In the previous two stories, I documented the damage wrought by an organized crime gang in Mexico that has been systematically bribing ATM technicians to install Bluetooth skimming components that allow thieves to steal card and PIN data wirelessly. What follows is a look at a mysterious new ATM company in Mexico that sources say may be tied to the skimming activity.
One ATM company operating in the Cancun area whose machines were apparently free from these skimming devices is a relatively new entity called Intacash. This company’s ATMs positively blanketed many of the areas I visited, particularly in the heavy tourist and commercial areas of downtown Cancun and Playa Del Carmen. For example, in a single city block on Boulevard Kukulcan in Zona Hotelera — probably the busiest tourist spot in Cancun — I counted no fewer than ten Intacash ATMs, most of which were all less than a couple hundred yards from each another.

Intacash ATMs positively blanket the most busy area of downtown Cancun and in very tight proximity to one another.
The experts I spoke with said they were mystified by Intacash’s strategy of placing so many cash machines in the region. Even for areas like Zona Hotelera with plenty of continuous foot traffic, adding so many cash machines in such a small space produces diminishing returns.
Two different ATM experts familiar with rates charged to place ATMs in the area and who asked to remain anonymous said there is no way Intacash could afford the rent required to place so many ATMs in such close proximity on public property and still turn a monthly profit. No way, that is, unless the company had a different profit motive in mind.
Intacash is a relative newcomer to the ATM scene in Mexico, bringing its first ATMs online there a little more than a year ago. It’s not at all clear who runs or owns Intacash, and there is precious little public information available about this company.
Intacash.com, registered in early 2014, consists of just four Web pages. There is no contact information for the firm on its site, which to this day has exactly zero sites linking in to it. From its inception, the site’s registration records have been hidden behind WHOIS privacy protection services. Intacash hosts its sites along with more than 6,000 other sites on a shared server at GoDaddy.com (for security and other reasons, financial institutions and service providers more typically spring for their own, dedicated servers).
Despite the presence of nearly 70 Intacash ATMs in Cancun, Playa Del Carmen, Tulum and other tourist areas in the Yucatan Peninsula, this company seems to have gone out of its way not to be noticed online. What’s more, a review of the text on Intacash.com suggests that much of the Web content on the site has been copied verbatim from other sites that preceded Intacash’s existence on the Internet.
Multiple emails sent to the contact addresses and forms on Intacash’s Web site went unreturned. Intacash’s sponsor bank in Mexico – Multiva — also did not respond to messages seeking comment.
THE INTACASH CONNECTION
Why was I so keen to learn more about Intacash? My source in the ATM industry who tipped me off about the Bluetooth skimming activity showcased in the first two stories here said his technicians began receiving bribes to let strangers install skimming components inside their machines around the same time that Intacash came online in Mexico. By early this year, all of my source’s ATM technicians had reported being approached by one of two guys who were trying to buy access to ATMs. The employees who reported these incidents to my ATM industry source said the men had Eastern European accents.
Several of my source’s employees later identified the men who approached them after managing to locate their profile pages on Whatsapp, a popular mobile messaging service.
“My partner was at a meeting with the operating manager of [a major hotel] in Cancun, doing his sales pitch,” my source recalled in a recent interview. “And the fellow at the hotel told my guy that just the day before he’d been approached by another ATM company, and that the guys were Eastern European.”
My source said that, when pressed, the hotel manager acknowledged that the other company was indeed Intacash. My source said his business partner happened to have bookmarked on his smartphone the Whatsapp profiles of the men who’d tried to bribe his technicians, and that he opened the profiles one by one and showed them to the hotel manager.
“My partner asked, ‘Just out of curiosity was it one of these guys?'” my source said. “The hotel manager said why, yes it was.”
ANALYSIS
Intacash may in fact be totally above-board. But beyond the above-mentioned circumstantial oddities, there are other clues that would suggest something is not quite right at Intacash.
For example, in my wanderings around Cancun and elsewhere in the region, I used a low-balance debit card to check out multiple Intacash ATMs — each of which offers customers the option to withdraw Mexican Pesos or U.S. Dollars. Curiously, every time I used one of these machines to make small Peso withdrawals, I received a paper receipt. Each time I took out dollars, I got no receipt (this behavior was the same across multiple Intacash machines).
In about one-third of the cases, after entering my PIN, the transactions were canceled without explanation (no receipt was issued in those failed transactions either). When I returned home and began researching this, it turns out I was not the only one who noticed this pattern.
Even more curious, Intacash ATMs charge nearly twice as much as virtually any other ATM company in the region for withdrawing funds — often 10 percent to 15 percent of the value of the withdrawal. I would imagine that a large percentage of consumers who put their cards and PINs into an Intacash ATM would cancel the transaction and look for another machine after seeing that withdrawing $100 would cost them $15.
I began to wonder whether it was possible that Intacash was a company essentially set up to capture card and PIN data? Phony ATM companies are certainly not unheard of, even in the United States. Back in 1993, U.S. federal agents arrested two men in Connecticut suspected of stealing more than $100,000 by placing fake ATMs. In the Connecticut case, the fraudsters simply placed fake ATMs that were devoid of cash. That may sound like a clever scheme, but the lack of cash in those machines is what quickly tipped off investigators that something was fishy about the ATMs.
Well, hang on a moment, you say: Wouldn’t selling or otherwise exploiting ATM/debit cards all stolen from one ATM company’s machines quickly draw unwanted attention from the banks, Visa and MasterCard to that company? You bet: Anyone in charge of such a fraud operation would want to spread their card-cloning scam across as many ATMs as possible: The more ATMs and the more ATM companies involved, the harder it is to trace the source of the fraudulent transactions. And here we come full circle to the cash machines in and around Cancun that were compromised with internal Bluetooth skimmers.
In addition, the absence of receipts and the propensity for ATMs to randomly “cancel” transactions after users insert their cards and enter their PINs would make it easier for a large card cloning operation to hide much of their activity. For example, if the transaction is cancelled before it reaches the processing switch of the customer’s bank, there would be absolutely no record of the customer using the ATM, despite the card data and PIN being compromised
How much could a fake ATM operation with 70 ATMs pull in each month? Various ATM companies I spoke with in the process of reporting and writing this story said — depending on the location — a typical machine may need between 300-500 customers per month to become profitable.
If we take the low end of that, and assume that some customers (let’s say 30 percent for rounding purposes) will be repeat customers using the same card and PIN, that’s conservatively 200 cards per month per machine. Even if the average checking account tied to each ATM card had just $100 in it, that’s $20,000 per machine per month, or — again, very conservatively — about $1.5 million across all 70 machines per month.
THE KEY ROLE OF ATM TECHNICIANS
Several readers have asked why experts are so certain that ATM company installers — not random crooks — had to have been responsible for installing the Bluetooth card and PIN pad skimmers in the compromised devices I found in Mexico. The explanation has to do with the reality that modern ATMs are designed to protect the security and privacy of the user’s PIN once it is entered into the system, and more importantly to protect the integrity of the PIN pad itself.
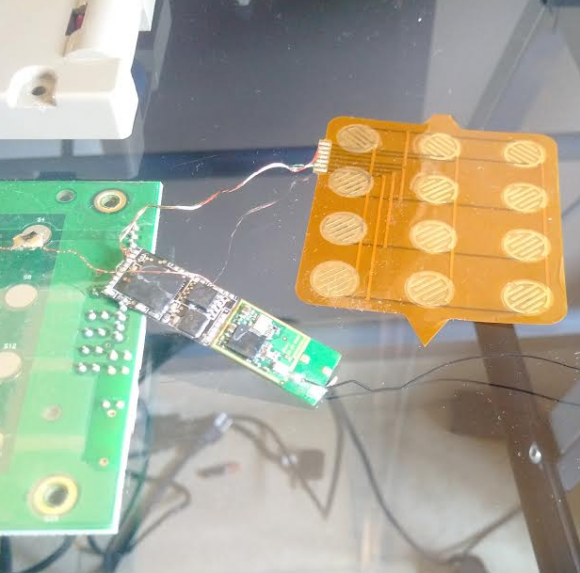
One of the Bluetooth PIN pads pulled from a compromised ATM in Mexico. The two components on the left are legitimate parts of the machine. The fake PIN pad made to be slipped under the legit PIN pad on the machine is the orange bit, top right. The Bluetooth and data storage chips are in the middle. The antenna for the Bluetooth board can be seen trailing off the right side of the photo.
If a random thief were to break into an ATM and attach electronic devices capable of intercepting PIN codes entered by customers, the ATM would simply cease to function properly after that. When ATM makers or banks wish to update software or hardware on their machines, they must subsequently input a special cryptographic key. That key — known as the “terminal master key,” is good for that machine and that machine only — and it comes directly from the manufacturer or the bank.
Some banks and ATM companies go a step further, requiring all such changes to be approved by two authorized personnel. This dual-authentication approach — the use of two keys, each assigned to different personnel who must approve physical and software changes to the ATM — is designed to short-circuit any attempts by rogue ATM installers to do what’s apparently been done in many Mexican ATMs. And it is likely that the victim ATMs documented in this series were not following this best practice.
Also, some readers have asked whether there was anything in particular about Mexico that made ATMs there more likely to be victimized by sophisticated ATM fraudsters who bribe their way into cash machines. I think the answer is yes and no. For one thing, the risks of doing this in the United States are far higher. It seems likely that anyone convicted of hacking cashing machines this way in the United States would be facing federal fraud charges and serious jail time here if convicted.
In Mexico, it seems unlikely such a person would ever even be prosecuted, let alone jailed for any length of time. Security experts I spoke with in Mexico said it is exceedingly easy to buy one’s way out of prosecution or jail in Mexico if one has the right amount of cash, and certainly an enterprise in charge of a skimming business or a fake ATM empire would indeed have plenty of that.
But in practice, this scheme could happen anywhere in the United States, and I would fully expect it to migrate north of the border soon (if it hasn’t already). There are no doubt plenty of ATMs that allow the swapping in of hardware without requiring two people to sign off on the change, and people here are obviously susceptible to bribes. It’s also worth noting that technicians here and abroad alike can be coerced into cooperating with thieves via non-financial means, such as extortion or threats to their personal safety and/or that of their families.
Finally, many readers have asked if any of the skimmed ATMs I found in Mexico were bank-owned and operated ATMs, or machines on the premises of bank properties. None of them were: All were free-standing cash machines owned and operated by private companies.
If you haven’t already seen them, please check out the first two stories in this series:





When in Mexico, I use the ATMs at Banks, and I have a travel account, where I keep a limited amount of money, and transfer more funds as needed over a VPN connection that I trust. Freestanding ATMs are obviously suspect, even without these revelations. Good story, though.
Chris, I live in Brasil. The only time I have had a card compromised was in a bank lobby ATM of a major European based bank. There is no real barrier to installing the skimming device in a stand alone ATM v. bank ATM, it is just about bribing the supposed security people or installing the device in a clandestine manner.
I use two separate accounts for cash withdrawals, and only fund those accounts online as I am leaving to make the cash withdrawal. That way, even if my card(s) are compromised, the account is empty or has only a few dollars in it. Still, when my card was compromised, the thieves made cash withdrawals larger than my daily limit, and overdrew the account. So, it appears there is simply no truly fail safe way to use an ATM, anywhere. Even using the Bluetooth signal detection suggested by Mr. Krebs is not foolproof, the ATM could have an old fashioned style skimmer, though you might avoid problems with those by covering your hand when entering the PIN.
You should try to get an account that doesn’t allow for overdrafts…
But mostly, you shouldn’t use debit cards at all. A credit card and merchants which provide cash back (grocers, or restaurants where some people pay in cash) is much safer.
The experts I spoke with said they were mystified by Intacash’s strategy of placing so many cash machines in the region.
“The sunk cost fallacy (“Concorde fallacy”, “escalation bias”, “commitment effect” etc.) could be defined as when an agent ignores that option X has the highest marginal return, and instead chooses option Y because he chose option Y many times before, or simply as “throwing good money after bad”. It can be seen as an attempt to derive some gain from mistaken past choices. (A slogan for avoiding sunk costs: “give up your hopes for a better yesterday!”) The single most famous example, and the reason for it also being called the “Concorde fallacy”, would be the British and French government investing hundreds of millions of dollars into the development of a supersonic passenger jet despite knowing that it would never succeed commercially (as it did not by its last flight in 2003). Since Arkes & Blumer 1985’s2 forceful investigation & denunciation, it has become received wisdom3 that sunk costs are a great bane on humanity.”
http://www.gwern.net/Sunk%20cost
Adding more ATM’s won’t improve it. Even with more migrants more machines are going to operate at a loss and tourism is down and crime is up.
“I no longer gave a damn about three-car garages and swimming pools, nor any other status symbol or “security.” There was no security in this world and only damn fools and mice thought there could be.
Somewhere back in the jungle I had shucked off all ambition of that sort. I had been shot at too many times and had lost interest…”
Ch. 3 Glory Road
I wonder if IntaCash is also laundering money (USD) with these many machines?
Great work Brian.
Some observations for what it’s worth:
1. The Common point of purchase (cpp or what i call detection by intersection) can be gamed in a similar manner to a cyclical redundancy check (CRC) as it comes down to both being polynomials. With a network of tainted devices, the black hats could theoretically make the CPP anything they wish. It was only a matter of time before cpp becomes useless due to increased ability of the black hats to trellis the compromised card info. Anyway, much like crc, cpp works great on single bit errors, but not so well if gamed with long bit bursts, or temporal shifts like resequencing the bit errors. Eg. Swipe data card 1, use card at local merchant, then hit up competitor’s atm. Swipe data card 2, use at same local merchant, then use on own atm machine. Common point of purchase? merchant, though they are clean, it was the atm with no record that rigged the cpp.
2. The bluetooth signal is an obvious mistake by the black hats that will certainly be addressed, thus folks may get a false sense of security if they scan for free2move and feel they are safe(er) when no signal is shown. The safe assumption, for those wanting to be safe, is to assume the free standing machines are potentially malicious after scanning shows no bt signal (much like scanning for viruses does not protect from zero day exploits.). after scanning one can know they are unsafe (free2move found), or not know if one is unsafe(signal turned off, name change, or other compromise. ). But we can’t conclude ‘safe’ because of the negative test result.
3. Some folks are confused because they used bank machines and were compromised. Two points here, first, there is no natural law that says there is only one scam operation ongoing at any time, so there could very well be, and could be other scams ongoing. And second, mexican, domincan, and banks located in similar situations have edges beyond the atm machine itself, particularly if debit cards drawn on the bank rather than credit v/mc transactions. So it may be connected, may be opportunistic , may be an atm compromise, or internal bank compromise. The timing is a correlation, but it is not necessarily related(correlation is not causation).
4. The scanning, looking about the machine, etc are all ways the user is trying to make up for the fact that the card doesn’t authenticate the machine. The system is designed to authenticate the user, but fails to allow the user to authenticate the system they are using the card on. Skimming is made possible in part because of the one sided authentication. Folks should remember, compromised or not, the atm is ‘the man in the middle’.
Lastly, more than just great reporting, your work on the ground should create some movement of the back hats that will hopefully make things a bit more clear.
I see some problems. Some of the above think security is in place in ATM’s. Everywhere. But, and here is other skinny, I’m from the KC area. Last fall the son of one of the biggest crimelords in the us, was arrested for skimming money at atm’s. The easy way, he was working for the company as one of the guards that refilled the machines. He had the service keys for the machine. At times he was in the banks filling the machines. And the machines have a master key, so the vibration sensors are turned off then, when getting serviced, so now all that is needed is a guy with a bt chip turned to no broadcast, waiting for you to input a data card.
Will this help the holders of the new cards? For a while, but I would bet within 60 days, the scams will be back in business, greater computing power will be readily available, compromised skimmers will used to force feed the numbers at an ever increasing rate to the clearing houses. For cash at first, from “stolen” machines still on the network.
Blue tooth is not a one way device, it can be used to receive as well. Has anyone checked the output of the device card, to see if it inputs as well? It could be used as a compromiser of the circuit? as well as an input point, use a blank card, have the data on a phone, feed into the circuit, withdraw. get cash, till the machine is empty.
It is very interesting that some company named “DiseñO2” posted on 15th July renders for Intacash ATM. Then this page was deleted from facebook but you can still find it in google cash: http://webcache.googleusercontent.com/search?q=cache:jXcHZ5wloG4J:https://www.facebook.com/pages/Dise%25C3%25B1O2/313933928729231%3Ffref%3Dphoto
May be there can be found traces.
Brian: You can not just set up an ATM in a tourist area, you obviously need a connection to a processor, who in turns connects to Banks and or Visa/MC. So why can Intacash not be identified? There must be some sort of authentication between each ATM and the host it is connected to. Also: you need a router for your internet connection, and that also needs to be registered at a local ISP. I think in the states this company could easily be identified.
If this were in the US, that would certainly be true. But given the rampant corruption in Mexico, I am not sure how easy that would be when the ISPs themselves could be compromised.
The ISP might only need to tip off the criminal gangs that someone is asking, and then ignore your request. I suppose you could say that you would find out who is responsible when they come after you.
@Brian:
>> said there is no way Intacash could afford the rent
>>required to place so many ATMs in such close proximity on public
>>property and still turn a monthly profit. No way, that is, unless the
>>company had a different profit motive in mind.
well – on the intacash website – I think they explain their business-model quite well:
they actually ‘rent’ out the ATMs to interested parties – or allow you to ‘invest’ into ATMs. (and give you even the option to stock the cash yourself – how cool is that ?)
… but yeah – the whole idea smells a lot like money-laundering.
(and very often money-laundering models are accepting to make some losses – if the turnover justifies it)
One has to wonder if the bad actors getting card data are any better with their passwords than the rest of the world.
They’re of course no better.
Firstly, the grunts stealing are usually not tech experts, let alone the people ordering the details.
Even more advanced security researchers with nothing to do regarding fraud per se, such as 001, used the password, xaxa23 on HY.
Brian,
Im very concern about your history but there are a lot of other brands there as cash hola, direct cash and more what about them??
A few years ago I had an experience at a Tulum ATM machine where it cancelled out the transaction after entering my pin. No receipt or cancel transaction slip received. Second attempt, same thing. Third attempt I got my cash. Unfortunately my bank statement showed three completed transactions, not just the one that worked.
Last year in Cancun I had a 7-11 gas attendant (yes gas stations still have attendants) tell me my credit card wasn’t working. After trying four cards I had no choice but to use the ATM and pay cash for my already pumped gas. All four cards ended up getting charged, so I paid for that $40 tank of gas five times including the cash transaction.
You are a hero Brian.
This type of investigation shows how one man CAN make a difference.
How about using a crowdsourcing method of aggregating lists/maps of ATM machines and reviews.. Totally doable for a concentrated tourist area.. Like a Yelp for ATM machine for travelers.. Startup idea anyone ?
Finally shows that even in an otherwise safe tourist areas folks should never let their guard down. Very good tips here on how to protect yourself and limit downside risk (change PINS, travel ATM card, etc.).
Loving this series, I was on the edge of my seat to hear what was going to happen next, thank you.
Your point at the end that technicians here and abroad alike can be coerced into cooperating with thieves via non-financial means made me wonder when the online hacks that were not financially motivated will surface to coerce people in sensitive roles to do things they would otherwise not want to do. If bribery doesn’t work, how about blackmail? It certainly wouldn’t be novel, governments have been doing it to spy on each other since ever. I’d like to think those in positions of responsibility were already considering this risk and planning against it, but they seem to have a hard enough time keeping data secure.
Please write more like these. 🙂
Never go to an ATM that isn’t physically in a bank. You should do this in EVERY country, including your home country, not just in Mexico.
Ditto.
Even without the bluetooth skimmers, there are otherways to steal PINs.
Only use ATM machines inside a bank, there are so many, why risk it?
In Mexico, there is enough labor and no surcharge to use a human teller too.
There is a risk at every ATM regardless if its in a bank or not. There have been many instances of all types of skimming devices being on Bank ATMs in Mexico, the USA, and Canada etc… General rule of thumb is to go with the names you see everywhere. The bigger a presence a company has, bank or street ATM, that usually means they are a bigger company and take security seriously. Typically I find a machine I’m familiar with and use it – any changes in the fascia, pin pad, or card slot and I call the company and ask before using it – Bank or Street ATM. Any legit company will answer their customer service phone number and send a technician out to check it for you.
I am no luddite, I use ATMs often enough, but primarily for small amounts of money, and I always, always use my own bank’s ATMs. For amounts larger than $20 or so, I get “cash back” at a store, and for really large amounts I go inside the bank and get cash in person. I also watch my checking and savings accounts online.
I’d think the card can be skimmed independently if you get $20 or $2000 from the ATM 🙂
Along the US Mexico border you will see countless of Currency Exchange outlets. Reason is Money Laundering! I’m sure skimming info is one reason, but money laundering is another.
Great investigative journalism Brian.
Another reason not to visit that slum called Mexico.
Thanks for your constructive comment, Warren.
Dear Brian,
I read your articles from several years now and somehow I always like them and find interesting things among them. I’m probably just one of your constant readers.
But now I start to have some … doubts, to be very light expressing that. Because at least your last article have behind either a very light documentation or either malicious intends lead by a third entity.
First, Intacash it’s a pan-american company. Second, it’s not a own operator company. I run under contract that company for about one year. So, let me make some things clear regarding … your points of view.
1. In Mexico, because of the cartels and out of law gangs the owners of companies prefer to be anonymous. It happened, not once, that owners of health companies to be kidnaped and force either to pay a protection monthly fee or a ransom or, worse, to be forced to sale their companies for nothing to the gangs. But in the case of Intacash, you have on each ATM (a sticker) and on the receipt, customer service phone numbers and the name of the company. So, you can reach the company as far as you really want to do it. Moreover, if you stay close to a company ATM you will meet, at least once per day, an employee which check the machine : technical team, technical supervisor or security. Exactly against skimmers. And all of them are using company outfits and badges, so you can’t miss them.
2. I don’t know your sources and experts you talk about in the industry but … In the ATM network industry everything has to do with the traffic. About 3-5% of the traffic in front of an ATM will use it. So, if you have an area with different traffic paths, in and from different directions, you can put an ATM on every path even if they are very close one to each other.
3. Most of the Intacash ATMs are in private spaces not in public ones. For example, in Cancun exist no one on a space owned by the municipality. The exception is in Playa del Carmen where the traffic it is mostly on the Quinta Ave. And again your experts lead you to a wrong way : they can’t get to instal ATMs in the most important shopping malls and best traffic paths because they are most of them unprofessional and the board of directors of the malls refuse them. In the places where they bribe management, they installed and pay the same rent. So, they afford it.
4. As you said, the single company ATMs which you didn’t find with any skimming device was Intacash ATMs. Like a journalist as you are, I hopped that you could go beyond what “an expert” from industry could tell you about. Of course that the competition are driving crazy by the success of Intacash and by the fact that it seems that the company grow healthy and fast. And now I will reveal you how : most of the others companies have one(1!) technicians for each about 80-100 ATMs! If a gang member bribe that technicians he maybe has access to all that 80-100 ATMs. On the other hand, again you was mislead : most of the old ATMs machines could be “penetrate’ without the technician. And 90% precent of the others companies in that area use old and very old ATMs. Most of them have not evan EMV (chip card reader kit). In the meantime, Intacash use only teams (two technicians in the same area, in the same time) and they are random assigned every day to another ATMs. More than that, every two teams has a technical supervisor and a technical manager who also make visits on the field. Over this, are the security teams who are trained to discover skimming devices. And who pay a visit to each ATM once at two days at least. The ones which are in high traffic paths are even scheduled with two visits per day. So, if somebody want to bribe a technician and have access to this ATMs they should bribe at least 15 people at once. Because the company use only new banking top notch ATMs which has all the anti-skimming devices included and it’s almost impossible to be “penetrated” without internal help. The Intacash has also cameras installed on or in the proximity of most of company ATMs. That’s why you find all the Intacash ATMs free of any skimming devices.
5. Most of the skimming gangs in the area are Venezuelan. And some Bulgarians also. They tried to bribe our technicians also. And most of them are not using male person to approach technicians. They use beautiful women who approach the technicians and the story it’s almost all the time, the same : I own a shop/store/hotel in the area and I want to instal an ATM. Could you help me ? If it works they go further with offers. We do the same like your “friend” did and we had a decoy technician who “accept’ the bribe. But they can’t deliver a skimming devices for our machines. They said that the Intacash ATMs are too complicated and with too much anti-skimming technology.
6. You gone be maybe surprised but the Intacash company it’s the most profitable company in the area. Exactly because it’s reliable, it’s safe, has the best up time, has the best customer service and it’s clean. And the income, taxes and profitability any authority could obtain them from the fiscal institution. Moreover, can’t be money laundry : they don’t use their money. All the money it’s from a credit facility from Multiva Bank. Nobody from Intacash touch any money. They came from Multiva and go to Multiva every month. Only the profits came back … also from Multiva. It’s everything about planning and management.
7. As per no receipt for the dollar transaction, as far as you get one for the pesos transactions, that means that it’s a problem with the soft of the PROSA (the national operator of financial transaction) at that moment. As an expert you are, I am sure that you know that an ATM it’s basically a very simple computer and that the soft it’s loaded by internet, half of it by the bank and half by the operator (PROSA) and has nothing to do with the company who runs that ATM. Again, it’s a security measure. Which is the same all over the world. But before you agree to make a transaction, you are always asked on the screen if you want to do it and what the charges are. It is by law and again has nothing to do with the will of the running company : Prosa and Multiva software do that. You can’t skip it.
In the end, I work no more in Mexico from almost an year now but that’s the facts in that part of the world. It is true, are a lot of skimming gangs there but as far as the rest of the companies will not adjust their organizational scheme and will not invest in technology the exposure for this kind of fraud will remain. And I believe in your good will and professional journalism. So, I hope that you gone … publish my comment and you gone … improve your article taking in consideration more than local “experts’.
Thank you and best regards
Brian, Thanks for the great article! I was curious what advice you would give to someone that is planning to travel to Mexico and will be staying at one of those resorts. I’ll obviously try to avoid those ATMs and scan for bluetooth signals, but that isn’t foolproof. Would you advice pre-paid debit cards, or just taking cash, or some other method?
Thanks!
great story Brian! The comment by “David” is also great 🙂
There is surely more to come and I am REALLY curious how this Intacash story unfolds.
Already his introduction is quoteworthy:
“1. In Mexico, because of the cartels and out of law gangs the owners of companies prefer to be anonymous.”
bruhahahahaha
On a sidenote: I did stories about skimmers in Europe for german tv and still have all the material. The technical improvements compared to stuff from 2004 is minimal. Boards and antennas my have shrunk a bit but its basically the same stuff except the downloadable memory of data bit. Transmission was via bluetooth 10 years ago and some POS transmitted directly to a cellphone hidden nearby. Later there was a full GSM module incorporated which sent the data via SMS message internationally…
Rod,
I wasn’t in the industry ten years ago and I didn’t make any documentary for german television but as far as I understand from people smarter than me, the skimmers technique was evolving a lot in the last ten years. They didn’t steal the pin with a camera or an external device anymore: they get IN the pinpad! To understood better I will recommend you to read again the Brian articles and to watch close the pictures.
Regarding your “bruhahahaha”, I will not comment your professional journalist approach but again, I will recommend you to search on google articles about los zetas. And “anonymous” in my text means anonymous regarding public, not anonymous regarding institutions and authorities. They can’t be unknown regarding this. Because to own and operate such a company in Mexico (and all over the world), as far as I know, you need to have authorizations from a lot of institutions, including National Bank of Mexico. But yes, Donald Trump way of acting will never work there.
Jeff, I don’t know how much will help you but when we use that “decoy” technician, we ask for a device for a NCR 16 SS….and they can’t do it. Knowing also the NCR protocols regarding security, I may say that NCR ATMs are almost impossible to be penetrated.
I think David deserves an answer from you Brian
Incredible research.
Your articles give a hint to think about ATM environment: starting from SW development, installation, maintenance and to self-service future. Really valuable experience.
Greatest thanks for your job!