A Slovenian man convicted of authoring the destructive and once-prolific Mariposa botnet and running the infamous Darkode cybercrime forum has been arrested in Germany on request from prosecutors in the United States, who’ve recently re-indicted him on related charges.

NiceHash CTO Matjaž “Iserdo” Škorjanc, as pictured on the front page of a recent edition of the Slovenian daily Delo.si, is being held by German authorities on a US arrest warrant for operating the destructive “Mariposa” botnet and founding the infamous Darkode cybercrime forum.
The Slovenian Press Agency reported today that German police arrested Matjaž “Iserdo” Škorjanc last week, in response to a U.S.-issued international arrest warrant for his extradition.
In December 2013, a Slovenian court sentenced Škorjanc to four years and ten months in prison for creating the malware that powered the ‘Mariposa‘ botnet. Spanish for “Butterfly,” Mariposa was a potent crime machine first spotted in 2008. Very soon after its inception, Mariposa was estimated to have infected more than 1 million hacked computers — making it one of the largest botnets ever created.
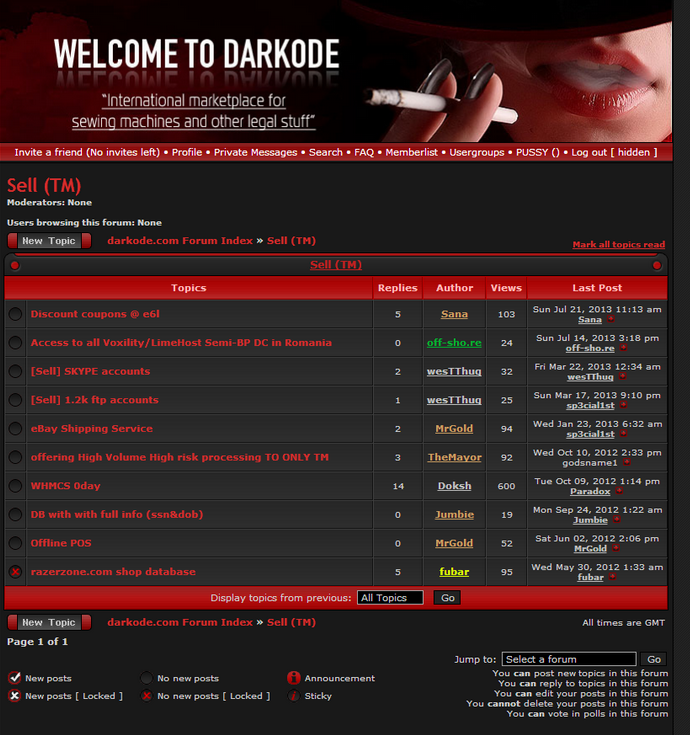
Škorjanc and his hacker handle Iserdo were initially named in a Justice Department indictment from 2011 (PDF) along with two other men who allegedly wrote and sold the Mariposa botnet code. But in June 2019, the DOJ unsealed an updated indictment (PDF) naming Škorjanc, the original two other defendants, and a fourth man (from the United States) in a conspiracy to make and market Mariposa and to run the Darkode crime forum.
More recently, Škorjanc served as chief technology officer at NiceHash, a Slovenian company that lets users sell their computing power to help others mine virtual currencies like bitcoin. In December 2017, approximately USD $52 million worth of bitcoin mysteriously disappeared from the coffers of NiceHash. Slovenian police are reportedly still investigating that incident.
It will be interesting to see what happens with the fourth and sole U.S.-based defendant added in the latest DOJ charges — Thomas K. McCormick, a.k.a “fubar” — allegedly one of the last administrators of Darkode. Prosecutors say McCormick also was a reseller of the Mariposa botnet, the ZeuS banking trojan, and a bot malware he allegedly helped create called “Ngrbot.”
Between 2010 and 2013, Fubar would randomly chat me up on instant messenger apropos of nothing to trade information about the latest goings-on in the malware and cybercrime forum scene.
Fubar frequently knew before anyone else about upcoming improvements to or new features of ZeuS, and discussed at length his interactions with Iserdo/Škorjanc. Every so often, I would reach out to Fubar to see if he could convince one of his forum members to call off an attack against KrebsOnSecurity.com, an activity that had become something of a rite of passage for new Darkode members.
On Dec. 5, 2013, federal investigators visited McCormick at his University of Massachusetts dorm room. According to a memo filed by FBI agents investigating the case, in that interview McCormick acknowledged using the “fubar” identity on Darkode, but said he’d quit the whole forum scene years ago, and that he’d even interned at Microsoft for several summers and at Cisco for one summer.
A subsequent search warrant executed on his dorm room revealed multiple removable drives that held tens of thousands of stolen credit card records. For whatever reason, however, McCormick wasn’t arrested or charged until December 2018.
According to the FBI, back in that December 2013 interview McCormick voluntarily told them a great deal about his various businesses and online personas. He also apparently told investigators he talked with KrebsOnSecurity quite a bit, and that he’d tipped me off to some important developments in the malware scene. For example:
“TM had found the email address of the Spyeye author in an old fake antivirus affiliate program database and that TM was able to find the true name of the Spyeye author from searching online for an individual that used the email address,” the memo states. “TM passed this information on to Brian Krebs.”
Read more of the FBI’s interview with McCormick here (PDF).
News of Škorjanc’s arrest comes amid other cybercrime takedowns in Germany this past week. On Friday, German authorities announced they’d arrested seven people and were investigating six more in connection with the raid of a Dark Web hosting operation that allegedly supported multiple child porn, cybercrime and drug markets with hundreds of servers buried inside a heavily fortified military bunker.




Phirst!
Hope they throw the book at this dude.
Great story! I wondered what had happened to these bad actors. It never ceases to amaze me when you look at how “professional” their websites and marketing appear. I’m sure many KOS readers wonder why they don’t just switch to legitimate businesses; after all the demand is there, and no one would be looking for them anymore.
I know – I’m the naive optimist. 🙂
I think there are some kinds of people that would rather “beat the system” than “make the system.” People will do things for “workouts” that they won’t want to do for “work.”
Easy.
There’s more money with no delays or bills in doing things the blackhat way.
I own a legitimate Consulting / PenTest firm, and it’s sickening how much more a Blackhat can make per engagement. You *need* my business and others like me, but don’t want to pay a quarter of what it will cost when you’re attacked.
I’d never go blackhat, as I enjoy my freedom, but when I can click “Go” on a phishing/mining campaign, do nothing, and sit back and watch the $ roll in….
I know a lot of people may disagree with you, but that’s the sad reality. I hear the same questions asked about bug bounties. “Why aren’t more blackhats doing bug bounties?” Same answer you gave. They get way more money breaching a company and selling personal information on the dark web rather than (i) reporting a bug, (ii) waiting for the client to respond, (iii) having them validate if it’s a legitimate bug or not, (iv) probably have the client say that it doesn’t affect them, (v) maybe have a little back and forth to prove its legitimacy, (vi) then you’re either getting a small bounty in reference to the amount of work you put in, or the client could just close out the report as Not Applicable.
The first bug I found was when I still had no idea how the platforms worked. It was an information disclosure bug that was a result from a leftover endpoint they forgot to remove in their application. That particular company didn’t offer bounties, but I’ve often wondered how much I could have gotten for that bug had the company provided a bounty–or had it been put on the dark web. Which, like you, I enjoy my freedom too much to do something so stupid.
I’m not that much of an online reader to be honest but your site is really nice, I’ll go ahead and bookmark your site to come back later on. Thanks for sharing this post.
Spammer
“Fubar” – When you get arrested by your own government and then extradited to the United States for prosecution
Oh, I remember ‘Mariposa’.
Those botnets made it so easy for attackers to compromise the victims’ networks; while it costs the victims so much money to protect themselves from such threats.
The world has not been the same since…
BTW, Thanks for this update Brian!
Anyone believing that Iserdo had nothing to do with the NiceHash hack of 62M of BTC while he was serving as the CTO is living in a dream world.
That would be nice hash they are smoking!
Well, when you hire a criminal as your CTO, what could possibly go wrong?
Book ’em, Danno!
Two interesting takedowns within a week in Germany? I wonder if authorities have a new tool up their sleeve, like a compromise of TOR or some such thing. Regardless, everybody that has an ethernet connection should know that there is no such thing as anonymity in reality. Signals come and go from known physical addresses, somebody just has to make the effort to connect the dots. Just as one can make it computationally intensive to rip a password hash, but one can’t make it impossible to do when the resources are basically limitless.
A thought to the wiseguys: The fly that keeps landing on your forehead in a room full of flies is usually the one that gets swatted first…
When I saw the name fubar, I immediately thought of foonet for some reason.
Talk about a blast from the past…..
Here’s the “problem”:
Iserdo has been already convicted for the crime and it is unconstitutional to be tried two times for the same crime…
So will the prosecutors break their own laws in order to get the conviction?
finally germans are using the bunkers again for something good and now this..
sad!
send anthrax to the US, not prisoners.
<3 ++
“On or about December 5, 2013” appears a lot in the indictment. The indictment was filed December 4th, 2018, one day before the statute of limitations on things like wire fraud (5 years). I wonder why they waited so long?
Waiting for the last minute, reveals a weak case. It’s likely that prosecutors know they’ll never be able to convict on evidence, but feel it’s important to send a political message that they can still inflict punishment.
And that punishment is this process: Legal fees, being held for extradition, constant searches of your body, imprisonment while awaiting bail, separation from friends and family, hearings, and more.
If they actually had a strong case, they would’ve nabbed him as he left his Slovenian prison cell a few years ago.
Still, the political message will likely compel other defendants to plead guilty, rather than deal with the same pile of poo. And some career DOJ employees might get a promotion for this abuse of power.
—
P.S. to Stephen (2 comments above yours), completely different jurisdictions involved, so it’s not double jeopardy.
Lol fubar been a fed before 2013.
Funny how mafi put so much trust into him. Everyone told him he was a fed from the jump.
All the real OG’s are still active. The real dk is not public or known to any researchers and never will be. The circle is under 12 and will remain.
Keep telling yourself that buddy. Enjoy prison.
I’ve been out of the game too long. statute of limitations.
Those of us who were smart took the blackhat money and invested it into legit online business.
I do however still keep in touch with old colleagues.
The dk raid taught those who are still at large a valuable lesson. The ones who are still active are beyond careful at this point. Probably a little too overcautious if you ask me.
“The real dk is not public or known to any researchers and never will be. ”
Al Capone, John Gotti, Mussolini, and Richard Nixon all thought they could get away with it. Good luck!
Sin1s there was never a user on darkode with your nick or a similar nickname before the takedown… so you’re just talking to sound cool or what? Can you backup anything you’ve said on this article’s comments? I doubt it, but please do prove me wrong.
ROFL.
Check the old leaked db’s.
I’m sure sinis, sinister or something similar is one one of the dumps.
Also, my handle has been changed multiple times.
Pm me you’re jabber..
Actually don’t, you’re a nobody.
Funny if they have less than 12 the forum would be useless, from what i remember they are a black market place selling malwares etc, how would they make money with 12 people when prob 4 of the are moderators lol sounds like you talking out your ass , sinister is a common “hacker” name which makes your statement invalid.
because it’s hardly a marketplace anymore.
12 is a roundabout. there is no moderation. those who are left are known to be trusted.
no business is being done over a site anymore – lesson learned.
“sinister is a common hacker name” – lol.
i don’t have to explain who i am. as i mentioned before – those who were smart took the spam/ransom/whatever blackhat money and and moved it into legitimate businesses.
Skorjanc was already sentenced for that crime in Slovenia.
Article 14 of International Covenant on Civil and Political Rights:
“No one shall be liable to be tried or punished again for an offence for which he has already been finally convicted or acquitted in accordance with the law and penal procedure of each country.”
Considering statute of limitations are up for 2 out of the 3 charges, it just seems like FBI has a little too much time on their hands.
Charge 1: Rico – 4 Year Statute Limitation (expired 2017)
Charge 2: Wire/Bank Fraud – 5 Years (expired 2018)
Charge 3: Identity fraud – 7 years. (expiring 2020 or in 2 months)
Lets hope he falls out of the plane on the way to the US.
So long as the sentences for these crimes stays pathetic, they will continue to encourage more criminals. Hell, if you get a million, spend 10 years in jail, still have the million – which is a hell of a lot more than I have after working 10 years. It’s a wonder more IT people aren’t criminals, it pays well, the punishment is mild at worst. And it might land you a job working for super criminals (governments) with unlimited benefits.
Still far worse than bankers who broke the world and got bailed out by tax payers
Hmmm…
Crook is Slovenian?
Has passport?
Slovenian has piece of US$ 52 million?
Is now nationalist hero status here in Ljubljana!
Capitalism pay off for small countries…finally…
Is future candidate for president in most African countries, south of Sahara; or east of Ukraine.
US$ 52 million…
And to think he never use gun…
Smart Slovenian…
Medieval, retrograde US crooks so backward.
Use gun for US$3.19 robbery of 7-11 empire, facing 20 years for gun use.
Forget dat US$3.19…
Hope many US crooks learn from this illustrious, Slovenian exploit.
Click here for super low cost, effective Slovenian malware: me-dufus.com…
i knew fubar is such a snitch bitch
lets hope mafi will be out soon and will see his family again
How do you know mafi is in prison? Any article links you can provide or proof to substantiate this claim?
https://www.justice.gov/opa/pr/major-computer-hacking-forum-dismantled
Indicted and pled guilty. But incarcerated? Are you sure?
Two years after that article, Krebs was still asking:
https://twitter.com/briankrebs/status/908717858313703424
Exactly… so is there any proof mafi was ever incarcerated? Doesn’t seem like it. I would be super interested if there was!
Incarcerated, yes. But only temporarily.
Mafi really isn’t that interesting. Iserdo should have done a better job when deciding who to hand the keys to the castle.
Troll… do you have any proof mafi was ever incarcerated? Come on, let’s see it. Friendly advice, I would be careful making claims regarding darkode for fun…
Fun fact.
Once upon a Time me and a friend needed a webmailer, asap.
Mafi came in clutch and said he could have it done by the end of the week. 60% inbox guarantee!
Bots -> webmail -> good data.
Wanna guess how many actually hit inbox? ROFL
Mafi couldn’t code himself out of a web paper bag, the community should have never been handed to him.
This is the man who single handedly destroyed it.
The man who let “lizard squad” run a muck.
He’s a joke.
Sin1s… you do know there were 3 founding members of darkode right? iserdo was just 1 of the 3. He didn’t “hand off” anything to fubar. The forum evolved long after iserdo left and fubar eventually emerged as one of several administrators.
Why so much hate on fubar anyway? The kid is fighting for his freedom. There were much much worse people on darkode with ties to Russian boards like mf and dcm causing millions in actual damage.
Ttoll? Fubar is a Fed, period. He’s always been a Fed.
Friendly advice lol.
If you had any idea what you’re talking about then I shouldn’t need to explain to you who I am.
I never said he handed anything to fubar.
Fubar is a nobody.
Its funny how the whole so called “infosec” community call this guy a criminal simply because the Government says so yet they never seen any evidence and don’t know the guy. Simply amazing how brainwashed people as a whole are
Hi Jack. What in particular do you think is in error in the USG’s claims and why? Mr. Škorjanc definitely has a great deal of evidence against him already.
They clearly want him for information he can provide. Owning nicehash he obviously has wealth of information that will be useful to U.S. The bottom line is U.S global reach can grab anyone it needs as intelligence asset under pretext of such evidence as text messages dated back many years ago. But this saga helps journalists like you sell stories, keep the plebs happy, career prosecutors make name for themselves, everybody win except the unfortunate victim who need to spend a fortune to defend themselves & comply or go to kangaroo trial. I don’t know this guy but reading comments on reputable blogs and twitter some saying “he must be locked up and key trowed away” and “he must be on electric chair” by people who never seen evidence, have opinion by contagion yet they call themselves researchers. Shame!
Maybe you didn’t see the question. Here it is again:
“What in particular do you think is in error in the USG’s claims and why?”
It is impossible to understand it without being yourself or someone close to you in similar situation, so it is meaningless to explain it here. Let me tell you a short story of a situation similar to this: imagine you are someone from a third country talking to random people on internet, and you talk with a “target” about hacking, malware etc curiosity. Now the U.S gov can, based on simply that message indict you and extradite you, for only writing text messages, no hacking, no stealing. Now this guy spent around a year in U.S jail and after they threaten to jail him for 30 years, they ask him to plead guilty just for “good public opinion” so people will think the Government is doing their job. Then on news it appears that he admitted guilt and was sent back to his country. This is real story and that is why i don’t believe anything i read on news. Its just like fake news, we can never really know the truth. People are forced to admit guilt even if they didn’t do anything illegal, just to go home to their families. I would not be surprised if this darkode guy story is similar
relationship
relationship
Vizit this website
canva