Over the past several weeks, a handful of frantic Microsoft Windows users have written in to ask what they might do to recover from PC infections from “CryptoLocker,” the generic name for an increasingly prevalent and nasty strain of malicious software that encrypts your files until you pay a ransom. Unfortunately, the answer for these folks is usually either to pay up or suck it up. This post offers a few pointers to help readers avoid becoming the next victim.
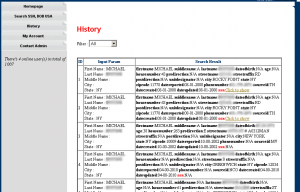
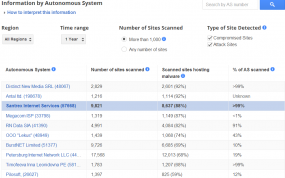
According to reports from security firms, CryptoLocker is most often spread through booby-trapped email attachments, but the malware also can be deployed by hacked and malicious Web sites by exploiting outdated browser plugins.
The trouble with CryptoLocker is not so much in removing the malware — that process appears to be surprisingly trivial in most cases. The real bummer is that all of your important files — pictures, documents, movies, MP3s — will remain scrambled with virtually unbreakable encryption unless and until you pay the ransom demand, which can range from $100 to $300 (and payable only in Bitcoins).
File-encrypting malware is hardly new. This sort of diabolical threat has been around in various incarnations for years, but it seems to have intensified in recent months. For years, security experts have emphasized the importance of backing up one’s files as a hedge against disaster in the wake of a malware infestation. Unfortunately, if your backup drives are connected physically or via the local network to the PC that gets infected with CryptoLocker, your backups may also be encrypted as well.
Computers infected with CryptoLocker may initially show no outward signs of infection; this is because it often takes many hours for the malware to encrypt all of the files on the victim’s PC and attached or networked drives. When that process is complete, however, the malware will display a pop-up message similar to the one pictured above, complete with a countdown timer that gives victims a short window of time in which to decide whether to pay the ransom or lose access to the files forever.
Fortunately, there are a couple of simple and free tools that system administrators and regular home users can use to minimize the threat from CryptoLocker malware. A team of coders and administrators from enterprise consulting firm thirdtier.net have released the CryptoLocker Prevention Kit — a comprehensive set of group policies that can be used to block CryptoLocker infections across a domain. The set of instructions that accompanies this free toolkit is comprehensive and well documented, and the group policies appear to be quite effective.