For the second time in the past nine months, Google has inadvertently but nonetheless correctly helped to identify the source of a large credit card breach — by assigning a “This site may be hacked” warning beneath the search results for the Web site of a victimized merchant.
A little over a month ago, KrebsOnSecurity was contacted by multiple financial institutions whose anti-fraud teams were trying to trace the source of a great deal of fraud on cards that were all used at a handful of high-end restaurants around the country.
Two of those fraud teams shared a list of restaurants that all affected cardholders had visited recently. A bit of searching online showed that nearly all of those establishments were run by Select Restaurants Inc., a Cleveland, Ohio company that owns a number of well-known eateries nationwide, including Boston’s Top of the Hub; Parker’s Lighthouse in Long Beach, Calif.; the Rusty Scupper in Baltimore, Md.; Parkers Blue Ash Tavern in Cincinnati, Ohio; Parkers’ Restaurant & Bar in Downers Grove, Illinois; Winberie’s Restaurant & Bar with locations in Oak Park, Illinois and Princeton and Summit, New Jersey; and Black Powder Tavern in Valley Forge, PA.
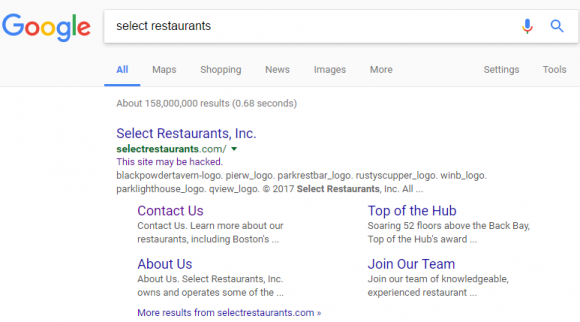
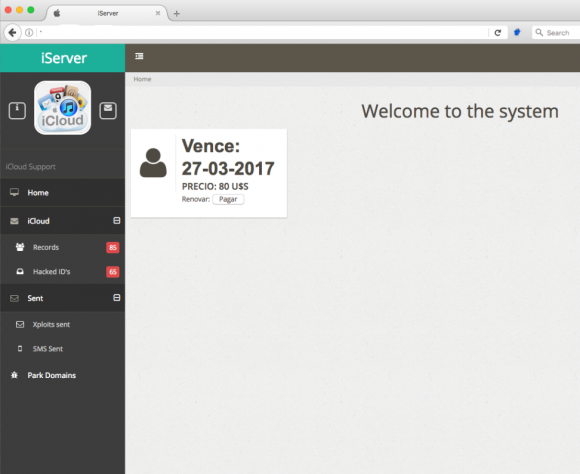
Google’s search listing for Select Restaurants, which indicates Google thinks this site may be hacked.
Knowing very little about this company at the time, I ran a Google search for it and noticed that Google believes the site may be hacked (it still carries this message). This generally means some portion of the site was compromised by scammers who are trying to abuse the site’s search engine rankings to beef up the rankings for “spammy” sites — such as those peddling counterfeit prescription drugs and designer handbags.
The “This site may be hacked” advisory is not quite as dire as Google’s “This site may harm your computer” warning — the latter usually means the site is actively trying to foist malware on the visitor’s computer. But in my experience it’s never a good sign when a business that accepts credit cards has one of these warnings attached to its search engine results.
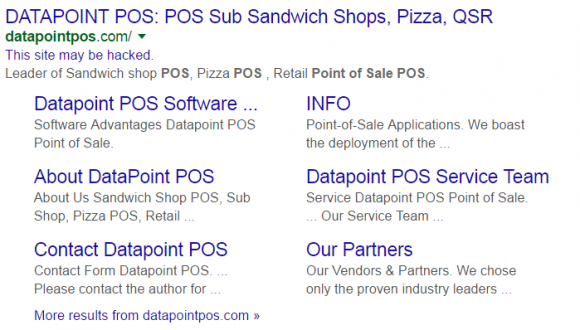
Case in point: I experienced this exact scenario last summer as I was reporting out the details on the breach at CiCi’s Pizza chain. In researching that story, all signs were pointing to a point-of-sale (POS) terminal provider called Datapoint POS. Just like it did with Select Restaurants’s site, Google reported that Datapoint’s site appeared to be hacked.
Select Restaurants did not return messages seeking comment. But as with the breach at Cici’s Pizza chains, the breach involving Select Restaurant locations mentioned above appears to have been the result of an intrusion at the company’s POS vendor — Geneva, Ill. based 24×7 Hospitality Technology. 24×7 handles credit and debit card transactions for thousands of hotels and restaurants.
On Feb. 14, 24×7 Hospitality sent a letter to customers warning that its systems recently were hacked by a “sophisticated network intrusion through a remote access application.” Translation: Someone guessed or phished the password that we use to remotely administer point-of-sale systems at its customer locations. 24×7 said the attackers subsequently executed the PoSeidon malware variant, which is designed to siphon card data when cashiers swipe credit cards at an infected cash register (for more on PoSeidon, check out POS Providers Feel Brunt of PoSeidon Malware).
KrebsOnSecurity obtained a copy of the letter (PDF) that 24×7 Hospitality CEO Todd Baker, Jr. sent to Select Restaurants. That missive said even though the intruders apparently had access to all of 24×7 customers’ payment systems, not all of those systems were logged into by the hackers. Alas, this was probably little consolation for Select Restaurants, because the letter then goes on to say that the breach involves all of the restaurants listed on Select’s Web site, and that the breach appears to have extended from late October 2016 to mid-January 2017. Continue reading




 Microsoft’s
Microsoft’s 

 On March 5, a security researcher named Bashis posted to
On March 5, a security researcher named Bashis posted to