The number of phishing websites tied to domain name registrar Freenom dropped precipitously in the months surrounding a recent lawsuit from social networking giant Meta, which alleged the free domain name provider has a long history of ignoring abuse complaints about phishing websites while monetizing traffic to those abusive domains.
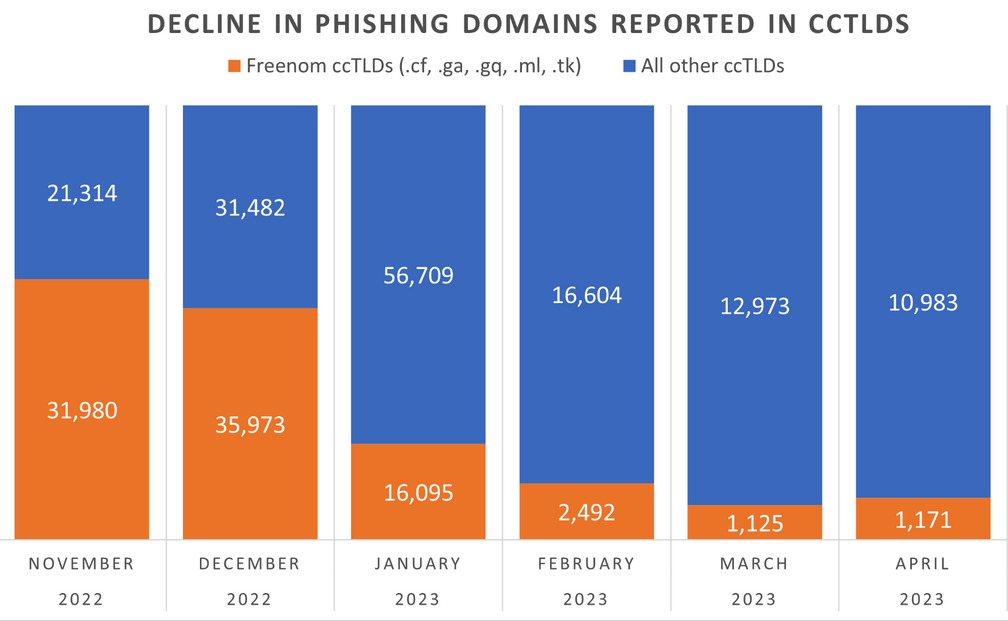
The volume of phishing websites registered through Freenom dropped considerably since the registrar was sued by Meta. Image: Interisle Consulting.
Freenom is the domain name registry service provider for five so-called “country code top level domains” (ccTLDs), including .cf for the Central African Republic; .ga for Gabon; .gq for Equatorial Guinea; .ml for Mali; and .tk for Tokelau.
Freenom has always waived the registration fees for domains in these country-code domains, but the registrar also reserves the right to take back free domains at any time, and to divert traffic to other sites — including adult websites. And there are countless reports from Freenom users who’ve seen free domains removed from their control and forwarded to other websites.
By the time Meta initially filed its lawsuit in December 2022, Freenom was the source of well more than half of all new phishing domains coming from country-code top-level domains. Meta initially asked a court to seal its case against Freenom, but that request was denied. Meta withdrew its December 2022 lawsuit and re-filed it in March 2023.
“The five ccTLDs to which Freenom provides its services are the TLDs of choice for cybercriminals because Freenom provides free domain name registration services and shields its customers’ identity, even after being presented with evidence that the domain names are being used for illegal purposes,” Meta’s complaint charged. “Even after receiving notices of infringement or phishing by its customers, Freenom continues to license new infringing domain names to those same customers.”
Meta pointed to research from Interisle Consulting Group, which discovered in 2021 and again last year that the five ccTLDs operated by Freenom made up half of the Top Ten TLDs most abused by phishers.
Interisle partner Dave Piscitello said something remarkable has happened in the months since the Meta lawsuit.
“We’ve observed a significant decline in phishing domains reported in the Freenom commercialized ccTLDs in months surrounding the lawsuit,” Piscitello wrote on Mastodon. “Responsible for over 60% of phishing domains reported in November 2022, Freenom’s percentage has dropped to under 15%.”
Interisle collects data from 12 major blocklists for spam, malware, and phishing, and it receives phishing-specific data from Spamhaus, Phishtank, OpenPhish and the APWG Ecrime Exchange. The company publishes historical data sets quarterly, both on malware and phishing.
Piscitello said it’s too soon to tell the full impact of the Freenom lawsuit, noting that Interisle’s sources of spam and phishing data all have different policies about when domains are removed from their block lists.
“One of the things we don’t have visibility into is how each of the blocklists determine to remove a URL from their lists,” he said. “Some of them time out [listed domains] after 14 days, some do it after 30, and some keep them forever.”
Freenom did not respond to requests for comment.
This is the second time in as many years that a lawsuit by Meta against a domain registrar has disrupted the phishing industry. In March 2020, Meta sued domain registrar giant Namecheap, alleging cybersquatting and trademark infringement.
The two parties settled the matter in April 2022. While the terms of that settlement have not been disclosed, new phishing domains registered through Namecheap declined more than 50 percent the following quarter, Interisle found.
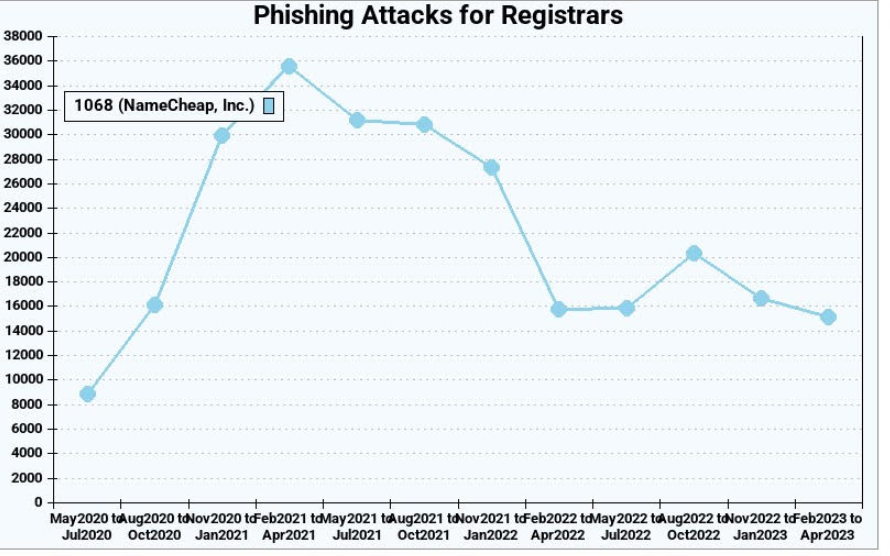
Phishing attacks using websites registered through Namecheap, before and after the registrar settled a lawsuit with Meta. Image: Interisle Consulting.
Unfortunately, the lawsuits have had little effect on the overall number of phishing attacks and phishing-related domains, which have steadily increased in volume over the years. Piscitello said the phishers tend to gravitate toward registrars that offer the least resistance and lowest price per domain. And with new top-level domains constantly being introduced, there is rarely a shortage of super low-priced domains.
“The abuse of a new top-level domain is largely the result of one registrar’s portfolio,” Piscitello told KrebsOnSecurity. “Alibaba or Namecheap or another registrar will run a promotion for a cheap domain, and then we’ll see flocking and migration of the phishers to that TLD. It’s like strip mining, where they’ll buy hundreds or thousands of domains, use those in a campaign, exhaust that TLD and then move on to another provider.”
Piscitello said despite the steep drop in phishing domains coming out of Freenom, the alternatives available to phishers are many. After all, there are more than 2,000 accredited domain registrars, not to mention dozens of services that let anyone set up a website for free without even owning a domain.
“There is no evidence that the trend line is even going to level off,” he said. “I think what the Meta lawsuit tells us is that litigation is like giving someone a standing eight count. It temporarily disrupts a process. And in that sense, litigation appears to be working.”




As I regularly trace and report spam and phishing attempts I have noticed that most such domains are registered by name.com and namecheap.com and reporting to them is pointless, but more recently most such domains come up as Cloudflare. Of course Cloudflare says they have nothing to do with this and it’s a quirk of whois that they are shown as the ISP. However their service is not free and they certainly know who the criminals are but don’t do anything, which presumably is why criminal spammers use cloudflare. It’s sad.
DDoS protection has a free tier. However they are really slow to respond to an abuse report – I have contacted them multiple times within recent 2 years and always it takes from 2 to 4 weeks to receive confirmation letter from their side.
Reporting to Namecheap is very much not pointless, Namecheap acts, and does it quickly.
I have the opposite experience. Namecheap did (I don’t know if they still do) have an open email relay server, which was heavily abused by spammers. They refused to do anything about that open server, and ignored spam reports. That shows that they are spam supporters.
Ulf, I’ve had pretty good luck reporting domains to Namecheap’s Twitter handle. When you provide a link showing a screenshot and deeper explanation they usually have enough to quickly take things down. I just share a link to a phishing site reported in my platform since it collects that information automatically.
as you check news only in phishing , check the material i sent for that notorious dark web that selling data of officers , lawyers , prosecutors on usa… take some news to the next level and let the feds do something about that.
One good thing about the publicity on dangers of .ZIP tld: Trying to phish from BankOfAmerica.zip will be useless since so many people are blocking that tld.
I for the last 25 years have always paid my mobile phone bill on time and I HAVE PAID MANY TIMES even IN ADVANCE my mobile phone bill to T-Mobile, I was not and am not a bad paying T-Mobile customer.
I failed to pay my mobile phone subscription on time last month because someone tampered with my mobile phone subscription without asking me and without my consent and I consider this an abuse and a breach of the contractual terms between T-Mobile and T-Mobile subscribers.
I have been a T-Mobile customer for almost 25 years and someone is making a mockery of T-Mobile customers by changing mobile phone subscriptions to old T-Mobile subscribers by secretly stealing T-Mobile benefits from old T-Mobile subscribers and answering other people other than T-Mobile employees to make a mockery of T-Mobile and old T-Mobile customers, someone is making a mockery of T-Mobile customers, T-Mobile employees and T-Mobile management in the US and those who do these things are Joe Biden and Joe Biden’s relatives employed in the Intelligence Service and Joe Biden’s relatives employed in Mexican-owned companies in the USA Joe Biden’s relatives employed by the Mexican Intelligence Service, Austrians in the US and other people who secretly kill T-Mobile employees in the US to steal their money or part of their money, secretly kill players at the Dinamo club in Romania, policemen, employees of the Mexican Intelligence Service, employees of the Security and Protection Service, employees of the Mexican Secret Service and employees of the Secret Services of the Allied Countries of the Second World War and Japan and ordinary citizens, so people talk or they screw them for life using Mexican Intelligence Service logistics and people are dying or die this way and the people who do this steal their money or part of their money and replace them with duplicates with people who look like the same but they are someone else FALSIFYING FALSE SECRET PROTOCOLS or FALSIFYING FALSE SECRET PROTOCOLS concluded between Comcast Corp and the Mexican Police concluded between Comcast Corp and the Ministry of Internal Affairs concluded between Comcast Corp and the Mexican Intelligence Service, that’s the way people talk.
But you paid your ChatGPT bill?
I think you need to check your meds, Annie.
There’s also a tremendous volume of phishing sites that are spun up on third-party hosting sites like workers.dev (owned by Cloudflare), Dynamic DNS sites (like hopto.org, owned by No-IP), and other similar platforms that allow attackers to bypass site registration (and, therefore, any way to look up a domain as newly-registered) altogether.
While my platforms sees thousands of phishing domains every day, I’d guess that somewhere near 50% of the attacks actually leverage those kinds of platforms instead. Tactics change to whatever is cheap, easy, and effective.
I’d love to see big business group up and stop the registrars allowing brand abuse and stopping these channels for BEC and fraud. It has to be possible.