The U.S. Securities and Exchange Commission (SEC) is investigating a security failure on the Web site of real estate title insurance giant First American Financial Corp. that exposed more than 885 million personal and financial records tied to mortgage deals going back to 2003, KrebsOnSecurity has learned.

First American Financial Corp.
In May, KrebsOnSecurity broke the news that the Web site for Santa Ana, Calif.-based First American [NYSE:FAF] exposed some 885 million documents related to real estate closings over the past 16 years, including bank account numbers and statements, mortgage and tax records, Social Security numbers, wire transaction receipts and drivers license images. No authentication was required to view the documents.
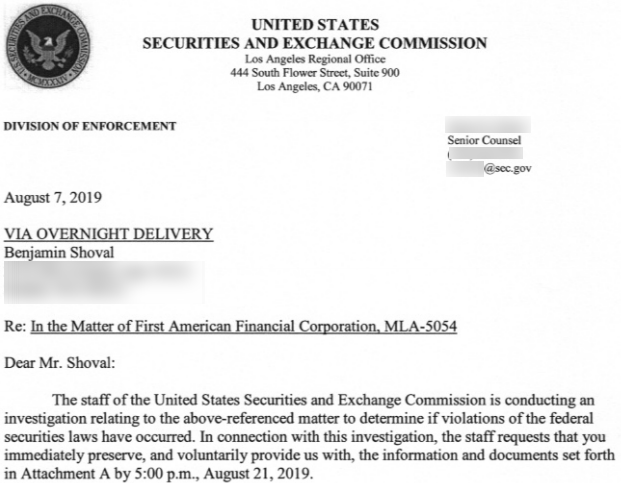
The initial tip on that story came from Ben Shoval, a real estate developer based in Seattle. Shoval said he recently received a letter from the SEC’s enforcement division which stated the agency was investigating the data exposure to determine if First American had violated federal securities laws.
In its letter, the SEC asked Shoval to preserve and share any documents or evidence he had related to the data exposure.
“This investigation is a non-public, fact-finding inquiry,” the letter explained. “The investigation does not mean that we have concluded that anyone has violated the law.”
The SEC declined to comment for this story.
Word of the SEC investigation comes weeks after regulators in New York said they were investigating the company in what could turn out to be the first test of the state’s strict new cybersecurity regulation, which requires financial companies to periodically audit and report on how they protect sensitive data, and provides for fines in cases where violations were reckless or willful. First American also is now the target of a class action lawsuit that alleges it “failed to implement even rudimentary security measures.”
First American has issued a series of statements over the past few months that seem to downplay the severity of the data exposure, which the company said was the result of a “design defect” in its Web site.
On June 18, First American said a review of system logs by an outside forensic firm, “based on guidance from the company, identified 484 files that likely were accessed by individuals without authorization. The company has reviewed 211 of these files to date and determined that only 14 (or 6.6%) of those files contain non-public personal information. The company is in the process of notifying the affected consumers and will offer them complimentary credit monitoring services.”
In a statement on July 16, First American said its now-completed investigation identified just 32 consumers whose non-public personal information likely was accessed without authorization.
“These 32 consumers have been notified and offered complimentary credit monitoring services,” the company said.
First American has not responded to questions about how long this “design defect” persisted on its site, how far back it maintained access logs, or how far back in those access logs the company’s review extended.
Updated, Aug, 13, 8:40 a.m.: Added “no comment” from the SEC.




Just 32 consumers? Hmmmmmm!
I share your skepticism that the breach affected only 32 consumers. The problem has to be of sufficient magnitude to motivate the SEC to investigate, methinks.
As for NeedsJavaToC#’s optimism that companies are beginning to take security seriously, I’m not there yet. Until companies are held accountable (i.e. civil penalties or adjudicated settlements big enough to put a serious dent in their bottom lines), any minor financial or PR “clean up” in the aftermath of security breaches would be chalked up to the cost of doing business. Equifax comes to mind as a good example. I’m sure First American will offer the standard fix — free security monitoring for a year. Whopppeeeeeeee!
Another problem is that consumers have been numbed by so many data breaches that many simply assume their sensitive information is already out there and have resigned themselves to accept this New World Order. I see it among my own circle of friends. The privacy and security conscious person that I am, I sometimes feel that I’m perceived as a hopeless idealist as I beat the drum asking, “Please care. It’s important. Please care.”
Totally agree! What bugs me as well, is that congress has threatened every since the last century to put more regulations on the credit bureaus. But they kept promising the world they didn’t need it, and would play fair and secure….well we see the results of that – it is high time they slap some more regulations on them with teeth in the law.
+1.
In addition, to hitting the business itself with meaningful, substantial financial penalties, I submit that those highly-paid CEO’s & others in corporate management should also be held *PERSONALLY-liable* for payment of any fines imposed, as well as, any monetary damages awarded in every civil lawsuit brought against the company.
That liability/responsibility by corporate insiders for corporate results is an area of law the really needs some work here. More and more it seems that the executive suite in corporations is playing a heads I win (good corp performance — profits, stock price…)/tails you lose (bad corporate performance, such as the breaches).
Nobody would work in those jobs if they were personally liable for someone else’s shortcomings. The same goes for software development. How many people would develop software if they were personally liable for bugs?
A Tesla crashes because of an autopilot bug. Do we go arrest the developers and levy millions in fines against them? You would not have even a single on-shore developer. It would put us back into the stone age.
Well said, plus that why you purchase cyber insurance. It’s always smart to spread your risk.
I feel like we are starting to see the start of companies taking security seriously. Sure its slow and there are plenty that just don’t, but I think the added pressure from states and people seemingly becoming more concerned about their data is pushing companies to react when they see another company burn.
Maybe I am being naive, but I am optimistic that for ever company that gets burned with a security breach, 10 will start getting their act together.
Sir you are naive. So many cases of “oops, I gave away your data, here is a subscription to monitor your credit”. Until these companies are forced to give over serious cash to each individual that is exposed, this will continue.
I thought the same…..back in 2014. Last I checked it was 2019 and nothing has changed. As a matter of fact Equifax actually made money no the breach above their payout amount. But as a security professional I am torn as I really have no financial interest in these companies taking security seriously. If they did then the endless amount of work may dwindle. Does Symantec really want to end all malware?
That makes me sad. But it is good to hear I am not the only one who was at least at one time optimistic. I suppose the upside to all this is there will always be demand for competent security professionals.
“Does Symantec really want to end all malware?”
There’s been no real danger of that since about 2003-ish.
That’s now a moot question since the symantec name and business security products are being sold off
So 32/885×10^6 = 3.61582^-8, or a minuscule fraction of the total? Either the perpetrating miscreant was really targeting a very small and selective group, or First American is blowing some dense smoke — my bet is on the latter.
Last week our security software flagged a link in emails coming from First American. (The link was to a page on their website and appeared in their standard signature.) I contacted the company multiple times to either alert them that there was a problem or to have them confirm that there was not.
I was routed first to the internal help desk where the user loaded the page in question and told me that it looked fine so there was nothing to worry about. The rest of the conversation didn’t go much better.
Long story short: I gave up. Hopefully it was a false positive.
That’s really interesting! Seems like you stumbled upon the smoking gun there. I was always caught between a rock and a hard place when I was a Security Analyst doing similar work. I’d find a strange event that just didn’t seem right and call the clients to inform them anyways. Not only are you covering your backside, but you may be the first line of defense that prevents a major breach. That was one thing they always told us, too: don’t ever get complacent. Just because you think you’ve seen it 1,000 times before, this could be the case of The Boy Who Cried Wolf.
Interesting article, well written, on such limited information.
Only 32 ” victims”? Sounds as though, they found an interesting account. Sounds as if they found a honey pot. And probably not a public identified victim.
Remember, even the best and the brightest are not 100% there every day. And they do not work 24×7. And they are the hardest to retrain to a new way of doing something. And their trainers are not the 1% of the best and the brightest but usually those who are affordable in today’s market.
Now, if companies would spend half of their marketing as security, maybe, if the governments spent time considering the victims plight? Maybe?
Getting organizations to invest in IT security is like pulling teeth. Security doesn’t develop or sell product and thus, doesn’t make any money for the bottom line. CEOs don’t want to put any money into it. I may be moving back into my role as a Software Engineer since I have been unable to obtain employment as Cybersecurity Analyst (CompTIA Security+, CompTIA CySA+) for 11 months now.
Dave – I was just looking at FireEye yesterday.
They state that 3.5 million cyber security jobs will go UNFILLED by 2021! https://content.fireeye.com/expertise-on-demand/video-one-expertise-on-demand?xs=73300
You have to keep trying! We need you there!
FireEye Career Opportunities – https://www.fireeye.com/company/jobs.html
They might say that, but the reality is most of these jobs are either extremely low paying, only serve to fill a checkbox for the company, or have so many hoops and restrictions they just aren’t worth showing up for. Add in the high tuition costs, ongoing certification circus, and lack of respect from the company leadership and I’m surprised anybody still wants to work in the field.
Same ol’ Same ol’ Song and Dance my friend!
Too many good comments here to reply to each one!
It seems the only companies that learn are the companies that get attacked.
Robert – As for Symantec – Well maybe Broadcom will fix the issue.
In regards to the credit monitoring – I probably have about 10 years worth of credit monitoring compressed to about 3 years.
I wonder if I already have it from one breach does the new breach give me an additional year or does the monitoring company just take the money and keep the original one going?
Here are those NY “strict new cybersecurity regulations” (with convenient exemptions):
https://www.dfs.ny.gov/docs/legal/regulations/adoptions/dfsrf500txt.pdf
What’s simply needed is a fine for *any* company that has a breach – minimum $10,000 per record breached. That’ll get their attention.
Of course, that opens up new ways to put your competitors out of business – pay a hacker, then let .gov do the rest of the dirty work.
As Brian said at the very end, log retention will be the ultimate decider. It doesn’t matter if the company has been vulnerable for 16 years if the access logs only go back six months. Unless there is some regulated retention requirement I doubt that there would be more than 12 to 18 months of logs because of the space requirement.
So that would mean 32 confirmed victims and an unknowable number of unconfirmed victims.
I don’t get why people want the government to just fine these companies. Why are we not seeking the government to represent those who are impacted and get substantial restitutions paid out to the victims? The government cant use it’s authority and resources to represent all parties affected. It could be less sometimes, it could be more other times. But at least it won’t be all going into government coffers and the victims are left to take care of themselves.
Last night I signed up for the free credit monitoring offered by Capital One’s data breach. I look forward to my “complimentary credit monitoring” from First American Financial.
All my credit files are frozen solid anyway. But how is credit monitoring going to help when cybercrooks probably now have enough information to initiate a wire transfer out of my bank account? Whatever minor detail the crooks are missing could be spear phished from my lawyer, banker, or mortgage broker.
This is silly. They clearly don’t want to notify their customers of their incompetence, so they are downplaying the severity in hopes of getting off the hook.
Just because the rest of the information was not classified as “non-public personal information” doesn’t mean it is worthless. It still is a valuable asset for anyone attempting to phish customers who used First American services.
Just because it only has their “public” names or property records, which are usually freely available through county assessors website, does not mean those customers should not be notified. Attacks now have an advantage over those individuals. They should be notified in case they start receiving suspicious emails and calls from someone posing as First American.
Funny.. I found a lot of PHI on the net, and it just gets deleted by the FBI.
Clearly there’s an epidemic of leaky consumer credit data. None of it is appearing on the dark web or resulting in identity theft. Who has it?
SIEM focuses on the perimeter but it cannot identity misconfiguration. The incorrect assumption is that this misconfiguration is accidental. In order to stop this you have to understand why it is happening. Only then can you figure out the common elements – including the vendors and technologies they use.
This is about data scraping. But how can anyone protect against it if you don’t understand how scraping and tracking technology works, why it is happening or who is doing it?
From what I’ve seen nearly every major breach involves an insider, either intentional or accidental. But these credit data leaks are likely intentional. Just looking at the SaaS they used intimates that someone was selling data.
Singapore – always the leader in Cybersecurity is working on a PII data dictionary. If it includes identifiers similar to SWIFT codes then hacking of financial data will stop because the data will no longer have any value. This is the only way to protect it is to remove its value on the open market.
All of this leaked data is solely being used to build NEGATIVE consumer profiles. Case in point the US is undergoing a credit crisis, thus the Fed dropping rates. The more data that’s compiled, the more damaging it is. This is why we have FCRA laws which only permit 7 years of credit data. Why didn’t Compliance pick that that they had legally expired data in production? Surely doing this wasn’t worth the risk of losing their NYDFS license. NY does shutter offenders unlike the Federal Gov.
CCPA, unlike GDPR does not distinguish between processor and controller so if any legitimate business is somehow using a vendor that uses or derives value from stolen data, it is a very bad business decision. It will be uncovered. Watch the data forensics field explode after 1/1/2020. Consumers will be tracking their data.
Everyone best familiarize yourself with what constitutes stolen data because I’m sure the California courts soon will.