Microsoft warned on Wednesday that malicious hackers are exploiting a particularly dangerous flaw in Windows Server systems that could be used to give attackers the keys to the kingdom inside a vulnerable corporate network. Microsoft’s warning comes just days after the U.S. Department of Homeland Security issued an emergency directive instructing all federal agencies to patch the vulnerability by Sept. 21 at the latest.
DHS’s Cybersecurity and Infrastructure Agency (CISA) said in the directive that it expected imminent exploitation of the flaw — CVE-2020-1472 and dubbed “ZeroLogon” — because exploit code which can be used to take advantage of it was circulating online.
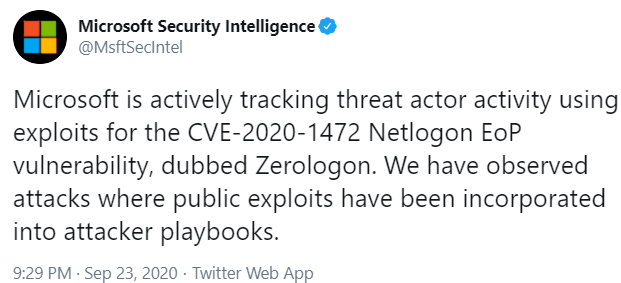
Last night, Microsoft’s Security Intelligence unit tweeted that the company is “tracking threat actor activity using exploits for the CVE-2020-1472 Netlogon vulnerability.”
“We have observed attacks where public exploits have been incorporated into attacker playbooks,” Microsoft said. “We strongly recommend customers to immediately apply security updates.”
Microsoft released a patch for the vulnerability in August, but it is not uncommon for businesses to delay deploying updates for days or weeks while testing to ensure the fixes do not interfere with or disrupt specific applications and software.
CVE-2020-1472 earned Microsoft’s most-dire “critical” severity rating, meaning attackers can exploit it with little or no help from users. The flaw is present in most supported versions of Windows Server, from Server 2008 through Server 2019.
The vulnerability could let an unauthenticated attacker gain administrative access to a Windows domain controller and run an application of their choosing. A domain controller is a server that responds to security authentication requests in a Windows environment, and a compromised domain controller can give attackers the keys to the kingdom inside a corporate network.
Scott Caveza, research engineering manager at security firm Tenable, said several samples of malicious .NET executables with the filename ‘SharpZeroLogon.exe’ have been uploaded to VirusTotal, a service owned by Google that scans suspicious files against dozens of antivirus products.
“Given the flaw is easily exploitable and would allow an attacker to completely take over a Windows domain, it should come as no surprise that we’re seeing attacks in the wild,” Caveza said. “Administrators should prioritize patching this flaw as soon as possible. Based on the rapid speed of exploitation already, we anticipate this flaw will be a popular choice amongst attackers and integrated into malicious campaigns.”




Appreciate that 2008R2 is out of support, but MS should be making an exception with this particular flaw – they’ve done so in the past, and they don’t get much worse than this.
Apparently getting people to pay for Extended Security Updates is more important than security. I understand that OS’s have to EOL at some point. But I think this bug was patched a mere 7 months after 2008 R2 went EOL. A fix to something as serious as easily getting Domain Admin credentials seems like it would be released free.
…20 years after it was released? 20 years. really?…
…10 years…
0patch has a micropatch for Zerologon on Windows Server 2008 R2 – https://blog.0patch.com/2020/09/micropatch-for-zerologon-perfect.html
Read the CVE. Windows 7 / Windows Server 2008 R2 patch (4571729) has already been released since 8/11/2020.
you can’t install it unless you have the ESU MAK key purchased and you have to have an Enterprise Agreement to be able to get it. if you don’t have ESU, the KB4571729 will fail to install.
I think you mean 4571719
do you know if windows xp source code really leaked?
https://boards.4channel.org/g/thread/77879263
https://boards.4channel.org/g/thread/77874231
My software tells me daily that null sessions are enabled on my computer and malware can be installed. I have a malware program but this keeps happening
So does this vulnerability impact any server running 2008-2019 or just DC’s?
This is the real question. Do I have 4 servers I need to immediately patch or 40?
“…The flaw is present in most supported versions of Windows Server, from Server 2008 through Server 2019…”
https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2020-1472
Server 2008 R2? easy fix. First install Servicing Stack Update KB4565354, no restart required, then install Security Monthly Rollup KB4571729. Restart. Done.
Steven – are you saying you can install those two updates without ESU?
and is that all that is required? one site said the patch only allows you to monitor for issues and then manually fix after patch is installed.
All of our Domain Controllers running 2008 R2 (without extended support) fail and then roll back when applying the patch, regardless of what pre-reqs we install first. When researching the error I stumbled across this gem from Microsoft’s support site regarding their patch:
“This is expected in the following circumstances:
If you are installing this update on a device that is running an edition that is not supported for ESU”
Yeah… not cool.
This mirrors my experience. Totally uncool whether or not the peanut gallery applies their value judgements to it or not. This vulnerability could have just as easily appeared 8 months ago when we were still getting updates so it’s MS responsibility to patch it based on it’s severity.
Download the latest version of windows
Hello Team,
Please confirm CVE-2020-1472 vulnerability need to patch on DC server only or all server as well as windows endpoints