In March 2013 I wrote about Perkele, a crimeware kit designed to create malware for Android phones that can help defeat multi-factor authentication used by many banks. In this post, we’ll take a closer look at this threat, examining the malware as it is presented to the would-be victim as well as several back-end networks set up by cybercrooks who have been using mobile bots to fleece banks and their customers.
Perkele is sold for $1,000, and it’s made to interact with a wide variety of malware already resident on a victim’s PC. When a victim visits his bank’s Web site, the Trojan (be it Zeus or Citadel or whatever) injects malicious code into the victim’s browser, prompting the user to enter his mobile information, including phone number and OS type.
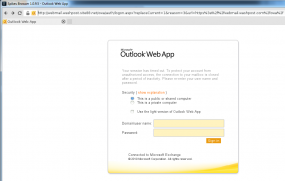
That information is relayed back to the attacker’s control server, which injects more code into the victim’s browser prompting him to scan a QR code with his mobile device to install an additional security mechanism.
Once the victim scans the QR code, the Perkele malware is downloaded and installed, allowing the attackers to intercept incoming SMS messages sent to that phone. At that point, the malware on the victim’s PC automatically initiates a financial transaction from the victim’s account.
When the bank sends an SMS with a one-time code, Perkele intercepts that code and sends it to the attacker’s control server. Then the malicious script on the victim’s PC receives the code and completes the unauthorized transaction.
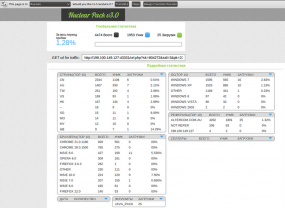
Web site security firm Versafe located a server that was being used to host malicious scripts tied to at least one Perkele operation. The company produced this report (PDF), which delves a bit deeper into the behavior and network activity generated by the crimeware kit.
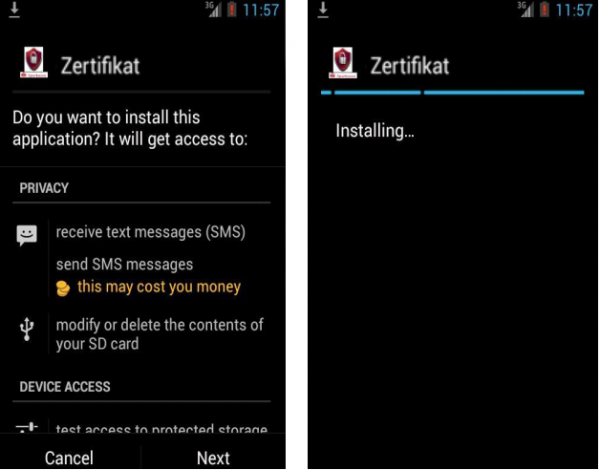
Versafe’s report includes several screenshots of the Perkele application as offered to would-be victims. The malware is presented as a security certificate; it’s named “zertificate” because the victim in this case banked at a German financial institution.
A few weeks ago, I encountered the back end system for what appears to be a Perkele distribution, or perhaps some other mobile malware bot; I should note that disguising an Android banking Trojan as a security certificate is not a ruse that’s limited to Perkele: The Pincert SMS malware also employs this trick, according to F-Secure.
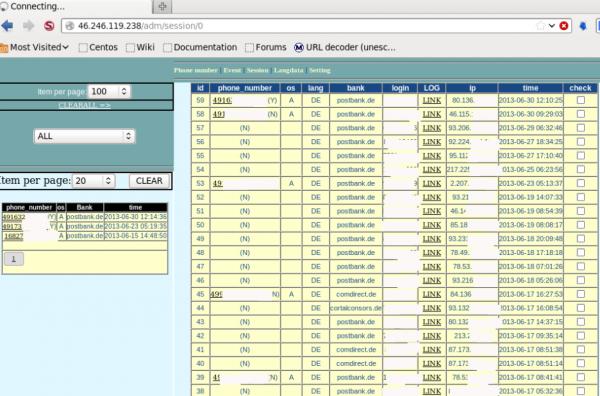
Anyhow, I scarcely had time to examine this particular mobile bot control panel before it was either taken down by German authorities or was moved elsewhere by the fraudsters. But it, too, was intercepting one-time codes from German banking victims using an Android malware component similarly disguised as a “zertificate.”
Apparently, it was fairly successful, stealing one-time codes from online banking customers of several German financial institutions, including Postbank and Comdirect.
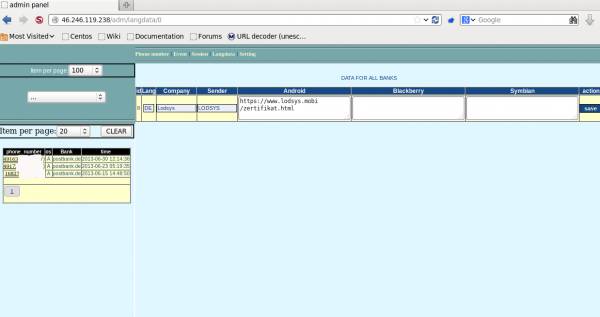
In the screen grab below, we can see the main administrative page of this panel, which controls which banks should be targeted and from where the fraudulent text messages should be sent.