In the previous two stories, I documented the damage wrought by an organized crime gang in Mexico that has been systematically bribing ATM technicians to install Bluetooth skimming components that allow thieves to steal card and PIN data wirelessly. What follows is a look at a mysterious new ATM company in Mexico that sources say may be tied to the skimming activity.
One ATM company operating in the Cancun area whose machines were apparently free from these skimming devices is a relatively new entity called Intacash. This company’s ATMs positively blanketed many of the areas I visited, particularly in the heavy tourist and commercial areas of downtown Cancun and Playa Del Carmen. For example, in a single city block on Boulevard Kukulcan in Zona Hotelera — probably the busiest tourist spot in Cancun — I counted no fewer than ten Intacash ATMs, most of which were all less than a couple hundred yards from each another.

Intacash ATMs positively blanket the most busy area of downtown Cancun and in very tight proximity to one another.
The experts I spoke with said they were mystified by Intacash’s strategy of placing so many cash machines in the region. Even for areas like Zona Hotelera with plenty of continuous foot traffic, adding so many cash machines in such a small space produces diminishing returns.
Two different ATM experts familiar with rates charged to place ATMs in the area and who asked to remain anonymous said there is no way Intacash could afford the rent required to place so many ATMs in such close proximity on public property and still turn a monthly profit. No way, that is, unless the company had a different profit motive in mind.
Intacash is a relative newcomer to the ATM scene in Mexico, bringing its first ATMs online there a little more than a year ago. It’s not at all clear who runs or owns Intacash, and there is precious little public information available about this company.
Intacash.com, registered in early 2014, consists of just four Web pages. There is no contact information for the firm on its site, which to this day has exactly zero sites linking in to it. From its inception, the site’s registration records have been hidden behind WHOIS privacy protection services. Intacash hosts its sites along with more than 6,000 other sites on a shared server at GoDaddy.com (for security and other reasons, financial institutions and service providers more typically spring for their own, dedicated servers).
Despite the presence of nearly 70 Intacash ATMs in Cancun, Playa Del Carmen, Tulum and other tourist areas in the Yucatan Peninsula, this company seems to have gone out of its way not to be noticed online. What’s more, a review of the text on Intacash.com suggests that much of the Web content on the site has been copied verbatim from other sites that preceded Intacash’s existence on the Internet.
Multiple emails sent to the contact addresses and forms on Intacash’s Web site went unreturned. Intacash’s sponsor bank in Mexico – Multiva — also did not respond to messages seeking comment.
THE INTACASH CONNECTION
Why was I so keen to learn more about Intacash? My source in the ATM industry who tipped me off about the Bluetooth skimming activity showcased in the first two stories here said his technicians began receiving bribes to let strangers install skimming components inside their machines around the same time that Intacash came online in Mexico. By early this year, all of my source’s ATM technicians had reported being approached by one of two guys who were trying to buy access to ATMs. The employees who reported these incidents to my ATM industry source said the men had Eastern European accents.
Several of my source’s employees later identified the men who approached them after managing to locate their profile pages on Whatsapp, a popular mobile messaging service.
“My partner was at a meeting with the operating manager of [a major hotel] in Cancun, doing his sales pitch,” my source recalled in a recent interview. “And the fellow at the hotel told my guy that just the day before he’d been approached by another ATM company, and that the guys were Eastern European.”
My source said that, when pressed, the hotel manager acknowledged that the other company was indeed Intacash. My source said his business partner happened to have bookmarked on his smartphone the Whatsapp profiles of the men who’d tried to bribe his technicians, and that he opened the profiles one by one and showed them to the hotel manager.
“My partner asked, ‘Just out of curiosity was it one of these guys?'” my source said. “The hotel manager said why, yes it was.”
ANALYSIS
Intacash may in fact be totally above-board. But beyond the above-mentioned circumstantial oddities, there are other clues that would suggest something is not quite right at Intacash.
For example, in my wanderings around Cancun and elsewhere in the region, I used a low-balance debit card to check out multiple Intacash ATMs — each of which offers customers the option to withdraw Mexican Pesos or U.S. Dollars. Curiously, every time I used one of these machines to make small Peso withdrawals, I received a paper receipt. Each time I took out dollars, I got no receipt (this behavior was the same across multiple Intacash machines).
In about one-third of the cases, after entering my PIN, the transactions were canceled without explanation (no receipt was issued in those failed transactions either). When I returned home and began researching this, it turns out I was not the only one who noticed this pattern.
Even more curious, Intacash ATMs charge nearly twice as much as virtually any other ATM company in the region for withdrawing funds — often 10 percent to 15 percent of the value of the withdrawal. I would imagine that a large percentage of consumers who put their cards and PINs into an Intacash ATM would cancel the transaction and look for another machine after seeing that withdrawing $100 would cost them $15.
I began to wonder whether it was possible that Intacash was a company essentially set up to capture card and PIN data? Phony ATM companies are certainly not unheard of, even in the United States. Back in 1993, U.S. federal agents arrested two men in Connecticut suspected of stealing more than $100,000 by placing fake ATMs. In the Connecticut case, the fraudsters simply placed fake ATMs that were devoid of cash. That may sound like a clever scheme, but the lack of cash in those machines is what quickly tipped off investigators that something was fishy about the ATMs.
Well, hang on a moment, you say: Wouldn’t selling or otherwise exploiting ATM/debit cards all stolen from one ATM company’s machines quickly draw unwanted attention from the banks, Visa and MasterCard to that company? You bet: Anyone in charge of such a fraud operation would want to spread their card-cloning scam across as many ATMs as possible: The more ATMs and the more ATM companies involved, the harder it is to trace the source of the fraudulent transactions. And here we come full circle to the cash machines in and around Cancun that were compromised with internal Bluetooth skimmers.
In addition, the absence of receipts and the propensity for ATMs to randomly “cancel” transactions after users insert their cards and enter their PINs would make it easier for a large card cloning operation to hide much of their activity. For example, if the transaction is cancelled before it reaches the processing switch of the customer’s bank, there would be absolutely no record of the customer using the ATM, despite the card data and PIN being compromised
How much could a fake ATM operation with 70 ATMs pull in each month? Various ATM companies I spoke with in the process of reporting and writing this story said — depending on the location — a typical machine may need between 300-500 customers per month to become profitable.
If we take the low end of that, and assume that some customers (let’s say 30 percent for rounding purposes) will be repeat customers using the same card and PIN, that’s conservatively 200 cards per month per machine. Even if the average checking account tied to each ATM card had just $100 in it, that’s $20,000 per machine per month, or — again, very conservatively — about $1.5 million across all 70 machines per month.
THE KEY ROLE OF ATM TECHNICIANS
Several readers have asked why experts are so certain that ATM company installers — not random crooks — had to have been responsible for installing the Bluetooth card and PIN pad skimmers in the compromised devices I found in Mexico. The explanation has to do with the reality that modern ATMs are designed to protect the security and privacy of the user’s PIN once it is entered into the system, and more importantly to protect the integrity of the PIN pad itself.
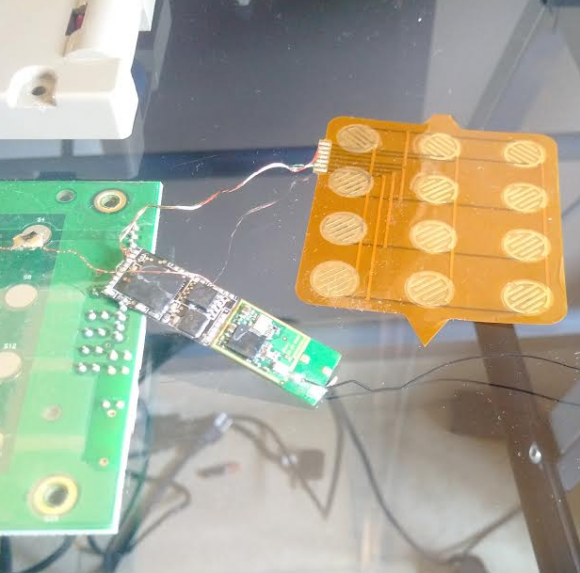
One of the Bluetooth PIN pads pulled from a compromised ATM in Mexico. The two components on the left are legitimate parts of the machine. The fake PIN pad made to be slipped under the legit PIN pad on the machine is the orange bit, top right. The Bluetooth and data storage chips are in the middle. The antenna for the Bluetooth board can be seen trailing off the right side of the photo.
If a random thief were to break into an ATM and attach electronic devices capable of intercepting PIN codes entered by customers, the ATM would simply cease to function properly after that. When ATM makers or banks wish to update software or hardware on their machines, they must subsequently input a special cryptographic key. That key — known as the “terminal master key,” is good for that machine and that machine only — and it comes directly from the manufacturer or the bank.
Some banks and ATM companies go a step further, requiring all such changes to be approved by two authorized personnel. This dual-authentication approach — the use of two keys, each assigned to different personnel who must approve physical and software changes to the ATM — is designed to short-circuit any attempts by rogue ATM installers to do what’s apparently been done in many Mexican ATMs. And it is likely that the victim ATMs documented in this series were not following this best practice.
Also, some readers have asked whether there was anything in particular about Mexico that made ATMs there more likely to be victimized by sophisticated ATM fraudsters who bribe their way into cash machines. I think the answer is yes and no. For one thing, the risks of doing this in the United States are far higher. It seems likely that anyone convicted of hacking cashing machines this way in the United States would be facing federal fraud charges and serious jail time here if convicted.
In Mexico, it seems unlikely such a person would ever even be prosecuted, let alone jailed for any length of time. Security experts I spoke with in Mexico said it is exceedingly easy to buy one’s way out of prosecution or jail in Mexico if one has the right amount of cash, and certainly an enterprise in charge of a skimming business or a fake ATM empire would indeed have plenty of that.
But in practice, this scheme could happen anywhere in the United States, and I would fully expect it to migrate north of the border soon (if it hasn’t already). There are no doubt plenty of ATMs that allow the swapping in of hardware without requiring two people to sign off on the change, and people here are obviously susceptible to bribes. It’s also worth noting that technicians here and abroad alike can be coerced into cooperating with thieves via non-financial means, such as extortion or threats to their personal safety and/or that of their families.
Finally, many readers have asked if any of the skimmed ATMs I found in Mexico were bank-owned and operated ATMs, or machines on the premises of bank properties. None of them were: All were free-standing cash machines owned and operated by private companies.
If you haven’t already seen them, please check out the first two stories in this series:





Brian
this is freaking interesting and scary for someone who lives in Mexico… few points
-could it be that you’re actually identificed two entirely different issues here?
the Bluetooth scanning has all the markings of an inside job within Cardtronics, or at least several technitians involved… (from the list that you published yesterday, most of them were from Cardtronics, few from Multiva – a bank owned by a powerful media/health/insurance company onwned by Olegario Vazquez Raña, and CiBanco -a smallish and newish bank in Mexico, their hackings could be the payoff to a technitian(s) for allowing the hacking of Cardtronics.
On the other hand, the Intacash thing smells a lot to me a lot like money laundering…probably from eastern european, but more likely by druglords. think about it… by not providing a receipt the company can claim that it gave $100 USD instead of just only the $20 it delivered…
-the mexican page for intacash is http://www.intacash.mx but a whois search also reveals that the registar is godaddy.com
-unfortunately yes… in for this kind of people is a lot easier to do business in Mexico than in the US as the chance of prosecution are extremely close to nil.
They will continue the ATM schemes until they are physically stopped. Too much money is at stake.
Wow! Just Wow!
This is the most amazing story I have read yet. You da man!
Is it common for a bank in the U.S. not to give a receipt, when you withdraw cash at a teller window?
If you visit a bank in person, you will almost always get a receipt, although some banks may ask if you want one.
US ATMs generally ask if you want a receipt or not. I always say “yes”, and I’ve always gotten one.
It is worth noting, however, that I only use ATMs that are built-in to banks. I don’t trust any free-standing machine, because I’ve read too many articles about fraudulent machines operated by criminal organizations.
I only deal with bank ATMs as I don’t have confidence in those free standing ATM. They always print receipts. RBC does offer a “quick” cash option where you have a pre-set amount that will be spit out and no receipt generated if you configure it so. Handy if you just need cash quickly.
At one bank branch location, when I deposit a check, I always get a receipt. But when I withdraw cash inside from a teller inside, I have to ask for a receipt, every time. The bank revolves tellers around the various branches so I don’t see the same tellers the couple of times I go inside each month.
“The experts I spoke with said they were mystified by Intacash’s strategy of placing so many cash machines in the region.”
Number of ATM’s on small radius could be explained with intacash terms for partnership found on this page http://intacash.com/partners.html , “…This is because the program is intended for people who want to invest in at least 20 locations.”
Apparently anyone with enough funds can rent those machines. Whoever wanted to use ATM at their location, probably had to rent more ATM stations than necessarry, or more businesses invested together to get one of ATM machines close to their store, etc… This is something that just people from Intacash can answer, everything else is speculation.
One more example, why we need BtCoin.
With the credit (or debit) card, I give the merchant or ATM operator the information to draw from my account.
With BitCoin, I send the amount I determine to the merchant or ATM operator. So the worst that could happen is that the ATM doesn’t dispense the money I just ordered in this very transaction.
Nothing wrong has ever happened with BitCoin. No one has ever lost their BitCoin account, wallet….no BitCoin exchange has ever been compromised. Not the panacea you make it out to be.
I don’t think that you mean Bitcoin as a solution. Blockchain technology…maybe?
BitCoin is not a solution. The block chain is already too big and validation is too slow for most consumers to tolerate at businesses they go to.
Businesses cannot pay their employees and taxes with BitCoin, so they have little incentive other than showing off to do any transactions with BitCoin.
Great series!
It makes me wonder if that even if cash machines required a 2 or even 3 factor authentication for internal access (no real reason why a central center wouldnt have to authorise the upgrades as well as the 2 onsite and or monitor the process via a webcam in the chassis) if the crooks wont just migrate to easier to access machines, such as super market self checkouts, or vending machines.
Certainly in europe with the use of Chip and Pin; its diversified the amount of devices in which you will find a card reader, often in unattended locations, which use common master keys to gain access to the internals. Worse still some of the most popular of card readers (due to its very secure looking keypad design) you find in unattended machines interface to the control software with an unencrypted RS232 interface which is super easy to sniff with a protocol decoder or arduino, with the encryption happening in software on the host computer which runs the rest of the machine. When i last dealt with that vendor and raised concerns there response was that the MCU on the keypad wasn’t powerful enough to encrypt at input and that a new model was 3 to 4 years off at least, that was 18 months ago…
Concerned former employee at a manufacturer of self service machines.
Since the ATMs network with US and other international banks and victims of fraud are mostly tourists, I would expect this scam to end sometime soon. Interpol enjoys going after crime rings, the US DOJ enjoys investigating financial crimes, and Mexico will be motivated to investigate something affecting their tourism industry.
This is a tough nut to crack. Even if the US banks find out that this specific geolocation ATM’s are garbage and refuse to dispense cash, the damage is already done. People have slipped their cards into the compromised units, so its only a matter of time before they are cloned and used.
When I travel I use cash and/or the multiple Gift card approach.
I do have a separate account I could use for travel, but that honestly has never been used since the rise in ATM skimmers. The reason for not using it anymore is quite simple. I don’t want my accounts drained as I am out on a vacation – being overly distracted and not performing my homebound daily rituals.
Come to think of it, I am in dire need of a vacation. You can betcha Mexico is not going to be on the list for quite some time.
Isla Mujeres is just across bat from Cancan. Most of us who were hacked can trace it back to ATM machine at CI Banco. So I thought it very interesting that bank was involved with Multiva. There are only maybe 12 ATM machines on Isla, so not hard to identify where card was skimmed. This is an ATM machine in a bank. Another bank, Banamex, has had skimming activity but not to extent the ATM at CI Banco is the culprit. Many ex-pats use it because it has such a low fee, around 18 pesos. In the local big supermarket there are 4 ATM machines, all bank affiliated. People have reported being skimmed at those as well.
So. Am confused when Brian said none of the machines with skimming capabilities were bank- affiliated. On Isla Mujeres, they all were.
very enlightning … makes me look at ATMs (and their place) in a completely new way …
But more generally – does this ‘Intacash’ model work in Europe too – or is it limited to those 3rd-world places without EMV-chips ?
very enlightning … – I’m starting to look at ATMs in a totally new way 🙂
I read this early this morning, so I apologize in advance if my question can be answered by re-reading Brian’s piece. In the beginning of the second paragraph it reads “…whose machines were apparently free from these skimming devices…” If the Intacash devices were all free from the Bluetooth skimming devices, then how are they fitting into this ATM fraud scheme? I apparently need some coffee before reading anything in the morning.
Intacash isn’t skimming because the crime organization owns the ATMs and you already provided your information to them when you put your card. The compromised ATMs aren’t in on the scam, so they must be skimmed.
I initially thought that as well. However, when you think about it, why would a company whose sole purpose is to clone cards need a wireless anything?
I would suspect that they could either simply program the software within the ATM to do the cloning using the existing hardware, or use devices where the technicians can manually extract the info during service calls.
Having a technician extract the info is risky because it adds another link in the chain of information. Take for example the employee who was caught taking the bribe. If he were part of the chain, he would be interrogated and probably give up any and all information about his nefarious employer. By doing the scheme via Bluetooth, its a one time bribe where the employee has minimum exposure to the inner workings of the scheme.
The ATM’s from the otherc ompanies use different hardware/software. And also as explained, you cannot just reprogram the hardware/sofwtare. It is often secured.
Using the bluetooth transmitter is a ‘smart’ move.
I’m thinking that the InstaCash machines may be receiving the bluetooth signals from compromised nearby ATMs.
WOW – that would be smart.
The intacash ATM reads out via BT the ‘last’ transaction of the ‘infected’ machine – and simulates/mimmicks another withdrawal via intacash…
hmmm … OR: if the BT-hardware allows it – it could make the withdrawal (from time to time) FAIL on the ‘infected’ machine – and force the customer to use intacash.
…yeah – zombie ATMs remote-controlled via another ATM.
thanks for asking this – i thought the same and figured “not” was just missing but the commenters following your comment explained it further. so thanks so much for asking!
Wow. I am speechless..
I am guessing that we haven’t heard the last of this subject.
Can’t wait to read “Nación ATM” when it comes out.
This is all very interesting, and as the author says, intriguing. So the drug lords are needing their monies worldwide? I wonder if they are consolidating forces. Or better yet. Now the payments to the locals is being erected. Quasi legal banking system, that is now able to move money anywhere without the 10 thousand limit imposed in America? Right to your lcl ATM! The possibilities are staggering.
“an organized crime gang in Mexico that has been systematically bribing ATM technicians to install Bluetooth skimming components”
Being Mexico, I suspect their request might be something more like “take the bribe and do this or we will harm you and your family.” Thus, the apparently widespread problem.
Perhaps the Mexican government has found a way to finance Trump’s really big, big wall – off the backs of tourists’ banks.
This is a pretty smart plan actually, especially if they want to run what appears to be a legit ATM business. Start a transaction, deter with high fees or cancel transactions before they go through, then use the cards at a competitor’s ATM after you’ve already had someone install a skimmer-like device.
Then (1) you have your money in-hand at a much better rate than what you could probably sell it to a carder forum for, (2) banks will start to aggregate date and connect the breach to the competitor’s ATMs, and (3) you can selectively choose to steal cards from people who live out of the country, without jurisdiction or the will to travel back-and-forth if they ever did decide to try to prosecute. Win-win-win.
And if this only affects some transactions at your machines (e.g. non-pesos transactions, and only some USD transactions), there will be plenty of people to say they used it and they were fine.
Fortunately, these guys had next-to-zero op-sec and/or just didn’t think it mattered. Awesome article Brian.
Great job, Brian. As one whose family will be in Quintana Roo over Thanksgiving, I have referred this series to the organization through which we have booked our vacation. They were very interested and referred me to one of their blogs, where I found this:
“Mexico pesos is not monopoly money! Mexico’s currency is the Peso, usually denoted by the MXP sign. Prices quoted in US dollars will normally be written ‘US$5’ or ‘5 USD’. And like the US Mexico has centavos (cents). The smallest coin is the 10 centavo coin and it’s pretty useless for making a purchase because 100 centavos = 1 peso and it take about 13 pesos to make one US dollar (at this time). Coins also come in denominations of 20 and 50 centavos and one, two, five, 10, 20 and 100 pesos. There are notes of 20, 50, 100, 200, 500 and 1000 pesos.
There are a lot of practical tips out there about credit card exchange rates, etc. but our local take is this… Cash is great, and some places like restaurants will take USD but you’ll get a lower exchange rate, sometimes lower than even the “casa de cambios”. Many larger grocery stores and membership clubs accept credit cards and give an excellent exchange rate. There are also change houses “casa de cambios” where you can exchange your currency for pesos. The rate may vary daily. The rate is not the international market rate just a bit below.
Using your credit cards: Credit cards such as Visa and Mastercard are more widely accepted at restaurants, eco parks and bigger gifts shops, but don’t be caught short at a little mom & pop business when they say “Solo efectivo…. cash only”. Some businesses may charge you a “convenience fee” for using your credit card instead of paying in cash.
ATM Machines in the Riviera Maya, beware of fees & exchange rates. ATMs (caja permanente or cajero automático) are an easy source of cash, when they are working. Be warned, in some of the smaller towns you may encounter that the machine has run out of money. The thing you will find when it comes to the ATM’s is that they will charge you a fee. The fees vary depending on the provider. Some very visible ATM’s on 5th Avenue in Playa del Carmen and other areas have sizable fees associated with them. Others like those for CiBanco have excellent exchange rate and low service fees when you withdraw from your checking account at home and receive pesos. Always request a receipt so you can balance out your check book when you get home. Or use the information to track everything on your phone or tablet with your bank’s app.
– See more at: https://www.locogringo.com/sthash.Wqcl1NYr.dpuf#sthash.Wqcl1NYr.4YqKjOUK.dpuf.”
They also referred me to Wells Fargo which apparently offers a travel card, which can be used to limit losses if compromised. One more tip they offered, to let your card company know you would be traveling.
Is anyone aware of similar goings-on on the Pacific side such as Puerto Vallarta?
Well….
http://www.intacash.mx/
Has ties/partnership to Top Live Servicios
http://www.toplifemexico.com/index.html
They are in Cancun too…..
Intacash expand the operations in Mexic building a partnership with Top Life Servicios, a mexican company. We are specialized in the placement and operation of top quality ATMs and thru this partnership we are prepare to provide to all our clients a reliable, secure, and easy way to withdraw cash from their credit or debit cards. We instal just state of art equipment with the latest security and safety features and we know that if we are not taking care of our clients, someone else will.
Something odd here…
Top Life Servicios is a unit of Banco Multiva, Intacash’s sponsor bank.
Ahhh…..thank you for the clarification……
haved lived here cancun and chetumal 25 years, been aware of these fine points you bring out. only solution is check your accounts/balance on line daily. even days you do not use atms. and change your pin regularly like once a week or once a month . helps a lot. can do it online or at the machine if some cases. the new atms may be a way for cartels to launder there usd cash and or pesos. always use banks machines where possible. less risk but still risks. always cover your hand when entering your pin. even if there is a cover/shield on the atm pin board. thanks for these updates.
great idea to change pin code periodically!
Is it possible that the bluetooth-enabled ATMs were only there for the hackers to replay the cards skimmed from the no-dollar ATMs?
…well – doesn’t make sense to me:
Let’s say you withdraw $100 + $6-fees from intacash – without a receipt. then the intacash machine ‘withdraws’ via remote-BT 100 from the ‘other’ machine… ? and then ? — you can’t teleport bank-notes yet….
so – unless the ‘infected’ ATM has a money-wiring option – it makes little sense to me …
Brian –
Thanks for your multi-part investigation into this “little problem.” I was directed to your Blog from a neighborhood website group that I belong to. We had a problem with an Internal Skimmer being planted into a Gas Pump at a local 7/11. Within days of using that pump – we started noticing bogus purchases from other far-flung gas stations in the SoCal area. Our local cops did a sweep of some gas stations and actually documented the skimmers and booked them as evidence of an investigation. I don’t know details about the type of skimmer – whether BluTooth or hard-wired.
The story is here:
http://www.vcstar.com/news/local-news/conejo-valley/operation-targets-credit-card-skimmers-in-ventura-county_54956292
Because of your story and efforts – I will be using my phone with the a BT scanner.
Brian – what App did you end up using in Mexico? Was it adequate for you? Could you get more detailed info – like Sig strength – so you could maybe figure out which of many devices had the BT xmitter?
Thanks for your “vacation” and work. Being in Mexico, or any foreign country, with graft and police corruption – you obviously have to be very careful not to piss off either the skimmer dudes nor the cop dudes that protect them!
Be careful out there –
G
Geo,
I didn’t use an app at all. All smartphones have an option/page under “settings” that lets you scan for nearby bluetooth signals. I just used the one that came with the Android OS on my crappy little Huawei smartphone.
If you’re really looking for an Android app, Bluetooth 4.0 Scanner from a developer named John Abraham and works quite well on my Android tablet. You can find it in the Google Play store. It will scan and show signal strength and also keeps records of what it has found and when along with latitude longitude coordinates.
I’ve seen an ATM kiosk dropped off and plugged in, in under the time it took me to gas up. Check along the 101 Frwy south of the 23 all the way to the 134/210 -the ATMs up against the outside wall of gas stations, especially where the “station” is just a booth with a cashier.
BTW, I am assuming you’re near Los Angeles because of the Ventura county citation. I just noticed the time stamps are all east coast time. (So any of us could be anywhere!!)
Hi Brian
I think with all this hot stuff you made many new “friends”.
I suggest you to take some MMA classes.
(BJJ, kickboxing, karate).
Thank you for the info.
Dear Brian:
We would like to talk with you in order to run your story on Newsweek en Español. How can we contact you?
The new skimmer-proof “chip” EMV credit cards are rolling out in the US right now, which bears on the story a couple ways…
1. With EMV coming online, it’s predicted that we will see an increase in other fraud types: card-not-present credit card fraud and ATM skimming. Score one for the predictions! Sadly that means this ATM skimming story may just be the first of many.
2. There’s actually an EMV standard for ATM cards too, which would negate this sort of ATM skimming, but it’s not getting pushed in the US. I assume the US will get them eventually, with big fraud cases accelerating things.
There is a liability shift for ATM machines, but that’s not until next year or the year after (MC is next year, Visa the year after). But I suspect that many of the machines will be upgraded next year as people could use either one in a given ATM.
I expect that many of the old crappy XP-based ATM machines will end up going away as it would be easier to start from scratch rather than try and retrofit something into those ancient machines.
Good point. Many people don’t realise that EMV does indeed prevent these kinds of fraude. After all, the ATM is used to get the user’s 4-digit code plus a copy of the magnetic strip.
In Europe many banks in various countries have simply blocked any ATM transaction using the magnetic strip data and/or all of them comming out of Europe. They can do this, as inside Europe also ATM’s use EMV. (Of course you as a customer can lift this block when going on a trip.)
Hence the 4-goto code is useless as the data coppied from the magnetic strip cannot be used, and copping the EMV data is not possible. There are some scams using modified ATM’s, but these are even harder to pull of then what the crooks in this artcle serries did as it requires reprogramming the actual ATM software itself.
So I expect a short burst of ATM fraude until banks replace teh current magnetic-strip based ATM’s. And they won’t do that untill liability shoft kicks in. Except perhaps for bank-owned ATM’s as they have an incentive themselves. Yet another reason to use bank-owned ATM’s as I expect those to shift to using EMV sooner.
A thought comes to mind…
What if the cancelled transactions were cancelled because the ATM either recognized the account did not contain much money (and thus not as interesting or potentially be a honey-pot card intentionally to be tracked) or that it attempted to do a larger authorization than was available on the card and the ATM had no choice but to cancel the transaction lest the customer may become aware of the scheme.
Thought of that this morning. Had started writing a comment, but cancelled it when I realized that has a significant gotcha: Contacting the user’s home bank IN ANY WAY leaves a trace that identifies the ATM into which the user’s card was inserted. Best not to do anything but skim the card data and then reject the card.
The user’s bank has to keep track of ALL transactions, after all, since the user’s card data can be skimmed just as easily during a balance check as during a cash withdrawal. Since ANY completed transaction could enable the user’s bank to trace the compromised ATM, best not to do ANY transactions at all from the compromised ATM with cards that will eventually be cloned and used elsewhere. That way, the user’s bank will NEVER be able to locate the ATM where the user’s card was originally skimmed.
Wow … guess I’ll keep using bank attached ATM’s. This type of corruption is frightening in its scope!
Hello!?! Being shocked that this type of crime is rampant in Mexico is like be shocked that Iowa has corn or that a beach has sand. This is Mexico folks, home of the narco wars and the Iguala mass kidnapping. Rick Steves has some good advice for tourists on the subject of financial security. It is called a money belt. Yes, it is old school but there is no service charge. Comments welcomed.