etc. don’t work because they stupidly install to the user’s appdata folder and won’t install anywhere else. So expect great cries of woe to come up from users who’ve grown accustomed to abusing their internet connection. BTW, while you can whitelist spotify, their update process runs from %temp% and of course that’s the one folder you absolutely don’t want to give executable privileges to, so it’ll work for a little while after you whitelist then never update until it stops working.
Hello SeymourB, thank you for the insight! That definitely makes sense to me. Also, I had no idea Spotify was installed / run like that. That seems strange to me. A lot of Anti-Virus or even IDS’s have IOCs that search specifically for programs that execute out of %TEMP%. That’s weird, I wonder what their reasoning behind that was.
One nice aporoach, if a bit slow, is AWS Glacier: No way to access the tapes for a few hours, even if the malwsre tries to delete them.
Also tecall that you need separate, offline backups of recovery certs & deciphering keys! Enciphered offline backups are useless if they are inaccessable or not deciphersble… ouch.
A number of things, really:
1.) A robust backup strategy takes money. When funds are tight, backups can take a backseat to other more (seemingly) pressing concerns.
2.) It takes time to restore from back up. And depending when the last backup was taken, you’ll likely lose some data.
3.) Combining points 1 and 2 (it costs money to backup, and time down is money lost), sometimes it makes most the most financial sense for a company to just give the ransom.
Giving the ransom perpetuates ransomware as a whole, so the societal good states to never give in. But businesses are self-interested. And ransomware hitting hospitals, emergency services, and municipalities poses serious and dire threats to public health.
Backup doesn’t do you any good if the backup is infected or you have a weakness in your system that an attacker was able to make use of.
Nor do many backup solutions (especially older ones) employ the separation that keeps backups from being corrupted by the same ransomware. Such separation makes a backup process slower and adds friction, which makes it difficult or impossible to use in scenarios where frequent or continuous backup is required.
One reason backups don’t provide the protection as described is many ransomware infections are on the network for days or weeks before encryption begins. If you restore servers to the day before encryption, you are also restoring the infection.
A recovery is more complicated than performing full system restores.
Quite right. I do regular backups and keep all them for as long as I have the media to hold them. But…dumb luck I guess….I’ve never had to use them. Must be a Murphy’s law for this.
Another great article from Krebs !
Anyone else notice that he’s posting this FROM THE FUTURE!?
“JUL 19
Is ‘REvil’ the New GandCrab Ransomware?”
That the month an year. The day is the big ’15’ above ‘Jul 19’
What Sean said. I see this every couple of weeks, you’d think folks would have worked it out by now.
A thought on the addition of Syria to the exclusion list. Maybe that tweet was the initial cause of the decision, but the developers must have been aware that any malware strain that significantly affected Syrian users and could be traced back to Russian authors would be damaging to the Russian military’s efforts to appear to be helpful and obliging to (some at least) of the people of that country. The local military brass would in time have sent signals back home that could have led to some most unwelcome attention from the authorities for the developers. Maybe they had already been advised, unofficially, to provide decryption keys for Syrians – and to do it fast, and for free. In which case, taking the financial hit would have been far better than any of the range of possible alternatives.
Bingo. Russia is virtually running Syria as a colony, at the moment. Any cyber attack on Syria by Russian hackers could stir up problems.
Yep
This situation reminds me of the problem with vaccination and herd cover, as in, if more people had decently secure systems, I. e vaccinated state, there would be too few vectors/carriers, which can lead eventualy to a disease being wiped out.
The problem has nothing to do with back ups, if folk had properly secured systems, they wouldn’t get infected and wouldn’t need to use the back ups, it’s bolting the door after the horse has bolted.
Its the reason I use an old phone running ms winmo 6.5,how many folk/groups are going to waste time/resources attacking such a tiny user base ?
If most folk had properly secure systems, ransom ware would quickly become non-viable, it should be a criminal offence to pay ransom, if fines were 3 times more than ransom, firms would soon improve security.
Greed and laziness on both sides have caused this problem.
You would hope that somewhere there is a multi government and industry group discussing how to build a properly secure Internet 3,without all the compromises and cock ups that allow so much criminal activity, that is far more efficient, more secure and is the opposite of the bodged systems we have now because nobody thought the problems through from the very begining.
Its interesting wondering what somebody like Geoffrey Pyke, of habbakuk ice ship fame, would have done if he had been alive at the begining of the digitaly connected world and how different the world might be !!
The problem with the “properly secured system” is that for all practical purposes, it does not exists. Especially in corporate environment, with all the legacy OS and apps.
Even if both the OS and apps are the latest and up to date with patches, the system is only secure against known vulnerabilities.
Augmenting protection for the “not-so-secure-software” can be costly as others eluded to it. Even then, there’s still the human factor that can override the system, weather it is intentional/unintentional.
HTML 5 was supposed to address some of these issues, but in some respect, it made thing worse. I don’t believe the Internet 3 will do better, but it does not prevent me from hoping…
Another thing that made at least the latter versions of GandCrab so insidious is that they did absolutely nothing to your system that was in any way abnormal until it triggered a pre-startup drive encryption operation.
We had one machine that was infected, and no anti-malware or anti-virus software we tried could detect the infection, before or after the encryption.
Our best guess was that an IT related tool by a small company had been compromised, given the timing of the attack, but that is only a guess. Nothing could be confirmed.
So what do you do to secure your systems? The system was up to date, anti-virus and anti-malware were installed and up to date, and all software installed was legitimate. There isn’t much else you can do to protect yourself, other than perhaps trust small software developers even less. But even then, we don’t know that that was the attack vector, it just seems the most likely.
Fortunately, we had a good backup system in place, and the impact to the company was minimal. It did scare the beegeezus out of everyone, especially since we never got that “Aha! This is the cause!” revelation. Everyone was on pins and needles, afraid to restart their machines for fear of the encryption, while we slowly confirmed one by one that only the one machine was affected.
So if the local authorities don’t recognize it as a crime, and since this ransomware is clearly made to target Western countries, can we send them our GBU-57A/B to the hole they are in?
It’s not that the local authorities don’t recognize it as a crime, it’s that they have no incentive to pursue it. They aren’t doing damage to the local population, and the external damage is just not significant enough to harm international relations in any meaningful way. This is especially true because nobody really knows where the creators of this malware are located.
There is nobody in Kazakhstan calling Kazakhstani police saying “I’ve been hacked!”, and then when the police look into it low and behold, the hacker is a fellow Kazakhstani who can be arrested and tried immediately.
Instead, you’ve got a Spaniard calling Spanish police saying “I’ve been hacked!”, and when the police look into it, it turns out the hacker is in Armenia. The Spanish police can’t just go arrest the hacker. They’ve got to negotiate with the Armenians for extradition, and when the crime is for something like $3,000 or less it’s just not worth it for the Armenians OR the Spanish to put any effort into pursuing it.
It’s not until there are hundreds or thousands of these cases, adding up to tens of millions of dollars in damages, that the damaged nation (Spain in this example) will find it worthwhile to put strong pressure on the attacker’s home country (Armenia, in this example).
That’s also the beauty of the affiliate program. Because they sell affiliate rights, the attacks no longer come from one country, but dozens of countries. It spreads the source of the damage out, diffusing it and reducing the rate at which the pressure builds for any given country to “do something about it”. That magnifies the amount of pressure required to build up before they are in any real danger.
As long as the original creators are smart and don’t commit any attacks themselves, leaving it all up to the affiliates, and as long as they convince their affiliate partners to not attack the CIS countries they are selling this malware to, the target countries will almost be required to focus on everyone except the creators of the ransomware, even if they would like to target the creators.
That’s also likely why GandCrab was retired – the pressure was building to the point where their host country might actually be convinced to do something about them. By dropping the malware, the host country can say “See? It’s not a problem any more, we don’t need to deal with this.” Because to the host country, the only thing that would make it worth prosecuting is their relationship with other countries. Something like this, cut off at the right time, is just not on the level to cause them problems internationally.
So it probably is on law enforcement’s radar in CIS countries, but it’s going to be real low priority to catch them. There just isn’t a reason to pursue it.
Ban Crypto Currencies that are anonymous. As soon as people start to evade taxes using zcash or monero, you’ll see governments ban any that don’t allow it to trace the transaction to an exchange.
I’m surprised the environmentalist movement isn’t more interested in the massive amounts of energy being wasted on crypto currencies. (1).
Between that and its utility for cybercrimes, some regulation of the industry — fueled almost exclusively by Chinese-made machines — may be warranted.
(1) https://www.wired.com/story/bitcoins-climate-impact-global-cures-local/
Or, google “crypto currency global warming.”
ban urself from webz, lol idiot
And how do you propose they do this? Say “You’re not allowed to use cryptocurrency!”? How well did saying “You’re not allowed to encrypt other people’s data!” work?
No, you would simply tax any movement of traditional currencies into or out of cryptocurrencies at a higher rate than bonds, commodities, stocks, and foreign currencies. And change financial reporting requirements to include cryptocurrencies.
Aside from a handful of legal businesses accepting cryptocurrencies as payment, the crypto industry is largely speculative investment with quick returns. It’s very similar to Ponzi schemes, where it’s largely greedy fools holding up the entire thing, so that cyber thieves can walk away with cash..
There’s very little involvement with this stuff by long-term investors or ordinary people doing ordinary transactions. No major investment company touches cryptocurrencies and it’s seen as a get-rich-quick gimmick only. Any barrier to its use, in the form of taxation or regulation, would effectively kill that market, by making traditional investments more attractive.
You can also limit the import of Chinese GPUs, which raises the cost of running crypto farms.
And charge higher rates for electricity to server mining farms, which can only find profit off cheap energy. They’d be very easy to detect, because of constant energy use at all hours in small buildings.
I should add that I would rather see traditional investments made easier and less expensive. Reducing the hassle and cost of using real money would also kill alternatives.
I have found a decryptor.top link that someone has already paid for. It has the decryption tool available to download. I also have a local copy. Contact via email for more info:
PGP: 51F5 CC26 A523 96FC
As I’ve said many times – use the Microsoft Management Control (MMC), along with Active Directory settings to configure all protections against unauthorized encryption. If your IT people don’t know how to do it, at least buy something like CryptoPrevent, Cybereason RansomFree, Malwarebytes Anti-Ramsomware or a better competitor, and be done with it. Of course larger concerns will want an Enterprise solution. I do not work for any of these companies, I just look for solutions – anything to foil the bad guys. PC Magazine has a good article testing one of these, but it is dated 2017, so I’d tint my decisions based on that.
Unfortunately managing the cryptography aspect is not always going to work. A lot of these ransomware utilize open source libraries or custom implementations. All of which MMC and AD have no control over.
Brian Krebs points to the idea that REvil is the new GrandCrab Ransomware which is logical. This misdirection would seem like a classic move by malware makers to perpetuate their business via re-branding of the name of their malware and some code modifications.
I got a slightly different picture of the REvil and GrandCrab actual infection vector by reading Bleeping Computer. The infection started by first infecting Managed Service Providers [MSP] via Remote Admin Management consoles and then infecting other company’s machines. Thus, said customers of Managed Service Providers probably know little about backups and security – since they are outsource their security to MSPs. Maybe, the MSPs should have read Brian Krebs ‘Spam Nation’?
“Sodinokibi Ransomware Spreads Wide via Hacked MSPs, Sites, and Spam”
https://www.bleepingcomputer[.]com/news/security/sodinokibi-ransomware-spreads-wide-via-hacked-msps-sites-and-spam/
“Ransomware Attacks Target MSPs to Mass-Infect Customers”
https://www.bleepingcomputer[.]com/news/security/ransomware-attacks-target-msps-to-mass-infect-customers/
It would be a shame if someone joined the program and went ahead and distributed the malware in the excluded countries, inviting the interest of the local authorities.
Would you even need to join the affiliate program? The affiliate program is for managing the keys for encryption/decryption.
This this case, you would not care about managing decryption. Just proxy forward the payload with a well crafted phishing message to people in Russian and CIS countries. Proxy forward the command and control exchanges. And watch the fireworks.
The decryption keys would be quickly released.
Now THAT would be quite a strategy, albeit one that would be “patched” quickly. Unfortunately, even though you’d be able to unleash the fiery wraith of Lenin upon those GC bastards, you’d also be infecting innocents… and that’s a no-go.
Or just set up honeypots on servers in those countries, or VPN through them. Infect your own honeypots, then launch complaints as locals.
Wouldn’t they require photos of one’s mother in a compromising position, before allowing a stranger to join?
Why not just take a copy of their software off an infected system, duplicate it on flash drives in bulk, then leave it on city transit vehicles in CIS?
https://nakedsecurity.sophos.com/2016/04/08/almost-half-of-dropped-usb-sticks-will-get-plugged-in/
1. Backups
2. Disaster Recovery
3. Knowledge
These will keep you safe.
Proper implementation of the concept of least privilege would go a long way towards protecting against ransomware. Backups performed by a dedicated account that can only read live data and is the only account able to write to backup media help prevent backup from being completely encrypted.
Unfortunately, least privilege is rarely implemented even in some of the more “secure” implementations. If you can read and write data almost anywhere, and particularly for ransomware, in any data area; then you are not in a least privilege state. If you can install or run uninstalled/unregistered apps, then you are not in a least privileged state. Hint: malware is not installed/registered.
For the enterprise, the resources are there to implement least privilege. Even adminstrators should not have admin rights on their day to day accounts they use for email and internet access. It’s just more convenient to have admin rights all the time.
For the small business and home user, the administrator is usually somebody who needs help in the least privilege area, that falls on the OS developers to provide. Windows only began doing so minimally in Vista, it is better but still focuses on convenience. Linux started much earlier, but convenience is creeping in. I do not know Mac. Things can be improved in this area “out of the box”
If people took lradt priv’s seriously we’d still be running VMS.
Clue: We aren’t.
Speed, price, & supposed convienence take the day.
I agree Krebs. These crooks are smart, and in a 3rd world country in eastern europe, the cost of bribes is in the millions so if they’re making tens and hundreds of millions, there is no way they retire and walk away.
They have rebranded, possibly moved, changed a few team members. The quote that stuck out the most:
“When asked by members of the forum what projects they worked on, they responded “we have been in many media reports” so their operational security is a concern for them. Definitely the same guys.
This is why I still use an Apple IIe.
(Now where did I put that number muchers floppy?)
+1 Anonnnnn July 16, 2019 at 7:42 am
That is a creative idea! It would be nice to strike back at some of these countries that protect ransomware makers and users.
Taking it one step further, I wonder if there are a few sketchy Managed Service Providers in Russia who would actually scam their own customers with ransomware – I am sure there are MSPs in the states who would do if to for a few dollars more. But, thinking about it – tangential problems could occurs as Leo notes.
To Leo, “…you’d be able to unleash the fiery wraith of Lenin upon those GC bastards, you’d also be infecting innocents… and that’s a no-go.”
Yes, that is very true.
and
To Joe, “…just set up honeypots on servers in those countries, or VPN through them. Infect your own honeypots, then launch complaints as locals.”
That is an interesting devilish idea. It would be fun but may have unintended consequences.
Some customers of MSPs or CSPs don’t fully grasp the power of Administrator/root privileges due to poor or zero IT training. In their zeal to expand their business or build a “cloud solution” they give away powerful Admin/root privilages to un-tested and unknown MSPs/CSPs. That is bad policy.
Brian Krebs has tried to point out the necessity of vetting and control MSP or Customer Service Providers who have Administrative /Root access – to other peoples sensitive files. Brian Krebs has pointed to that fact in his “Microsoft to Require Multi-Factor Authentication for Cloud Solution Providers” post:
“…When an organization buys Office365 licenses from a reseller partner, the partner is granted administrative privileges in order to help the organization set up the tenant and establish the initial administrator account. Microsoft says customers can remove that administrative access if they don’t want or need the partner to have access after the initial setup…companies partner with a CSP simply to gain more favorable pricing on software licenses — not necessarily to have someone help manage their Azure/O365 systems. And those entities are more likely to be unaware that just by virtue of that partnership they are giving someone at their CSP (or perhaps even outside contractors working for the CSP) full access to all of their organization’s email and files stored in the cloud…”- Brian Krebs.
https://krebsonsecurity.com/2019/06/microsoft-to-require-multi-factor-authentication-for-cloud-solution-providers/
Being an “Administrator or Root” is a very potent IT roll that should be carefully doled out.
Most companies who want to grow fast or scale-out quickly should be extremely careful to properly investigate their MSPs or CSPs for integrity, actual track record, moral-character, before handing said MSPs the keys to the kingdom when setting up a cloud solution. Carelessly giving ‘Administrative or Root’ privileges to un-tested MSPs could cause breaches or ransomed crypto-locked data for years into the future.
How about just tracking down this scum and hang them in the public square.
Solution: Do regular full secure system backups, if possible at multiple locations and make some offline so as soon as you get hit, completely wipe all your infected systems and restore…
Train employees on fishing attacks.
Employ competent IT security staff and heavily filter emails and restrict emails to company domains only, allow only users who are required to email other domains for work purposes to be able to do so.
We know someone who was attacked by Sodinokibi and they had a well known anti-virus program and the AV folks have no idea how it got in. Brian – How does this thing get onto the computer?