The U.S. Federal Trade Commission (FTC) today said it tracked a nearly 50 percent increase in identity theft complaints in 2015, and that by far the biggest contributor to that spike was tax refund fraud. The announcement coincided with the debut of a beefed up FTC Web site aimed at making it easier for consumers to report and recover from all forms of ID theft.
In kicking off “Tax Identity Theft Awareness Week,” FTC released new stats showing that the agency received more than 490,000 identity theft complaints last year, a 47 percent increase over 2014. In a conference call with the news media, FTC Chairwoman Edith Ramirez called tax refund fraud “the largest and fastest growing ID theft category” that the commission tracks.
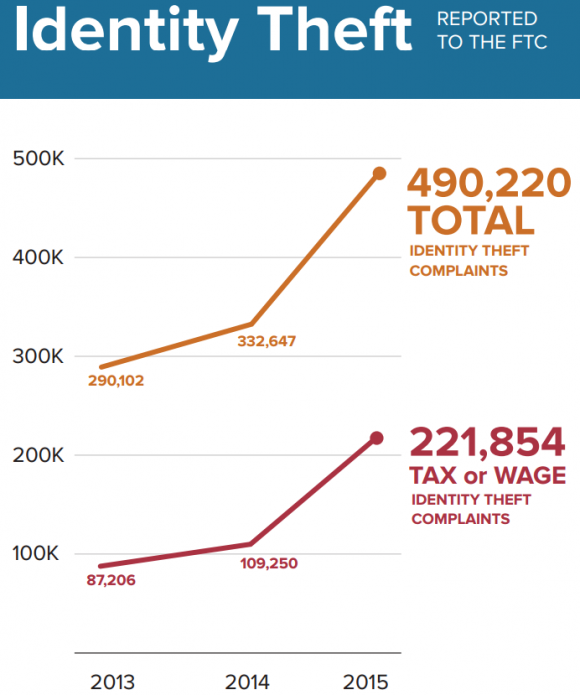
Tax refund fraud contributed mightily to a big spike in ID theft complaints to the FTC in 2015. Image: FTC
Those numbers roughly coincide with data released by the Internal Revenue Service (IRS), which also shows a major increase in tax-related identity theft in 2015.

Incidence of tax-related ID theft as of Sept. 2015. Source: IRS.
Ramirez was speaking to reporters to get the word out about the agency’s new and improved online resource, identitytheft.gov, which aims to streamline the process of reporting various forms of identity theft to the FTC, the IRS, the credit bureaus and to state and local officials.
“The upgraded site, which is mobile and tablet accessible, offers an array of easy-to-use tools, that enables identity theft victims to create the documents they need to alert police, the main credit bureaus and the IRS among others,” Ramirez said. “Identity theft victims can now go online and get a free, personalized identity theft recovery plan.”
Ramirez added that the agency’s site does not collect sensitive data — such as drivers license or Social Security numbers. The areas where that information is required are left blank in the forms that get produced when consumers finish stepping through the process of filing an ID theft complaint (consumers are instructed to “fill these items in by hand, after you print it out”).
The FTC chief also said the agency is working with the credit bureaus to further streamline the process of reporting fraud. She declined to be specific about what that might entail, but the new and improved identitytheft.gov site is still far from automated. For example, the “recovery plan” produced when consumers file a report merely lists the phone numbers and includes Web site links for the major credit bureaus that consumers can use to place fraud alerts or file a security freeze.
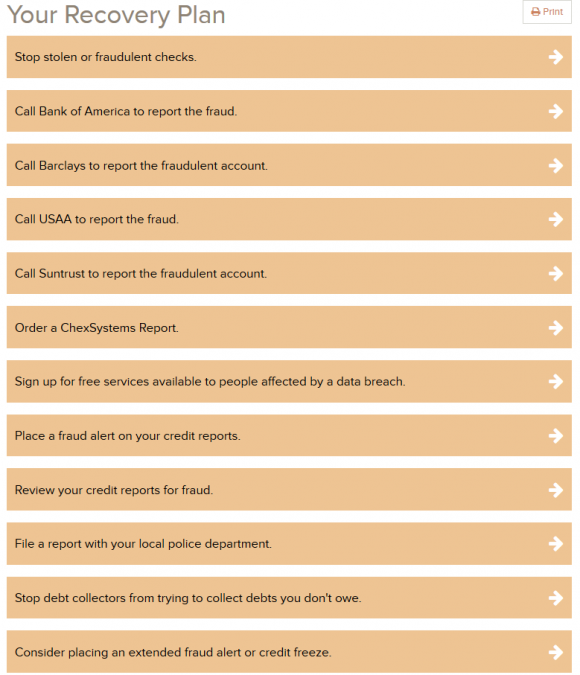
The “My Recovery Plan” produced when I filed a test report claiming the worst possible scenario of ID theft that I could think up. The FTC kindly requests that consumers not file false reports (I had their PR person remove this entry after filing it).
Nevertheless, I was encouraged to see the FTC urging consumers to request a security freeze on their credit file, even if this was the last option listed on the recovery plan that I was issued and the agency’s site appears to do little to help consumers actually file security freezes.
I’m also glad to see the Commission’s site employ multi-factor authentication for consumers who wish to receive a recovery plan in addition to filing an ID theft report with the FTC. Those who request a plan are asked to provide an email address, pick a complex password, and input a one-time code that is sent via text message or automated phone call. Continue reading




 Bob Bertini, spokesperson for the Dublin, Ohio-based restauranteur, said the company began receiving reports earlier this month from its payment industry contacts about a potential breach and that Wendy’s has hired a security firm to investigate the claims.
Bob Bertini, spokesperson for the Dublin, Ohio-based restauranteur, said the company began receiving reports earlier this month from its payment industry contacts about a potential breach and that Wendy’s has hired a security firm to investigate the claims. According to Oracle’s
According to Oracle’s 

 At issue is a cyber insurance policy issued to Houston-based Ameriforge Group Inc. (doing business as “AFGlobal Corp.“) by Federal Insurance Co., a division of insurance giant Chubb Group. AFGlobal maintains that the policy it held provided coverage for both computer fraud and funds transfer fraud, but that the insurer nevertheless denied a claim filed in May 2014 after scammers impersonating AFGlobal’s CEO convinced the company’s accountant to wire $480,000 to a bank in China.
At issue is a cyber insurance policy issued to Houston-based Ameriforge Group Inc. (doing business as “AFGlobal Corp.“) by Federal Insurance Co., a division of insurance giant Chubb Group. AFGlobal maintains that the policy it held provided coverage for both computer fraud and funds transfer fraud, but that the insurer nevertheless denied a claim filed in May 2014 after scammers impersonating AFGlobal’s CEO convinced the company’s accountant to wire $480,000 to a bank in China. In
In  Toni Casala found this out the hard way. Casala’s firm — Children in Film — works as an advocate for young actors and their families. The company’s entire operations run off of application hosting services at a managed cloud solutions firm in California, from QuickBooks to Microsoft Office and Outlook. Employees use Citrix to connect to the cloud, and the hosting firm’s application maps the cloud drive as a local disk on the user’s hard drive.
Toni Casala found this out the hard way. Casala’s firm — Children in Film — works as an advocate for young actors and their families. The company’s entire operations run off of application hosting services at a managed cloud solutions firm in California, from QuickBooks to Microsoft Office and Outlook. Employees use Citrix to connect to the cloud, and the hosting firm’s application maps the cloud drive as a local disk on the user’s hard drive. Six of the nine patches Microsoft is pushing out today address flaws the software giant considers “critical,” meaning the vulnerabilities could be exploited by malware or miscreants to break into vulnerable computers remotely without any help from users. The critical updates tackle problems with
Six of the nine patches Microsoft is pushing out today address flaws the software giant considers “critical,” meaning the vulnerabilities could be exploited by malware or miscreants to break into vulnerable computers remotely without any help from users. The critical updates tackle problems with 