A recent phishing campaign targeting Coinbase users shows thieves are getting smarter about phishing one-time passwords (OTPs) needed to complete the login process. It also shows that phishers are attempting to sign up for new Coinbase accounts by the millions as part of an effort to identify email addresses that are already associated with active accounts.
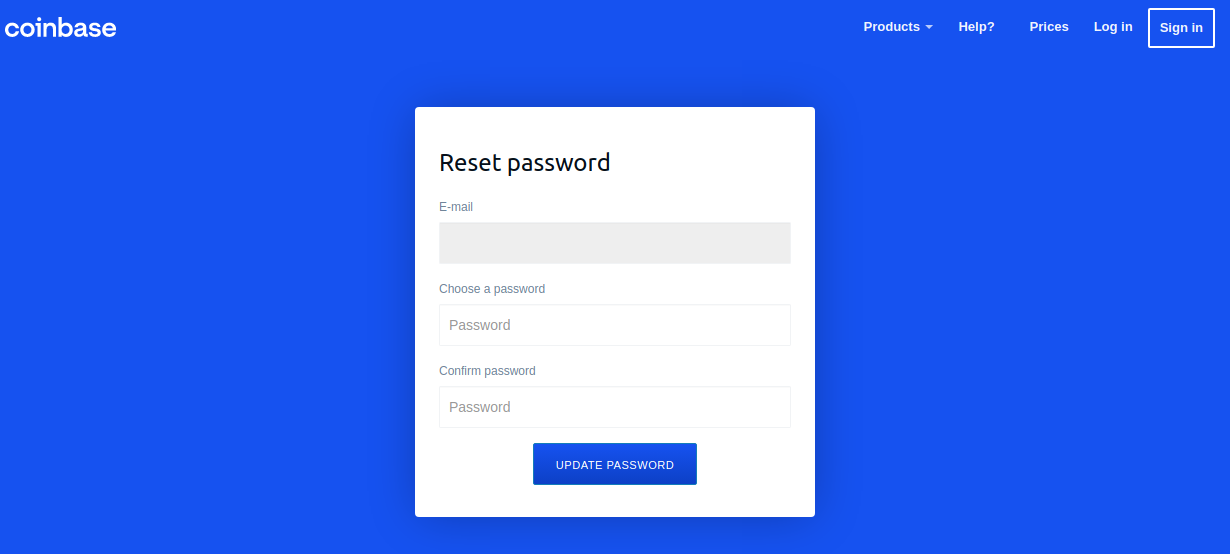
A Google-translated version of the now-defunct Coinbase phishing site, coinbase.com.password-reset[.]com
Coinbase is the world’s second-largest cryptocurrency exchange, with roughly 68 million users from over 100 countries. The now-defunct phishing domain at issue — coinbase.com.password-reset[.]com — was targeting Italian Coinbase users (the site’s default language was Italian). And it was fairly successful, according to Alex Holden, founder of Milwaukee-based cybersecurity firm Hold Security.
Holden’s team managed to peer inside some poorly hidden file directories associated with that phishing site, including its administration page. That panel, pictured in the redacted screenshot below, indicated the phishing attacks netted at least 870 sets of credentials before the site was taken offline.

The Coinbase phishing panel.
Holden said each time a new victim submitted credentials at the Coinbase phishing site, the administrative panel would make a loud “ding” — presumably to alert whoever was at the keyboard on the other end of this phishing scam that they had a live one on the hook.
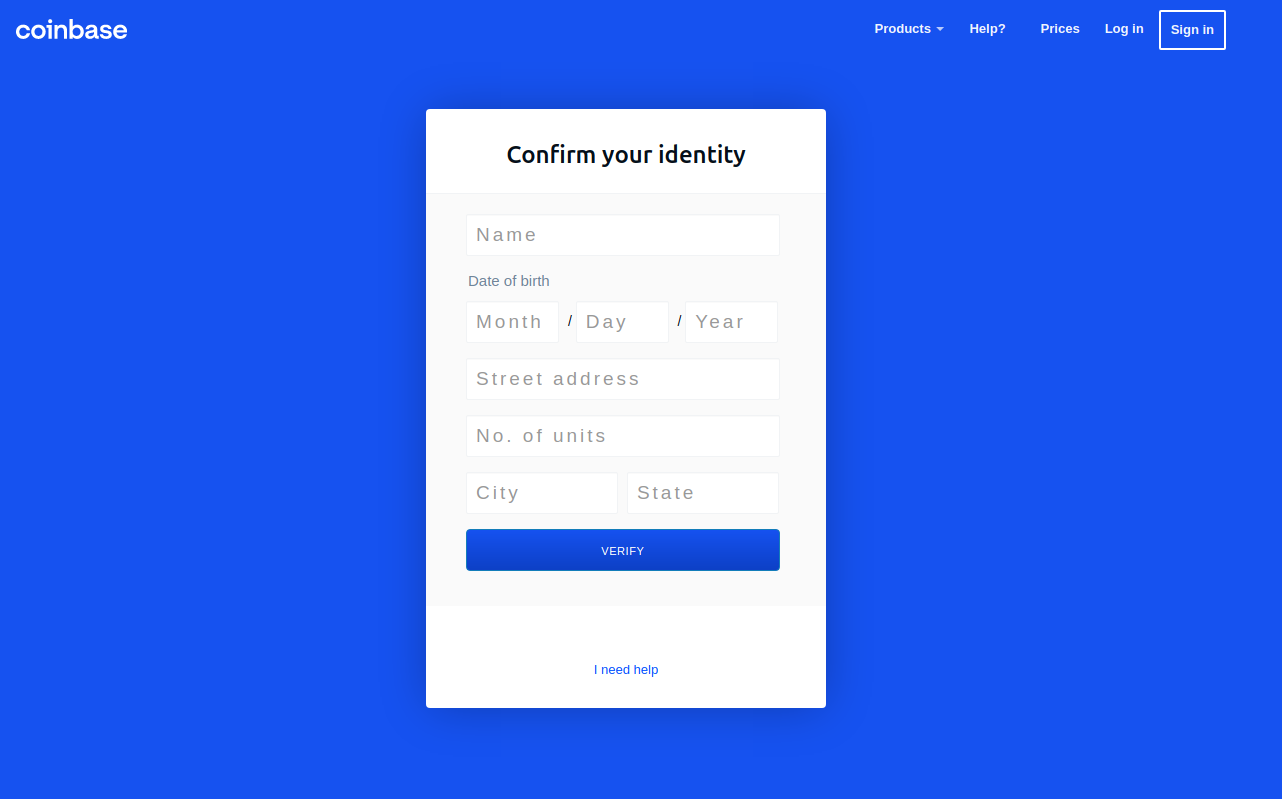
In each case, the phishers manually would push a button that caused the phishing site to ask visitors for more information, such as the one-time password from their mobile app.
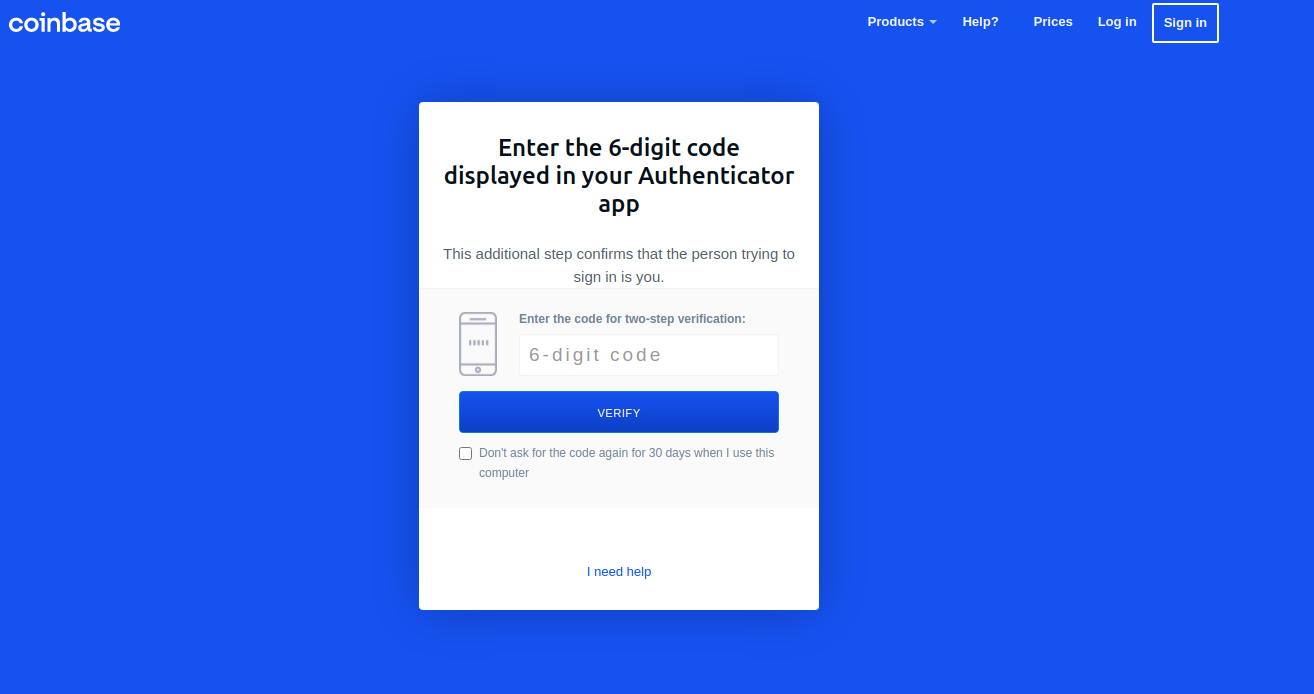
“These guys have real-time capabilities of soliciting any input from the victim they need to get into their Coinbase account,” Holden said.
Pressing the “Send Info” button prompted visitors to supply additional personal information, including their name, date of birth, and street address. Armed with the target’s mobile number, they could also click “Send verification SMS” with a text message prompting them to text back a one-time code.
SIFTING COINBASE FOR ACTIVE USERS
Holden said the phishing group appears to have identified Italian Coinbase users by attempting to sign up new accounts under the email addresses of more than 2.5 million Italians. His team also managed to recover the username and password data that victims submitted to the site, and virtually all of the submitted email addresses ended in “.it”.
But the phishers in this case likely weren’t interested in registering any accounts. Rather, the bad guys understood that any attempts to sign up using an email address tied to an existing Coinbase account would fail. After doing that several million times, the phishers would then take the email addresses that failed new account signups and target them with Coinbase-themed phishing emails.
Holden’s data shows this phishing gang conducted hundreds of thousands of halfhearted account signup attempts daily. For example, on Oct. 10 the scammers checked more than 216,000 email addresses against Coinbase’s systems. The following day, they attempted to register 174,000 new Coinbase accounts.
In an emailed statement shared with KrebsOnSecurity, Coinbase said it takes “extensive security measures to ensure our platform and customer accounts remain as safe as possible.” Here’s the rest of their statement:
“Like all major online platforms, Coinbase sees attempted automated attacks performed on a regular basis. Coinbase is able to automatically neutralize the overwhelming majority of these attacks, using a mixture of in-house machine learning models and partnerships with industry-leading bot detection and abuse prevention vendors. We continuously tune these models to block new techniques as we discover them. Coinbase’s Threat Intelligence and Trust & Safety teams also work to monitor new automated abuse techniques, develop and apply mitigations, and aggressively pursue takedowns against malicious infrastructure. We recognize that attackers (and attack techniques) will continue to evolve, which is why we take a multi-layered approach to combating automated abuse.”
Last month, Coinbase disclosed that malicious hackers stole cryptocurrency from 6,000 customers after using a vulnerability to bypass the company’s SMS multi-factor authentication security feature.
“To conduct the attack, Coinbase says the attackers needed to know the customer’s email address, password, and phone number associated with their Coinbase account and have access to the victim’s email account,” Bleeping Computer’s Lawrence Abrams wrote. “While it is unknown how the threat actors gained access to this information, Coinbase believes it was through phishing campaigns targeting Coinbase customers to steal account credentials, which have become common.”
This phishing scheme is another example of how crooks are coming up with increasingly ingenious methods for circumventing popular multi-factor authentication options, such as one-time passwords. Last month, KrebsOnSecurity highlighted research into several new services based on Telegram-based bots that make it relatively easy for crooks to phish OTPs from targets using automated phone calls and text messages.These OTP phishing services all assume the customer already has the target’s login credentials through some means — such as through a phishing site like the one examined in this story.
Savvy readers here no doubt already know this, but to find the true domain referenced in a link, look to the right of “http(s)://” until you encounter the first slash (/). The domain directly to the left of that first slash is the true destination; anything that precedes the second dot to the left of that first slash is a subdomain and should be ignored for the purposes of determining the true domain name.
In the phishing domain at issue here — coinbase.com.password-reset[.]com — password-reset[.]com is the destination domain, and the “coinbase.com” is just an arbitrary subdomain of password-reset[.]com. However, when viewed in a mobile device, many visitors to such a domain may only see the subdomain portion of the URL in their mobile browser’s address bar.
The best advice to sidestep phishing scams is to avoid clicking on links that arrive unbidden in emails, text messages or other media. Most phishing scams invoke a temporal element that warns of dire consequences should you fail to respond or act quickly. If you’re unsure whether the message is legitimate, take a deep breath and visit the site or service in question manually — ideally, using a browser bookmark so as to avoid potential typosquatting sites.
Also, never provide any information in response to an unsolicited phone call. It doesn’t matter who claims to be calling: If you didn’t initiate the contact, hang up. Don’t put them on hold while you call your bank; the scammers can get around that, too. Just hang up. Then you can call your bank or wherever else you need.
By the way, when was the last time you reviewed your multi-factor settings and options at the various websites entrusted with your most precious personal and financial information? It might be worth paying a visit to 2fa.directory (formerly twofactorauth[.]org) for a checkup.




“However, when viewed in a mobile device, many visitors to such a domain may only see the subdomain portion of the URL in their mobile browser’s address bar.”
So that’s a UX vuln?
URL padding with subdomains or other junk so that the real domain is pushed far to the right on the address bar is not exactly a new problem. But yes, UX definitely comes into play here.
Years ago you used to get http://domain.com:—————@——————————otherdomain.com The Apache web server used the bit before the @ sign to send usernames and passwords for protected directories. Eventually, it was altered to remove that function. Moving to SSL also helps unless otherdomain.com has a wildcard SSL certificate. Domain registrars could do a lot more to help. When I ran a registrar (Until 2009) it was common for stolen card numbers to be used to register domains for fake bank websites. I put a subroutine in our ordering system to send any requests for domains that included words like Paypal and Bank for manual intervention. In those days there was not extensive use of VPNs and a lot of this activity came from certain countries so you could bounce traffic from those countries because we had no real customers in those markets. I used to bounce them to affiliate links on other registrars! Eventually that caught up with us and we got banned from all the affiliate programs. I should really write a book about those early days. I was in the Internet industry from 1999 to 2009 which was an important period in its development.
How would the scammers know if the email is taken on the coin base forgot your password page? It merely shows “if account exists we will send you the email” for any email typed in.
What I wrote was that they were doing new Coinbase account signups in using email addresses of Italians they wanted to phish. But they only sent the phishing messages to the email addresses that failed new account signup, because they knew all those address were already coinbase users.
Users can be protected from being tricked if website owners use encrypted custom proprietary keys for each user.
Another reason to never leave an idle balance of fiat or crypto in a cryptocurrency exchange account. Put your money in, buy/sell, take your money out ASAP.
“ …when was the last time you reviewed your multi-factor settings and options at the various websites entrusted with your most precious personal and financial information?”
Using the Public Beta, and doing all within the confines of iOS iCloud Password Keychain and Hide My Email, I used the approach of iOS 15 to do exactly this.
For about 400 online accounts, I (roughly in order of the steps necessary for you to do the same):
– changed all online account profile emails from my old standard of:
– – myinitials.xyz+001(…etc)@gmail for critical sites (where xyz= fin, med, gov. This being a newer scheme to remove my name from my online profile emails and to add a tracking feature (+001, +002 … +nnn) to make email addresses site unique for breach monitoring (in practice this didn’t work well because few sites honored the + symbol in an address);
– – myrealname@domain (important sites), or
– – mynickname@domain (free newsletters, blogs, non critical or important websites, where all of these had an alias persona);
where the 2nd and 3rd above were legacy from when I went online in the late 00’s and before I read KoS;
– upgraded all previously 15-char unique p/w’s to apples newer 20-char p/w standard (compared to a few years ago almost all sites accepted this generated password) and saved in the Keychain;
– changed all existing 2FA via SMS to 2FA via iOS Keychain’s new built in authenticator (to reduce SIM jacking risk);
– saved the OTC’s generated by the authenticator setup in the Keychain;
– where an authenticator option wasn’t offered, I elected to receive the PIN via email (or where required via a site’s iOS app);
– updated all challenge question answers and pass phrases to random answers and saved them in the Keychain;
– removed phone numbers for all sites where 2FA could be handled by anything other than a mobile number; and
– reverted Sign In w/ Apple back to authentication via e/m and p/w w/2FA (if offered); because SIA is so rarely supported, I liked the idea of having a standard login practice. (There is no standard practice for reverting from SIA, but it is generally done by logging into site via SIA; going into profile; creating a new email address using HME button; (or if glitchy jumping over to HME in settings and creating one there then copy pasting it into the site’s profile); confirming new iCloud email address from HME if required; then inputting a new p/w or logging out and using sites Forgot Password function to create one. Afterward don’t forget to decouple site account from SIA inside the profile and then to do the same from SIA in iOS Settings> iCloud > Security> SIA);
– deactivated(deleted) half a dozen email address accounts that I’d used for the top critical online accounts (my email syncing runs much better since then). I’ll keep the myname@domain because this is how people have reached me forever and I don’t want to cut off folks with whom I don’t have frequent contact, but I will eventually delete mynickname@domain after a 6-12 month monitoring for anything I may have missed (and I won’t miss it bc it receives the majority of spam!);
I was pleased to see how many sites were offering 2FA via an authenticator (this has clearly improved since my last big upgrade effort 3-4years ago.)
Where possible, I used a more stringent data minimization philosophy and removed as much contact info as possible. For non critical things I use a standard fake name and birthday, and for non critical accounts that only offer 2FA via mobile number I’ve gone back to single factor so I can remove my number from such sites as I see no 2FA as an indicator of bad site security and don’t want to lose any more info in a breach than necessary.)
I started all these upgrades sometime around the end of June, but hit a wall bc at the time Apple limited HME beta to 100 unique email addresses. After this limitation was lifted sometime in August I continued and finished sometime in early September.
It was quite a bit of work but so did it while watching TV or just relaxing. I have a non spreadsheet system for knowing what authentication method and info I have on each site so, from time to time, in years to come I’ll upgrade the straggler sites to the above standards.
All this is possible if you are a bit comfortable with moving from app to app and back using the app switcher in iOS so you can copy+paste the occasional new HME email or correct the e/m and p/w info in the Keychain. (If you are still writing down your p/w’s or using a spreadsheet, you’re doing in a tedious inefficient way and should start using your iCloud Keychain, if you are all apple it’s a breeze, and now that there is a Keychain browser extension for PC’s it’s easier for windows PC drivers too.)
Apples User interfaces for SIA, HME, Passwords, for some reason are not integrated into a single sheet which makes the upgrade process more cumbersome and tedious than necessary (especially given the amount of overlap in content and functional purpose of these 3 features), but after getting everything upgraded this lack of integration is less irritating (or confusing, I suppose, to the unfamiliar.)
Good luck! (If you have feedback, feel free to drop me a line at this purpose made iCloud address: bunnies-ungodly-0q (at) icloud.com , and, yes, HME creates some very whimsical iCloud addresses!)
Their are online security websites that will allow you see the URL redirects of the domain name in question or allow you to see a browser view picture of what the phishing website looks like,
I had my coinbase account hacked and drained monday. I used an authentication app to log in, not a text message and my phone was never sim swapped, I checked with tmobile. I used a unique to CB password, randomly generated, and never visited a fake site or clicked on a phishing email. Coinbase let someone log in and disable my 2fa setting, then buy as much coin as possible and transfer it out along with my existing coin. What’s the point of 2FA if they let someone just turn it off ? Disabling security settings should put a mandatory 24-48 hold on all transfers. I signed up with a different company who puts a higher value on their sites security.
I also signed up for a coinbase card 2 weeks earlier, shows it was sent but I never received it. I am hoping coinbase wasn’t stupid enough to put it in a bright blue envelope that said Your Coincase Card Is Here and include any additional information with the card, like my email or phone number but seems strange my account was hacked right after they sent me the card that I never got.
Bob, sorry to hear about the hack. It is damned frustrating. Oct. 4th after the internet drop for several hours I had checked my CB Wallet to verify that I still had coins in that account. Had been waiting for a cold storage device to show up in mail up to this point.. Oct. 7 I had logged into my CB Wallet account only to find all of the coins removed. I would have expected to see 20 coins remaining as this was a requirement to open the account initially. Like yourself, I had entrusted a separate 2FA from Google. Set the account to private meaning that my address could not be seen, nor could coins be sent until I selected a public setting. My only recourse was to contact CB and lock my account. At present I am waiting on a response from an investigation that was filed. I did also contact the FBI to file a report. What else can you do? I believe that if the SEC wants to be useful instead of being predatory. Referring to the Ripple deal here. They would employee a special unit to Trac the block chain and recover reported theft. Just a thought..
Coinbase will give you the run around in their complaint responses. This will include lying, falsely accusing you of looting your own account, blame you for getting SIM swapped, malware, sloppy with yur password, and ignore your actual complaint with nonsense responses.
The FBI, SEC, CFPB, BBB, police and every other entity in the US will do nothing for you. They will clain they don’t have jurisdiction, pawn you off on another agency who will do nothing, file your complaint “”for future use” or just send your complaint back to Coinbase.
The only thing that has any legal weight is filing for arbitration after you go through the Coinbase complaint run around. Look at their terms of service for details on it.
DId you check your IP history on Coinbase for the day of your hack? It will show the 2FA activity. See if they failed before they got successfully got past it.
Also, depositing USD from your linked bank account to your CB account, then buying crypto, and transferring it out the same day should be stopped by CB’s auto-generated 5 day hold period, until the funds have time to clear. This leads me to believe that not only was the 2FA exploited, but also the admin’root level of the CB network. Now, this could be done easier by a CB employee or outside hacker with Admin access (working with an employee).
I think CB has an internal theft problem. This would be disaterous for CB and also why it took them so long to find out about this latest hack. Internal theft takes longer to catch.
CB would never admit to an inernal exploitation of their system and that is why they keep blaming customers for sloppy password security. No one is questioning CB on their own security.
Userid enumeration bug is a basic check in any Pentest. Shame on Coinbase for not doing that properly. All they needed to do at the user registration stage is to ask for an email address and then print a message saying – “We have sent a message to the email address you submitted, please click the link to confirm your ownership of the email.” They should do that even for already registered email addresses. Otherwise you get this exact situation where scammers can suss out who is already an existing user.
Remind me again, cryptocurrency is a solution to what problem?
Remind me again, in what sense is your question relevant in this discussion?
If you receive any link or request for info by email, just follow through by visiting that website using your own browser bookmark. It’s not hard at all. Except sometimes we are too quick to click… without thinking? In my case…
I use Firefox with three different profiles:
1. Financial – All cookies and scripts are blocked (NoScript) unless specifically whitelisted (e.g. my bank, my broker, etc.).
2. Google (including GMail) – same as #1 (e.g. only the specific google products/sites I use).
3. General – ‘normal’ security settings.
With the above, reading an email (Profile #2) and accidentally clicking a “bank” link — real or fake — won’t do anything, since only Google cookies and scripts are allowed. And when nothing happens, I’d remember to go to Profile #1 and click on my bank bookmark. Phishing attempt foiled.
Finally, as extra layers of protection, always sign in as a “standard” user – not admin – so malware that somehow manages to download itself are unlikely to self-install successfully. And keep OS, antimalware, and apps updated. I think doing these will prevent pretty much all baddies that can reasonably be expected to hit individual home users like me.
My Coinbase was hacked also and Coinbase has insisted it was my fault and keeps saying how they won’t reimburse me. Done with cryptocurrency.
This was on September 6
People want “decentralized” and to be free from bank control.
Until they miss them FDIC.
lol.. no kidding.. people hate taxes but i like paved roads, trash removal service, clean water and electricity.
Proof that all men are created feeble ∆
i know a coworker lost $300,000 worth of bitcoin before it went to 60k…
so today he probably several million. he is technically sound,
not incompetent in the least and still got hacked.
the higher it goes.. the more targeted you become.
governments and mafia dont like competition.
Claiming that this cryptocurrency cybercrime is about governments and Mafia, not liking “competition”…
Is like those a-holes who claim people are just haters, because their “jealous”.
The reality is that speculators want the value to go up, and that brings criminals who are also speculators. It’s not jealousy, it’s greed, on both ends.
Actually, it was in response to the lower interest rate driven down by the financial crisis, the Great Recession, and the pandemic events. Because the banks are offering lower interest rates to hold your money led people to gravitate to crypto to use the gains to move into other investments.
hey want to be targeted by hackers and the goberment at the same time!?. just buy buttcoin!
glad emp weapons, corrupt governments, or taxes dont exist.. but might want to watch out for dns hacks, sim swaps and general digital tom foolery.
HELLO MY PEOPEL
BK: “It might be worth paying a visit to 2fa.directory (formerly twofactorauth[.]org) for a checkup.”
First time I have seen mention of 2fa.directory – having referred to twofactorauth.org before. Should we always be dubious of domain changes or “new domains”?
So I go to twofactorauth.org expecting to be bounced to 2fa.directory – but I get bounced to https://brainstation.io/cybersecurity/two-factor-auth. Now I am wondering what is going on! (A whois on “twofactorauth.org” shows registrant is “Domains By Proxy, LLC” – which does not reassure)
A whois on 2fa.directory shows registrant is “DATA REDACTED” which is similarly unreassuring! And the “about page” makes it look like a “hobby site”. Could we expect some organisation (like FIDO?) to maintain a definitive list?
So for a trusted list of 2FA using organisations it seems I have to use a single factor. Even if that “factor” is BK, I remain wary!
Some people like myself lost thousands and I never fall for phishing attacks, always sign in directly from my favorites bar, never belonged to any social media groups, and my Coinbase account was still drained $24,717.99 with 283 transactions in just an hour. So sick of seeing comments blaming users for giving out information. I am puzzled how scammer managed to take over my phone number for a short time and dump it. Something strange going on here. How do they know how much BTC one has? If I have to hold up signs and photo ID’s to get my password reset, why do hackers get to reset passwords without doing the same. This is 100% on Coinbase and their terrible security. Only scammers complete 100’s of transactions in minutes. If the user has been with Coinbase for many years and never acts this way, isn’t that a red flag. Xbox does better. Pet food companies have better security. It’s so shameful, almost like they don’t even care. Customer service is non-existent. No live support. Gee, I only got taken for $25K on your exchange that you boasted how secure you are.
Hello everyone, i would like to share my experience with you all, I lost over 100 thousand dollars to all these fake so called BO merchants, after several attempts in trying to recover my money all efforts failed, i was looking through the page of the internet then i saw JimFundsRecovery that were recommended as a good and reputable company so i reach out to them, to my surprise i was able to recover all my funds. contact: Jimfundsrecovery At consultant Dot com.