Crooks are constantly dreaming up new ways to use and conceal stolen credit card data. According to the U.S. Secret Service, the latest scheme involves stolen card information embedded in barcodes affixed to phony money network rewards cards. The scammers then pay for merchandise by instructing a cashier to scan the barcode and enter the expiration date and card security code.
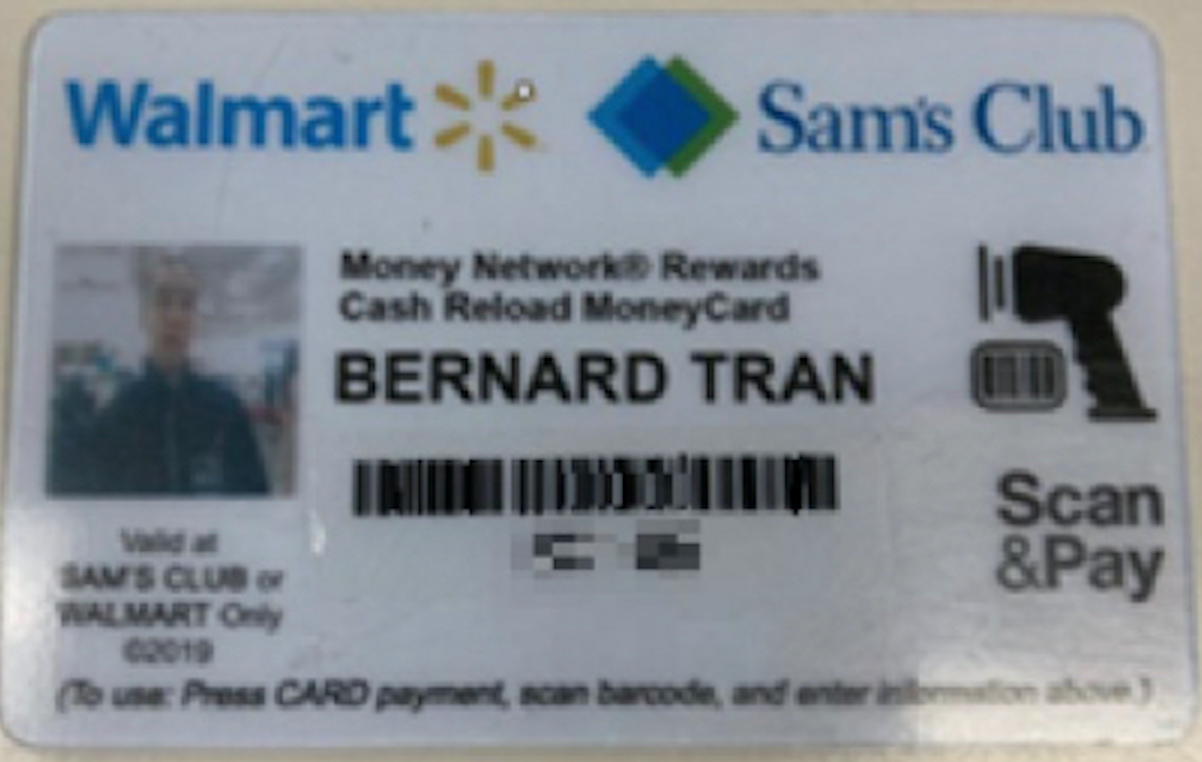
This phony reloadable rewards card conceals stolen credit card data written to a barcode. The barcode and other card data printed on the card have been obfuscated. Image: U.S. Secret Service.
Earlier this month, the Secret Service documented a recent fraud incident in Texas involving a counterfeit club membership card containing a barcode, and a card expiration date and CVV printed below the barcode.
“Located underneath the barcode are instructions to the cashier on the steps necessary to complete the transaction,” reads an alert the Secret Service sent to law enforcement agencies. “They instruct the cashier to select card payment, scan the barcode, then enter the expiration date and CVV. In this instance, the barcode was encoded with a VISA credit card number.”
The instructions on the phony rewards card are designed to make the cashier think it’s a payment alternative designed for use exclusively at Sam’s Club and WalMart stores. When the transaction goes through, it’s recorded as card-not-present purchase.
“This appears to be an evolution of the traditional card-not-present fraud, and early indications are linking this type of activity to criminal organizations of Asian descent,” the Secret Service memo observed.
“As a result of this emerging trend, instead of finding a large number of re-encoded credit cards during a search, a subject may only possess stickers or cards with barcodes that contain stolen card data,” the alert continues. “Additionally, the barcodes could be stored on the subject’s cell phone. If barcodes are discovered in the field, it could be beneficial to utilize a barcode scanning app to check the barcode for credit card data.”




Where to get C-C?? There is carding forums and carding shops but they are scammers!!
No good Stuff any more!
It’s totally appropriate that the first comment on this story should be from someone seeking info about where to buy stolen card data.
Maybe you should do just a little bit of research. One of the most popular card fraud bazaars on the Internet is actually named after this author and uses his likeness in their advertisements.
I Can’t fund nothing just typing on Google!!
I got scammed by Wu transfers I payed upfront 40% but no Wu transfer.
there is so many websites out there! as Krebs says there is a website under his name, also the notorious one the joker or you just go to the deepweb one Marketplace calls White House Marketplace. Please Krebs let him read my comment.
If he doesn’t trust the carding shops, he can acquire his card data the old fashioned way and steal it himself.
LOL! – For sure!
Another great article BTW, Brian! I wondered when we’d see something like gift card fraud come along.
Wtf?? U Can’t seal yourself I heared there is legit shops Only
He’d just steal his own card, which kind of defeats the purpose.
Art imitates life, which imitates art.
Poor Arthur.
Brian, card I purchased from your club does not work! PLEASE REFUND MY BITCOIN!
Dear Glup,
I’m Brian’s accountant. Sorry for the inconvenience. It was a processing error with your credit cards order. Please email me you bank account details along with your SSN and I will promptly refund you.
ROTFLMA!! That was priceless!
yoh made my day! loooooooooooool
… OMG it pretty much writes itself doesn’t it Brian LOLOL!!!
Yeah see I think that one commenter was right in that initial article you posted about your “imposter” hacked card bazaar site when they said they thought that it’s really been you all along… I mean the login does have your picture and passport and I think your personalized coffee mug on it too…
And it’s all starting to make sense now – h0w else could you have afforded to conscript an army of 380,000 thermostats, refrigerators and dishwashers into staging a fake war against yourself so you could get a better AdSense score on this, your “other” site (and of course publicity for Google Shield)!
And now see this poor guy “Connect” straight out of the box blows y’all’s whole cover by getting the two sites confused and “connect”ing to and commenting on the wrong one… I wonder if at around the same time there’s some post on the “other” site talking about whatever current scammy crime they talk about where this “Connect” guy also just breaks in and makes some overtly “white-hat” comment about being pro-2FA and Zero Trust and agreeing with Schneier about encryption or better yet however he would naturally have tried to convey “watch out for those darn scammers!” LOL It’s like he XSSd his own damn self…
Brian you truly have been an inspiration to me… As a professional software developer who spent 25 years building software to try to make life a little easier for people, I had become, up until a few months ago, so fed-up and dismayed with the state of cybersecurity and how it has impacted my whole industry (nay, planet) that I was ready to just give it all up completely and clean vet kennels or something (at least that would involve less s#!t). It was in one of my darkest moments when I was wrangling with my own horrifically persistent home networking botnet/C&C/rootkit/whatever mess that I finally ran across one of your Washington Post articles, got sucked in, read about what you’re all about and have been hooked ever since. I swear it was you and Schneier who saved my possibly my career and probably my sanity that same day.
And of course I did figure out what I should have known all along (since I did support Windows 1.0 for Dell Corporate in 1991), that the main root of all my networking/device problems turned out to be Windows 10 Home (dead smack in the middle of the Build 1803 days) – since we all know that Microsoft has been peddling the same cobbled-together DOS 3.3 code that they got sued for containing so many illegally undocumented and yet oh-so-powerful so functions. And exactly because of my experience I will freely and fairly hand out blame for our current security fiasco out to all the other major hardware and OS manufacturers too – Intel, Apple, AMD, Google, FaceBook, Sprint, TMobile, Spectrum/Time Warner, Samsung, Huweii, LG, Charter, Comcast, HP – all of ’em for being more concerned about stock prices and market share and stuffing unnecessary, unwelcome and often immature new features down our throats causing project scope creep and rushed SDLC timelines that do not include ample security design and testing.
So Brian thanks (I think LOL) to you and Schneier I have had my vigor for the industry restored but now applying it completely in the direction of security analysis/engineering to do what I can to help fight the good fight.
Thanks again Brian, you are indeed possibly the Internet’s first bonafide CyberHero!!!
BTW For anybody who does not get any of the allusions I made here in total jest and/or do not yet know or truly appreciate who Brian Krebs really is and stands for I implore you to read https://krebsonsecurity.com/2016/09/krebsonsecurity-hit-with-record-ddos/
And for anybody who does not know what Google Project Shield did not just for KrebsOnSecurity.com and Mr. Krebs but for all journalists worldwide – and the institution of journalism itself – from technological censorship imposed (via DDoS in this particular case) by any political, corporate, organizational and/or private entity to cause denial of free speech and/or suppression, subversion, domination, obfuscation or corruption of the truth.
Krebs and Schneier. Two people whose blogs I check almost daily.
Aww, thanks. That’s high praise!
me too, I think I have never missed a single article . Thanks krebs, I hate you sometimes cause you little zionist RAT but love your articles.
Brain, please! You’re going to make his head explode.
Yea Baby, yer on it, check out the time and date stamp. 🙂
Want a surefire way to get a CC # every time?
Pull out your wallet, look for a card with either a VISA, Mastercard or Amex logo. Bingo bango bongo. If you need the CVV that’s also easy. Just flip the card over. #ThumbsUp
I tried that, but it stopped working after the 47th iPhone.
Ain’t nothin’ as funny as a stupid criminal. Thanks for giving all your session data to Brian and to Google. 😉
Do we know wht the entry mode would be? On file, manually entered, keyed? TY
I would expect that the entry mode would be “01” with cardholder presence code = 0, but the article is a little vague on it was Card Not Present. I do not know many stores that can do CNP from the check out lanes unless they are doing it from customer service for a special order, or pick up which of course would be entry mode 81.
Yes, it comes through as ’01’ manually keyed without the ecom flag.
This is either a sublime troll or a criminal who is only temporarily not in custody.
Not a big fan of China-Mart ( A.K.A. Wal-mart) they place way to much emphasis on retail theft and watching people , then doing anything serious about stopping credit card fraud.
RE: Walmart not stopping credit card fraud. There was a case a few years back where a wealthy business person had his cards canceled while on vacation because he purchased something from Walmart. Probably just a coincidence.
The title of the article DOES make it sound like a “how-to” guide on encoding credit card numbers on a barcode. I wonder how many disappointed crooks will find it.
I did a software project for a major bank a few years ago. I was required to take an online course on how to identify money laundering. It was a really good introduction on how to launder money without getting caught. I never applied what I learned, however.
Exactly this. Along those same lines, “in order to catch a hacker, you have to think like a hacker.” It’s not about the knowledge you have, but the wisdom you have in applying it (err… not applying it).
That sounds like those courses businesses send their employees to, that, instead of teaching the employees how to avoid sexual harassment situations, concentrate on how to fabricate evidence and file a lawsuit against their employer.
When I pointed this out to several of the management layers involved with the process, they claimed to have no idea what I was talking about. Though I did note that if they were taking any classes, they weren’t the ones the rest of us were attending.
I expect they reaped what they sowed, there…
That is a classic case of the strong tone from the top not echoing to the bottom. I literally just had a webinar with an InfoSec group yesterday that was performing some new techniques to undisguise, and catch footprints using a variety of tools with repos on Kali and some that can be used on Win/Mac. It is highly likely dependent on the legalities we will be using some of these techniques. We do POCs to emulate criminals quite frequently alike to pen testing alongside with our vendors. You really can’t afford not to or you will find yourself as a cover story on Krebs or worse when you look at the amount of money you lost, or data compromised.
“criminal organizations of Asian descent”
Well, not only is that not helpful, but it could be regarded as racist. What Asian? Russian, Chinese, Mongolian, Indian, Thai, etc. It might as well be African, or European.
Yes, all of them.
Wutang Financial aint nothing to mess with
You, sir, win the internet!
No. Derivative crap wins nothing.
Can we stop with all this “racist” crap? My gosh, you can’t even say the words Asian, Black, or Mexican anymore without some moron getting offended. How about you grow a pair, Dave?
If the crooks have PAN, CVV and expiration, why not just imprint and encode a magstripe card? Are they missing fields they need for track1/track2 or is there some other reason for crafting their own format of card?
This is the reason (mentioned in the article):
“As a result of this emerging trend, instead of finding a large number of re-encoded credit cards during a search, a subject may only possess stickers or cards with barcodes that contain stolen card data”
They’re using CNP credentials – so CVV2 – not magstripe data with CVV. The article doesn’t seem to differentiate the two but that’s how it comes through.
Not using one of those Walmart cards, I have to say I don’t get the scam. Are the crooks making their own barcode?
At Walmart the clerk never touches my credit card (bank issued). In fact I try to never use a clerk. I go to the self check out.
If you think you are safe with the self-checkout lanes, think again.
At the Home Depot breach some time back, the self-checkout lanes were affected. They installed a program there to grab the card data.
not to mention Kreb’s has a piece on phony terminal covers on walmart terminals at the self check out from a yer or two ago,
If only there was something in the merchant services chain that detected no chip was present and rejected the card… This is only plausible by laziness of the merchant and their payment processor.
As stated in the article, the transactions are considered card-not-present – meaning no chip is expected or even applicable.
I think this boils down to “know your procedures” and “follow your procedures”. The cashier not being familiar with this form of payment should have engaged a supervisor who hopefully would have known better.
This is bizarre… a POS system that allows for CNP transaction scanning card data in clear from a barcode? After all discussions on EMV, PCI DSS, P2PE? It’s like locking the window and keeping the door wide open – and complaining someone got in…
Interesting. Dry, good article, nice catch Krebs. Re-encoding a refund card, neat. So will refund cards are now suspect.
Actually, with the new chips present, all cards should and could be suspect, not just the mag stripe. There is nothing to stop a recoded chip card. And, that’s not a personnel training issue, or a lazy procedure issue, it’s a theft issue.
This one easiest resolution point, put a cash register with money in customer service, and eliminate the refund card. But that means staffing one more position. Not a Walmart idea.
“There is nothing to stop a recoded chip card” False.
Last year December I was contacted by a broker who convinced me to invest into Cryptoallday. I made an initial investment of € 190,00 and they asked for € 14,500 more in order to access my withdrawal. I followed their instructions and made another deposit. For 2 months now I have been trying to contact Cryptoallday but I got no response. I talked to my friends and colleagues about it and luckily for me a friend of mine just got out of a situation like that and introduced to a wealth recovery team that helped her during her investment problem, within 3 days of contacting them they were able to help me get 100% of my lost money back. They only got paid after the recovery and I had no problem with giving them 10% from the recovered funds after I got it back. You can reach out to them for more insight.
Bitcoinretrieval2018 gmail com / WhatsApp: +1 (347)201-0316
Great article. Thanks for the detailed information. Your blog is by far the best source I’ve found.
Do anybody deal with pros?
How common is it that the government not investigate human trafficking, that involves police all throughout the state? What started this was my attempted public murder in 37160, this neglagance has led to Tennessee’s infrastructure being infiltrated and access sold to the highest bidder. For what? Harassment and ongoing oppression of “James Sandoval”. How did this occur? They framed me setting me up illegally in 2004, pooled money to frame me as A sexual predator, and even used doppelgangers to collect this pooled money, using scamming to skim everyone’s paychecks, promising millions in return. At this moment ‘heritage south community credit union’ along with all the banks in TN have used NTP vulns to hold the internet back for at least 10 years. I have been tormented for 4 long years, ID stolen and after investigating what I could, its human trafficking hidden in “crisis acting”, all possible for hate crimes against me and every other poverty stricken individual. Now they have been infiltrating the gov, moving spies into Tennessee, german-russian intel.