Avanti Markets, a company whose self-service payment kiosks sit beside shelves of snacks and drinks in thousands of corporate breakrooms across America, has suffered of breach of its internal networks in which hackers were able to push malicious software out to those payment devices, the company has acknowledged. The breach may have jeopardized customer credit card accounts as well as biometric data, Avanti warned.
According to Tukwila, Wash.-based Avanti’s marketing literature, some 1.6 million customers use the company’s break room self-checkout devices — which allow customers to pay for drinks, snacks and other food items with a credit card, fingerprint scan or cash.

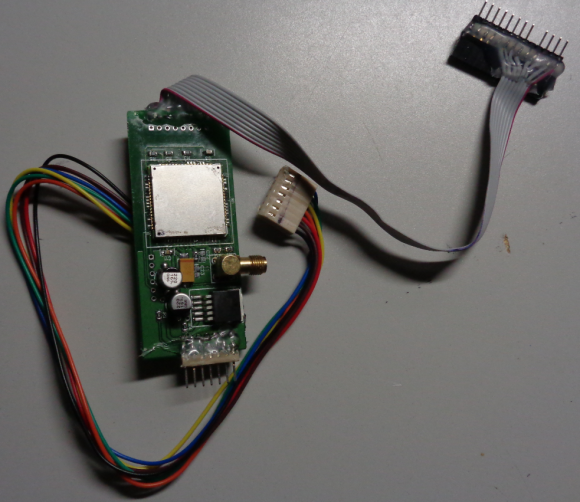
An Avanti Markets kiosk. Image: Avanti
Sometime in the last few hours, Avanti published a “notice of data breach” on its Web site.
“On July 4, 2017, we discovered a sophisticated malware attack which affected kiosks at some Avanti Markets. Based on our investigation thus far, and although we have not yet confirmed the root cause of the intrusion, it appears the attackers utilized the malware to gain unauthorized access to customer personal information from some kiosks. Because not all of our kiosks are configured or used the same way, personal information on some kiosks may have been adversely affected, while other kiosks may not have been affected.”
Avanti said it appears the malware was designed to gather certain payment card information including the cardholder’s first and last name, credit/debit card number and expiration date.
Breaches at point-of-sale vendors have become almost regular occurrences over the past few years, but this breach is especially notable as it may also have jeopardized customer biometric data. That’s because the newer Avanti kiosk systems allow users to pay using a scan of their fingerprint.
“In addition, users of the Market Card option may have had their names and email addresses compromised, as well as their biometric information if they used the kiosk’s biometric verification functionality,” the company warned.
On Thursday, KrebsOnSecurity learned from a source at a law firm that the food vending machine in its employee lunchroom was no longer able to accept credit cards. The source said his firm’s information technology personnel told him the credit card functionality had been temporarily disabled because of a breach at Avanti.
Another source told this author that Avanti’s corporate network had been breached, and that Avanti had made the decision to turn off all self-checkouts for now — although the source said customers could still use cash at the machines.
“I was told that about half of the self-checkouts do not have P2Pe,” the source said, on condition of anonymity. P2Pe is short for “point-to-point encryption,” and it’s a technological solution that encrypts sensitive data such as credit card information at every point in the card transaction. In theory, P2Pe should to be able to protect card data even if there is malicious software resident on the device or network in question.
Avanti said in its notice that it had shut down payment processing at some locations, and that the company was working with its operators to purge infected systems of any malware from the attack and to take steps to “substantially minimize the risk of a data compromise in the future.”
THE MALWARE
On Friday evening, security firm RiskAnalytics published a blog post that detailed an experience from a customer who shared a remarkably similar experience to the one referenced by the anonymous law firm source above.
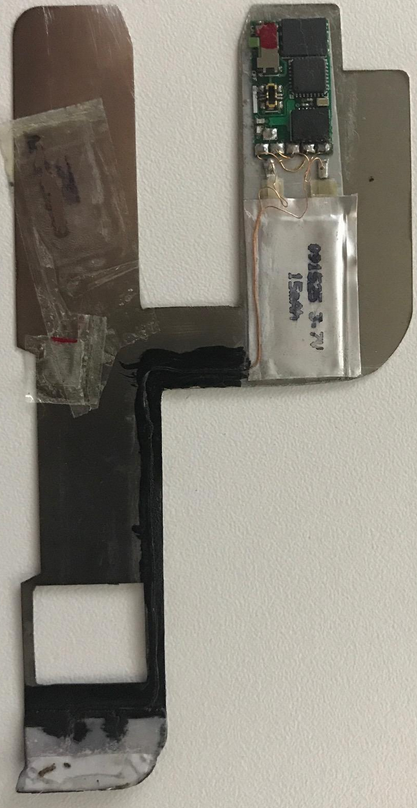
RiskAnalytics’s Noah Dunker wrote that the company’s technology on July 4 flagged suspicious behavior by a break room vending kiosk. Further inspection of the device and communications traffic emanating from it revealed it was infected with a family of point-of-sale malware known as PoSeidon (a.k.a. “FindPOS”) that siphons credit card data from point-of-sale devices.
“In our analysis of the incident, it seems most likely that the larger vendor was compromised, and some or all of the kiosks maintained by local vendors were impacted,” Dunker wrote. “We’ve been able to identify at least two smaller vendors with local operations that have been impacted in two different cities though we are not naming any impacted vendors yet, as we’ve been unable to contact them directly.”
KrebsOnSecurity reached out to RiskAnalytics to see if the vendor of the snack machine used by the victim organization he wrote about also was Avanti. Dunker confirmed that the kiosk vendor that was the subject of his post was indeed Avanti.
Dunker noted that much like point-of-sale devices at many restaurant chains, these snack machines usually are installed and managed by third-party technology companies, adding another layer of complexity to the challenge of securing these devices from hackers.
Dunker said RiskAnalytics first noticed something wasn’t right with its client’s break room snack machine after it began sending data out of the client’s network using an SSL encryption certificate that has long been associated with cybercrime activity — including ransomware activity dating back to 2015.
“This is a textbook example of an ‘Internet of Things’ (IoT) threat: A network-connected device, controlled and maintained by a third party, which cannot be easily patched, audited, or controlled by your own IT staff,” Dunker wrote. Continue reading →







 The updates from Microsoft concern many of the usual program groups that seem to need monthly security fixes, including Windows, Internet Explorer, Edge, Office, .NET Framework and Exchange.
The updates from Microsoft concern many of the usual program groups that seem to need monthly security fixes, including Windows, Internet Explorer, Edge, Office, .NET Framework and Exchange. As it is accustomed to doing on Microsoft’s Patch Tuesday, Adobe released a new version of its Flash Player browser plugin that addresses a trio of flaws in that program.
As it is accustomed to doing on Microsoft’s Patch Tuesday, Adobe released a new version of its Flash Player browser plugin that addresses a trio of flaws in that program.
