In February, KrebsOnSecurity wrote about a novel cybercrime service that helped attackers intercept the one-time passwords (OTPs) that many websites require as a second authentication factor in addition to passwords. That service quickly went offline, but new research reveals a number of competitors have since launched bot-based services that make it relatively easy for crooks to phish OTPs from targets.

An ad for the OTP interception service/bot “SMSRanger.”
Many websites now require users to supply both a password and a numeric code/OTP token sent via text message, or one generated by mobile apps like Authy and Google Authenticator. The idea is that even if the user’s password gets stolen, the attacker still can’t access the user’s account without that second factor — i.e. without access to the victim’s mobile device or phone number.
The OTP interception service featured earlier this year — Otp[.]agency — advertised a web-based bot designed to trick targets into giving up OTP tokens. This service (and all others mentioned in this story) assumes the customer already has the target’s login credentials through some means.
OTP Agency customers would enter a target’s phone number and name, and then the service would initiate an automated phone call that alerts that person about unauthorized activity on their account. The call would prompt the target to enter an OTP token generated by their phone’s mobile app (“for authentication purposes”), and that code would then get relayed back to the bad guy customers’ panel at the OTP Agency website.
OTP Agency took itself offline within hours of that story. But according to research from cyber intelligence firm Intel 471, multiple new OTP interception services have emerged to fill that void. And all of them operate via Telegram, a cloud-based instant messaging system.
“Intel 471 has seen an uptick in services on the cybercrime underground that allow attackers to intercept one-time password (OTP) tokens,” the company wrote in a blog post today. “Over the past few months, we’ve seen actors provide access to services that call victims, appear as a legitimate call from a specific bank and deceive victims into typing an OTP or other verification code into a mobile phone in order to capture and deliver the codes to the operator. Some services also target other popular social media platforms or financial services, providing email phishing and SIM swapping capabilities.”
Intel471 says one new Telegram OTP bot called “SMSRanger” is popular because it’s remarkably easy to use, and probably because of the many testimonials posted by customers who seem happy with its frequent rate of success in extracting OTP tokens when the attacker already has the target’s “fullz,” personal information such as Social Security number and date of birth. From their analysis:
“Those who pay for access can use the bot by entering commands similar to how bots are used on popular workforce collaboration tool Slack. A simple slash command allows a user to enable various ‘modes’ — scripts aimed as various services — that can target specific banks, as well as PayPal, Apple Pay, Google Pay, or a wireless carrier.
Once a target’s phone number has been entered, the bot does the rest of the work, ultimately granting access to whatever account has been targeted. Users claim that SMSRanger has an efficacy rate of about 80% if the victim answered the call and the full information (fullz) the user provided was accurate and updated.”
Another OTP interception service called SMS Buster requires a tad more effort from a customer, Intel 471 explains:
“The bot provides options to disguise a call to make it appear as a legitimate contact from a specific bank while letting the attackers choose to dial from any phone number. From there, an attacker could follow a script to trick a victim into providing sensitive details such as an ATM personal identification number (PIN), card verification value (CVV) and OTP, which could then be sent to an individual’s Telegram account. The bot, which was used by attackers targeting Canadian victims, gives users the chance to launch attacks in French and English.”
These services are springing up because they work and they’re profitable. And they’re profitable because far too many websites and services funnel users toward multi-factor authentication methods that can be intercepted, spoofed, or misdirected — like SMS-based one-time codes, or even app-generated OTP tokens.
The idea behind true “two-factor authentication” is that the user is required to present two out of three of the following: Something they have (mobile devices); something they know (passwords); or something they are (biometrics). For example, you present your credentials to a website, and the site prompts you to approve the login via a prompt that pops up on your registered mobile device. That is true two-factor authentication: Something you have, and something you know (and maybe also even something you are).
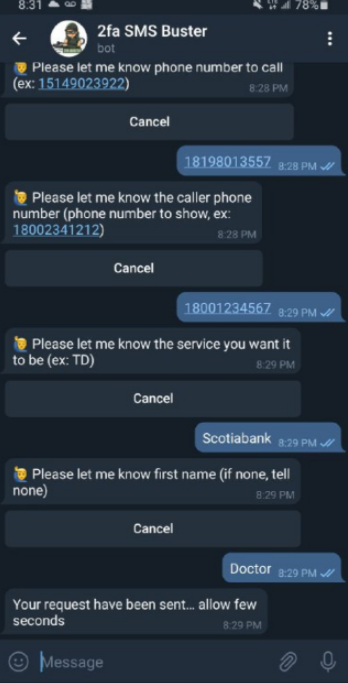
The 2fa SMS Buster bot on Telegram. Image: Intel 471.
In addition, these so-called “push notification” methods include important time-based contexts that add security: They happen directly after the user submits their credentials; and the opportunity to approve the push notification expires after a short period.
But in so many instances, what sites request is basically two things you know (a password and a one-time code) to be submitted through the same channel (a web browser). This is usually still better than no multi-factor authentication at all, but as these services show there are now plenty of options of circumventing this protection.
I hope these OTP interception services make clear that you should never provide any information in response to an unsolicited phone call. It doesn’t matter who claims to be calling: If you didn’t initiate the contact, hang up. Don’t put them on hold while you call your bank; the scammers can get around that, too. Just hang up. Then you can call your bank or whoever else you need.
Unfortunately, those most likely to fall for these OTP interception schemes are people who are less experienced with technology. If you’re the resident or family IT geek and have the ability to update or improve the multi-factor authentication profiles for your less tech-savvy friends and loved ones, that would be a fabulous way to show you care — and to help them head off a potential disaster at the hands of one of these bot services.
When was the last time you reviewed your multi-factor settings and options at the various websites entrusted with your most precious personal and financial information? It might be worth paying a visit to 2fa.directory (formerly twofactorauth[.]org) for a checkup.




I’m confused how this works. Does the criminal already have the username and password of the victim? They enter that and then when prompted for the sms code, they use this app to call the victim?
Yes
My question for background would be what is Telegram saying or doing about it?
While Telegram is a useful tool I feel they can’t control the beast they created. I have seen more moderation on the DN. Until they have an incentive to control the actions they will not. Any attempt to police their service could cause a drop in users and break off from what they wanted to create.
That’s the Facebook/AWS paradigm of it, they need to wise up.
If it violates the EULA they have to go away, there must be rules.
It follows that market share is probably not greatly improved
by allowing criminal groups to operate scams on a platform
-after that becomes widely reported on and known at least.
OTP codes are good for 1 minute and the bad guy would have between 1 and 59 seconds to apply that factor to the login before it rotates to the next code. Seems like an awfully narrow window with a huge chance of failure.
It takes a few milliseconds for the automated computer programs to login and transfer the funds. Do you think it’s like the movie’s where some kid spends time in front of the computer hacking away? You are WAY behind. The program is written the hack is done on several accounts at a time. It’s not like War Games, that takes too much time.
Are you just pulling this out of your arse?
A lot of people using OTP Bots are manually entering and transferring the funds.
Ugh, a one-minute window to grab the right device, fumble with an app, then type in the code? What even is the max operational ping of the services that are delivering the code?
My bank had set a ten-minute window on confirming email. …It got to the point that their email service wouldn’t even send the email in ten minutes. Let alone it get to my email service and then picked up by my client, read by me, and then replied to.
They are always already on the phone with the victim. The fraudster tells the victim to expect a verification code.
So when the SMS message comes in, it’s literally only a few seconds for the victim to tell the scammer the code over the phone, and for that scammer to type it in
Exactly right. That story I linked at the end of the piece about the security pro who got hoodwinked because he didn’t count on the fact that the fraudsters were already on the phone with his bank impersonating him. When he put the fraudsters on hold to call his bank and ask if they were already in a conversation with him, they said yes. Because from their vantage point, that was true. But they were talking to the fraudsters. When he came back on the line and decided they were really his bank, he gave them the code. That code got relayed to the fraudsters in real time.
Now it makes sense! This was the missing piece I wasn’t getting. Thanks for asking the question. (I’m glad Brian confirmed it, too.)
Puzzled-No-More.
The article is missing an explanation that would help me (tech-savvy but not a professional) understand how it works. The article says, “The call would prompt the target to enter an OTP token generated by their phone’s mobile app….”
I thought OTPs came directly from the institution/organization (bank, commerce-site, etc.) sent via a second channel other than the WWW (e.g., mobile phone, landline telephone, email).
So is this scam limited to mobile phones, which can generate its own OTP that is some kind of device identifying token that can then be used by the institutions/organizations?
Puzzled.
The source of the OTP doesn’t matter, whether it came from an SMS text or authenticator app the result is the same. The bot calls the legitimate user and asks them to enter the OTP code. The bot then forward the OTP to the attacker for them to use in real time.
OTPs can be generated either on the backend servers performing authentication, sent via SMS to the account owner… or generated on the mobile device using a shared secret (seed / QR code) that the backend servers also have.
The SMS example has some other flaws that are commonly exploited since it puts your cellular carrier in control of SMS messages (if they get bribed or tricked into porting your phone number for example).
But in this case, the account owner is phished for the OTP code regardless of where it was generated or how it was sent to the person.
There or applications like Google Authenticator that actually run on your phone and generate one time pass codes.
For those using landlines, once you hang up on the scammer, wait a minutes before picking up and calling your financial institution. Due to phone company’s delayed disconnect, scammers often stay on the line when you hang up and hope you will immediately try to dial your bank. They then fake a dialtone and pose as your bank.
Thank you, Alexandra!
I’D Hacker
Yubikeys FTW
Agreed. Yubikey and Android’s and now Apple’s Platform FIDO authenticators. The recently released (with no big announcements) Apple FIDO work is really slick. If you want to see a demo, go to demo.quado.io on an apple device and select platform authentication.
But doesn’t a yubikey or other physical device have the exact same issue? As long as the victim reads the code over the phone to the scammer, that’s all they need. Regardless of what is generating the code (sms, app, yubi, or a rock in the backyard). Or am I misunderstanding?
Actually not. With FIDO there is no “code to type into a web page”. While some Yubikeys support One Time Passcode, these are NOT FIDO authenticators. When you register the FIDO authenticator you setup a unique key from the SSL protected domain of the bank/store, etc. Compromising a FIDO authenticator would require
1) Compromise of the bank/store and getting access to the FIDO identifiers.
2) Compromise of the SSL certificate.
3) Compromise of the DNS records and
4) developing a full FIDO implementation for each specific domain that you want to compromise.
If #1 happens above, there is a lot more damage that attackers can do without having to implement 2-4. The keys on the end devices (Yubikey, or Android/Apple platform) are unique to one bank/store, so compromise of one doesn’t compromise any others.
The main protection is there is no CODE to type into any webpage which is the main weakness with OTP.
Yubikey and other FIDO2 (or even older U2F) have very good anti-phishing features.
The one-time code isn’t even shown to the victim/user. Rather, these USB hardware tokens communicate to the web browser. No OTP code is displayed to be told to the attacker.
This code is more dynamic than an OTP based on a single preshared seed/secret. This code is based on the requesting webpage, which is why it requires USB passthrough to the browser. The hardware token, Yubikey, needs to get information from the requesting webpage. There are random nonces and unique identifiers. The Yubikey returns the “one-time authentication code” based on cryptography of the info from the web browser.
So really cannot be phished over the phone. The attacker would have to socially engineer them to a computer, to plug in their Yubikey, and go to the attacker’s website. And even then, it still won’t work because the attacker would need to somehow spoof the real legitimate website, domain and all. So it really can’t be done without some technical vulnerability in the system.
FIDO / U2F hardware tokens protect users from this kind of phishing. Only drawback, is that very few online websites currently allow USB hardware tokens as a 2FA factor. While OTP is vastly more popular.
Now, there is a Yubico Authenticator mobile phone app that does unlock a standard OTP on your phone, and that could be phished. But that is a very uncommon use case.
New Android and Iphone devices can act as a FIDO2 device now, so no need to have a separate USB token. But the concept is the same, the internal chip does the cryptography and is only valid for the requesting website. Spoofing the website and trying to redirect does not work, which is why FIDO2 is so secure.
Thanks for this info JamminJ.
If using it for something like TOTP yes, but if the site is using FIDO for 2fa then there is no ‘code’ that is given or typed in, it’s all handled automatically between the browser and the token. I wish FIDO was more popular than it currently is.
What was stopping FIDO was coverage and the failure of the usability of Bluetooth options, but with Apple Platform support coverage is pretty complete.
USB, NFC, Windows PC fingerprint readers, Mac Fingerprint readers, Android Fingerprint readers, Apple Touch ID and Face ID.
Seriously try the developer demo (kind of geeky), but you will see the full User experience after you select your options (cross platform = USB, NFC, Platform = attached fingerprint/Face ID). This can now be implemented from any website without the need to install any applications.
demo.quado.io
FaceID is buggy AF and changes with every update. Not my tea.
And this is why I check Krebs daily … relevant information clearly presented.
Thanks BK
I can’t think of a legitimate case to enter a OTP generated code into a SMS reply. So the scam works because the victim is unclear on how OTP works.
I personally don’t like using a phone for OTP. I use the Symantec code fobs. All air gapped.
I would use FreeOTP if offered.
https://freeotp.github.io/
I do have one service using an app and it had to be their app. I have no idea how I will transfer this to a new phone. That wouldn’t be a problem with FreeOTP. Plus for (name your deity) sake it is from Red Hat and open source.
Codes are not being sent as an SMS reply. The legit bank sends the code via SMS, and the attacker calls the victim with voice phone call to socially engineer and get the code.
Symantec should not be entirely trusted. Especially since their security has gone downhill after getting acquired by Broadcom. RSA key fobs worked the same way, and their seed files were hacked. Your fob may be airgapped, but do you trust them to secure the seeds on their servers?
Fundamentally, any bank sending an SMS token instead of helping their customers properly configure OTP is a failure of the bank.
SMS based “2FA” is not “2FA” it’s “some myth you trust”.
Te myth includes “I trust all sales associates at my cellular provider not to be interested in selling a phone to someone claiming to be me who appears to have damaged/lost their/my phone and urgently needs to get back online” and “I trust that no employee at my cellular provider could be bribed to issue/transfer/etc my account to someone else” and “I trust that there are no bugs in the SMS/Cellular stack [1] – SS7”.
The idea of “2FA” as outlined in Brian’s article is “Something you know” (password) + “Something you have” (e.g. a phone)*. SMS isn’t something you have, it’s a misguided belief that you have a working contract with an operator that they won’t mess up. This belief is totally foolish and entirely misguided. This belief isn’t a tangible thing you have. It might be something you know, and hopefully you can understand that it’s wrong.
[1] https://www.theguardian.com/technology/2016/apr/19/ss7-hack-explained-mobile-phone-vulnerability-snooping-texts-calls
* Yes, there’s “something you are”, but that’s a whole *different* disaster. Something you are isn’t something a computer understands. It only has “something it can read”. And anything that can be read can be recorded (it is) and transmitted and replayed. And if that’s the case, then it’s at best “Something you know and promise to share”. A picture of your face is something you share constantly as you walk around in public. Your fingerprints are something you leave on every surface you touch. These are not secrets. They’re commons. (There’s a distinction between Identity and Authorization, and Know/Have fall into Authorization, Are falls into identity — as does your name or you SSN — things that are not secrets.)
Preach.
🙂
Completely agree and been saying for years.
I’ m unclear as to how this works? Is the target the person who is using 2fa in the moment to get into their account? Or is the target getting a request for an OTP out-of-the blue?
It seems to be combined with a phone call, and some social engineering.
The attacker calls the victim pretending to be their bank. They already have their personal information (fullz from a breach, or skimmed CC from a gas station, etc.).
Then the attacker on the phone tells the victim that they are sending an OTP to “verify the victim”. So when the get the SMS, it’s not out of the blue.
Normally banks don’t call you, if their is a problem they temporary suspend your account and then you call them to rectify the issue.
It depend, In Canada they normally don’t call you unless you are on collection department where they will call you every days until you refund or repay what you need to
So true. Since when does any company call you unless they are selling you worthless crap? LOL
This is a stretch for me. I can’t see this working well on anyone who has a modicum of common sense. Maybe someone’s grandmother.
Stretch yourself to any one of hundreds of the other articles or statistics about scammers and social engineering.
Even Jim Browning fell victim to a convincing social engineering attack.
Lesson to be learned. It’s not common sense, it’s vigilance. And even smart people get complacent.
lol, try telling this jamaica’s scammer inc and other social engin scammers..they make millions off this tactic. They just need the pin sent to your device from the authorized financial institution.. they have all the ppi to clear a bank but not the sent pin.
guess who you can thank for all your ppi info available.. big tech selling it or lossing the to data breaches do to incompetence or not vetting the buyers who are the scammers. But i digress.. everyones data was going to be available when greed is put before all else..
I have been warning about this for more than 10 years.
Correct authentication should not rely on user devices.
To protect against account take over two level authentication with a time out before lock out is required to prevent attackers deliberately triggering lockout to take over accounts in addition to MitM described in this article.
A video explaining how attackers circumvent systems is available at https://armorlog.com
Not the Yubikey I have – I plug it in (if it isn’t in already) and touch it. No OTP is given to me so I can’t pass it on to anyone.
HTH, –Peter
Yubikey can be intercepted if your USB port has been tampered with, also it creates a plaintext code which is typically “pasted” into the relevant interface. A capture layer on a web interface or ssh session could easily capture this.
This is why yubikey is being phased out at security focused organizations.
It gets even better:
https://citeseerx.ist.psu.edu/viewdoc/download?doi=10.1.1.642.5552&rep=rep1&type=pdf
That SCA paper was nearly a decade ago, only affected yubikey version 2, and only the Yubico OTP. Yubikeys can also use HMAC chalresp, FIDO2, PIV certs, etc.
Yubikey hardware is now version 5 and they fixed the issue before the paper was even published.
“Having discovered the security problem, before publication, we contacted the vendor Yubico as mentioned before. Yubico acknowledged our results and has taken measures to mitigate the security issues. We examined an updated firmware (version 2.4) and found that our attacks do not apply to this improved version.”
Since 2013, more security focused organizations have adopted Yubikey and other similar hardware tokens. They are NOT being phased out, rather they are being used more and more by organizations and now private consumers.
We are doomed with this hackers
The biggest issue with 2FA being hacked is users. It’s easy to grab someone’s 2nd factor code with Phishing. This affects all 2FA methods including Akamai phish proof 2FA that has been advertised on this site. Instead of hacking the 2nd factor codes you reach out to the user and get them to provide the code so you can gain access to their account.
Example.
This is bob from IT and we will be testing our login servers. you may get a popup asking to approve the login. for the first attempt please deny the request and when the 2nd request comes in approve the code. Gullible user follows instructions and bad guy now has access to your account. similar approaches can be used to grab the users code from SMS or authenticator app. Using a physical authenticator key where you need the key to complete the login is about the only way to stop phishing your credentials.
The red flag here is the bank calling you. If they do, don’t give them ANY information. Tell the caller that you will call your bank back in a few minutes to verify the issue. Then hang up. Wait about 10 minutes and call your bank. Problem solved.
Never, ever give any information if you RECEIVE the call. Only give out info when you are the CALLER to the bank. You will then be properly vetted by your bank.
Correct, this should be in bold text and elevated. This is everything.
Hi,
If you get one of these social engineering phone calls, in addition to immediately hanging up, start the process of changing all your passwords. Passwords should be unique, random strings of all possible character sets, and 24 characters or more or as long as the host allows. This is to thwart rainbow table hacks.
I wonder how many people are going to simply generate an OTP because they got a phone call asking for one, knowing that they haven’t initiated a log in?
Seams like this generation has to be the dumbest in the history of humanity.
Hold your outrage there Doug.
First, a skilled and experienced social engineer can create urgency and trust over the phone. They can convince people to open their authentication app and read a number if the victim is convinced that the bank needs to verify it.
Secondly, an SMS code is much more likely to given up since people get these all the time for various accounts. Often the sender of SMS OTP codes don’t have enough room for a good disclaimer that would cause a victim to think twice.
And lastly… the victims are not from “this generation”. Overwhelmingly, the victims are much older.
Brian,
This really is not an interception since the victim is providing the OTP to the scammer.
Yeah, good point.
Although that word is all over the article including the URL and Headline… it should be changed.
Interception is a very different attack. Vishing or Phishing with a phone call are the correct terms to use.
Nice article. I had to read the whole thing to figure out how they were doing the hacking.
This is only a hack for OTP. The thieves already have to have your login credentials.
This also requires that the OTP is generated solely on your Phone, PC, etc without any interaction from the hacked service. I.E. An authentic generator which simply generates a OTP based on an algorythm. If the site would send a code to the generator, thus initiating the generation of the OTP this would not work.
The user uses the stand alone OTP generation and sends it to the thieves who then enter it and access your account.
Correct?
Not correct.
OTP codes are generated by the legit server that the scammer is trying to access. Then this OTP is send via SMS to the account owner.
Yes, the attacker enters the stolen credentials, is prompted by the legit server for the 2FA code. At the same time, the attacker (using the criminal service like SMS Ranger or SMS Buster) calls the victim user. They will usually call the victim first, so they are expecting an SMS code to arrive while their are on the phone.
There are many more sites/services on the internet that use SMS OTP codes rather than phone generated OTP using an Authenticator App. Victims using an app that generates OTP codes with shared seed (QR Code during setup) are probably less likely to fall for this scam, but they are also a much smaller minority since not many banks even allow this kind of OTP. Either way, the victim could still be convinced.
Diabolicaller and disbolicaller
While Telegram is a useful tool I feel they can’t control the beast they created. I have seen more moderation on the DN. Until they have an incentive to control the actions they will not. Any attempt to police their service could cause a drop in users and break off from what they wanted to create.
JamminJ I don’t understand why you say ‘not correct’. The case you describe is harder for the victim to be scammed, because if the OTP is provided by the legit server, then the victim has to log into the legit server to get the OTP then give it to the hacker who is still on the phone, right? If the legit server uses the mechanism of synching to the victims authenticator app, the victim just has to generate the OTP and provide it to the hacker on the phone.
Sorry if my comment and the article aren’t clear enough. The second sentence describes how the OTP is sent to the account owner.
“OTP codes are generated by the legit server that the scammer is trying to access. Then this OTP is send via SMS to the account owner.
“the victim has to log into the legit server to get the OTP”
This is incorrect. The victim gets an SMS text message while on the phone with the scammer. This is somewhat easier than if the victim has an authenticator app since the SMS will probably be in a popup notification on the phone, and the scammer doesn’t have to guess the name of the authenticator app to appear more convincing.
I really feel that the people who read Krebs on Security aren’t those who are being targeted (or falling for) for these scams. I thought my 81 year old mom was fairly competent but I have found in the last year that she was a victim of the fender bender insurance car scam AND that she said that Microsoft kept bugging her for her email and password, so she gave it to them. The funniest part of that was that when I went to change her password on the account, she didn’t have the correct one. I’m just thankful that this article wasn’t about how my OTP generator had been hacked. That is why I read it. Best to all here.
“But in so many instances, what sites request is basically two things you know (a password and a one-time code) to be submitted through the same channel (a web browser).” The OTP isn’t really a thing you know, because you didn’t know it before initiating the login attempt. It gets sent to the user’s device (probably a mobile phone), so only someone who has that device should be able to enter it into the web browser. It thus authenticates something that you have. (As long as everything works as intended, of course!)
@Rick , It takes a few milliseconds for the automated computer programs to login and transfer the funds. Do you think it’s like the movie’s where some kid spends time in front of the computer hacking away? You are WAY behind. The program is written the hack is done on several accounts at a time. It’s not like War Games, that takes too much time.
Can your Google Authenticator OTP be intercepted or hacked if it is on a secondary phone that has no SIM card/cell phone service and is only turned on for logging into an exchange periodically? Social engineering is not an option.