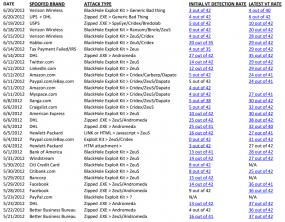
Shadowy online businesses that sell knockoff prescription drugs through spam and other dodgy advertising practices have begun relying more heavily on the U.S. Postal Service to deliver prescription drugs to buyers in the United States direct from warehouses or mules within the U.S. The shift comes as rogue online pill shops are seeking ways to lower shipping costs, a major loss leader for most of these operations.
Traditionally, a majority of the counterfeit pills advertised and sold to Americans online have shipped from India. But the process of getting the pills from India to customers in the United States is so expensive and fraught with complications that it has proved to be a big cost center for the largest rogue pharmaceutical operations, according to a study I wrote about last month.
“One of the surprising things we found was that shipping dominates program costs,” said Stefan Savage, one of the lead authors on the study, and a professor in the systems and networking group at the University of California San Diego.
The researchers discovered that most rogue pharmacy operations spend between 11 to 12 percent of their annual revenue on shipping costs. Part of the reason for the high cost is that pill shipments from India and elsewhere outside of the United States frequently get delayed or confiscated by U.S. Customs officials. This forces the rogue pharmacies to either refund the customer’s money, or to eat the costs of re-shipping the pills.
Increasingly, however, some of the largest spam affiliate programs are delivering some of their most popular drugs — including erectile dysfunction pills and everything from Accutane to Cipro and Diflucan and Plavix — direct to U.S. buyers from shipping locations within the United States.
“This is why you see pharmacy outfits like RX-Partners, Mailien and Stimulcash picking the most popular drugs and warehousing them in the United States so they can do USPS shipping through mules,” Savage said.