A 33-year-old Illinois man was sentenced to two years in prison today following his conviction last year for operating services that allowed paying customers to launch powerful distributed denial-of-service (DDoS) attacks against hundreds of thousands of Internet users and websites.
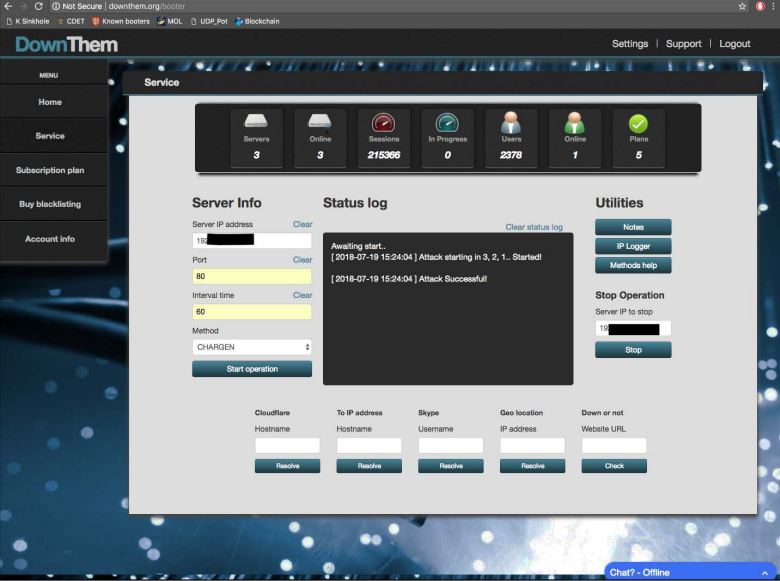
The user interface for Downthem[.]org.
Matthew Gatrel of St. Charles, Ill. was found guilty for violations of the Computer Fraud and Abuse Act (CFAA) related to his operation of downthem[.]org and ampnode[.]com, two DDoS-for-hire services that had thousands of customers who paid to launch more than 200,000 attacks.
Despite admitting to FBI agents that he ran these so-called “booter” services (and turning over plenty of incriminating evidence in the process), Gatrel opted to take his case to trial, defended the entire time by public defenders. Gatrel’s co-defendant and partner in the business, Juan “Severon” Martinez of Pasadena, Calif., pleaded guilty just before the trial.
After a nine-day trial in the Central District of California, Gatrel was convicted on all three counts, including conspiracy to commit unauthorized impairment of a protected computer, conspiracy to commit wire fraud, and unauthorized impairment of a protected computer.
Prosecutors said Downthem sold subscriptions allowing customers to launch DDoS attacks, while AmpNode provided “bulletproof” server hosting to customers — with an emphasis on “spoofing” servers that could be pre-configured with DDoS attack scripts and lists of vulnerable “attack amplifiers” used to launch simultaneous cyberattacks on victims.
Booter and stresser services let customers pick from among a variety of attack methods, but almost universally the most powerful of these methods involves what’s known as a “reflective amplification attack.” In such assaults, the perpetrators leverage unmanaged Domain Name Servers (DNS) or other devices on the Web to create huge traffic floods.
Ideally, DNS servers only provide services to machines within a trusted domain — such as translating an Internet address from a series of numbers into a domain name, like example.com. But DNS reflection attacks rely on consumer and business routers and other devices equipped with DNS servers that are (mis)configured to accept queries from anywhere on the Web.
Attackers can send spoofed DNS queries to these DNS servers, forging the request so that it appears to come from the target’s network. That way, when the DNS servers respond, they reply to the spoofed (target) address.
The bad guys also can amplify a reflective attack by crafting DNS queries so that the responses are much bigger than the requests. For example, an attacker could compose a DNS request of less than 100 bytes, prompting a response that is 60-70 times as large. This “amplification” effect is especially pronounced if the perpetrators query dozens of DNS servers with these spoofed requests simultaneously.
The government charged that Gatrel and Martinez constantly scanned the Internet for these misconfigured devices, and then sold lists of Internet addresses tied to these devices to other booter service operators.
“Gatrel ran a criminal enterprise designed around launching hundreds of thousands of cyber-attacks on behalf of hundreds of customers,” prosecutors wrote in a memorandum submitted in advance of his sentencing. “He also provided infrastructure and resources for other cybercriminals to run their own businesses launching these same kinds of attacks. These attacks victimized wide swaths of American society and compromised computers around the world.”
The U.S. and United Kingdom have been trying to impress on would-be customers of these booter services that hiring them for DDoS attacks is illegal. The U.K. has even taken out Google ads to remind U.K. residents when they search online for terms common to booter services.
The case against Gatrel and Martinez was brought as part of a widespread crackdown on booter services in 2018, when the FBI joined law enforcement partners overseas to seize 15 different booter service domains.
Those actions have prompted a flurry of prosecutions, with wildly varying sentences when the booter service owners are invariably found guilty. However, DDoS experts say booter and stresser services that remain in operation continue to account for the vast majority of DDoS attacks launched daily around the globe.




Good news. Needed some, thanks, Brian!
Two years isn’t enough by any means. Everyone involved in a DOS attack should face a decade or more to think about their poor choices in life.
Two years is plenty. The combination of incarceration (in itself a living nightmare) plus the difficulties he’ll face for the rest of his life in a number of different ways including whenever he applies for a real job are enough to teach a lesson
Seems doubtful considering this guy got busted trying to use bogus bar code stickers at a Walmart right before his sentencing.
lol who are the people commenting stuff like this? i’m sure even brian wouldn’t want most of these mislead kids facing decades in jail for clicking some buttons they learned from other skids online.
Not enough time to learn a lesson. Hope it is a felony.
Thanks, Brian. Each time I read your articles, I always come away wiser. Sadder, but wiser.
I hazard a guess that the two year sentence will probably take into account time served (like the six months it’s taken to go from conviction to sentencing, plus however much time he was incarcerated prior to trial), and time off for good behavior, plus prison policies that prefer to release non-violent offenders early since the prisons are overcrowded, and then there’s Covid to consider, and on and on.
So I guess he was released today?
Hi Peter,
Thanks. That’s a fair assumption, given past cases. It crossed my mind, too, as I was reporting this. I asked the Central District prosecutors whether the judge in this case mentioned at his sentencing any reason(s) he should not serve his entire sentence. They said no, that he was free on bond but ordered to surrender to the Bureau of Prisons on July 19.
Interesting – thanks again, Brian. Appreciate the follow-up.
Thank you very much for another informative article and all the work you do!
Brian — I suggest you amend this (otherwise excellent) article to include the conviction was by a jury; this wasn’t a bench trial. To me, the importance of the distinction is the reluctance of prosecutors to go to trial with what they perceive to be “complicated” evidence that may be challenging for a jury to follow; hence, prosecutors’ willingness to reduce charges and obtain a ‘guilty’ plea. A 9-day trial suggests this wasn’t a simple case.
What was Martinez’ penalty?
It’s so fascinating to me that there are cybercrime-as-a-service businesses. The screenshot of the DownThem interface looks so innocuous for the most part, as if it was a normal SaaS product.
They need to prosecute the customers. That’s actually the only way to actually stop this from happening in the future. All of these sites get taken down or hacked. So it seems that inevitability may actually make people think twice about using a service like this.
If customers actually go to prison, then you’ve got hope for this conviction to not be the same as screaming into the void. This guy got busted trying to pass bogus bar code stickers while on trial.
Brian do you know if there’s any plans to go after the customers?