The U.S. Justice Department today unsealed indictments against four Chinese officers of the People’s Liberation Army (PLA) accused of perpetrating the 2017 hack against consumer credit bureau Equifax that led to the theft of personal data on nearly 150 million Americans. DOJ officials said the four men were responsible for carrying out the largest theft of sensitive personal information by state-sponsored hackers ever recorded.
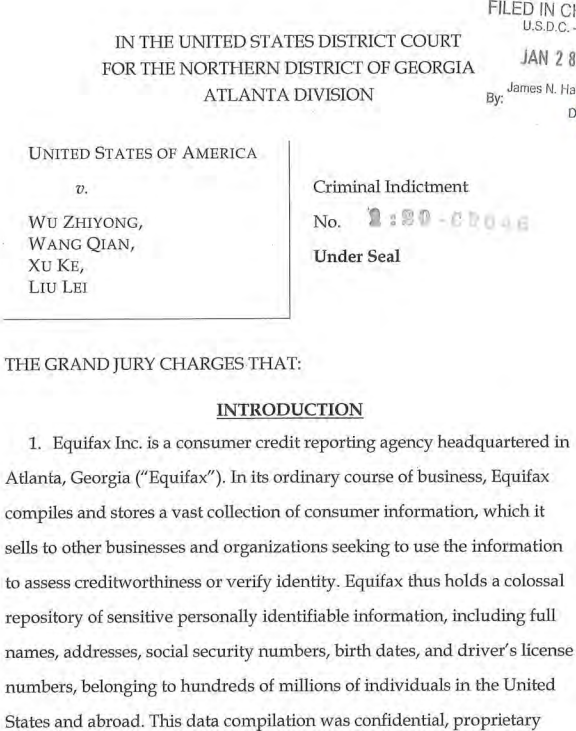 The nine-count indictment names Wu Zhiyong (吴志勇), Wang Qian (王乾), Xu Ke (许可) and Liu Lei (刘磊) as members of the PLA’s 54th Research Institute, a component of the Chinese military. They are each charged with three counts of conspiracy to commit computer fraud, economic espionage and wire fraud.
The nine-count indictment names Wu Zhiyong (吴志勇), Wang Qian (王乾), Xu Ke (许可) and Liu Lei (刘磊) as members of the PLA’s 54th Research Institute, a component of the Chinese military. They are each charged with three counts of conspiracy to commit computer fraud, economic espionage and wire fraud.
The government says the men disguised their hacking activity by routing attack traffic through 34 servers located in nearly 20 countries, using encrypted communications channels within Equifax’s network to blend in with normal network activity, and deleting log files daily to remove evidence of their meanderings through the company’s systems.
U.S. Attorney General Bill Barr said at a press conference today that the Justice Department doesn’t normally charge members of another country’s military with crimes (this is only the second time the agency has indicted Chinese military hackers). But in a carefully worded statement that seemed designed to deflect any criticism of past offensive cyber actions by the U.S. military against foreign targets, Barr said the DOJ did so in this case because the accused “indiscriminately” targeted American civilians on a massive scale.
“The United States, like other nations, has gathered intelligence throughout its history to ensure that national security and foreign policy decision makers have access to timely, accurate and insightful information,” Barr said. “But we collect information only for legitimate national security purposes. We don’t indiscriminately violate the privacy of ordinary citizens.”
FBI Deputy Director David Bowdich sought to address the criticism about the wisdom of indicting Chinese military officers for attacking U.S. commercial and government interests. Some security experts have charged that such indictments could both lessen the charges’ impact and leave American officials open to parallel criminal allegations from Chinese authorities.
“Some might wonder what good it does when these hackers are seemingly beyond our reach,” Bowdich said. “We answer this question all the time. We can’t take them into custody, try them in a court of law and lock them up. Not today, anyway. But one day these criminals will slip up, and when they do we’ll be there. We in law enforcement will not let hackers off the hook just because they’re halfway around the world.”
The attorney general said the attack on Equifax was just the latest in a long string of cyber espionage attacks that sought trade secrets and sensitive data from a broad range of industries, and including managed service providers and their clients worldwide, as well as U.S. companies in the nuclear power, metals and solar products industries.
“Indeed, about 80 percent of our economic espionage prosecutions have implicated the Chinese government, and about 60 percent of all trade secret thefts cases in recent years involved some connection with China,” he said.
The indictments come on the heels of a conference held by US government officials this week that detailed the breadth of hacking attacks involving the theft of intellectual property by Chinese entities.
“The FBI has about a thousand investigations involving China’s attempted theft of U.S.-based technology in all 56 of our field offices and spanning just about every industry and sector,” FBI Director Christopher Wray reportedly told attendees at the gathering in Washington, D.C., dubbed the “China Initiative Conference.”
At a time when increasingly combative trade relations with China combined with public fears over the ongoing Coronavirus flu outbreak are stirring Sinophobia in some pockets of the U.S. and other countries, Bowdich was quick to clarify that the DOJ’s beef was with the Chinese government, not its citizenry.
“Our concern is not with the Chinese people or with the Chinese American,” he said. “It is with the Chinese government and the Chinese Communist Party. Confronting this threat directly doesn’t mean we should not do business with China, host Chinese students, welcome Chinese visitors or co-exist with China as a country on the world stage. What it does mean is when China violates our criminal laws and international norms, we will hold them accountable for it.”
A copy of the indictment is available here.
ANALYSIS
DOJ officials praised Equifax for their “close collaboration” in sharing data that helped investigators piece together this whodunnit. Attorney General Barr noted that the accused not only stole personal and in some cases financial data on Americans, they also stole Equifax’s trade secrets, which he said were “embodied by the compiled data and complex database designs used to store personal information.”
While the DOJ’s announcement today portrays Equifax in a somewhat sympathetic light, it’s important to remember that Equifax repeatedly has proven itself an extremely poor steward of the highly sensitive information that it holds on most Americans.
Equifax’s actions immediately before and after its breach disclosure on Sept 7, 2017 revealed a company so inept at managing its public response that one couldn’t help but wonder how it might have handled its internal affairs and security. Indeed, Equifax and its leadership careened from one feckless blunder to the next in a series of debacles that KrebsOnSecurity described at the time as a complete “dumpster fire” of a breach response.
For starters, the Web site that Equifax set up to let consumers check if they were affected by the breach consistently gave conflicting answers, and was initially flagged by some Web browsers as a potential phishing site.
Compounding the confusion, on Sept. 19, 2017, Equifax’s Twitter account told people looking for information about the breach to visit the wrong Web site, which also was blocked by multiple browsers as a phishing site.

And two weeks after its breach disclosure, Equifax began notifying consumers of their eligibility to enroll in free credit monitoring — but the messages did not come from Equifax’s domain and were in many other ways indistinguishable from a phishing attempt.
It soon emerged the intruders had gained access to Equifax’s systems by attacking a software vulnerability in an Internet-facing server that had been left unpatched for four months after security experts warned that the flaw was being broadly exploited. We also learned that the server in question was tied to an online dispute portal at Equifax, which the intruders quickly seeded with tools that allowed them to maintain access to the credit bureau’s systems.
This is especially notable because on Sept. 12, 2017 — just five days after Equifax went public with its breach — KrebsOnSecurity broke the news that the administrative account for a separate Equifax dispute resolution portal catering to consumers in Argentina was wide open, protected by perhaps the most easy-to-guess password combination ever: “admin/admin.”

A partial list of active and inactive Equifax employees in Argentina. This page also let anyone add or remove users at will, or modify existing user accounts.
Perhaps we all should have seen this megabreach coming. In May 2017, KrebsOnSecurity detailed how countless employees at many major U.S. companies suffered tax refund fraud with the IRS thanks to a laughably insecure portal at Equifax’s TALX payroll division, which provides online payroll, HR and tax services to thousands of U.S. firms.

Equifax’s TALX — now called Equifax Workforce Solutions — aided tax thieves by relying on outdated and insufficient consumer authentication methods.
In October 2017, KrebsOnSecurity showed how easy it was to learn the complete salary history of a large portion of Americans simply by knowing someone’s Social Security number and date of birth, thanks to yet another Equifax portal.
Around that same time, we also learned that at least two Equifax executives sought to profit from the disaster through insider trading just days prior to the breach announcement. Jun Ying, Equifax’s former chief information officer, dumped all of his stock in the company in late August 2017, realizing a gain of $480,000 and avoiding a loss of more than $117,000 when news of the breach dinged Equifax’s stock price.
Sudhakar Reddy Bonthu, a former manager at Equifax who was contracted to help the company with its breach response, bought 86 “put” options in Equifax stock on Sept. 1, 2017 that allowed him to profit when the company’s share price dropped. Bonthu was later sentenced to eight months of home confinement; Ying got four months in prison and one year of supervised release. Both were fined and/or ordered to pay back their ill-gotten gains.
While Equifax’s stock price took a steep hit in the months following its breach disclosure, shares in the company [NYSE:EFX] gained a whopping 50.5% in 2019, according to data from S&P Global Market Intelligence.
KrebsOnSecurity has long maintained that the 2017 breach at Equifax was not the work of financially-motivated identity thieves, as there has been exactly zero evidence to date that anything close to the size of the data cache stolen from that incident has shown up for sale in the cybercrime underground.
However, readers should understand that there are countless other companies with access to SSN, DOB and other information crooks need to apply for credit in your name that get hacked all the time, and that this data on a great many Americans is already for sale across various cybercrime bazaars.
Readers also should know that while identity theft protection services of the kind offered by Equifax and other companies may alert you if crooks open a new line of credit in your name, these services generally do nothing to stop that identity theft from taking place. ID theft protection services are most useful in helping people recover from such crimes.
As such, KrebsOnSecurity continues to encourage readers to place a freeze on their credit files with Equifax and the other major credit bureaus. This process puts you in control over who gets to grant credit in your name. Placing a freeze is now free for all Americans and their dependents. For more information on how to do that and what to expect from a freeze, please see this primer.




“Bowdich was quick to clarify that the government’s beef was with the Chinese government, not its citizenry”
Exactly. This action is likely more about this “beef” than the data breach itself.
The whole Justice Department press conference today was a big show of nothing, it was all talk, nobody has been arrested , these four Chinese Military Officers will never be prosecuted.
It does mean, however, that the indicted persons will probably never be able to travel outside the PRC without fear of getting nicked and then extradited to the U.S.
No Paris, no Rome, no London, no Sydney, etc. Hope they like vacations in Wuhan.
You mean countries that don’t have extradition treaties with the United States They could always vacation in North Korea or Russia !
prosecution was not the point – there’s evidence of chinese hacking going back 20 years, mostly classified, we disclosed them, that was the point…
Don’t forget Equifax’s insane move to no longer require PINs to unfreeze accounts
A recent direct Equifax statement: “In an effort to enhance the security of consumer data, we changed how we authenticate consumers before we disclose any information or make any changes on their credit file. As a part of these enhancements, a specific PIN number is no longer required.”
https://krebsonsecurity.com/2019/03/myequifax-com-bypasses-credit-freeze-pin/
You’re right, and their “authentication” method requires me to send them a physical letter through the U.S. Post Office, just to thaw the freeze I have in place. Thanks Equifax!
I recently did a temporary Equifax unfreeze online–no USPS involved. But, I’ve seen a Equifax error message that I seem to recall as persistent years now, having to retry login multiple times before getting past the error message.
Excellent article. This is the first time ” Barr” has had to do part of his actual job. He may be worth his keep after all. Dang. So far, China, and Russians, have been charged. No Ukrainian. And a bunch of Americans.
Barr didn’t do jack. He’s only in that job to run distraction for Donnie Traitor. Anything else that happens is entirely secondary. This had nothing to do with him except announcing it because he’s the huge-headed liar atop the dept. His job is looking the other way but of course he’d be happy to take credit you would mistakenly give him as if he had done his job at any point here. Charging Chinese Army officers is a political act without actual teeth.
Of course China’s PLA is behind some big % of the hacks. If Barr felt they somehow benefitted his boss politically, he’d be running distraction and cover for them too. He’s a traitor.
The people the US Govmint (I know it’s misspelled) ought to be going after are the f-ing morons who run/ran Equifax. They’re the ones who are guilty for putting all that data at risk in the 1st place, and they’re the ones who ought to be in jail. The Chinese will never go to jail, unless, like some other miscreants, they are stupid enough to step onto the soil of a country that has an extradition treaty with the US, in which case they get what they deserve (extradited…).
“ought to be going after are the f-ing morons who run/ran Equifax”
Absolutely not! We simply cannot have a reduction in the bribery… uh, I mean “free speech” donations of campaign funds.
While Equifax is not innocent in all this, you are blaming the victim. Lets say I forgot to lock my car. Someone then steals it. Are they not STILL guilty of theft? Are they still not criminals who deserve to be charged, even if they ran off to Mexico? Lets not lose sight of the fact that Equifax was the victim of criminals. It may have been facilitated by their own ineptitude, but just because im incompetent doesnt mean people can freely steal from me and not get charged with theft.
Except in the case of Equifax they hoovered up the non public personal information of hundreds of millions of American consumers and then left it laying about unsecured. In your scenario if you had filled up your car with unencrypted credit card numbers you would have committed a PCI violation when the thieves broke in and stole the unsecured data you left laying about.
Expecting companies to uphold their obligations of confidentiality is NOT victim blaming.
Gross criminal negligence at least, is what I call it.
Anyone who runs Linux servers knows you have to keep the Apache Struts servers updated and patched – or any server for that matter! I’m a lot more angry at Equifax than I am at the Chinese – everyone also knows the PRC has been attacking our economy for decades, and should know better than to sit on their thumbs when it comes to IT security.
The victim is the people’s data Equifax failed to safe guard. Imagine, I collect your data with out your consent, store it on a laptop, leave it in an unlocked car in a bad neighborhood, and it gets stolen. I am going to a angry with the idiots who left the data to be stolen more than the thief. Equifax should have known better.
— “We in law enforcement will not let hackers off the hook just because they’re halfway around the world.”
This may sound stupid (plus I haven’t had my coffee yet), but I’ve always wondered with the surge of bug bounties (i.e., crowd-sourced hacking) if they would do something similar such as crowd-sourced law enforcement assisting. Almost like a hackers-hacking-hackers thing, but to solely aid law enforcement. For example, in the case mentioned by Bowdich, if they’re halfway around the world, why not have a platform to have white-hat hackers “take to the streets” so to speak and help to take them down. Of course, there would be laws and regulations to abide by, but it would have incentives similar to bug bounties. Maybe I need to go hit the coffee pot…
“crowd-sourced law enforcement”
That’s called vigilanteism or posse comitatus.
Someone’s been watching “don’t F&#k with Cats” on Netflix.
I think another interesting part of the article was where the miscreants appear to use TOR but still got fingered. That goes to show that TOR was created by the US Navy and therefore the US government has the ability to see who is using it and where they are from. It may be a conspiracy theory but its hard to believe that your ever really anonymous on the internet even if you use TOR.
Tor provides anonymity but not invisibility – an adversary who can see traffic on both ends will eventually correlate activity on the source and destination side and thus unmask.
My understanding is TOR reduces the likelihood for tracing actions and data back to the user–TOR provides anonymity up to a point.
Acorn, you are correct. If you can control multiple TOR relays and entry/exit nodes you can analyze the traffic you are decrypting at each relay or node. This allows you to begin correlating the data you decrypt at each step in order to build traffic/route patterns, identify who the source host is, where they are located, where they are trying to go, and other additional information to help fingerprint and identify exactly who you are dealing with. Below is some high level information from the TOR Project to help readers who may not be as technical or educated about TOR that will help them understand my comments above.
(From the TOR Project) Onion routing is implemented by encryption in the application layer of a communication protocol stack, nested like the layers of an onion. Tor encrypts the data, including the next node destination IP address, multiple times and sends it through a virtual circuit comprising successive, random-selection Tor relays. Each relay decrypts a layer of encryption to reveal the next relay in the circuit to pass the remaining encrypted data on to it. The final relay decrypts the innermost layer of encryption and sends the original data to its destination without revealing or knowing the source IP address.
The US government doesnt have some special ability to unmask TOR, that just a silly conspiracy theory. The CIA does own quite a large number of exit nodes though, allowing them to correlate traffic, something just about anyone with enough resources and access to the infrastructure could do. Something other governments are also likely doing.
If the PLA put the Equifax records into a database and only issued queries against “legitimate” intelligence targets would they still be “indiscriminately” targeting American civilians on a massive scale? Compare XKeyscore.
XKeyscore is/was by definition not indescriminate. Words have meaning, try again.
Equifax = fin data = everybody’s detailed info and nothing else. That info then gets rolled into phishing to spoof credentials for the theft/disruption, penny-ante Beijing economic gamesmanship because their economy (and culture) is based on theft.
XKeyscore = actual intrique metrics get you placed higher in observation queues. Depending on what they see, different things happen or don’t. Most folks are 100% unaffected by it.
People who fit certain XKdata profiles got looked at more carefully, which is every system if you drill down to it. There is no sovereign “right” to the unimpeded internet, not anywhere in the “free” world and combing metadata for legitimate security threats is still a legitimate security concern.
Obviously that’s a far cry from stealing the credit histories of millions of civilians en masse to use against the host nation in a targeted disinformation/influence/cybercrime/disruption campaign which China does 100,000 times per hour. That’s not defensive or particularly targeting a legitimate security threat. You’re conflating very different things that have one commonality.
If you wanted a better example of the type of wide bycatch targeting just anything, https://www.darkreading.com/threat-intelligence/cias-secret-ownership-of-crypto-ag-enabled-extensive-espionage/d/d-id/1337016
What is ultimately done with the data/intel makes a big difference. China = kleptocracy and cybercrime. Until you get a phishing email from the CIA you’re comparing apples and cattle.
Terrible comparison, try again.
XKeyscore is individual traffic-based analysis. That data doesn’t get rolled into criminal groups’ cybertheft campaigns, and just the fact that your data was being back-end categorized for sensitive security purposes doesn’t mean it’s able to be used against you by a 3rd party.
Not the case with a huge broad trove of financial data, especially as the PLA just gives it directly to their APT groups for attacks. The comparison is pretty specious.
If the US were using Xkeyscore to send broad phishing campaigns against average Chinese citizens to trick them out of their financial credentials with a theft motive, you’d be less out in left field there.
Equifax hack?…how convenient: KNEEE-how! ;-/
The hackers also stole Equifax’s trade secrets of their use of the login “admin/admin”.
Combining the Experian data and the OPM data (2014), China now has a very detailed information on most every person in the US government.
Also, remember that in August of 2017, the FBI arrested Yu Pingan, a Chinese national, as he arrived in the US to attend a conference. He was charged with something related to the OPM breach.
https://www.transunion.com/china
TransUnion, one of the “big three” along with Equifax and Experian, is Chinese-owned and operated.
Very militaristic and mercantilist.
We don’t “own” a thing in America anymore. We “owe” them for all that stuff “made in China” that we buy on credit.
Was Jun Ying working with the Chinese? It’s hard not to notice his ethnicity or the fact that he was personally invested in a Chinese company (Meritsoft, in Wuhan of all places!).
Perhaps espionage.