My PayPal account was hacked on Christmas Eve. The perpetrator tried to further stir up trouble by sending my PayPal funds to a hacker gang tied to the jihadist militant group ISIS. Although the intruder failed to siphon any funds, the successful takeover of the account speaks volumes about why most organizations — including many financial institutions — remain woefully behind the times in authenticating their customers and staying ahead of identity thieves.

Junaid Hussain’s Twitter profile photo.
On Christmas Eve morning, I received an email from PayPal stating that an email address had been added to my account. I immediately logged into my account from a pristine computer, changed the password, switched my email address back to to the primary contact address, and deleted the rogue email account.
I then called PayPal and asked how the perpetrator had gotten in, and was there anything else they could do to prevent this from happening again? The customer service person at PayPal said the attacker had simply logged in with my username and password, and that I had done everything I could in response to the attack. The representative assured me they would monitor the account for suspicious activity, and that I should rest easy.
Twenty minutes later I was outside exercising in the unseasonably warm weather when I stopped briefly to check email again: Sure enough, the very same rogue email address had been added back to my account. But by the time I got back home to a computer, my email address had been removed and my password had been changed. So much for PayPal’s supposed “monitoring;” the company couldn’t even spot the same fraudulent email address when it was added a second time.
PayPal locked the account shortly after the assailant allegedly tried to send my money to the email account of the late Junaid Hussain, a 17-year-old member of the hacktivist group Team Poison. Hussain — who used the nickname “TriCk” and is believed to have been a prominent ISIS propagandist online — was reportedly killed in a U.S.-led drone strike earlier this year in Raqqa, Syria. No doubt, the attempted transfer was a bid to further complicate matters for me by associating my account with known terrorists.
In my second call to PayPal, I insisted on speaking with a supervisor. That person was able to tell me that, as I suspected, my (very long and complex) password was never really compromised. The attacker had merely called in to PayPal’s customer support, pretended to be me and was able to reset my password by providing nothing more than the last four digits of my Social Security number and the last four numbers of an old credit card account.
Let’s leave aside for a moment the reality that all of this static information about Brian Krebs has been posted online by various miscreants over the years (and probably remains online): Any company that authenticates customers with nothing more than static identifiers — address, SSN, DOB, phone number, credit card number, etc. — is vulnerable to these takeover attempts.
This almost certainly includes all of the companies that supply utilities to your residence, your bank or credit union, and a host of other companies. They’re vulnerable because those static identifiers about you are no longer secret and are available for sale in the underground.
I asked the PayPal supervisor why the company couldn’t simply verify my identity by sending a text message to my phone, or a special signal to a PayPal mobile app? After all, PayPal has had the same mobile number of mine on file for years (the attacker also deleted that number from my profile as well). The supervisor explained that the company didn’t have any mobile authentication technologies, and that in order to regain access to the funds in my account I had to send the company a photocopied or scanned copy of my driver’s license.
Nevermind that it was PayPal’s lack of any modern authentication methods that led to this mess. Also, let’s forget for the moment that there are a half-dozen services online that let customers create fake but realistic looking scans of all types of documents, including utility bills, passports, driver’s licenses, bank statements, etc. This is the ultimate and most sophisticated customer authentication system that PayPal has: Send us a copy of your driver’s license. Continue reading




 Hyatt’s
Hyatt’s  New authentication methods now offered by Yahoo! and to a beta group of Google users let customers log in just by supplying their email address, and then responding to a notification sent to their mobile device.
New authentication methods now offered by Yahoo! and to a beta group of Google users let customers log in just by supplying their email address, and then responding to a notification sent to their mobile device.
 The FTC sued Oracle over years of failing to remove older, more vulnerable versions of Java SE when consumers updated their systems to the newest Java software. Java is installed on more than 850 million computers, but only recently (in Aug. 2014) did the company change its updater software to reliably remove older versions of Java during the installation process.
The FTC sued Oracle over years of failing to remove older, more vulnerable versions of Java SE when consumers updated their systems to the newest Java software. Java is installed on more than 850 million computers, but only recently (in Aug. 2014) did the company change its updater software to reliably remove older versions of Java during the installation process. Mountain View, Calif. based Gyft lets customers buy and use gift cards entirely from their mobile devices. Acting on a tip from a trusted source in the cybercrime underground who reported that a cache of account data on Gyft customers was on offer for the right bidder, KrebsOnSecurity contacted Gyft to share intelligence and to request comment.
Mountain View, Calif. based Gyft lets customers buy and use gift cards entirely from their mobile devices. Acting on a tip from a trusted source in the cybercrime underground who reported that a cache of account data on Gyft customers was on offer for the right bidder, KrebsOnSecurity contacted Gyft to share intelligence and to request comment.

 IT helpdesk guy by day and security researcher by night, 31-year-old Chris Vickery said he unearthed the 21 gb trove of MacKeeper user data after spending a few bored moments searching for database servers that require no authentication and are open to external connections.
IT helpdesk guy by day and security researcher by night, 31-year-old Chris Vickery said he unearthed the 21 gb trove of MacKeeper user data after spending a few bored moments searching for database servers that require no authentication and are open to external connections. The good news is that the states and Uncle Sam have got a whole new bag of technological tricks up their sleeves this coming tax season. The bad news is ID thieves are already testing those defenses, and will be working against a financially strapped federal agency that’s been forced to cede much of its ability to investigate and prosecute such crimes.
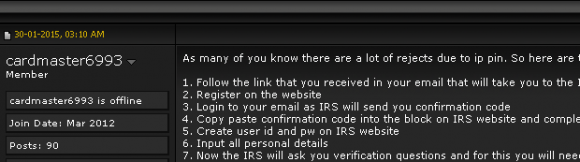
The good news is that the states and Uncle Sam have got a whole new bag of technological tricks up their sleeves this coming tax season. The bad news is ID thieves are already testing those defenses, and will be working against a financially strapped federal agency that’s been forced to cede much of its ability to investigate and prosecute such crimes.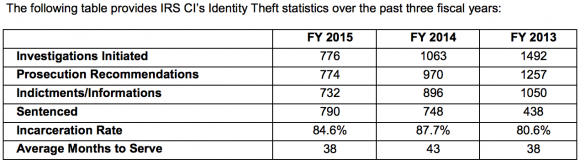
 This type of scam mainly impacts brick-and-mortar retailers that issue gift cards when consumers return merchandise at a store without presenting a receipt. Last week I heard from KrebsOnSecurity reader Lisa who recently went online to purchase a bunch of steeply discounted gift cards issued by pet supply chain Petco.
This type of scam mainly impacts brick-and-mortar retailers that issue gift cards when consumers return merchandise at a store without presenting a receipt. Last week I heard from KrebsOnSecurity reader Lisa who recently went online to purchase a bunch of steeply discounted gift cards issued by pet supply chain Petco.