On March 8, 2024, KrebsOnSecurity published a deep dive on the consumer data broker Radaris, showing how the original owners are two men in Massachusetts who operated multiple Russian language dating services and affiliate programs, in addition to a dizzying array of people-search websites. The subjects of that piece are threatening to sue KrebsOnSecurity for defamation unless the story is retracted. Meanwhile, their attorney has admitted that the person Radaris named as the CEO from its inception is a fabricated identity.
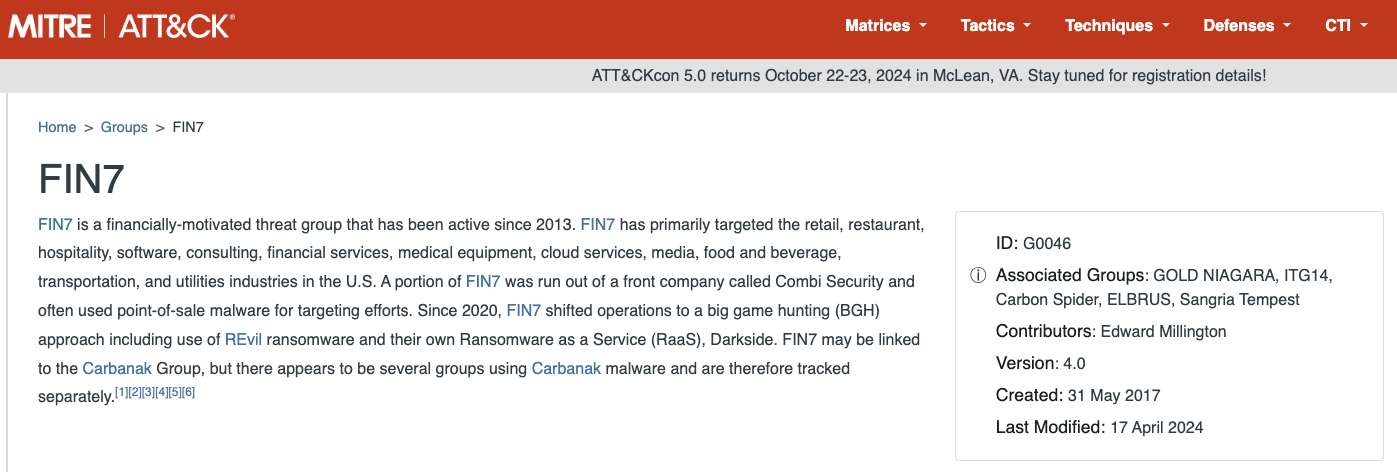
Radaris is just one cog in a sprawling network of people-search properties online that sell highly detailed background reports on U.S. consumers and businesses. Those reports typically include the subject’s current and previous addresses, partial Social Security numbers, any known licenses, email addresses and phone numbers, as well as the same information for any of their immediate relatives.
Radaris has a less-than-stellar reputation when it comes to responding to consumers seeking to have their reports removed from its various people-search services. That poor reputation, combined with indications that the true founders of Radaris have gone to extraordinary lengths to conceal their stewardship of the company, was what prompted KrebsOnSecurity to investigate the origins of Radaris in the first place.
On April 18, KrebsOnSecurity received a certified letter (PDF) from Valentin “Val” Gurvits, an attorney with the Boston Law Group, stating that KrebsOnSecurity would face a withering defamation lawsuit unless the Radaris story was immediately retracted and an apology issued to the two brothers named in the story as co-founders.
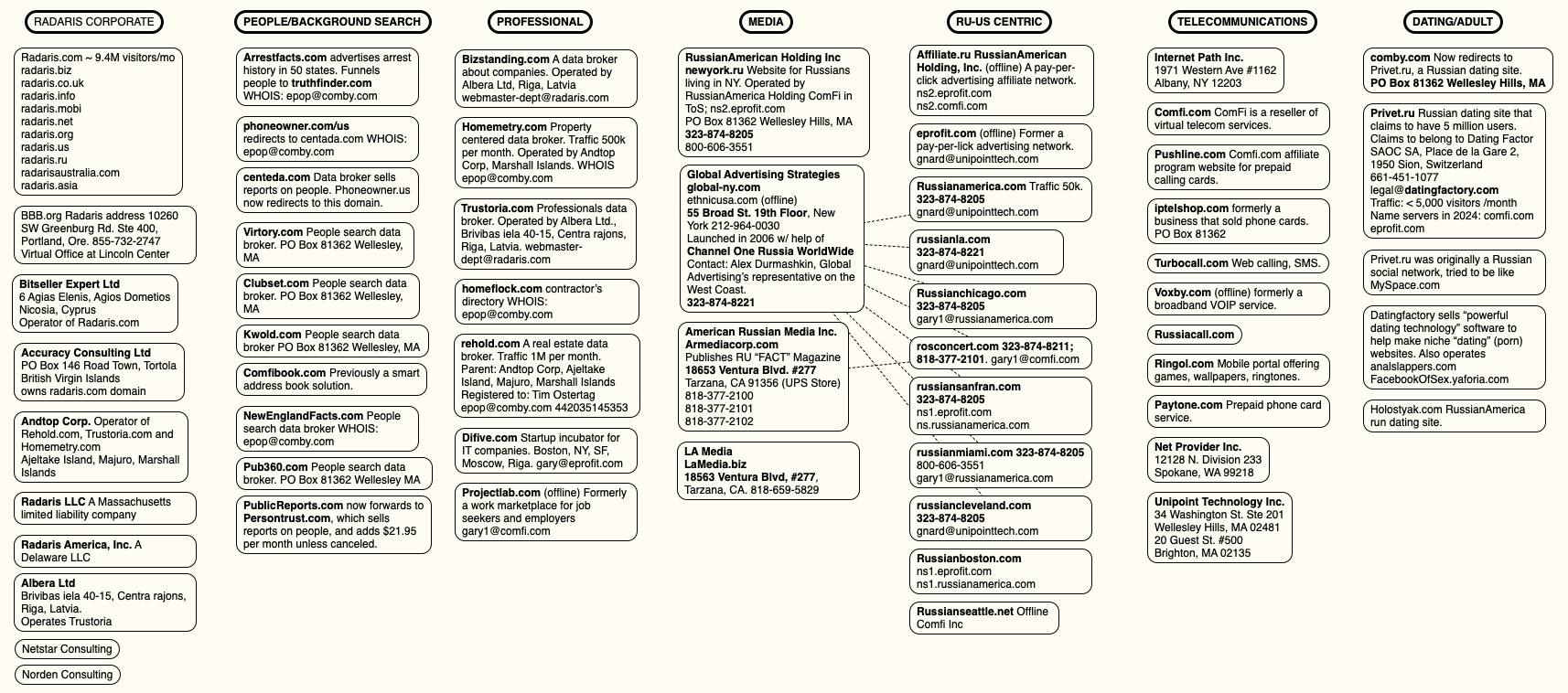
That March story worked backwards from the email address used to register radaris.com, and charted an impressive array of data broker companies created over the past 15 years by Massachusetts residents Dmitry and Igor Lubarsky (also sometimes spelled Lybarsky or Lubarski). Dmitry goes by “Dan,” and Igor uses the name “Gary.”
Those businesses included numerous websites marketed to Russian-speaking people who are new to the United States, such as russianamerica.com, newyork.ru, russiancleveland.com, russianla.com, russianmiami.com, etc. Other domains connected to the Lubarskys included Russian-language dating and adult websites, as well as affiliate programs for their international calling card businesses.
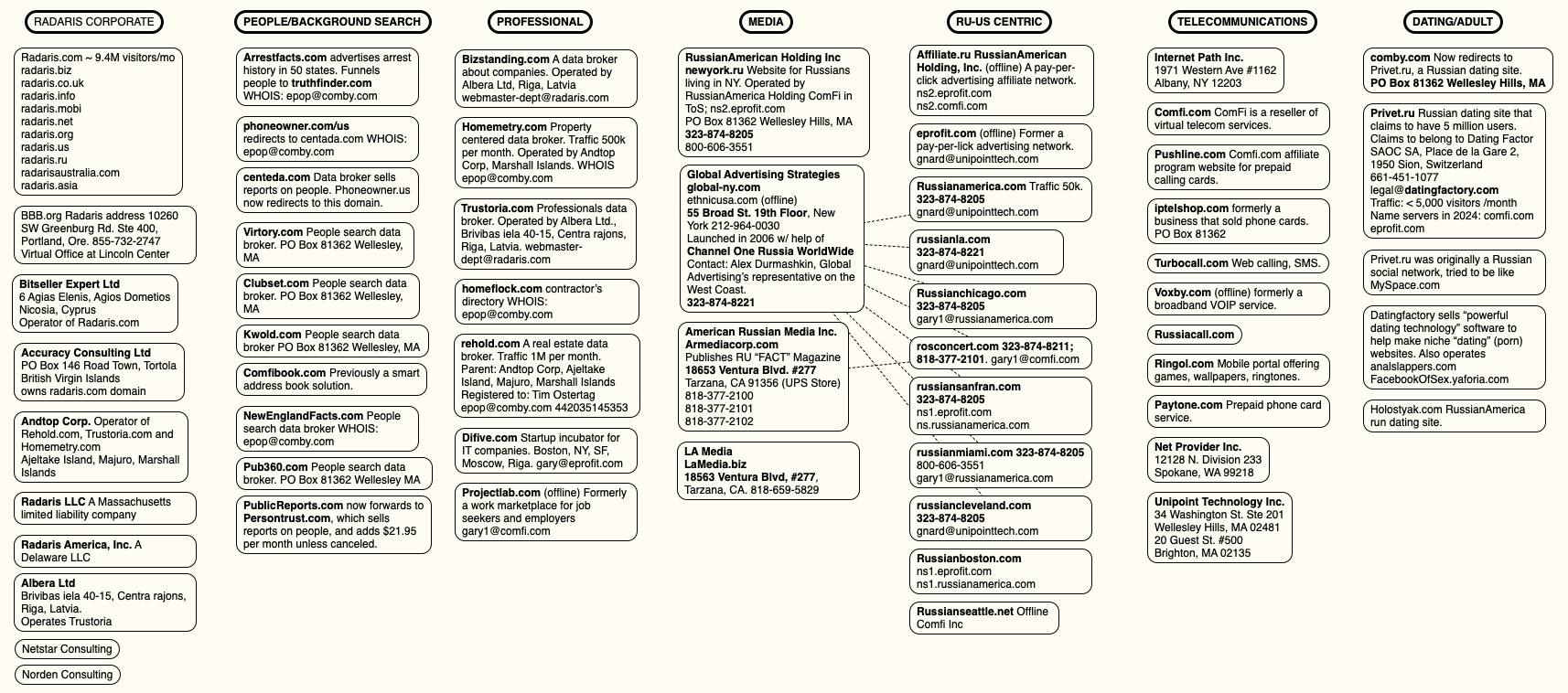
A mind map of various entities apparently tied to Radaris and the company’s co-founders. Click to enlarge.
The story on Radaris noted that the Lubarsky brothers registered most of their businesses using a made-up name — “Gary Norden,” sometimes called Gary Nord or Gary Nard.
Mr. Gurvits’ letter stated emphatically that my reporting was lazy, mean-spirited, and obviously intended to smear the reputation of his clients. By way of example, Mr. Gurvits said the Lubarskys were actually Ukrainian, and that the story painted his clients in a negative light by insinuating that they were somehow associated with Radaris and with vaguely nefarious elements in Russia.
But more to the point, Mr. Gurvits said, neither of his clients were Gary Norden, and neither had ever held any leadership positions at Radaris, nor were they financial beneficiaries of the company in any way.
“Neither of my clients is a founder of Radaris, and neither of my clients is the CEOs of Radaris,” Gurvits wrote. “Additionally, presently and going back at least the past 10 years, neither of my clients are (or were) officers or employees of Radaris. Indeed, neither of them even owns (or ever owned) any equity in Radaris. In intentional disregard of these facts, the Article implies that my clients are personally responsible for Radaris’ actions. Therefore, you intentionally caused all negative allegations in the Article made with respect to Radaris to be imputed against my clients personally.”
Dan Lubarsky’s Facebook page, just prior to the March 8 story about Radaris, said he was from Moscow.
We took Mr. Gurvits’ word on the ethnicity of his clients, and adjusted the story to remove a single mention that they were Russian. We did so even though Dan Lubarsky’s own Facebook page said (until recently) that he was from Moscow, Russia.
KrebsOnSecurity asked Mr. Gurvits to explain precisely which other details in the story were incorrect, and replied that we would be happy to update the story with a correction if they could demonstrate any errors of fact or omission.
We also requested specifics about several aspects of the story, such as the identity of the current Radaris CEO — listed on the Radaris website as “Victor K.” Mr. Gurvits replied that Radaris is and always has been based in Ukraine, and that the company’s true founder “Eugene L” is based there.
While Radaris has claimed to have offices in Massachusetts, Cyprus and Latvia, its website has never mentioned Ukraine. Mr. Gurvits has not responded to requests for more information about the identities of “Eugene L” or “Victor K.”
Gurvits said he had no intention of doing anyone’s reporting for them, and that the Lubarskys were going to sue KrebsOnSecurity for defamation unless the story was retracted in full. KrebsOnSecurity replied that journalists often face challenges to things that they report, but it is more than rare for one who makes a challenge to take umbrage at being asked for supporting information.
On June 13, Mr. Gurvits sent another letter (PDF) that continued to claim KrebsOnSecurity was defaming his clients, only this time Gurvits said his clients would be satisfied if KrebsOnSecurity just removed their names from the story.
“Ultimately, my clients don’t care what you say about any of the websites or corporate entities in your Article, as long as you completely remove my clients’ names from the Article and cooperate with my clients to have copies of the Article where my clients’ names appear removed from the Internet,” Mr. Gurvits wrote.
MEET THE FAKE RADARIS CEO
The June 13 letter explained that the name Gary Norden was a pseudonym invented by the Radaris marketing division, but that neither of the Lubarsky brothers were Norden.
This was a startling admission, given that Radaris has quoted the fictitious Gary Norden in press releases published and paid for by Radaris, and in news media stories where the company is explicitly seeking money from investors. In other words, Radaris has been misrepresenting itself to investors from the beginning. Here’s a press release from Radaris that was published on PR Newswire in April 2011:

A press release published by Radaris in 2011 names the CEO of Radaris as Gary Norden, which was a fake name made up by Radaris’ marketing department.
In April 2014, the Boston Business Journal published a story (PDF) about Radaris that extolled the company’s rapid growth and considerable customer base. The story noted that, “to date, the company has raised less than $1 million from Cyprus-based investment company Difive.”
“We live in a world where information becomes much more broad and much more available every single day,” the Boston Business Journal quoted Radaris’ fake CEO Gary Norden, who by then had somehow been demoted from CEO to vice president of business development.
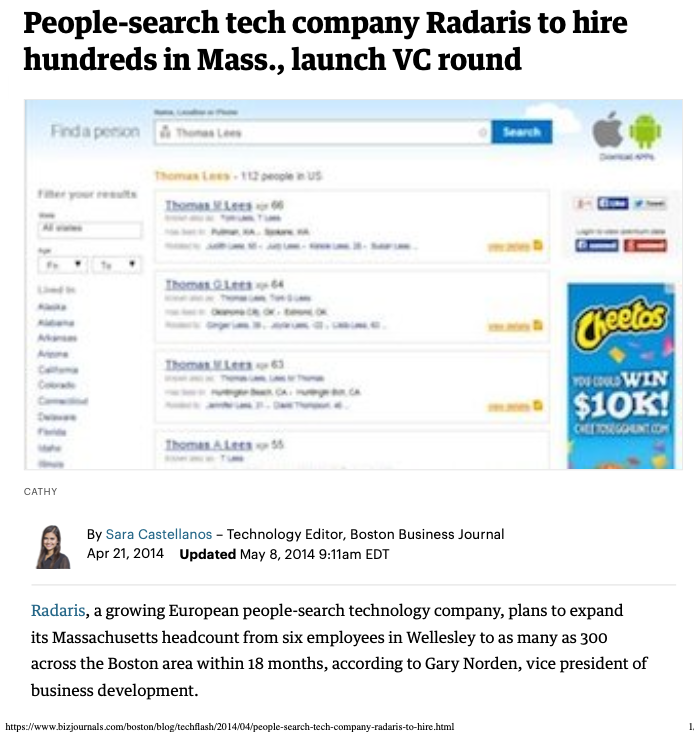
A Boston Business Journal story from April 2014 quotes the fictitious Radaris CEO Gary Norden.
“We decided there needs to be a service that allows for ease of monitoring of information about people,” the fake CEO said. The story went on to say Radaris was seeking to raise between $5 million and $7 million from investors in the ensuing months. Continue reading →