InfraGard, a program run by the U.S. Federal Bureau of Investigation (FBI) to build cyber and physical threat information sharing partnerships with the private sector, this week saw its database of contact information on more than 80,000 members go up for sale on an English-language cybercrime forum. Meanwhile, the hackers responsible are communicating directly with members through the InfraGard portal online — using a new account under the assumed identity of a financial industry CEO that was vetted by the FBI itself.
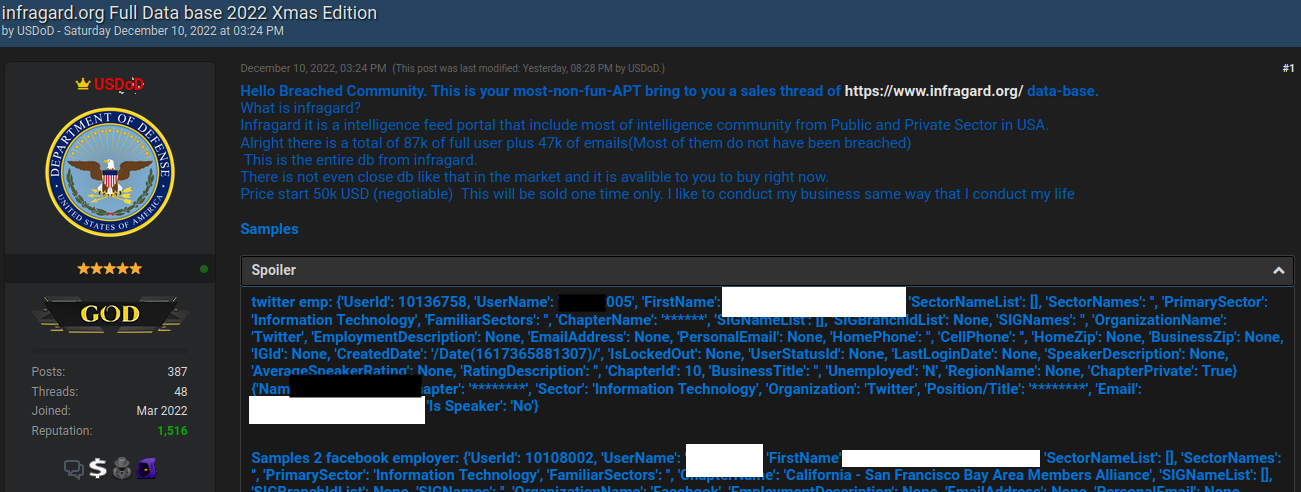
On Dec. 10, 2022, the relatively new cybercrime forum Breached featured a bombshell new sales thread: The user database for InfraGard, including names and contact information for tens of thousands of InfraGard members.
The FBI’s InfraGard program is supposed to be a vetted Who’s Who of key people in private sector roles involving both cyber and physical security at companies that manage most of the nation’s critical infrastructures — including drinking water and power utilities, communications and financial services firms, transportation and manufacturing companies, healthcare providers, and nuclear energy firms.
“InfraGard connects critical infrastructure owners, operators, and stakeholders with the FBI to provide education, networking, and information-sharing on security threats and risks,” the FBI’s InfraGard fact sheet reads.
In response to information shared by KrebsOnSecurity, the FBI said it is aware of a potential false account associated with the InfraGard Portal and that it is actively looking into the matter.
“This is an ongoing situation, and we are not able to provide any additional information at this time,” the FBI said in a written statement.
KrebsOnSecurity contacted the seller of the InfraGard database, a Breached forum member who uses the handle “USDoD” and whose avatar is the seal of the U.S. Department of Defense.
USDoD said they gained access to the FBI’s InfraGard system by applying for a new account using the name, Social Security Number, date of birth and other personal details of a chief executive officer at a company that was highly likely to be granted InfraGard membership.
The CEO in question — currently the head of a major U.S. financial corporation that has a direct impact on the creditworthiness of most Americans — told KrebsOnSecurity they were never contacted by the FBI seeking to vet an InfraGard application.
USDoD told KrebsOnSecurity their phony application was submitted in November in the CEO’s name, and that the application included a contact email address that they controlled — but also the CEO’s real mobile phone number.
“When you register they said that to be approved can take at least three months,” USDoD said. “I wasn’t expected to be approve[d].”
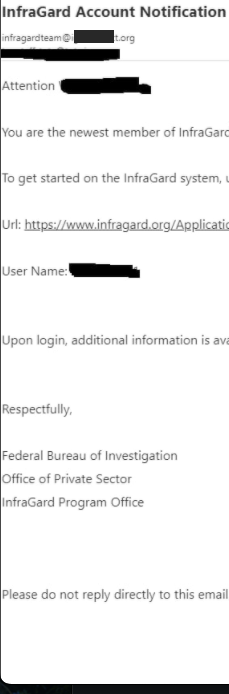 But USDoD said that in early December, their email address in the name of the CEO received a reply saying the application had been approved (see redacted screenshot to the right). While the FBI’s InfraGard system requires multi-factor authentication by default, users can choose between receiving a one-time code via SMS or email.
But USDoD said that in early December, their email address in the name of the CEO received a reply saying the application had been approved (see redacted screenshot to the right). While the FBI’s InfraGard system requires multi-factor authentication by default, users can choose between receiving a one-time code via SMS or email.
“If it was only the phone I will be in [a] bad situation,” USDoD said. “Because I used the person[‘s] phone that I’m impersonating.”
USDoD said the InfraGard user data was made easily available via an Application Programming Interface (API) that is built into several key components of the website that help InfraGard members connect and communicate with each other.
USDoD said after their InfraGard membership was approved, they asked a friend to code a script in Python to query that API and retrieve all available InfraGard user data.
“InfraGard is a social media intelligence hub for high profile persons,” USDoD said. “They even got [a] forum to discuss things.”
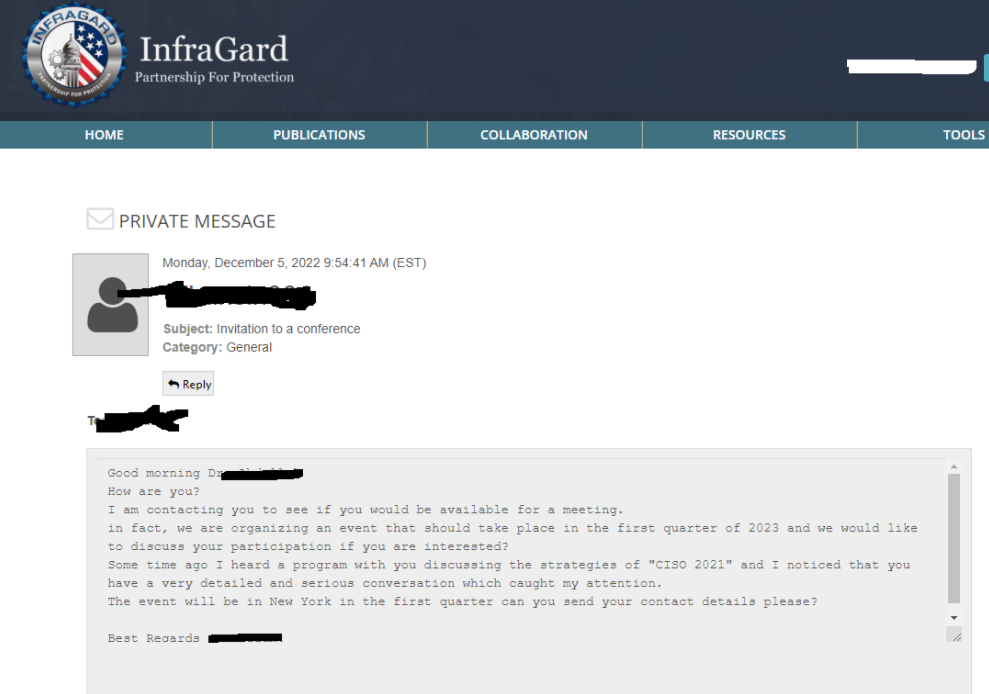
To prove they still had access to InfraGard as of publication time Tuesday evening, USDoD sent a direct note through InfraGard’s messaging system to an InfraGard member whose personal details were initially published as a teaser on the database sales thread.
That InfraGard member, who is head of security at a major U.S. technology firm, confirmed receipt of USDoD’s message but asked to remain anonymous for this story.
USDoD acknowledged that their $50,000 asking price for the InfraGard database may be a tad high, given that it is a fairly basic list of people who are already very security-conscious. Also, only about half of the user accounts contain an email address, and most of the other database fields — like Social Security Number and Date of Birth — are completely empty.
“I don’t think someone will pay that price, but I have to [price it] a bit higher to [negotiate] the price that I want,” they explained.
While the data exposed by the infiltration at InfraGard may be minimal, the user data might not have been the true end game for the intruders.
USDoD said they were hoping the imposter account would last long enough for them to finish sending direct messages as the CEO to other executives using the InfraGuard messaging portal. USDoD shared the following redacted screenshot from what they claimed was one such message, although they provided no additional context about it.
USDoD said in their sales thread that the guarantor for the transaction would be Pompompurin, the administrator of the cybercrime forum Breached. By purchasing the database through the forum administrator’s escrow service, would-be buyers can theoretically avoid getting ripped off and ensure the transaction will be consummated to the satisfaction of both parties before money exchanges hands.
Pompompurin has been a thorn in the side of the FBI for years. Their Breached forum is widely considered to be the second incarnation of RaidForums, a remarkably similar English-language cybercrime forum shuttered by the U.S. Department of Justice in April. Prior to its infiltration by the FBI, RaidForums sold access to more than 10 billion consumer records stolen in some of the world’s largest data breaches.
In November 2021, KrebsOnSecurity detailed how Pompompurin abused a vulnerability in an FBI online portal designed to share information with state and local law enforcement authorities, and how that access was used to blast out thousands of hoax email messages — all sent from an FBI email and Internet address.
Update, 10:58 p.m. ET: Updated the story after hearing from the financial company CEO whose identity was used to fool the FBI into approving an InfraGard membership. That CEO said they were never contacted by the FBI.
Update, 11:15 p.m. ET: The FBI just confirmed that it is aware of a potential false account associated with the InfraGard portal. The story now includes their full statement.
This is a developing story. Updates will be noted here with timestamps.




Interesting article
This sounds like it could be very promising. Would InfraGard be a good source of up to date information about attacks and scams and how to deal with them? Has anyone here been a member and found them useful?
Mainly OSINT. I’ve never found it to be useful. Generally just delete emails from them.
Same. Attended a single meeting but heard nothing I couldn’t gather from staying on top of industry news cycles.
As an InfraFard member, I value the formal purpose and intention of the group. In the event of a realized threat, due to the association to critical infrastructure, new communication channels become available in realtime, due to one’s association to critical infrastructure, not just because your a member of InfraGard. But InfraGard thru its association to Homeland and the FBI, would be one of the channels used to share information.
Independent of your Chapter, (I’m in Chicago), there is also informal sharing of information by the members. The informal sharing, via private forums and email is in near real-time. Over the years, these informal shares are real-time, and not (yet) in the news. If you are associated to critical infrastructure, yes, this is a valuable organization to be a member. It compliments your other formal associations. And opens your informal networking to a group of your peers who are both business leaders, and often nerdy enough to know the consequences of the technology being compromised.
For sure, if you qualify, it is a group of peers who are likely making decisions about threats to the Confidentiality, Integrity, and Availability (CIA) of critical infrastructure from either a global, national, state, regional, or own business perspective.
I believe the issue a lot of us security pros/InfraGard members have to do with the content is exemplified in your post. Many InfraGard presentations have a lot of windbaggery and grandstanding, with the non-technical (or very outdated technically) presenters going on and on about basic topics of infosec management. The fact that you took pains to expand the CIA triad (InfoSec 101), and state “global…regional” is typical of these presentations.
I’ve never seen a situation where InfraGard supplied information helped any organization get ahead of any threats.
sounds like a skill issue
hello
I’ve always found the threat intel very useful. Yes, I can find it from other sources (Mandiant, Talos, etc.) but I find that at least Infragard contains all of the information and not distilled to a set of products. The local chapter meetings have been very useful as well.
Aside from the general OSINT, it really depends on the Chapter you are a member of. Some chapters are more active than others. My chapter has actually put on a fair amount of seminars with experts on various aspects of security, both physical and cyber. I find these live events to be the far more compelling aspect of membership.
Agreed!
Yes, it’s good for that purpose.
Ooops
Whoopsie!
I am in InfraGuard member, and the FBI has not disclosed the breach and the potential exposure of my PII to me.
If I did not follow Krebs, I would not know. The District of Columbia does have breach notification requirements on the books; do they not apply?
Ah…Late news bulletin for you…
Sorry you skipped the US civics class…but who has the time for the mundane?
We are a Federal republic with 53 separate state entities, and 3000+ counties.
Each has the power to enact separate laws, as long as they don’t conflict with the Feds, or its own state’s laws.
Got that?
DC can pass any “municipal law” it wants; no effect on the local FBI HQ (your point).
Congress, by the archaic, sclerotic 1787 Constitution, rules both the FBI and DC.
Much good luck on your further studies of our basic US governing documents…
Glad to have helped your education!
Now you can tackle partisan state gerrymandering, or Presidential pardons as a obstruction of justice tool…
The start of a very long charge sheet, indeed…
FBI might not hire any person nerdy enough to firewall. However, as I see it, the onus is on flabby nerdy. And no, I do not have six-pack absolutely-s. I imagine, is all. Everybody is hacked, or whatever? Axiom of Choice is saying no. Not everybody is getting hacked.
It’s not clear that it is a firewall / hack issue since the data was taken over the API. It’s more of a vetting and policy issue: how much access to allow between vetted members?
Vetting becomes progressively harder as criminal technology advances: even if someone applies in person, how to know that the ID they present isn’t fake along with the stolen credentials they are assuming?
As a former member of InfraGard, back when I applied, we had to physically show up at an orientation meeting at the local FBI field office and were vetted/had our accounts created on site. My membership lapsed when I moved employers, but clearly they relaxed their standards/due diligence. It’s sad to see this happen to an organization that is supposed to be security focused above all else. This news makes me feel a little bit embarrassed to have ever been associated with the program.
The API shouldn’t be wide open for any user to query as they please
It’s not because you must be a “vetted” member.
and vetting makes it super secure
Vetting zoo.
ROFL
So the people who continue to target anyone who does not agree with the mainstream media comments can’t even protect their own Datbase.
I’m just done….the fBI get’s BILLIONS and they can’t even protect something as simple….as an online Database.
Just Wow
I know you’re upset that they investigated your favorites – California congressman TJ Cox and Texas Rep. Henry Cuellar, but investigations target those who ask to be investigated by their actions.
Yup, just like Rev Dr Martin Luther King, right? I have no opinion on the folks you mentioned, for the record. Hell, I don’t even know who they are. Just pointing out that the idea you’re promoting is simplistic and, quite frankly, dangerous. Blind trust in anything – especially government – is foolish.
Those guys aren’t MLK. The comparison is insulting.
I’ll go further, kind sir…
In this libertarian US economy, blind trust in the private sector, and particularly anything connected to electronic commerce , is equally dangerous for a US Consumer.
Have you not heard of truly massive private data base’s breaches and fraud since 2000?
I wish thee much good luck…
With scammers like these, I’m always surprised they don’t get an English-language editor involved to touch up their phishing emails. I know there’s the whole “people who ignore the typos/bad grammar are more likely to fall for further scams” aspect, but as the blog post mentions, these targets are already security-conscious people. The message in the article above is likely to get no hits, while even some basic editing could really clean it up and boost its chances.
That was my first thought too. The letter is supposed to be from a CEO. Did its author really think anyone who writes like that would be CEO of anything larger than a corner vape shop? The letter is a surefire way to eliminate worthless executives: anyone who falls for the letter doesn’t belong in their job.
ChatGPT has entered the chat…
LOL…. exactly
Have you seen the CEO’s of some companies. Sam Bankman-Fried and so many others become celebrity executives.
Totally read this the first time through that the US Department of Defense was hacking the FBI. Funny how in these bizarre times my brain thought yup…that sounds about right.
The FBI is certainly not what they once were…
Don’t know. You could be reasonably certain if you passed information from the CIA to the FBI it would get leaked.
Would the information be used anyway.? Sort of like providing information to the government prior to the piles of dead bodies. But, then again, can they be sure the information is any good without a few dead bodies?* And they do not give out medals they say “I stopped these,” with a little dead body underneath. (Though you can make your own little award and pop it on your desk.)
*Yes
If some kind of report was produced a very long time ago, then you can be sure no one is going to tell you, if it said something like this.
https://www.chathamhouse.org/sites/default/files/2022-04/2022-04-12-ukraine-war-threats-food-energy-security-benton-et-al_0.pdf
…along with a whole lot other of intel, especially if there is gas to be got, and oil to be shipped.
Think of the economic cost for God’s sake, or losing all that election financing! (And the short term political gain in ignoring a whole lot of trouble that likely can’t be solved anyway).
Good God man, what you are proposing would turn the whole system on it’s head! We gave all that information to the FBI about the Russians and that sat on that for decades.
What was it you were saying again?
You know that look Batman has on his face when Catwoman told him something, but he never listened to it?
Bolton, Comey, Clinton all had that look.
Thats better than a cup of coffee. I’ve had big issues with the infragard and its funny that they’ve finally got slapped with Karma.
FBI should have to buy it back…
Aren’t these the guys who want back doors into everything? Sure, they can be trusted with it.
Interesting story. Just wondering if the “major U.S. financial corporation that has a direct impact on the creditworthiness of most Americans” is one of the three major credit bureaus. That possibility tickles my funny bone. Not that I delight in the CEO’s misfortune of being impersonated, especially for nefarious purposes, but might it be an instance of poetic justice that the shoe is on the other foot?
That’s a bingo
Not a security professional, but it seems kind of naive to just accept “USDod said” as an indicator of truth. Particularly one who has claimed to have spoofed the FBI. Where is the indicator they have this data and aren’t spoofing you too?
You mean apart from the fact that I verified they were able to direct message InfraGard members via the InfraGard site with the fake CEO identity they claimed? Or the fact that the FBI confirmed they were investigating a rogue account?
Not a security professional, but I wouldn’t terminate that account either if I could monitor to collect other data on its origin from someone dumb enough to keep logging back in. Here’s another thought – the FBI did reach out by phone to the person who didn’t apply (as the hacker states s/he feared) to confirm it was a penetration attempt, but then approved the account early to see where it would go. It doesn’t sound like a lot of value was obtained in any event – a list of subscribers with most of the other data fields left blank – even assuming USDoD’s claim of what it downloaded is true.
What is astonishing is the lack of due diligence for site membership. If the premise of the site is to share information and communicate among others, then identity verification is critical.
nothing online,is private,someone,somewhere,has all your info,it;s a game called “buy and sell”
I just double-checked my email. I haven’t received any notification from Infragard or the FBI that my information was exposed. Doesn’t this mean they are violating the breach notification standards?
Same – a little let down I found out in my Teams chat last night via a Krebs article. Grateful but still – you’d think they’d say SOMETHING and then back away saying ongoing. I did email and the response I got was the canned one:
The FBI is aware of a potential false account associated with the InfraGard Portal and is actively looking into this matter. This is an ongoing situation, and we are not able to provide additional information at this time.
Federal agencies often aren’t bound by state law.
Fwiw, California’s law is explicitly limited to businesses and state agencies.
Fun trivia: USPS vehicles aren’t required to have and don’t have license plates. (USPS is a constitutional entity.)
Krebs broke the story.
Sus.
So have they locked the site up? I’ve been trying to log in since last night and can’t get in – curious how much of myself I put out there and not really too concerned about it – all of our intense work is done in person and not online there.
The internet is not secure. Never was, and never will be. But it is forever. 🙂
An expose on the shoddy security of the infraguard.org website was published on LinkedIn on 24 Nov. 2019. Title: “Do as I say, not as I do. INFRAGUARD.ORG”.
Article link: https://www.linkedin.com/pulse/do-i-say-infragardorg-arthur-carp/
The author saw this breech coming over 2 years ago, and like Cassandra, the warning was ignored. The author published an number of exposes of insecure organizations including .gov, .mil, and .org where the organizations are government backed. Most were ignored by the entities owning the domains.
USDoD was joking when he said he took it down, he actually released the full dataset for free on the 17th or 18th, albeit behind an 8 credit wall. I don’t know why no one is talking about this. Forum thread title as proof “InfraGard Database – Leaked, Download!”.
I don’t mean to spam, just posting again because I’m not sure if comment is held for review or error posting. Just in case here is redundant comment:
USDoD was joking when he said he took it down, he actually released the full dataset for free on the 17th or 18th, albeit behind an 8 credit wall. I don’t know why no one is talking about this. Forum thread title as proof “InfraGard Database – Leaked, Download!” .
Think about it.
The problem with Infragard is not security. It is the existence of Infragard. In a democratic country, do we really want the FBI running a social media site?
Just what is “social media?”
Infragard is Twitter, with the FBI cutting out the middleman.
Think about it.
The problem with Infragard is not security. It is the existence of Infragard. In a democratic country, do we really want the FBI running a social media site?
Just what is “social media?”
Infragard is Twitter, with the FBI cutting out the middleman.
Much of what other posters have to say about InfraGard is true but if you subtract the snark, these things are true about all human endeavors. None of us always operates at the level to which we aspire, though we hope that in an emergency we’ll be able. And yet we demand that others are at their most capable at all times, especially in retrospect. InfraGard is neither a program for FBI spying on business or a Social Media operation. At its most useful it is a networking group that helps folks to climb out of their silos. We have all heard the phrase: “If you see something, say something.” InfraGard facilitates the conversations that may assist us by introducing us to those of our peers to whom we can “say something’ if the need arrises.