Social networks are constantly battling inauthentic bot accounts that send direct messages to users promoting scam cryptocurrency investment platforms. What follows is an interview with a Russian hacker responsible for a series of aggressive crypto spam campaigns that recently prompted several large Mastodon communities to temporarily halt new registrations. According to the hacker, their spam software has been in private use until the last few weeks, when it was released as open source code.

Renaud Chaput is a freelance programmer working on modernizing and scaling the Mastodon project infrastructure — including joinmastodon.org, mastodon.online, and mastodon.social. Chaput said that on May 4, 2023, someone unleashed a spam torrent targeting users on these Mastodon communities via “private mentions,” a kind of direct messaging on the platform.
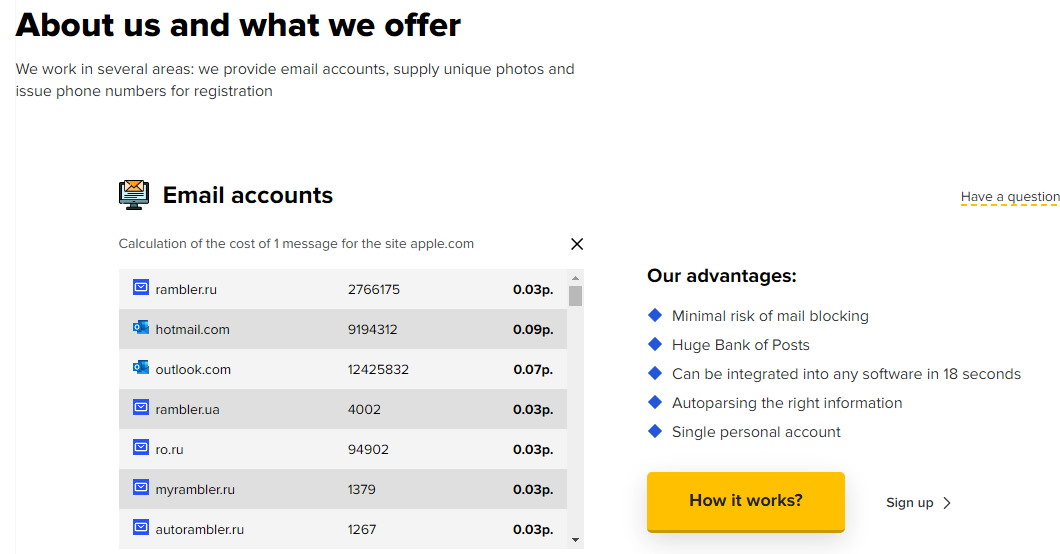
The messages said recipients had earned an investment credit at a cryptocurrency trading platform called moonxtrade[.]com. Chaput said the spammers used more than 1,500 Internet addresses across 400 providers to register new accounts, which then followed popular accounts on Mastodon and sent private mentions to the followers of those accounts.
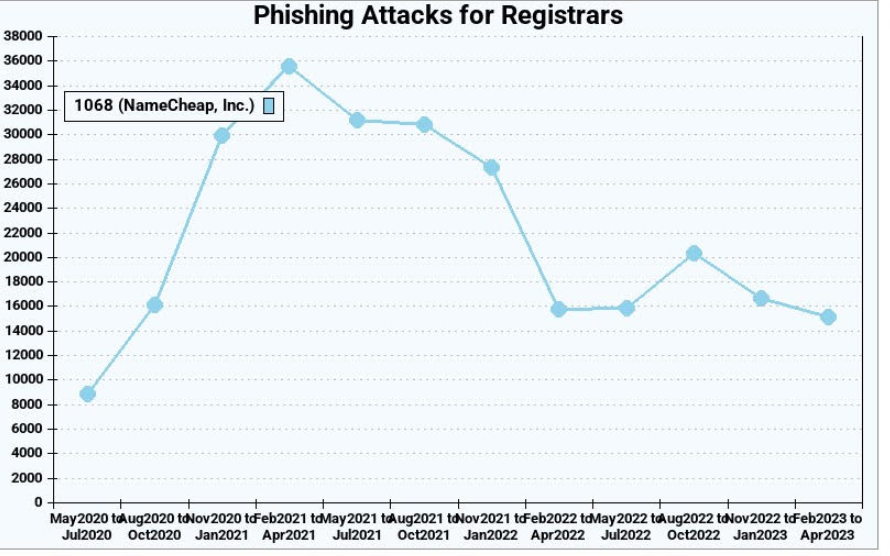
Since then, the same spammers have used this method to advertise more than 100 different crypto investment-themed domains. Chaput said that at one point this month the volume of bot accounts being registered for the crypto spam campaign started overwhelming the servers that handle new signups at Mastodon.social.
“We suddenly went from like three registrations per minute to 900 a minute,” Chaput said. “There was nothing in the Mastodon software to detect that activity, and the protocol is not designed to handle this.”

One of the crypto investment scam messages promoted in the spam campaigns on Mastodon this month.
Seeking to gain a temporary handle on the spam wave, Chaput said he briefly disabled new account registrations on mastodon.social and mastondon.online. Shortly after that, those same servers came under a sustained distributed denial-of-service (DDoS) attack.
Chaput said whoever was behind the DDoS was definitely not using point-and-click DDoS tools, like a booter or stresser service.
“This was three hours non-stop, 200,000 to 400,000 requests per second,” Chaput said of the DDoS. “At first, they were targeting one path, and when we blocked that they started to randomize things. Over three hours the attack evolved several times.”
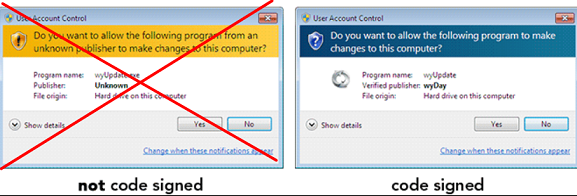
Chaput says the spam waves have died down since they retrofitted mastodon.social with a CAPTCHA, those squiggly letter and number combinations designed to stymie automated account creation tools. But he’s worried that other Mastodon instances may not be as well-staffed and might be easy prey for these spammers.
“We don’t know if this is the work of one person, or if this is [related to] software or services being sold to others,” Chaput told KrebsOnSecurity. “We’re really impressed by the scale of it — using hundreds of domains and thousands of Microsoft email addresses.”
Chaput said a review of their logs indicates many of the newly registered Mastodon spam accounts were registered using the same 0auth credentials, and that a domain common to those credentials was quot[.]pw.
A DIRECT QUOT
The domain quot[.]pw has been registered and abandoned by several parties since 2014, but the most recent registration data available through DomainTools.com shows it was registered in March 2020 to someone in Krasnodar, Russia with the email address edgard011012@gmail.com.
This email address is also connected to accounts on several Russian cybercrime forums, including “__edman__,” who had a history of selling “logs” — large amounts of data stolen from many bot-infected computers — as well as giving away access to hacked Internet of Things (IoT) devices.
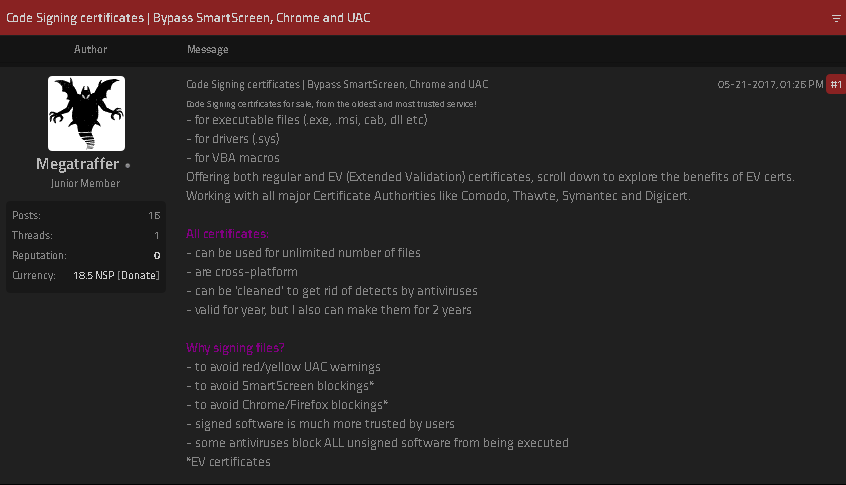
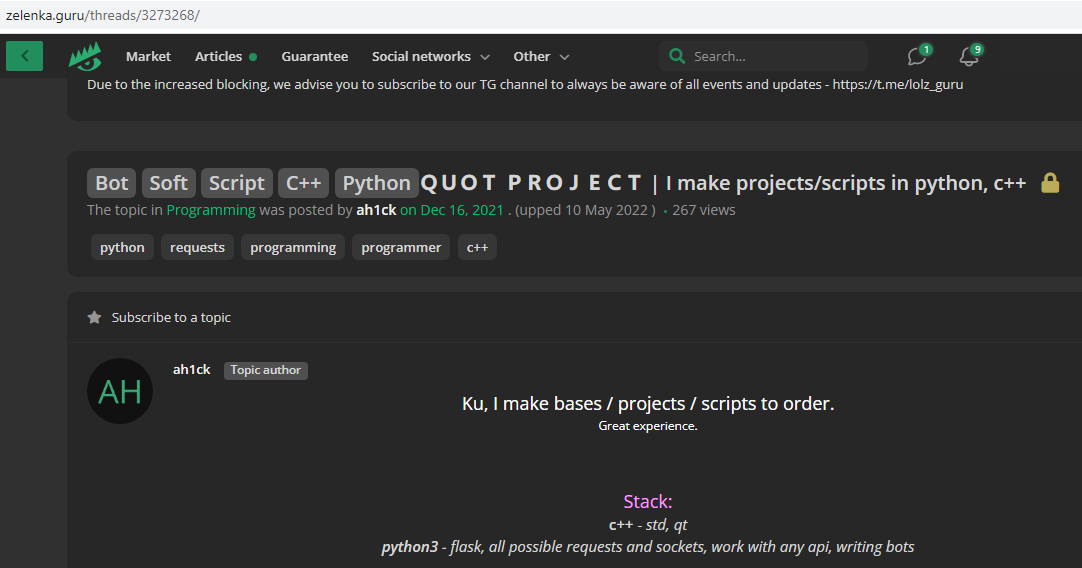
In September 2018, a user by the name “ципа” (phonetically “Zipper” in Russian) registered on the Russian hacking forum Lolzteam using the edgard0111012@gmail.com address. In May 2020, Zipper told another Lolzteam member that quot[.]pw was their domain. That user advertised a service called “Quot Project” which said they could be hired to write programming scripts in Python and C++.
“I make Telegram bots and other rubbish cheaply,” reads one February 2020 sales thread from Zipper.
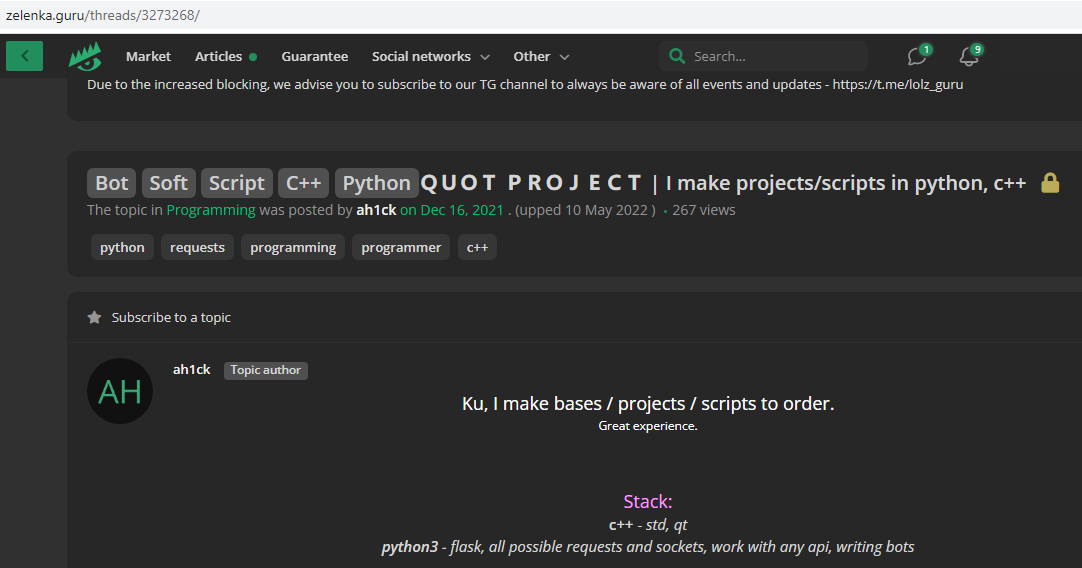
Quotpw/Ahick/Edgard/ципа advertising his coding services in this Google-translated forum posting.
Clicking the “open chat in Telegram” button on Zipper’s Lolzteam profile page launched a Telegram instant message chat window where the user Quotpw responded almost immediately. Asked if they were aware their domain was being used to manage a spam botnet that was pelting Mastodon instances with crypto scam spam, Quotpw confirmed the spam was powered by their software.
“It was made for a limited circle of people,” Quotpw said, noting that they recently released the bot software as open source on GitHub.
Quotpw went on to say the spam botnet was powered by well more than the hundreds of IP addresses tracked by Chaput, and that these systems were mostly residential proxies. A residential proxy generally refers to a computer or mobile device running some type of software that enables the system to be used as a pass-through for Internet traffic from others.
Very often, this proxy software is installed surreptitiously, such as through a “Free VPN” service or mobile app. Residential proxies also can refer to households protected by compromised home routers running factory-default credentials or outdated firmware.
Quotpw maintains they have earned more than $2,000 sending roughly 100,000 private mentions to users of different Mastodon communities over the past few weeks. Quotpw said their conversion rate for the same bot-powered direct message spam on Twitter is usually much higher and more profitable, although they conceded that recent adjustments to Twitter’s anti-bot CAPTCHA have put a crimp in their Twitter earnings.
“My partners (I’m programmer) lost time and money while ArkoseLabs (funcaptcha) introduced new precautions on Twitter,” Quotpw wrote in a Telegram reply. “On Twitter, more spam and crypto scam.”
Asked whether they felt at all conflicted about spamming people with invitations to cryptocurrency scams, Quotpw said in their hometown “they pay more for such work than in ‘white’ jobs” — referring to legitimate programming jobs that don’t involve malware, botnets, spams and scams.
“Consider salaries in Russia,” Quotpw said. “Any spam is made for profit and brings illegal money to spammers.” Continue reading →