Last week, security firm RSA detailed a new cybecriminal project aimed at recruiting 100 botmasters to help launch a series of lucrative online heists targeting 30 U.S. banks. RSA’s advisory focused primarily on helping financial institutions prepare for an onslaught of more sophisticated e-banking attacks, and has already received plenty of media attention. I’m weighing in on the topic because their analysis seemed to merely scratch the surface of a larger enterprise that speaks volumes about why online attacks are becoming bolder and more brash toward Western targets.
RSA wasn’t specific about where it got its intelligence, but the report’s finding appear tied to a series of communications posted to exclusive Underweb forums by a Russian hacker who uses the nickname “vorVzakone,” which translates to “thief in law.” This is an expression in Russia and Eastern Europe that refers to an entire subculture of elite criminal gangs that operate beyond the reach of traditional law enforcement. The term is sometimes also used to refer to a single criminal kingpin.

A screen shot posted by vorVzakone, showing his Project Blitzkrieg malware server listing the number of online victims by bank.
In early September, vorVzakone posted a lengthy message announcing the beginning stages of a campaign he dubbed “Project Blitzkrieg.” This was envisioned as a collaborative effort designed to exploit the U.S. banking industry’s lack of anti-fraud mechanisms relative to European financial institutions, which generally require two-factor authentication for all wire transfers.
The campaign, purportedly to be rolled out between now and the Spring of 2013, proposes organizing hacker cells throughout the cybercriminal community to collaborate in exploiting these authentication weaknesses before U.S. banks erect more stringent controls. “The goal – together, en-masse and simultaneously process large amount of the given material before anti-fraud measures are increased,” vorVzakon wrote. A professionally translated version of his entire post is available here.
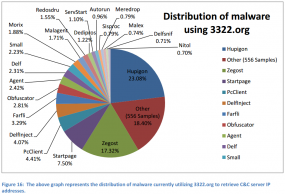
RSA said the project is being powered by a version of the Gozi Trojan called “Gozi Prinimalka.” The company believes this Trojan is part of family of malware used by a tight-knit crime gang that has stolen at least $5 million from banks already. From its analysis:
“In a boot camp-style process, accomplice botmasters will be individually selected and trained, thereby becoming entitled to a percentage of the funds they will siphon from victims’ accounts into mule accounts controlled by the gang. To make sure everyone is working hard, each botmaster will select their own ‘investor,’ who will put down the money required to purchase equipment for the operation (servers, laptops) with the incentive of sharing in the illicit profits. The gang and a long list of other accomplices will also reap their share of the spoils, including the money-mule herder and malware developers.
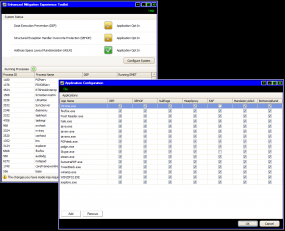
While the campaign is not revolutionary in technical terms, it will supposedly sport several noteworthy features. A novel virtual-machine-synching module announced by the gang, installed on the botmaster’s machine, will purportedly duplicate the victim’s PC settings, including the victim’s time zone, screen resolution, cookies, browser type and version, and software product IDs. Impersonated victims’ accounts will thus be accessed via a SOCKS proxy connection installed on their infected PCs, enabling the cloned virtual system to take on the genuine IP address when accessing the bank’s website.”
vorVzakone also says the operation will flood cyberheist victim phone lines while the victims are being robbed, in a bid to prevent account holders from receiving confirmation calls or text messages from their banks (I’ve covered this diversionary tactic in at least a couple of stories). Interestingly, this hacker started discussion threads on different forums in which he posts a video of this service in action. The video shows racks of centrally-managed notebook computers that are each running an installation of Skype. While there are simpler, cheaper and less resource-intensive ways of tying up a target’s phone line, causing all of these systems to call a single number simultaneously would probably achieve the same result. If you don’t see English subtitles when you play the video below, click the “cc” icon in the player to enable them:
THE FIRST RULE OF PROJECT BLITZKRIEG…
vorVzakone’s post has been met with a flurry of curiosity, enthusiasm and skepticism from members of the underground. The skepticism appears to stem from some related postings in which he brags about and calls attention to his credentials/criminal connections, an activity which tends to raise red flags in a community that generally prefers to keep a low profile.
In the following introductory snippet from a homemade movie he posted to youtube.com, vorVzakone introduces himself as “Sergey,” the stocky bald guy in the sunglasses. He also introduces a hacker who needs little introduction in the Russian underground — a well-known individual who used the nickname “NSD” [an abbreviation for the Russian term несанкционированный доступ, or “unauthorized access”] in the mid-2000s, when he claims to have exited the hacking scene.
“Good day to everybody, evening or night, depends on when you are watching me,” the hacker begins, standing in front of a Toyota Land Cruiser. “My name is Serega, you all know me by my nickname “vor v zakone” on the forum. This is my brother, my offline representative – Oleg ‘NSD’. So, what? I decided to meet you, let’s say ‘remotely.’ Without really meeting, right? Now you will see how I live. Let’s go, I will show you something.”
And he proceeds to show viewers around what he claims is his home. But many in the underground community found it difficult to take seriously someone who would be so cavalier about his personal safety, anonymity and security. “This guy’s language and demeanor is that of street corner drug dealer or a night club bouncer, and not of someone who can comprehend what ‘backconnect socks’ or GeoIP is,” remarked one Russian expert who helped translate some of the documentation included in this blog post.
But soon enough, hackers on the forums in which vorVzakone had posted his videos began checking the story, digging up records from Russian motor vehicle agencies indicating that the license plates on the Toyota and other cars in video were registered to a 27-year-old Oleg Vsevolodovich Tolstykh from Moscow. Further, they pointed out, the videos were posted by a youtube user named 01NSD, who also had previously posted Finnish and Russian television interviews with NSD describing various facets of the hacker underground. Indeed, if you pause this 2007 video 22 seconds in, you can see on NSD’s screen that he’s in the midst of a chat conversation with a hacker named vorVzakone.
In response to taunts and ridicule from some in the underground, vorVzakone posted this message on Oct. 6 to a prominent crime forum explaining why he doesn’t worry about going public with his business. Continue reading