Tag Archives: spamhaus
Stark Industries Solutions: An Iron Hammer in the Cloud
Two weeks before Russia invaded Ukraine in February 2022, a large, mysterious new Internet hosting firm called Stark Industries Solutions materialized and quickly became the epicenter of massive distributed denial-of-service (DDoS) attacks on government and commercial targets in Ukraine and Europe. An investigation into Stark Industries reveals it is being used as a global proxy network that conceals the true source of cyberattacks and disinformation campaigns against enemies of Russia.
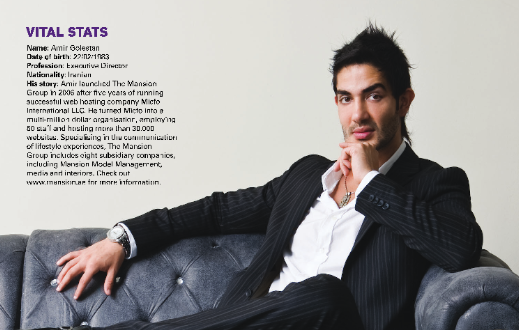
Tech CEO Sentenced to 5 Years in IP Address Scheme
Amir Golestan, the 40-year-old CEO of the Charleston, S.C. based technology company Micfo LLC, has been sentenced to five years in prison for wire fraud. Golestan’s sentencing comes nearly two years after he pleaded guilty to using an elaborate network of phony companies to secure more than 735,000 Internet Protocol (IP) addresses from the American Registry for Internet Numbers (ARIN), the nonprofit which oversees IP addresses assigned to entities in the U.S., Canada, and parts of the Caribbean.
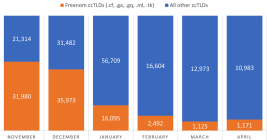
Phishing Domains Tanked After Meta Sued Freenom
The number of phishing websites tied to domain name registrar Freenom dropped precipitously in the months surrounding a recent lawsuit from social networking giant Meta, which alleged the free domain name provider has a long history of ignoring abuse complaints about phishing websites while monetizing traffic to those abusive domains.
DEA Investigating Breach of Law Enforcement Data Portal
The U.S. Drug Enforcement Administration (DEA) says it is investigating reports that hackers gained unauthorized access to an agency portal that taps into 16 different federal law enforcement databases. KrebsOnSecurity has learned the alleged compromise is tied to a cybercrime and online harassment community that routinely impersonates police and government officials to harvest personal information on their targets.
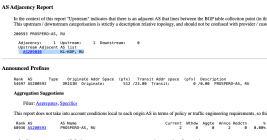
Tech CEO Pleads to Wire Fraud in IP Address Scheme
The CEO of a South Carolina technology firm has pleaded guilty to 20 counts of wire fraud in connection with an elaborate network of phony companies set up to obtain more than 735,000 Internet Protocol (IP) addresses from the nonprofit organization that leases the digital real estate to entities in North America.
Robocall Legal Advocate Leaks Customer Data
A California company that helps telemarketing firms avoid getting sued for violating a federal law that seeks to curb robocalls has leaked the phone numbers, email addresses and passwords of all its customers, as well as the mobile phone numbers and other data on people who have hired lawyers to go after telemarketers.
Feds Allege Adconion Employees Hijacked IP Addresses for Spamming
Federal prosecutors in California have filed criminal charges against four employees of Adconion Direct, an email advertising firm, alleging they unlawfully hijacked vast swaths of Internet addresses and used them in large-scale spam campaigns. KrebsOnSecurity has learned that the charges are likely just the opening salvo in a much larger, ongoing federal investigation into the company’s commercial email practices.
Who’s Behind the Screencam Extortion Scam?
The sextortion email scam last month that invoked a real password used by each recipient and threatened to release embarrassing Webcam videos almost certainly was not the work of one criminal or even one group of criminals. Rather, it’s likely that additional spammers and scammers piled on with their own versions of the phishing email after noticing that some recipients were actually paying up. The truth is we may never find out who’s responsible, but it’s still fun to follow some promising early leads and see where they take us.
Bad .Men at .Work. Please Don’t .Click
Web site names ending in new top-level domains (TLDs) like .men, .work and .click are some of the riskiest and spammy-est on the Internet, according to experts who track such concentrations of badness online. Not that there still aren’t a whole mess of nasty .com, .net and .biz domains out there, but relative to their size (i.e. overall number of domains) these newer TLDs are far dicier to visit than most online destinations.