For at least the past decade, a computer crook variously known as “Yalishanda,” “Downlow” and “Stas_vl” has run one of the most popular “bulletproof” Web hosting services catering to a vast array of phishing sites, cybercrime forums and malware download servers. What follows are a series of clues that point to the likely real-life identity of a Russian man who appears responsible for enabling a ridiculous amount of cybercriminal activity on the Internet today.

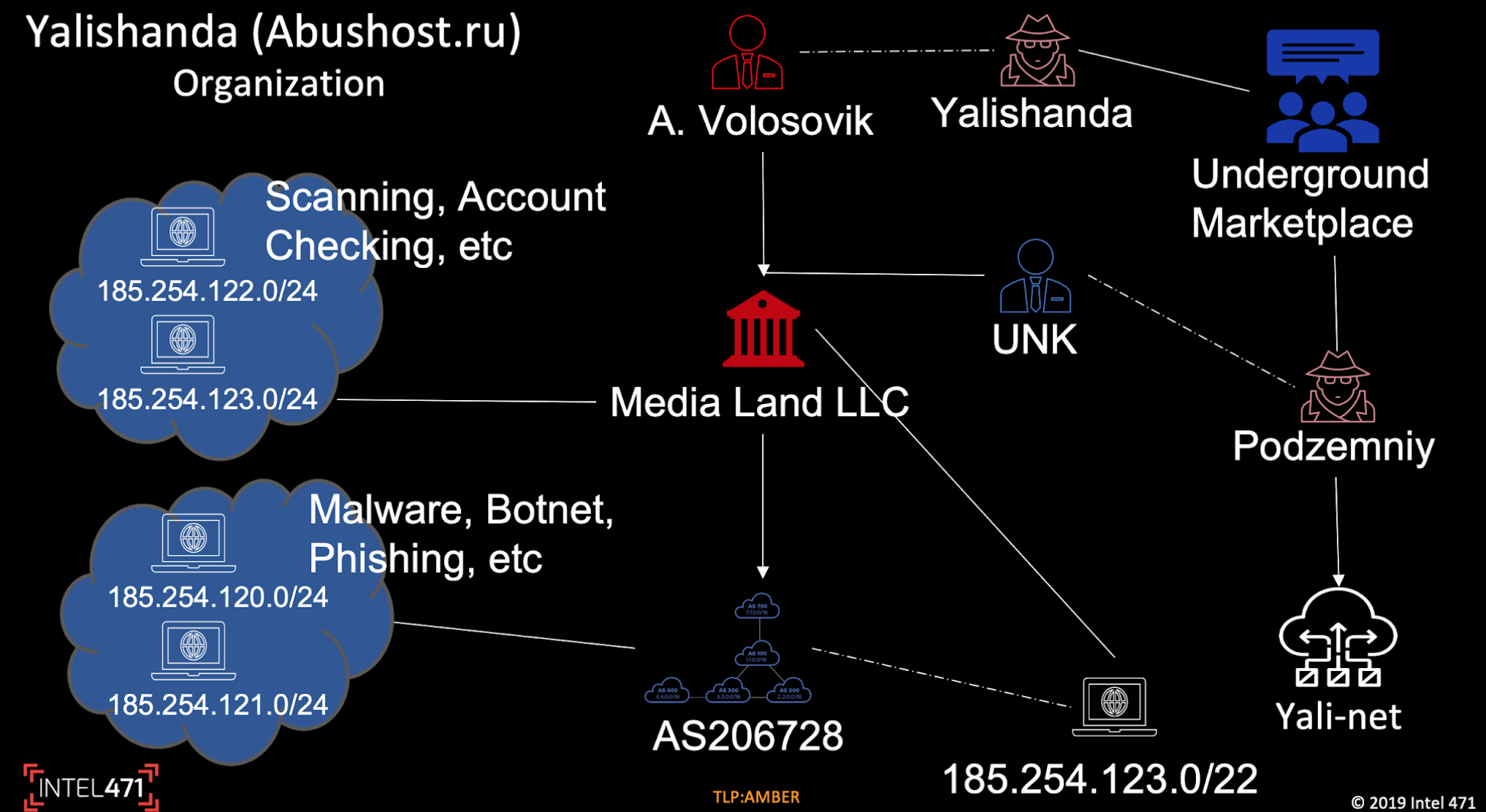
Image: Intel471
KrebsOnSecurity began this research after reading a new academic paper on the challenges involved in dismantling or disrupting bulletproof hosting services, which are so called because they can be depended upon to ignore abuse complaints and subpoenas from law enforcement organizations. We’ll get to that paper in a moment, but for now I mention it because it prompted me to check and see if one of the more infamous bulletproof hosters from a decade ago was still in operation.
Sure enough, I found that Yalishanda was actively advertising on cybercrime forums, and that his infrastructure was being used to host hundreds of dodgy sites. Those include a large number of cybercrime forums and stolen credit card shops, ransomware download sites, Magecart-related infrastructure, and a metric boatload of phishing Web sites mimicking dozens of retailers, banks and various government Web site portals.
I first encountered Yalishanda back in 2010, after writing about “Fizot,” the nickname used by another miscreant who helped customers anonymize their cybercrime traffic by routing it through a global network of Microsoft Windows computers infected with a powerful malware strain called TDSS.
After that Fizot story got picked up internationally, KrebsOnSecurity heard from a source who suggested that Yalishanda and Fizot shared some of the same infrastructure.
In particular, the source pointed to a domain that was live at the time called mo0be-world[.]com, which was registered in 2010 to an Aleksandr Volosovyk at the email address stas_vl@mail.ru. Now, normally cybercriminals are not in the habit of using their real names in domain name registration records, particularly domains that are to be used for illegal or nefarious purposes. But for whatever reason, that is exactly what Mr. Volosovyk appears to have done.
WHO IS YALISHANDA?
The one or two domain names registered to Aleksandr Volosovyk and that mail.ru address state that he resides in Vladivostok, which is a major Pacific port city in Russia that is close to the borders with China and North Korea. The nickname Yalishanda means “Alexander” in Mandarin (亚历山大).
Here’s a snippet from one of Yalishanda’s advertisements to a cybercrime forum in 2011, when he was running a bulletproof service under the domain real-hosting[.]biz:
-Based in Asia and Europe.
-It is allowed to host: ordinary sites, doorway pages, satellites, codecs, adware, tds, warez, pharma, spyware, exploits, zeus, IRC, etc.
-Passive SPAM is allowed (you can spam sites that are hosted by us).
-Web spam is allowed (Hrumer, A-Poster ….)-Forbidden: Any outgoing Email spam, DP, porn, phishing (exclude phishing email, social networks)
There is a server with instant activation under botnets (zeus) and so on. The prices will pleasantly please you! The price depends on the specific content!!!!
Yalishanda would re-brand and market his pricey bulletproof hosting services under a variety of nicknames and cybercrime forums over the years, including one particularly long-lived abuse-friendly project aptly named abushost[.]ru.
In a talk given at the Black Hat security conference in 2017, researchers from Cisco and cyber intelligence firm Intel 471 labeled Yalishanda as one the “top tier” bulletproof hosting providers worldwide, noting that in just one 90-day period in 2017 his infrastructure was seen hosting sites tied to some of the most advanced malware contagions at the time, including the Dridex and Zeus banking trojans, as well as a slew of ransomware operations.
“Any of the actors that can afford his services are somewhat more sophisticated than say the bottom feeders that make up the majority of the actors in the underground,” said Jason Passwaters, Intel 471’s chief operating officer. “Bulletproof hosting is probably the biggest enabling service that you find in the underground. If there’s any one group operation or actor that touches more cybercriminals, it’s the bulletproof hosters.”
Passwaters told Black Hat attendees that Intel471 wasn’t convinced Alex was Yalishanda’s real name. I circled back with Intel 471 this week to ask about their ongoing research into this individual, and they confided that they knew at the time Yalishanda was in fact Alexander Volosovyk, but simply didn’t want to state his real name in a public setting.
KrebsOnSecurity uncovered strong evidence to support a similar conclusion. In 2010, this author received a massive data dump from a source that had hacked into or otherwise absconded with more than four years of email records from ChronoPay — at the time a major Russian online payment provider whose CEO and co-founders were the chief subjects of my 2014 book, Spam Nation: The Inside Story of Organized Cybercrime.
Querying those records on Yalishanda’s primary email address — stas_vl@mail.ru — reveal that this individual in 2010 sought payment processing services from ChronoPay for a business he was running which sold counterfeit designer watches.
As part of his application for service, the person using that email address forwarded six documents to ChronoPay managers, including business incorporation and banking records for companies he owned in China, as well as a full scan of his Russian passport.
That passport, pictured below, indicates that Yalishanda’s real name is Alexander Alexandrovich Volosovik. The document shows he was born in Ukraine and is approximately 36 years old.
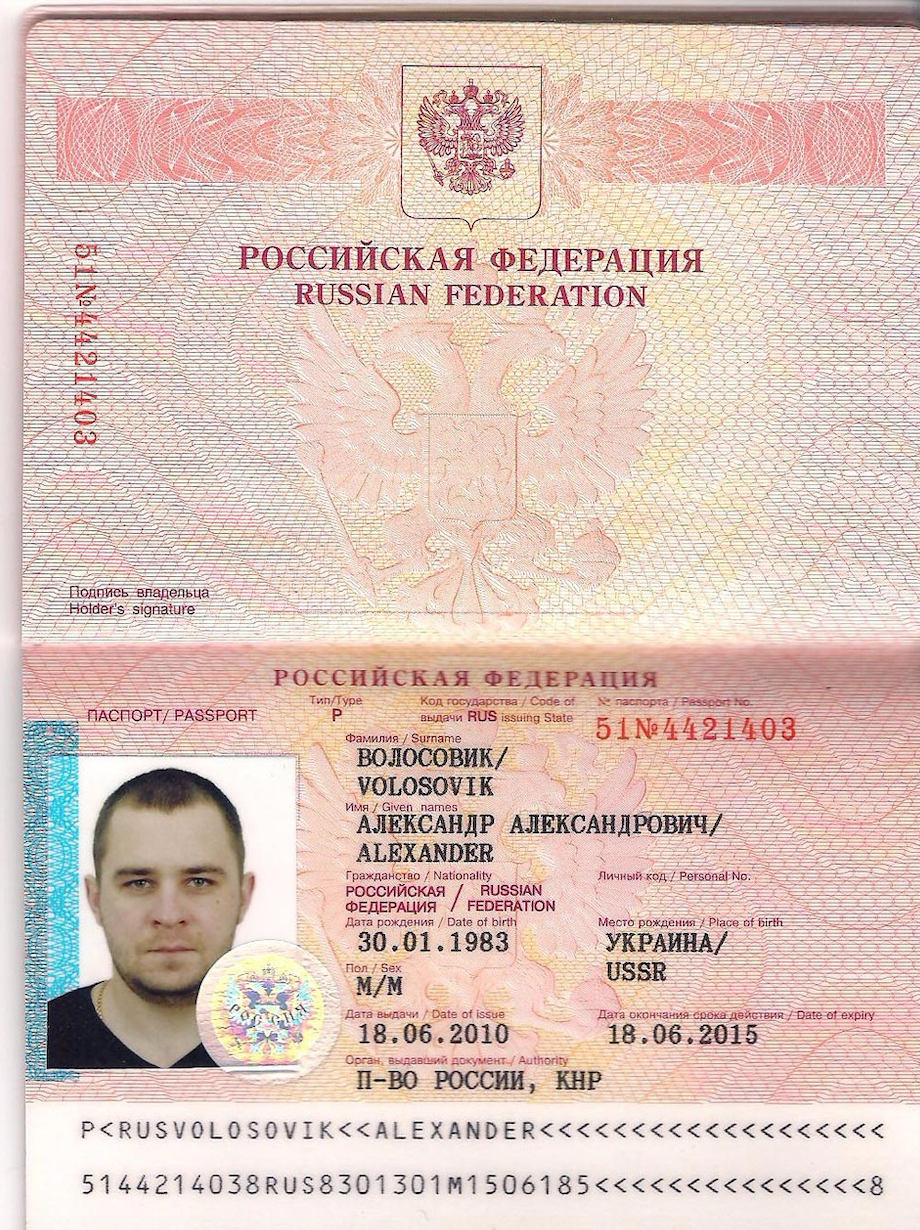
The passport for Alexander Volosovyk, a.k.a. “Yalishanda,” a major operator of bulletproof hosting services.
According to Intel 471, Yalishanda lived in Beijing prior to establishing a residence in Vladivostok (that passport above was issued by the Russian embassy in Beijing). The company says he moved to St. Petersburg, Russia approximately 18 months ago.
His current bulletproof hosting service is called Media Land LLC. This finding is supported by documents maintained by Rusprofile.ru, which states that an Alexander Volosovik is indeed the director of a St. Petersburg company by the same name.
ARMOR-PIERCING BULLETS?
Bulletproof hosting administrators operating from within Russia probably are not going to get taken down or arrested, provided they remain within that country (or perhaps within the confines of the former republics of the Soviet Union, known as the Commonwealth of Independent States).
That’s doubly so for bulletproof operators who are careful to follow the letter of the law in those regions — i.e., setting up official companies that are required to report semi-regularly on various aspects of their business, as Mr. Volosovik clearly has done.
However, occasionally big-time bulletproof hosters from those CIS countries do get disrupted and/or apprehended. On July 11, law enforcement officials in Ukraine announced they’d conducted 29 searches and detained two individuals in connection with a sprawling bulletproof hosting operation.
The press release from the Ukrainian prosecutor general’s office doesn’t name the individuals arrested, but The Associated Press reports that one of them was Mikhail Rytikov, a man U.S. authorities say was a well-known bulletproof hoster who operated under the nickname “AbdAllah.”

Servers allegedly tied to AbdAllah’s bulletproof hosting network. Image: Gp.gov.ua.
In 2015, the U.S. Justice Department named Rytikov as a key infrastructure provider for two Russian hackers — Vladimir Drinkman and Alexandr Kalinin — in a cybercrime spree the government called the largest known data breach at the time.
According to the Justice Department, Drinkman and his co-defendants were responsible for hacks and digital intrusions against NASDAQ, 7-Eleven, Carrefour, JCP, Hannaford, Heartland, Wet Seal, Commidea, Dexia, JetBlue, Dow Jones, Euronet, Visa Jordan, Global Payment, Diners Singapore and Ingenicard.
Whether AbdAllah ever really faces justice for his alleged crimes remains to be seen. Ukraine does not extradite citizens, as the U.S. authorities have requested in this case. And we have seen time and again how major cybercriminals get raided and detained by local and federal authorities there, only to quickly re-emerge and resume operations shortly thereafter, while the prosecution against them goes nowhere.
Some examples of this include several Ukrainian men arrested in 2010 and accused of running an international crime and money laundering syndicate that used a custom version of the Zeus trojan to siphon tens of millions of dollars from hacked small businesses in the U.S. and Europe. To my knowledge, none of the Ukrainian men that formed the core of that operation were ever prosecuted, reportedly because they were connected to influential figures in the Ukrainian government and law enforcement.
Intel 471’s Passwaters said something similar happened in December 2016, when authorities in the U.S., U.K. and Europe dismantled Avalanche, a distributed, cloud-hosting network that was rented out as a bulletproof hosting enterprise for countless malware and phishing attacks.
Prior to that takedown, Passwaters said, somehow an individual using the nickname “Sosweet” who was connected to another bulletproof hoster that occurred around the same time as Avalanche got a tip about an impending raid.
“Sosweet was raided in December right before Avalanche was taken down, [and] we know that he was tipped off because of corruption [because] 24 hours later the guy was back in service and has all his stuff back up,” Passwaters said.
The same also appears to be true for several Ukrainian men arrested in 2011 on suspicion of building and disseminating Conficker, a malware strain that infected millions of computers worldwide and prompted an unprecedented global response from the security industry.
So if a majority of bulletproof hosting businesses operate primarily out of countries where the rule of law is not strong and/or where corruption is endemic, is there any hope for disrupting these dodgy businesses?
Here we come full circle to the academic report mentioned briefly at the top of this story: The answer seems to be — like most things related to cybercrime — “maybe,” provided the focus is on attempting to interfere with their ability to profit from such activities.
That paper, titled Platforms in Everything: Analyzing Ground-Truth Data on the Anatomy and Economics of Bulletproof Hosting, was authored by researchers at New York University, Delft University of Technology, King Saud University and the Dutch National High-Tech Crimes Unit. Unfortunately, it has not yet been released publicly, and KrebsOnSecurity does not have permission yet to publish it.
The study examined the day-to-day operations of MaxiDed, a bulletproof hosting operation based in The Netherlands that was dismantled last summer after authorities seized its servers. The paper’s core findings suggest that because profit margins for bulletproof hosting (BPH) operations are generally very thin, even tiny disruptions can quickly push these businesses into the red.
“We demonstrate the BPH landscape to have further shifted from agile resellers towards marketplace platforms with an oversupply of resources originating from hundreds of legitimate upstream hosting providers,” the researchers wrote. “We find the BPH provider to have few choke points in the supply chain amenable to intervention, though profit margins are very slim, so even a marginal increase in operating costs might already have repercussions that render the business unsustainable.”




Good article! I bet this miscreant wouldn’t want to find a screenshot of his passport here. No more traveling abroad for him 🙂
I have a question though. Brian, how do you know that his passport was issued by the “Russian embassy in Beijing”? П-ВО РОССИИ, КНР stands for “Russian embassy, People’s Republic Of China”. And there’s more than one consulate of Russia in China.
Im also wondering, if the profit margin for those dodgy hosting companies is so thin, and the local authorities don’t do swat to eliminate them, why can’t some larger security company just DDoS them out of existence if it’s known that they host all kinds of illegal content?
It could be a easy deduction as he lived in Beijing at the time? I mean it wouldn’t make sense to travel out of that city to another that had a Russian Embassy when you can get one in the same city would it?
It’s not like he was using it for fake documentation.
There’s only one embassy (and it’s in Beijing), while there are a much larger number of consulates in various cities around the country.
Is it even legal (and ethical) to post someones personal data online like this? Even if you believe he is related to some cyber crime.
Of course it’s legal, but why wouldn’t it be ethical? Isn’t investigating and revealing unethical behavior and illegal activity almost the definition of ethical?
eth·i·cal
relating to moral principles…
I appreciate all the work that went into this, but doxing Yalishanda…
I can only imagine the unfortunate fallout of that. Stay safe and keep up the good work!
I agree but to be fair, I’m sure Krebs already has a lot of enemies and he’s managed to survive ok. One more shouldn’t hurt, right?
I have a strange feeling Brian isn’t in any hurry to visit any part of the CIS.
Here’s to hoping the rule of law continues to exist in the US and Brian ultimately dies of old age a happy man surrounded by friends and family.
legal, yes.
ethical? If he is the kind of person
it has been reported, then
f#%k em. He’s helped ruin a lot
of lives.
Why
are you
typing on so
many
different
lines
?
The first thing which popped into my mind was “Burn ‘im, Danno!”…
This is a great article, thank you for all your hard work in the security community
Interesting, well done. Another face to add to a collection. Beijing? School? I would wonder.
Why don’t other large companies controlling large parts of the internet backbone simply isolate and block these types of providers? I say let the fluff scream about ‘censorship’ etc, as it would do more than simply depending on foreign governments/law enforcement who rarely do anything as you have noted.
Or… Just wait until Russia finishes building their own special russia only censored internet they are working on.
Suggested:
http://www.change.org/p/icann-internet-corporation-for-assigned-names-and-numbers-tell-the-worldwide-internet-maintainers-to-disconnect-select-networks-in-china-from-the-internet-internet-2-0
This seems like a slippery slope to me.
“Commonwealth of Independent States” – I’m sure they are about as independent as the Russians would wish Ukraine was – NOT! These dirt bags deserve to sweat!!
Great insight Brian, as you usual you are the forefront breaking the key stories.
What I got from this is that Brian Krebs wrote a bestselling book about a Ukrainian living in Russia named Hoster who wears bulletproof spam.
🙂
Oh, just kidding.
If I ever begin a life of crime online, I’ll be sure to register domains and email accounts in other people’s names, so when BK doxxes me, it’ll be the wrong person.
Good work.
Thin profit margins? The law of supply and demand would lead us to conclude that there’s still plenty of BPH supply. And while the disturbance techniques could thin the herd, it would seem that there will always be a few remaining BPH to fulfill the demand.
(Unless the thin profit is due to the necessity of greasing the palms of regional authorities to allow them to continue)
I agree with this. Altering the economics may alter the way business is done, sure, but it’s not hard to imagine the reaction: cost of doing business goes up? well.. then.. so do the prices charged to the customer…
That being said, there are things that could be done to make it worse… A rising tide lifts all boats evenly, so don’t apply pressure evenly, be disruptive unevenly. Play whack-a-mole on purpose.
Komrade Krebs! It is shame you shine bad light on model citizen such as Volosovik. I mean come on. Take one look at that passport and tell me, is that not one handsome upstanding gentleman! But must not judge book by cover, yes? Here’s hoping I never get on Kreb’s “list”. Keep up good work and as they say in Mother Russia, hasta la vista, baby! *throws Vodka bottle at the wall*
this is a great article.thank you for posting.
Miscreant. That about sums it up.
Why the hell cant we as a global community ask our governments to enforce ISP’s around the globe (The trusted ones) to simply block all ASN-BGP broadcasts from these pricks and set a 127.0.0.1 if any traffic comes from these buggers.
Eventually the whole country will have to crackdown on the BPH’s and even if they try a VPN in say Australia or the USA then its the responsibility of the VPN provider to block that IP from the country as well.
We can do this as a community, block China as well as Russia because im sick of crackers, crawlers and spam coming from them 2 countries hitting my routers.
|The rule is simple. IF ASN = BlockList, Return Lookback. Sever the communication at that point and dont allow any data to hit the next hop and the country will bleed dry economically and socially (Block bank transfers as well and then the average Joe will start complaining).
If the ISP does not comply, throw the bloody CEO and Directors in prison and you watch how fast they react and how fast these spammers etc will all be hauled to jail.
Why depend on the government? There is a great tool on most Linux servers/desktop installations called iptables that can block whole countries at the system level. China, bye. Vietnam, bye. Russia, bye. Anybody, bye… It’s been great at eliminating brute force attacks against SSH/logins & email spam. Sadly, I don’t see a similar tool in Windows…
Windows apps that IP block, that I used years ago: 1. Peerblock 2. Blocklist Manager, which to my knowledge can block CIDR notation.
To Jammer’s point, some of the IP’s in the Kreb’s graphic were Spamhaus Block List(ed) (SBL[‘d]). Spamhaus also maintains Extended Don’t Route or Peer (EDROP) which doesn’t currently list the suballocated CIDR of the ASN shown in the graphic which are “controlled by spammers or cyber criminals”, partially quoted from Spamhaus.
I know iptables very well, i set GEO locations to block when setting up UTM’s and Meraki’s but that still doesnt solve the underlying issue does it. Instead of using sanctions like the USA against iran, imagine blocking electronic communications to a whole country? I bet they would start acting quick smart.
You only have to host a service/port thats internet facing to see the amount of bots, crawlers, crackers etc running constantly lol, when i show end users they simply freak out and then they understand why i am so anal about passwords and blocking countries that host payloads.
I wouldn’t start with blocking an entire country; but, individual ASN’s. But, if non-cleanup I’d continue blocking up to the point of the entire country, from outside the country. The point of: https://krebsonsecurity.com/2019/07/meet-the-worlds-biggest-bulletproof-hoster/#comment-492913
I’m with you that not enough blocking of entire IP network ranges and ASN’s, a particular one in mind in Vietnam and Caribbean, etc, is occuring. I’ve seen other notoreously dirty ASN’s over the last year drastically cleanup.
The information in this post was something that a part of the IT security community has known for a long time and managed to keep it for themselves, to allow covertly tracking Alex and his friend Podzemniy.
So nice work Krebs!
You basically ruined several years of tracking and law enforcement work by publishing this article.
Idiot!
Krebs is a journalist with the duty to expose information of newsworthy value to the light. He can’t sit on a story indefinitely, either.
Is the goal to track bad guys for years, or is the goal to eventually stop them?
Pardon my callousness, but why doesn’t the CIA just off these people left and right? They do it to minor players all the time in politics. Not like anyone is going to miss these leaches on society, and the CIA can keep the cash for their dirty covert politics.
Because, Mahhn, sometimes the CIA has skin in the game. Read “American War Machine: Deep Politics, the CIA Global Drug Connection, and the Road to Afghanistan (War and Peace Library)” by Peter Dale Scott…
The CIA is not a hit squad. That’s why.
Even if they were a hit squad, this man is not a threat to national interests. There’s no practical reason to risk diplomatic relations or risk the safety of undercover agents or their informants for such a killing.
But they’re not a hit squad. So don’t be silly.
So as someone that has run a small ISP, I have to ask… If there are so many security orgs watching these business, why not publish a list of ASes that are evil, and then an additional list of ASes that are enabling this business? It seems like cutting these operations off from the internet is incredibly feasible, at least by ISPs that care to protect their customers from reaching or being reached by these IPs/ASes?
Sure they can change IPs and such, but part of their business does rely on having fixed addresses for some of the services…
I think part of the challenge is a lot of these BP hosters are liberally (ab)using the major cloud providers to spread their operations out and to achieve resiliency and hide in the crowd.
I’ve seen many backbones, major providers, rather dirty in and of themselves, at least not so many years ago.
Some of the IP’s mentioned in this article, from their network ranges, aren’t hiding from the CBL blocklist.
The Spamhaus Composite Block List (CBL) had some of the IP’s shown in this article, last I looked. Some where on the SBL, since removed. I haven’t, or yet, looked up the IP’s in other blocklists.
Also, currently excalated to the UCEprotect’s Level 2 blcoklist, for “one or several networks which [the] IP belongs to have [sent] too much spam within the last week”.
The IPs ending:
…11, …16,…31, …37, …40
None of the article-shown IP ranges are listed onUCEprotect’s Level 3 blocklist, which “lists IP Space of the WORST [upper-cased by me] ASNs”.
That is definitely a criminal wiring job on those racks!